Properties of Salesforce CRM.pdf
•
0 likes•2 views
By incorporating salesforce with other applications, businesses can now unleash the large data pool and use it to their advantage. The guide provides all the necessary information that your business needs for Salesforce CRM integration.
Report
Share
Report
Share
Download to read offline
Recommended
Salesforce CRM - Transforming Customer Relationships in the Digital Age

Salesforce CRM - Transforming Customer Relationships in the Digital AgeSachin Wadekar (sachinwadekar@hotmail.com)
Transforming Customer Relationships in the Digital Age using Salesforce CRMHow Salesforce CRM works & who should use it?

You’ve heard the word “Salesforce” being thrown around by small and big enterprises, but you have no idea if your business needs it? If you’re running a business that’s growing just the way you want it to, you will probably need Salesforce CRM sooner than later. But first things first—learn what Salesforce CRM is, how it works and how you should use it to support your day to day operations.
Read the blog in detail
http://suyati.com/how-salesforce-crm-works-and-uses/
For any information on our Salesforce capabilities, email services@suyati.com.
http://suyati.com/
Boost Your Enterprise Growth with Salesforce Consulting Services

Salesforce CRM is a powerful tool that can help enterprises grow by providing a centralized view of customer data, automating sales and marketing processes, and providing insights that can help businesses make better decisions.
Here are some of the benefits of using Salesforce CRM for enterprise growth:
FOR More Details - https://www.fexle.com/salesforce-consulting-services
Data Centralization
With Salesforce consulting services, business visionaries can help enterprises centralize their customer data, which can make it easier to track customer interactions, identify opportunities, and provide personalized service.
Automation
Do you want an automated sales and marketing process? It definitely can save time and money for businesses. For example, Salesforce CRM can automatically send follow-up emails to leads, track leads through the sales pipeline, and generate reports on marketing campaigns.
Insights to make better decisions
Systematic, well-presented, and optimally analyzed insight is the key of success for any enterprise. With the cloud computing technology businesses make better decisions. For example, Salesforce CRM can track customer behavior, identify trends, and generate reports on sales performance.
Implementing Salesforce CRM can be a complex process. That's why it's important to work with a Salesforce Consulting Partner. A Salesforce Consulting company can help you assess your needs, implement Salesforce CRM, and train your team on how to use it.
Here are some of the benefits of working with a Salesforce Consulting Partner:
Expertise
Salesforce Consulting Partners have extensive experience implementing Salesforce CRM. They can help you choose the right solution for your needs and implement it effectively.
Support
Certified Salesforce experts can provide support after the implementation is complete. They can help you troubleshoot problems, train your team, and make sure that you are getting the most out of Salesforce CRM.
Peace of mind
Working with a Salesforce Partner can give you peace of mind knowing that your Salesforce CRM implementation is in good hands.
If you are an enterprise looking to grow your business with Salesforce CRM, I recommend working with FEXLE Services, a Salesforce Gold Consulting Partner. It will help you get the most out of Salesforce CRM and achieve your business goals.
Mastering the Art of Salesforce CRM

A Salesforce CRM Specialist is a professional who specializes in implementing and managing Salesforce CRM systems. They have a deep understanding of the platform’s features and capabilities, as well as best practices for customization, integration, and administration.
Top 40 CRM Features

Your CRM platform has the ability to automate certain aspects of your sales. Learn to know the top 40 CRM Features
CRM Software: Streamlining Customer Relationship Management

CRM software, or Customer Relationship Management software, is a powerful tool that helps businesses effectively manage their customer relationships. It provides a centralized platform to store and organize customer data, automate sales and marketing processes, and improve customer interactions. CRM software streamlines workflows, enhances customer understanding, and enables personalized marketing efforts, ultimately driving customer engagement, sales growth, and long-term customer loyalty.
Recommended
Salesforce CRM - Transforming Customer Relationships in the Digital Age

Salesforce CRM - Transforming Customer Relationships in the Digital AgeSachin Wadekar (sachinwadekar@hotmail.com)
Transforming Customer Relationships in the Digital Age using Salesforce CRMHow Salesforce CRM works & who should use it?

