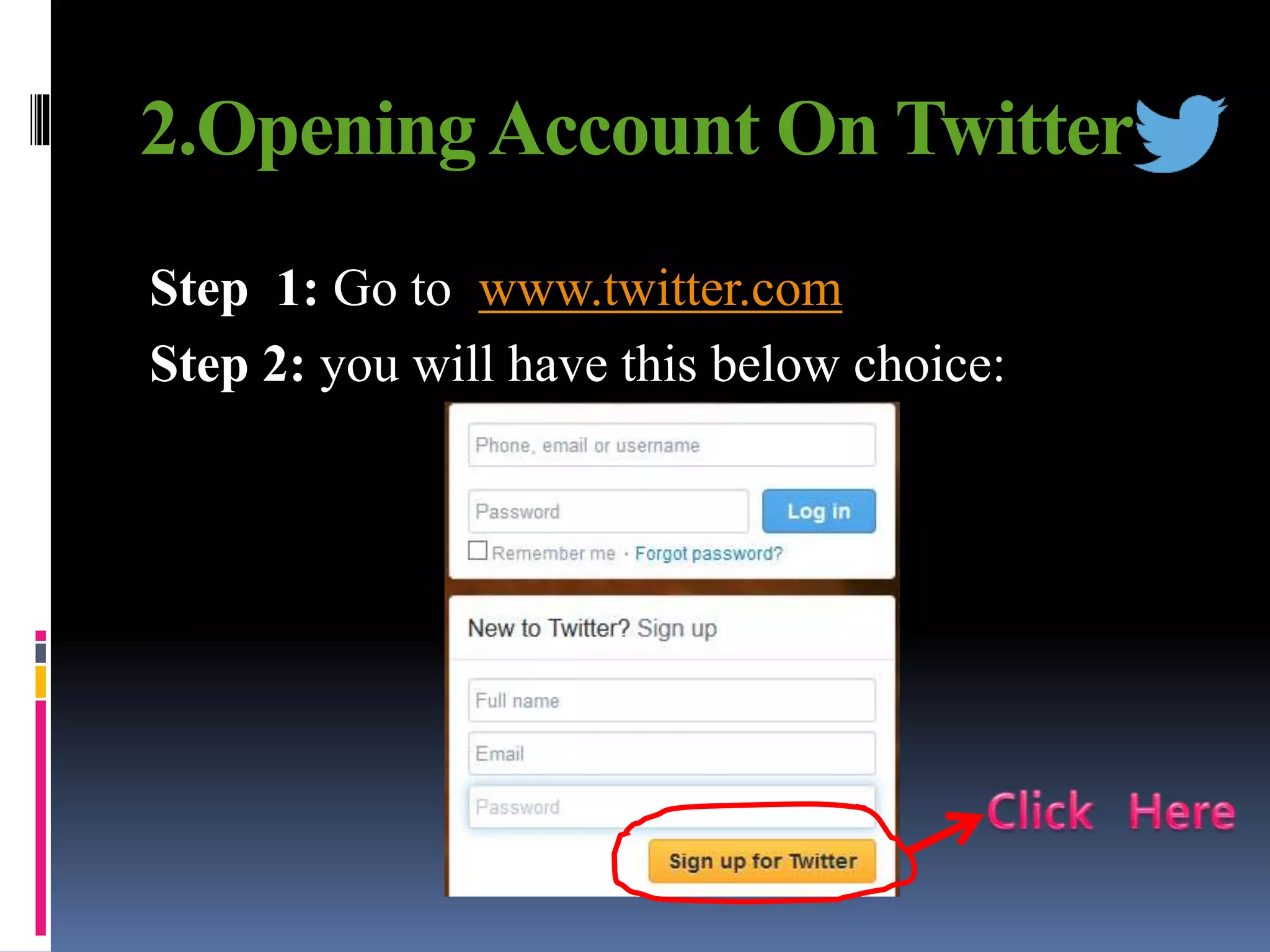
