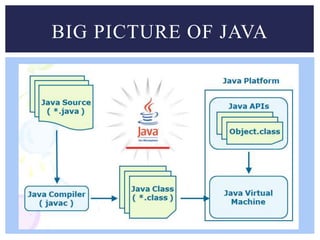
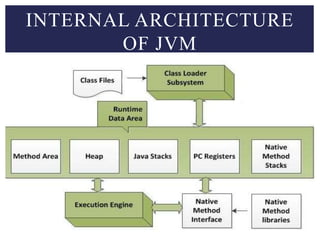
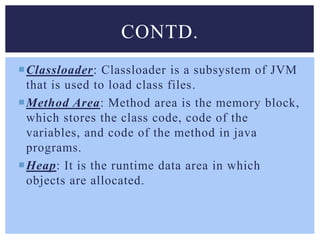
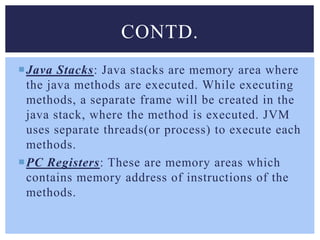
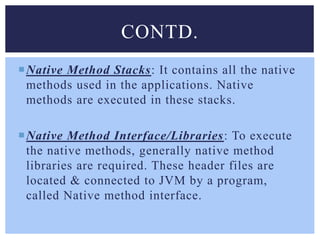
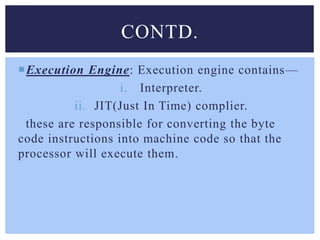
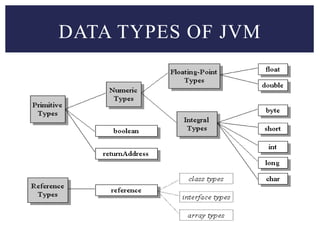
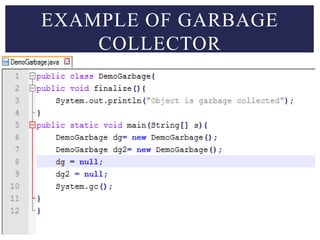
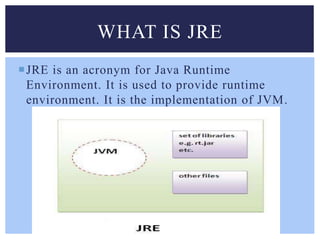
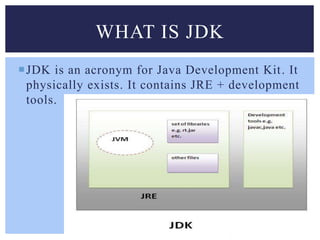
The document provides a comprehensive overview of the Java Virtual Machine (JVM), describing its role as the execution environment for Java bytecode and its internal architecture, including components like classloader, method area, and garbage collection. It also distinguishes between different editions of Java (SE, EE, ME) and explains the relationships among JVM, Java Runtime Environment (JRE), and Java Development Kit (JDK). The document emphasizes the significance of the JVM in Java program execution and its security promises.