You’ve heard the word “Salesforce” being thrown around by small and big enterprises, but you have no idea if your business needs it? If you’re running a business that’s growing just the way you want it to, you will probably need Salesforce CRM sooner than later. But first things first—learn what Salesforce CRM is, how it works and how you should use it to support your day to day operations.
Read the blog in detail
http://suyati.com/how-salesforce-crm-works-and-uses/
For any information on our Salesforce capabilities, email services@suyati.com.
http://suyati.com/
Boost Your Enterprise Growth with Salesforce Consulting Services

Salesforce CRM is a powerful tool that can help enterprises grow by providing a centralized view of customer data, automating sales and marketing processes, and providing insights that can help businesses make better decisions.
Here are some of the benefits of using Salesforce CRM for enterprise growth:
FOR More Details - https://www.fexle.com/salesforce-consulting-services
Data Centralization
With Salesforce consulting services, business visionaries can help enterprises centralize their customer data, which can make it easier to track customer interactions, identify opportunities, and provide personalized service.
Automation
Do you want an automated sales and marketing process? It definitely can save time and money for businesses. For example, Salesforce CRM can automatically send follow-up emails to leads, track leads through the sales pipeline, and generate reports on marketing campaigns.
Insights to make better decisions
Systematic, well-presented, and optimally analyzed insight is the key of success for any enterprise. With the cloud computing technology businesses make better decisions. For example, Salesforce CRM can track customer behavior, identify trends, and generate reports on sales performance.
Implementing Salesforce CRM can be a complex process. That's why it's important to work with a Salesforce Consulting Partner. A Salesforce Consulting company can help you assess your needs, implement Salesforce CRM, and train your team on how to use it.
Here are some of the benefits of working with a Salesforce Consulting Partner:
Expertise
Salesforce Consulting Partners have extensive experience implementing Salesforce CRM. They can help you choose the right solution for your needs and implement it effectively.
Support
Certified Salesforce experts can provide support after the implementation is complete. They can help you troubleshoot problems, train your team, and make sure that you are getting the most out of Salesforce CRM.
Peace of mind
Working with a Salesforce Partner can give you peace of mind knowing that your Salesforce CRM implementation is in good hands.
If you are an enterprise looking to grow your business with Salesforce CRM, I recommend working with FEXLE Services, a Salesforce Gold Consulting Partner. It will help you get the most out of Salesforce CRM and achieve your business goals.
Mastering the Art of Salesforce CRM

A Salesforce CRM Specialist is a professional who specializes in implementing and managing Salesforce CRM systems. They have a deep understanding of the platform’s features and capabilities, as well as best practices for customization, integration, and administration.
Top 40 CRM Features

Your CRM platform has the ability to automate certain aspects of your sales. Learn to know the top 40 CRM Features
CRM Software: Streamlining Customer Relationship Management

CRM software, or Customer Relationship Management software, is a powerful tool that helps businesses effectively manage their customer relationships. It provides a centralized platform to store and organize customer data, automate sales and marketing processes, and improve customer interactions. CRM software streamlines workflows, enhances customer understanding, and enables personalized marketing efforts, ultimately driving customer engagement, sales growth, and long-term customer loyalty.
Salesforce.pptx

CETPA Infotech offers certification courses for Salesforce, which can help you enhance your knowledge and skills, and make you more marketable in the job market.Salesforce is a widely-used platform, and completing a course from CETPA Infotech can open up various career opportunities for you in fields such as sales, marketing, customer service, and more.Salesforce professionals are in high demand, and completing a Salesforce course from CETPA Infotech can increase your chances of landing a high-paying job in this field.CETPA Infotech has partnerships with various companies, which can provide you with access to industry connections and job opportunities.Salesforce course from CETPA Infotech can provide you with enhanced skills, certification, career opportunities, salary increment, hands-on training, and industry connections.
CRM and ERP – Know the Difference

Both CRM and ERP have one goal, to automate businesses and help companies all around the world become faster and more efficient and foster their growth. While both Customer Relationship Management (CRM) and Enterprise Resource Planning (ERP) are important for a business, let us take a look at some of the key differences between both.
Read the full blog here: http://suyati.com/crm-and-erp-know-the-difference/
Reach us at: jghosh@suyati.com
CRM Development Company