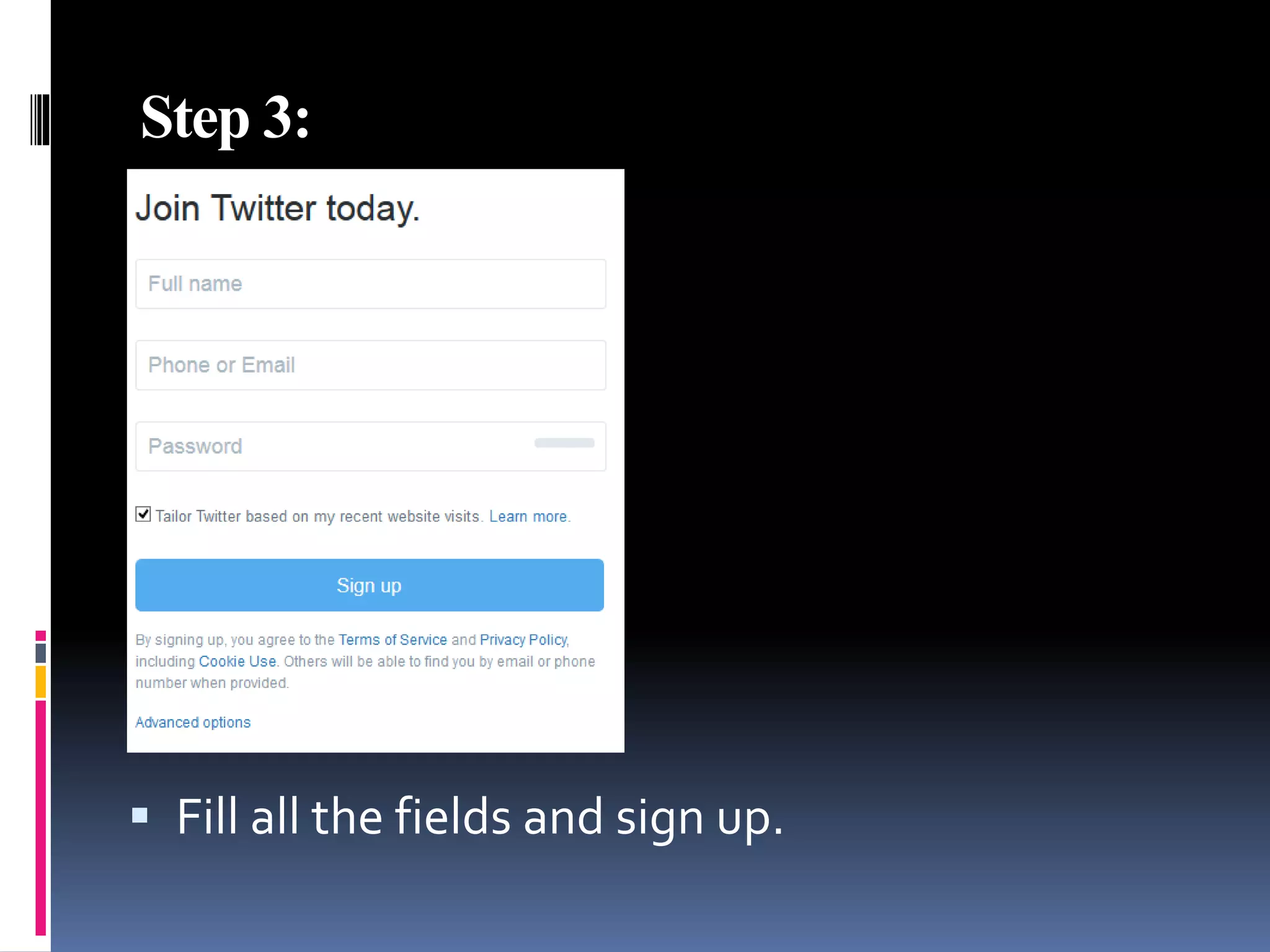
