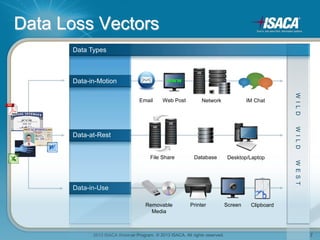
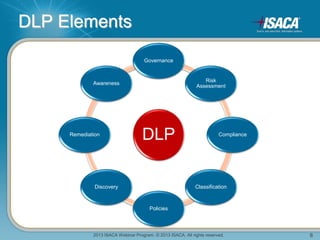
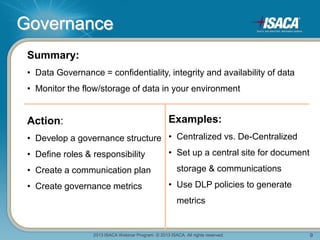
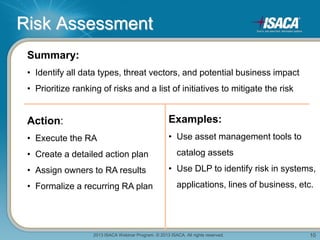
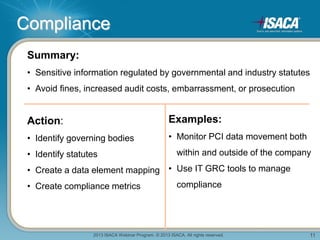
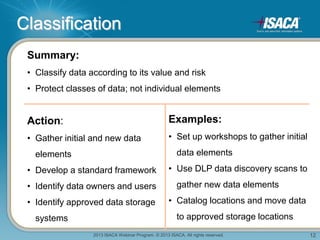
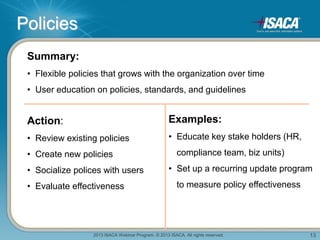
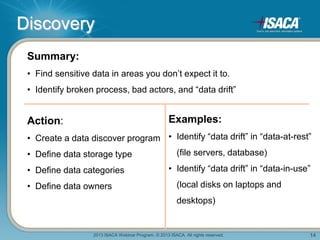
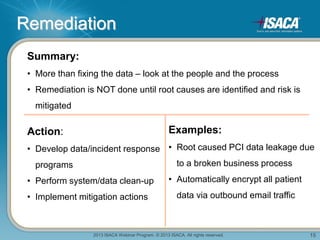
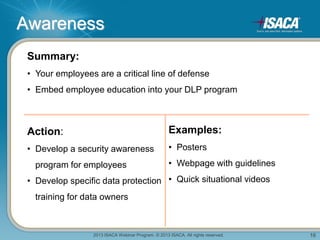
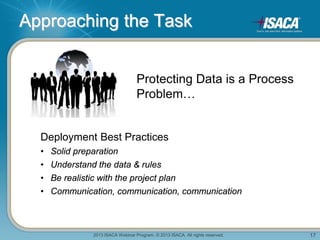
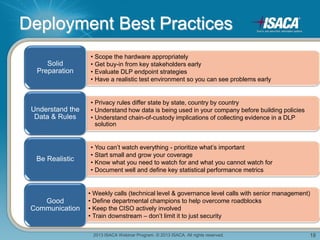
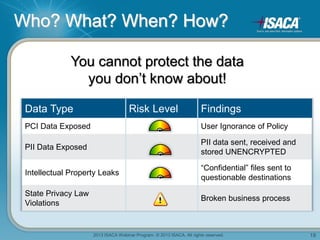
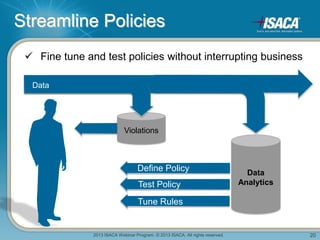
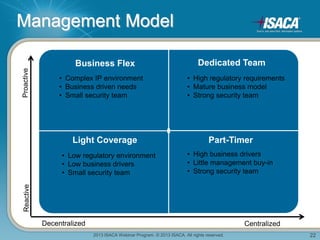
The ISACA webinar discusses best practices for implementing Data Loss Prevention (DLP) led by experts Michael Avdeev and John Callaghan. Key topics include the governance framework, risk assessment, compliance, data classification, policy development, discovery, remediation, and awareness training. The presentation emphasizes the importance of understanding data, clear communication, and involving stakeholders to effectively protect sensitive information.