Here are the key differences:
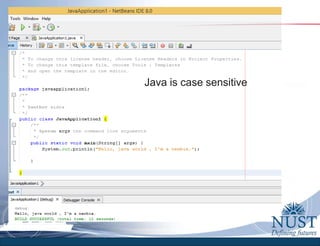
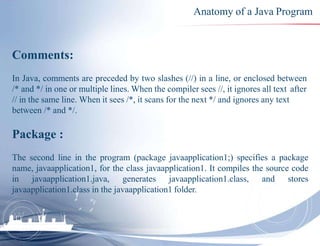
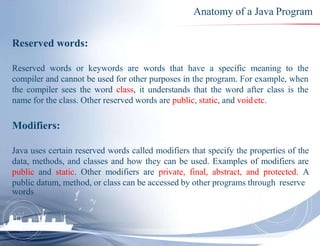
Reserved words: These are words that have special meaning in Java like class, public, etc. They cannot be used as regular identifiers.
Modifiers: Modifiers like public, private, static etc. specify attributes of classes, methods and variables.
Package: A package is a namespace that organizes related classes and interfaces. It provides access protection.
Libraries: Libraries are pre-compiled classes that provide useful functionality that can be included in programs using import statements.
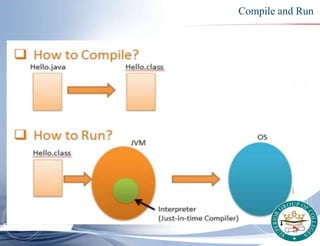
JVM version: The Java Virtual Machine version specifies the Java runtime environment. Programs need to be compatible with the JVM version.
JVM: The Java Virtual Machine is an abstract computing machine that



![1. // Your First Program
2. class HelloWorld
{
3. public static void
main(String[] args)
{
4.
System.out.println("Hello
, World!");
}
}
In line 1; In Java, any line starting
with // is a comment
In line 2; in the program, HelloWorld is
the name of the class, and the class
definition is: class helloworld
In line 3; This is the main method.
Every application in Java must contain
the main method. The Java compiler
starts executing the code from the
main method.
In line 4; The code above is a print
statement. It prints the text Hello,
World! to standard output (your
screen). The text inside the quotation
marks is called String in Java.](https://image.slidesharecdn.com/lecture1-updated-230127140454-5568741f/85/OOP-with-Java-16-320.jpg)
![Anatomy of a Java Program
Statements:
A statement represents an action or a sequence of actions. The statement
System.out.println(“Hello Java world!") in the program in Example is a statement
to display the greeting " Hello Java world! “. Every statement in Java ends with a
semicolon (;).
Blocks:
A pair of braces in a program forms a block that groups components of aprogram.
public class JavaApplication1 {
public static void main(String[] args) {
System.out.println("Hello Java World !");
}
}
Class block
Meth
CE&ME, NUST
od block](https://image.slidesharecdn.com/lecture1-updated-230127140454-5568741f/85/OOP-with-Java-19-320.jpg)