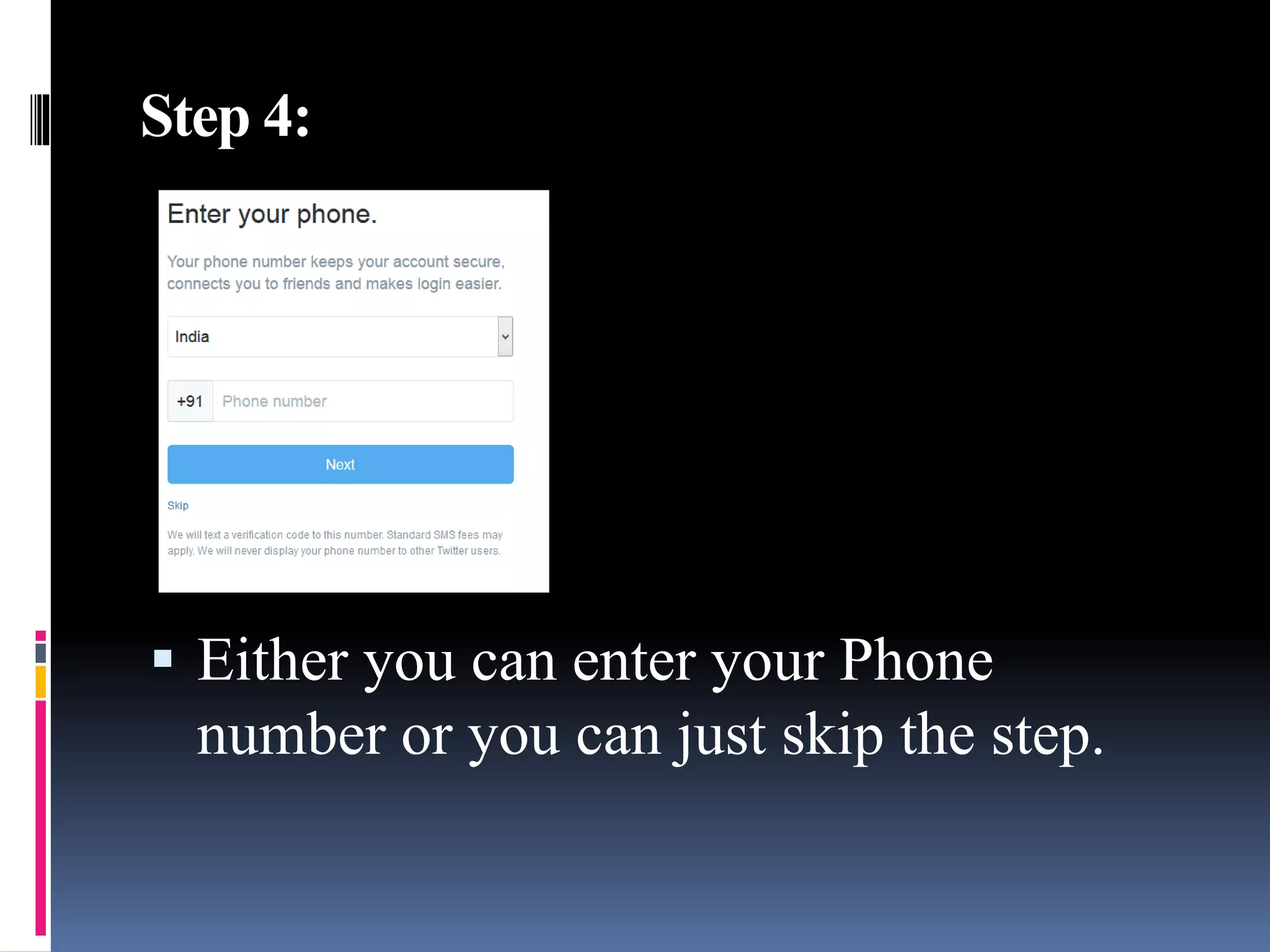