FlightsLogic is one of the best Custom CRM Software Development Company. We deliver the best CRM software development Solutions around the world. Nurture your business with our customized CRM Software Development Services.
For more details, Pls visit our Website:
https://www.flightslogic.com/crm-development-company.php
Salesforce pros and cons - know the truth

Business automation involves complex hardware & software implementation. This should also supports reducing costs, monitoring all operations, controlling interactions with customers and giving a quick response.
Most companies opt for Salesforce as it helps in streamlining business operations. Salesforce is a cloud-based platform which is not only a CRM solution but an all-in-one solution which offers sales management, customer service, marketing automation and partner relationship management.
According to recent statistics Salesforce has more than 150,000 clients worldwide.
Salesforce Services

QR Solutions a Salesforce consulting & implementation company in Australia has helped many businesses by developing & integrating the world’s No.1 Salesforce CRM System.
To know more, visit-https://qrsolutions.in/solutions/salesforce/
Customer relationship management(crm)

Overview about Customer Relationship Management.
modules in crm.
Why erp must have crm?
crm includes?
types of crm
what does crm includes
features of crm
crm software.
A beginners guide for salesforce service cloud customers

Salesforce is a CRM cloud-based solution that caters towards companies, everything being equal, – it is a single platform intended to deal with all parts of deals, service, marketing, and analytics, through zone explicit "Clouds" in request to meet explicit business needs.
Salesforce Online Training

Salesforce Training will cover salesforce development training and salesforce administration training by Keylabs.
http://www.keylabstraining.com/salesforce-online-training-hyderabad-bangalore
Salesforce is a world leader on demand customer relationship management tool. Salesforce.com is also known as Customer Relationship Management (CRM).
salesforce training,
salesforce online training,
salesforce training institutes in hyderabad,
salesforce training institutes in bangalore,
best salesforce training institutes in hyderabad,
salesforce training online,
salesforce online course,
salesforce developer training,
salesforce administrator training,
salesforce training in mumbai
Unlocking Sales Success.pdf

From Nimble Nurturing to Copper’s Customer Magic: Meet the CRM All-Stars of 2023 and uncover the secrets behind seamless sales and personalized experiences.
Sales Force Automation

Automate, Simplify and Manage all the information your sales organization needs with one comprehensive CRM tool: Impel CRM
How Salesforce Sales Cloud Implementation Can Propel Business Growth?

Sales Cloud is a platform that supports the sales, marketing, and customer service functions of an enterprise. It provides a unified view of the customer information in an integrated platform by incorporating sales, marketing, lead generation, customer service, and business analytics.
Here are some irresistible benefits of Salesforce Sales Cloud implementation:
Salesforce CRM Managed Services A Beginner's Guide

Explore our insightful infographic providing a comprehensive overview of Salesforce CRM Managed Services. Designed for beginners, it breaks down key concepts, benefits, and the role of managed services in optimizing your CRM.
Managed IT Service Provider in New York.pdf

Sysvoot is a prominent consulting and professional services firm that has established a strong foothold in New York, offering IT services that encompass cyber risk management, data analytics, and cloud computing.
What is Paas Benefit of Paas.pdf

PaaS stands for Platform as a Service, which is a cloud computing model that provides a platform for software development and deployment. In this model, the provider offers infrastructure, middleware, and software tools as a service to users, who can then build and deploy their applications on top of this platform. This eliminates the need for users to manage and maintain the underlying infrastructure, allowing them to focus on developing and delivering their applications.
More Related Content
Similar to Properties of Salesforce CRM.pdf
Salesforce.pptx

CETPA Infotech offers certification courses for Salesforce, which can help you enhance your knowledge and skills, and make you more marketable in the job market.Salesforce is a widely-used platform, and completing a course from CETPA Infotech can open up various career opportunities for you in fields such as sales, marketing, customer service, and more.Salesforce professionals are in high demand, and completing a Salesforce course from CETPA Infotech can increase your chances of landing a high-paying job in this field.CETPA Infotech has partnerships with various companies, which can provide you with access to industry connections and job opportunities.Salesforce course from CETPA Infotech can provide you with enhanced skills, certification, career opportunities, salary increment, hands-on training, and industry connections.
CRM and ERP – Know the Difference

