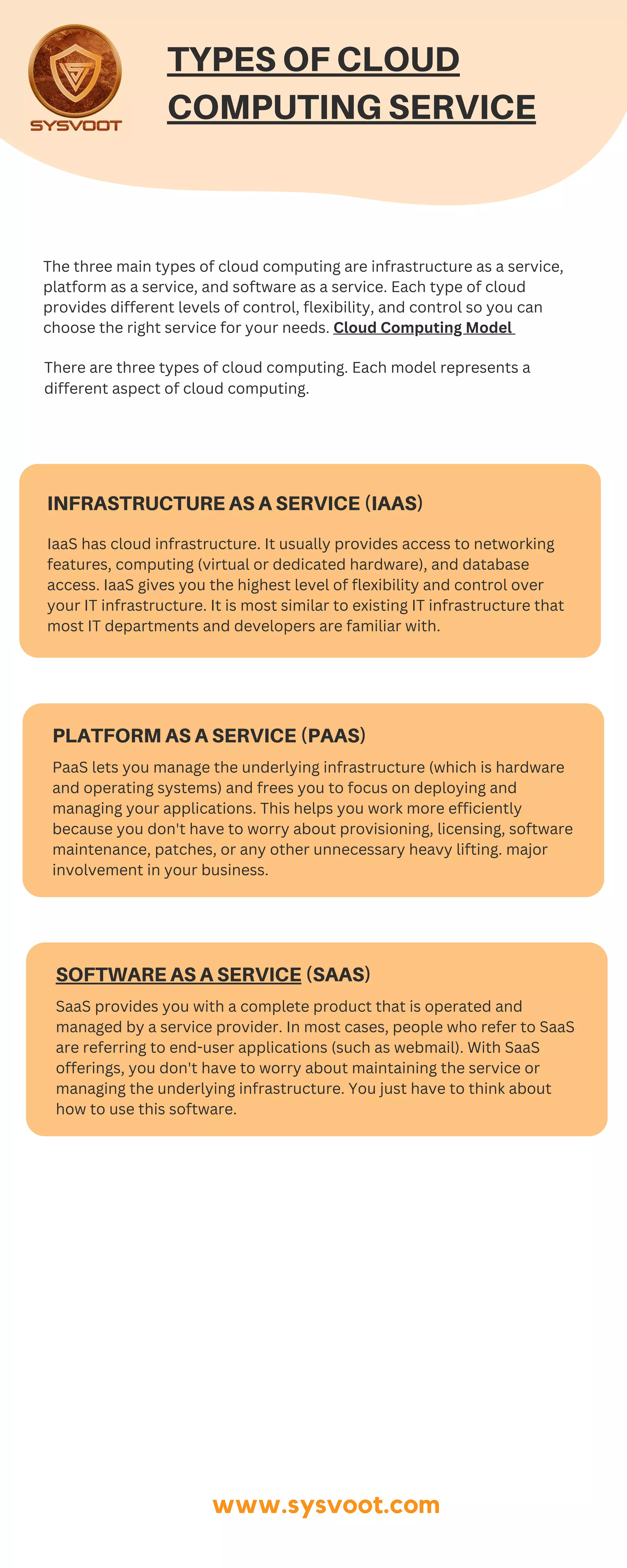
The document outlines the three main types of cloud computing: Infrastructure as a Service (IaaS), Platform as a Service (PaaS), and Software as a Service (SaaS). IaaS offers flexibility and control over IT infrastructure, PaaS lets users manage applications without worrying about underlying infrastructure, and SaaS provides fully managed end-user applications. Each type caters to different needs of businesses and developers, emphasizing varying levels of responsibility and management.