Both CRM and ERP have one goal, to automate businesses and help companies all around the world become faster and more efficient and foster their growth. While both Customer Relationship Management (CRM) and Enterprise Resource Planning (ERP) are important for a business, let us take a look at some of the key differences between both.
Read the full blog here: http://suyati.com/crm-and-erp-know-the-difference/
Reach us at: jghosh@suyati.com
CRM Development Company

FlightsLogic is one of the best Custom CRM Software Development Company. We deliver the best CRM software development Solutions around the world. Nurture your business with our customized CRM Software Development Services.
For more details, Pls visit our Website:
https://www.flightslogic.com/crm-development-company.php
Salesforce pros and cons - know the truth

Business automation involves complex hardware & software implementation. This should also supports reducing costs, monitoring all operations, controlling interactions with customers and giving a quick response.
Most companies opt for Salesforce as it helps in streamlining business operations. Salesforce is a cloud-based platform which is not only a CRM solution but an all-in-one solution which offers sales management, customer service, marketing automation and partner relationship management.
According to recent statistics Salesforce has more than 150,000 clients worldwide.
Salesforce Services

QR Solutions a Salesforce consulting & implementation company in Australia has helped many businesses by developing & integrating the world’s No.1 Salesforce CRM System.
To know more, visit-https://qrsolutions.in/solutions/salesforce/
Customer relationship management(crm)

Overview about Customer Relationship Management.
modules in crm.
Why erp must have crm?
crm includes?
types of crm
what does crm includes
features of crm
crm software.
A beginners guide for salesforce service cloud customers

Salesforce is a CRM cloud-based solution that caters towards companies, everything being equal, – it is a single platform intended to deal with all parts of deals, service, marketing, and analytics, through zone explicit "Clouds" in request to meet explicit business needs.
Salesforce Online Training

Salesforce Training will cover salesforce development training and salesforce administration training by Keylabs.
http://www.keylabstraining.com/salesforce-online-training-hyderabad-bangalore
Salesforce is a world leader on demand customer relationship management tool. Salesforce.com is also known as Customer Relationship Management (CRM).
salesforce training,
salesforce online training,
salesforce training institutes in hyderabad,
salesforce training institutes in bangalore,
best salesforce training institutes in hyderabad,
salesforce training online,
salesforce online course,
salesforce developer training,
salesforce administrator training,
salesforce training in mumbai
Unlocking Sales Success.pdf

From Nimble Nurturing to Copper’s Customer Magic: Meet the CRM All-Stars of 2023 and uncover the secrets behind seamless sales and personalized experiences.
Sales Force Automation

Automate, Simplify and Manage all the information your sales organization needs with one comprehensive CRM tool: Impel CRM
How Salesforce Sales Cloud Implementation Can Propel Business Growth?

Sales Cloud is a platform that supports the sales, marketing, and customer service functions of an enterprise. It provides a unified view of the customer information in an integrated platform by incorporating sales, marketing, lead generation, customer service, and business analytics.
Here are some irresistible benefits of Salesforce Sales Cloud implementation:
Salesforce CRM Managed Services A Beginner's Guide

Explore our insightful infographic providing a comprehensive overview of Salesforce CRM Managed Services. Designed for beginners, it breaks down key concepts, benefits, and the role of managed services in optimizing your CRM.
Similar to Properties of Salesforce CRM.pdf (20)
Uses Of New And Emerging Technologies In Marketing Software

Uses Of New And Emerging Technologies In Marketing Software
A beginners guide for salesforce service cloud customers

A beginners guide for salesforce service cloud customers
Salesforce online training || Salesforce Integration | salesforce lightning

Salesforce online training || Salesforce Integration | salesforce lightning
How Salesforce Sales Cloud Implementation Can Propel Business Growth?

How Salesforce Sales Cloud Implementation Can Propel Business Growth?
Salesforce CRM Managed Services A Beginner's Guide

Salesforce CRM Managed Services A Beginner's Guide
More from Sysvoot Antivirus
Managed IT Service Provider in New York.pdf

Sysvoot is a prominent consulting and professional services firm that has established a strong foothold in New York, offering IT services that encompass cyber risk management, data analytics, and cloud computing.
What is Paas Benefit of Paas.pdf

PaaS stands for Platform as a Service, which is a cloud computing model that provides a platform for software development and deployment. In this model, the provider offers infrastructure, middleware, and software tools as a service to users, who can then build and deploy their applications on top of this platform. This eliminates the need for users to manage and maintain the underlying infrastructure, allowing them to focus on developing and delivering their applications.
Benefit of SaaS.pdf

SaaS is commonly used for customer relationship management (CRM), enterprise resource planning (ERP), and other business-critical applications. Some examples of SaaS include Microsoft Office 365, Salesforce, and Zoom.
Best Practices to Secure Company's Legacy Applications in 2023.pdf

Sysvoot offers comprehensive legacy application security services to protect your organization's sensitive data and operations. We conduct risk assessments, implement security best practices, and provide regular updates and patches to ensure your systems are secure. Trust Sysvoot for end-to-end legacy application security solutions.
Types of Cloud Computing Service 

The three main types of cloud computing are infrastructure as a service, platform as a service, and software as a service. Each type of cloud provides different levels of control, flexibility, and control so you can choose the right service for your needs. Cloud Computing Model
Properties of Salesforce CRM.pdf

By incorporating salesforce with other applications, businesses can now unleash the large data pool and use it to their advantage. The guide provides all the necessary information that your business needs for Salesforce CRM integration.
Sysvoot - Characteristics Of Service Model Of Cloud Computing.pdf

Multi-Occupant: Multi-tenure is a design where a solitary occurrence of a product application serves different clients. Every client is known as an inhabitant.
How to Choose Managed IT Service Provider.pdf

Every step or decision you take for your business influences the course of your business. While some decisions may not be that instrumental, deciding on a Managed Service Provider (MSP) can surely make a lot of impacts.
How to Make an Effective Cloud Disaster Recovery Strategy.pdf

Problems are inevitable and a problem that hinders the operations of a company can be tagged as a Disaster. Technical glitches or security breaches can result in disasters and once it sets in, the organization can face huge issues.
Now coming to disaster recovery. It can be defined as the process to evade or bounce back after a disaster. This helps them restore important documents. A cloud disaster recovery system aids the company to restore their files with the usage of cloud services.
Latest Cyber Attacks and Trends That You Should Know.pdf

Cybersecurity is an ever evolving field and cybercriminals are devising novel ways to infiltrate systems and cause havoc. In such times it is essential to stay informed and take necessary actions to keep them at bay. So head to our blog section and find the latest cybersecurity threats that you should be aware of.
Read More:-
https://www.sysvoot.com/blog/latest-cyber-attacks-and-trends-that-you-should-know/
How to Use a Firewall For The Best Protection.pdf

Firewalls are a key security tool that every firm must use. However, the sad reality is that many don't understand how to make the best out of it. This blog provides you with tips on how any firewall should be used to the best of its abilities. For more such informational posts do follow SYSVOOT.
Read More:- https://www.sysvoot.com/blog/how-to-use-a-firewalls-for-the-best-protection/
5 Main Aspects of IoT Impact on Cybersecurity.pdf

The mere velocity of growth in the IoT market guarantees fresh challenges and hazards in the immediate future. The field of cybersecurity requires development at the same speed in order to retort the growing number of pleas for security and protection.
Top 10 Malware May 2022 .pdf

Malware is a constant threat and being aware of them is the first step to keeping them at bay. Here we have listed the top 10 malware to watch out for this upcoming month.
Read More:- https://www.sysvoot.com/blog/top-10-malware-may-2022/
Windows vs Mac Which to Choose.pdf

Windows and Mac are both equally good and choosing from either of the two is based on your requirement. Just peruse the pros and cons before you make a pick so that you can understand which OS works for you. We hope you find this article useful.
What is Identity and Access Management.pdf

Wondering what is IAM? Well, head to our blog section and find all the required information about IAM and why you need it for your firm.
Read More:- https://www.sysvoot.com/blog/what-is-identity-and-access-management/
6 Ways to Protect Yourself From Online Catfishing Scams.pdf

Catfishing is the act of using fake images and information to formulate a fraudulent identity on the internet. A catfish will try to steal some other person's personal information including name, pictures, emails, etc. to create their own identity. In our blog, we have tried to explain what exactly it is and what necessary steps you can undertake to stay protected.
What is Access Control and Why is it Important for Cybersecurity.pdf

Access control is the modern way to keep your data protected. Understand what is it and why is it important by heading to our blog section. Stay informed and stay protected!
How To Identify Popular Spyware

So here was top spyware to watch out for. The easiest way to keep them at bay is by using a high-quality antivirus like SYSVOOT. Sysvoot is instilled with advanced technology that helps warn you about any lurking spyware and in the process saves you and your personal information. So don’t be a victim of spyware and install Sysvoot now.
Why are Proxy Servers Important for Cybersecurity

Using proxies accentuates the safety of any user or firm. You can use various types of Proxies as per your need and protect yourself. Sysvoot comes with a proxy feature to help safeguard your firm or personal information from being a victim of various types of cybercrimes. Install Sysvoot now and add protection to your devices.
What Are Social Engineering Attacks .pdf

Social engineering attacks arrive in many patterns. The term is used to depict a vast range of vicious activities carried out through human exchanges. Criminals manipulate human nature and essential human tendencies – rather than specialized susceptibility or technical setbacks – to attack an organization.
More from Sysvoot Antivirus (20)
Best Practices to Secure Company's Legacy Applications in 2023.pdf

Best Practices to Secure Company's Legacy Applications in 2023.pdf
Sysvoot - Characteristics Of Service Model Of Cloud Computing.pdf

Sysvoot - Characteristics Of Service Model Of Cloud Computing.pdf
How to Make an Effective Cloud Disaster Recovery Strategy.pdf

How to Make an Effective Cloud Disaster Recovery Strategy.pdf
Latest Cyber Attacks and Trends That You Should Know.pdf

Latest Cyber Attacks and Trends That You Should Know.pdf
6 Ways to Protect Yourself From Online Catfishing Scams.pdf

6 Ways to Protect Yourself From Online Catfishing Scams.pdf
What is Access Control and Why is it Important for Cybersecurity.pdf

What is Access Control and Why is it Important for Cybersecurity.pdf
Recently uploaded
Encryption in Microsoft 365 - ExpertsLive Netherlands 2024

In this session I delve into the encryption technology used in Microsoft 365 and Microsoft Purview. Including the concepts of Customer Key and Double Key Encryption.
Mission to Decommission: Importance of Decommissioning Products to Increase E...

Mission to Decommission: Importance of Decommissioning Products to Increase Enterprise-Wide Efficiency by VP Data Platform, American Express
Accelerate your Kubernetes clusters with Varnish Caching

A presentation about the usage and availability of Varnish on Kubernetes. This talk explores the capabilities of Varnish caching and shows how to use the Varnish Helm chart to deploy it to Kubernetes.
This presentation was delivered at K8SUG Singapore. See https://feryn.eu/presentations/accelerate-your-kubernetes-clusters-with-varnish-caching-k8sug-singapore-28-2024 for more details.
From Daily Decisions to Bottom Line: Connecting Product Work to Revenue by VP...

From Daily Decisions to Bottom Line: Connecting Product Work to Revenue by VP of Product, Amplitude
Elevating Tactical DDD Patterns Through Object Calisthenics

After immersing yourself in the blue book and its red counterpart, attending DDD-focused conferences, and applying tactical patterns, you're left with a crucial question: How do I ensure my design is effective? Tactical patterns within Domain-Driven Design (DDD) serve as guiding principles for creating clear and manageable domain models. However, achieving success with these patterns requires additional guidance. Interestingly, we've observed that a set of constraints initially designed for training purposes remarkably aligns with effective pattern implementation, offering a more ‘mechanical’ approach. Let's explore together how Object Calisthenics can elevate the design of your tactical DDD patterns, offering concrete help for those venturing into DDD for the first time!
When stars align: studies in data quality, knowledge graphs, and machine lear...

Keynote at DQMLKG workshop at the 21st European Semantic Web Conference 2024
Generating a custom Ruby SDK for your web service or Rails API using Smithy

Have you ever wanted a Ruby client API to communicate with your web service? Smithy is a protocol-agnostic language for defining services and SDKs. Smithy Ruby is an implementation of Smithy that generates a Ruby SDK using a Smithy model. In this talk, we will explore Smithy and Smithy Ruby to learn how to generate custom feature-rich SDKs that can communicate with any web service, such as a Rails JSON API.
De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovati...

De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovation With Your Product by VP of Product Design, Warner Music Group
Key Trends Shaping the Future of Infrastructure.pdf

Keynote at DIGIT West Expo, Glasgow on 29 May 2024.
Cheryl Hung, ochery.com
Sr Director, Infrastructure Ecosystem, Arm.
The key trends across hardware, cloud and open-source; exploring how these areas are likely to mature and develop over the short and long-term, and then considering how organisations can position themselves to adapt and thrive.
Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024

As AI technology is pushing into IT I was wondering myself, as an “infrastructure container kubernetes guy”, how get this fancy AI technology get managed from an infrastructure operational view? Is it possible to apply our lovely cloud native principals as well? What benefit’s both technologies could bring to each other?
Let me take this questions and provide you a short journey through existing deployment models and use cases for AI software. On practical examples, we discuss what cloud/on-premise strategy we may need for applying it to our own infrastructure to get it to work from an enterprise perspective. I want to give an overview about infrastructure requirements and technologies, what could be beneficial or limiting your AI use cases in an enterprise environment. An interactive Demo will give you some insides, what approaches I got already working for real.
Designing Great Products: The Power of Design and Leadership by Chief Designe...

Designing Great Products: The Power of Design and Leadership by Chief Designer, Beats by Dr Dre
FIDO Alliance Osaka Seminar: The WebAuthn API and Discoverable Credentials.pdf

FIDO Alliance Osaka Seminar
The Art of the Pitch: WordPress Relationships and Sales

Clients don’t know what they don’t know. What web solutions are right for them? How does WordPress come into the picture? How do you make sure you understand scope and timeline? What do you do if sometime changes?
All these questions and more will be explored as we talk about matching clients’ needs with what your agency offers without pulling teeth or pulling your hair out. Practical tips, and strategies for successful relationship building that leads to closing the deal.
Leading Change strategies and insights for effective change management pdf 1.pdf

Leading Change strategies and insights for effective change management pdf 1.pdf
Transcript: Selling digital books in 2024: Insights from industry leaders - T...

The publishing industry has been selling digital audiobooks and ebooks for over a decade and has found its groove. What’s changed? What has stayed the same? Where do we go from here? Join a group of leading sales peers from across the industry for a conversation about the lessons learned since the popularization of digital books, best practices, digital book supply chain management, and more.
Link to video recording: https://bnctechforum.ca/sessions/selling-digital-books-in-2024-insights-from-industry-leaders/
Presented by BookNet Canada on May 28, 2024, with support from the Department of Canadian Heritage.
Neuro-symbolic is not enough, we need neuro-*semantic*

Neuro-symbolic (NeSy) AI is on the rise. However, simply machine learning on just any symbolic structure is not sufficient to really harvest the gains of NeSy. These will only be gained when the symbolic structures have an actual semantics. I give an operational definition of semantics as “predictable inference”.
All of this illustrated with link prediction over knowledge graphs, but the argument is general.
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

Effective Application Security in Software Delivery lifecycle using Deployment Firewall and DBOM
The modern software delivery process (or the CI/CD process) includes many tools, distributed teams, open-source code, and cloud platforms. Constant focus on speed to release software to market, along with the traditional slow and manual security checks has caused gaps in continuous security as an important piece in the software supply chain. Today organizations feel more susceptible to external and internal cyber threats due to the vast attack surface in their applications supply chain and the lack of end-to-end governance and risk management.
The software team must secure its software delivery process to avoid vulnerability and security breaches. This needs to be achieved with existing tool chains and without extensive rework of the delivery processes. This talk will present strategies and techniques for providing visibility into the true risk of the existing vulnerabilities, preventing the introduction of security issues in the software, resolving vulnerabilities in production environments quickly, and capturing the deployment bill of materials (DBOM).
Speakers:
Bob Boule
Robert Boule is a technology enthusiast with PASSION for technology and making things work along with a knack for helping others understand how things work. He comes with around 20 years of solution engineering experience in application security, software continuous delivery, and SaaS platforms. He is known for his dynamic presentations in CI/CD and application security integrated in software delivery lifecycle.
Gopinath Rebala
Gopinath Rebala is the CTO of OpsMx, where he has overall responsibility for the machine learning and data processing architectures for Secure Software Delivery. Gopi also has a strong connection with our customers, leading design and architecture for strategic implementations. Gopi is a frequent speaker and well-known leader in continuous delivery and integrating security into software delivery.
AI for Every Business: Unlocking Your Product's Universal Potential by VP of ...

AI for Every Business: Unlocking Your Product's Universal Potential by VP of Product, Slack
Recently uploaded (20)
Encryption in Microsoft 365 - ExpertsLive Netherlands 2024

Encryption in Microsoft 365 - ExpertsLive Netherlands 2024
Mission to Decommission: Importance of Decommissioning Products to Increase E...

Mission to Decommission: Importance of Decommissioning Products to Increase E...
Accelerate your Kubernetes clusters with Varnish Caching

Accelerate your Kubernetes clusters with Varnish Caching
From Daily Decisions to Bottom Line: Connecting Product Work to Revenue by VP...

From Daily Decisions to Bottom Line: Connecting Product Work to Revenue by VP...
Elevating Tactical DDD Patterns Through Object Calisthenics

Elevating Tactical DDD Patterns Through Object Calisthenics
When stars align: studies in data quality, knowledge graphs, and machine lear...

When stars align: studies in data quality, knowledge graphs, and machine lear...
Generating a custom Ruby SDK for your web service or Rails API using Smithy

Generating a custom Ruby SDK for your web service or Rails API using Smithy
De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovati...

De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovati...
Key Trends Shaping the Future of Infrastructure.pdf

Key Trends Shaping the Future of Infrastructure.pdf
Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024

Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024
FIDO Alliance Osaka Seminar: FIDO Security Aspects.pdf

FIDO Alliance Osaka Seminar: FIDO Security Aspects.pdf
Designing Great Products: The Power of Design and Leadership by Chief Designe...

Designing Great Products: The Power of Design and Leadership by Chief Designe...
FIDO Alliance Osaka Seminar: The WebAuthn API and Discoverable Credentials.pdf

FIDO Alliance Osaka Seminar: The WebAuthn API and Discoverable Credentials.pdf
The Art of the Pitch: WordPress Relationships and Sales

The Art of the Pitch: WordPress Relationships and Sales
Leading Change strategies and insights for effective change management pdf 1.pdf

Leading Change strategies and insights for effective change management pdf 1.pdf
Transcript: Selling digital books in 2024: Insights from industry leaders - T...

Transcript: Selling digital books in 2024: Insights from industry leaders - T...
Neuro-symbolic is not enough, we need neuro-*semantic*

Neuro-symbolic is not enough, we need neuro-*semantic*
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...
AI for Every Business: Unlocking Your Product's Universal Potential by VP of ...

AI for Every Business: Unlocking Your Product's Universal Potential by VP of ...
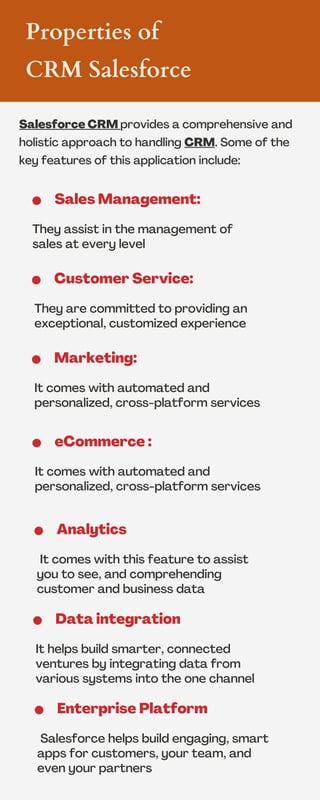
Properties of Salesforce CRM.pdf
- 1. Salesforce CRM provides a comprehensive and holistic approach to handling CRM. Some of the key features of this application include: Sales Management: They assist in the management of sales at every level Properties of CRM Salesforce Customer Service: They are committed to providing an exceptional, customized experience Marketing: It comes with automated and personalized, cross-platform services eCommerce : It comes with automated and personalized, cross-platform services Analytics It comes with this feature to assist you to see, and comprehending customer and business data Data integration It helps build smarter, connected ventures by integrating data from various systems into the one channel Enterprise Platform Salesforce helps build engaging, smart apps for customers, your team, and even your partners