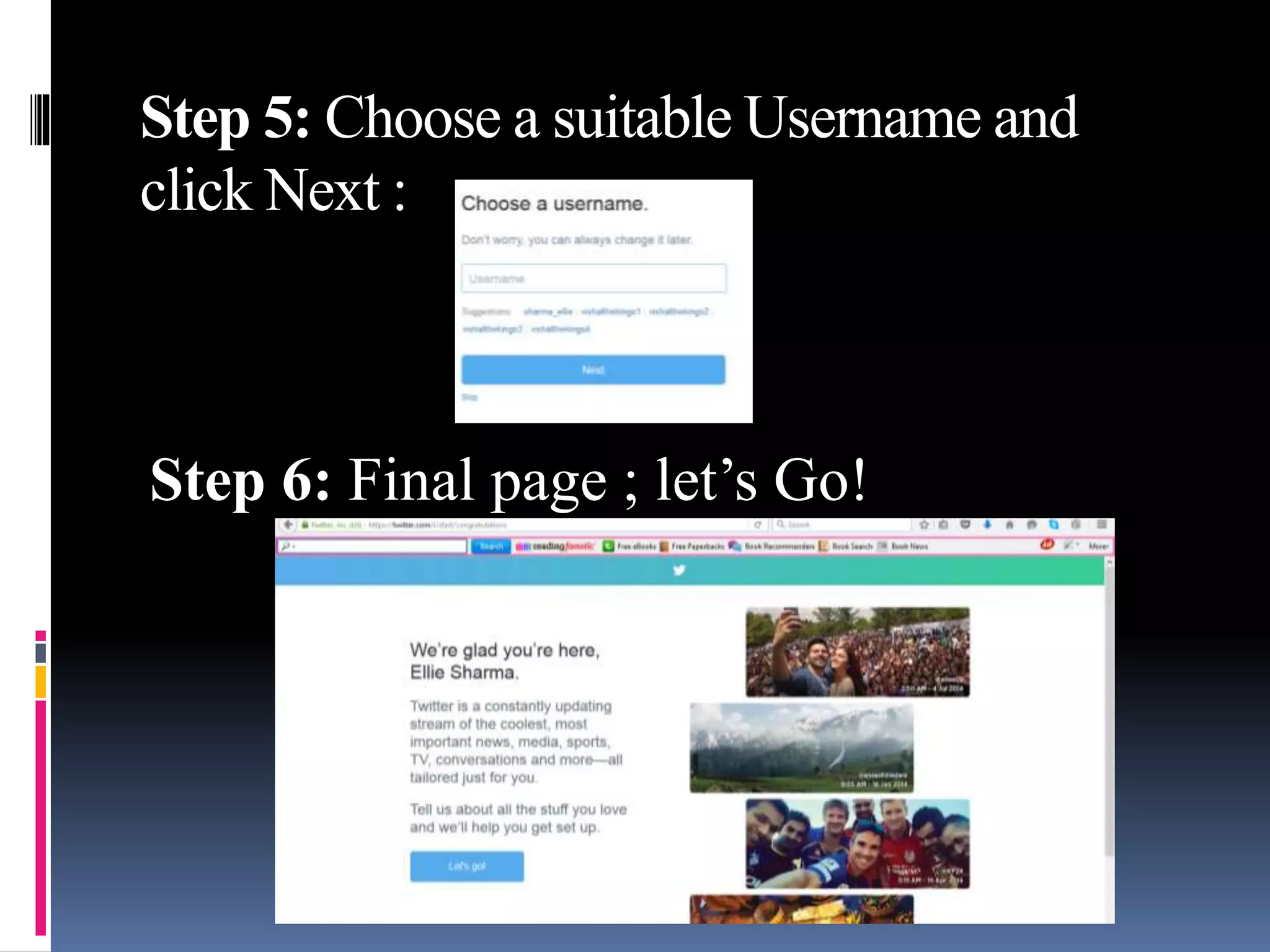
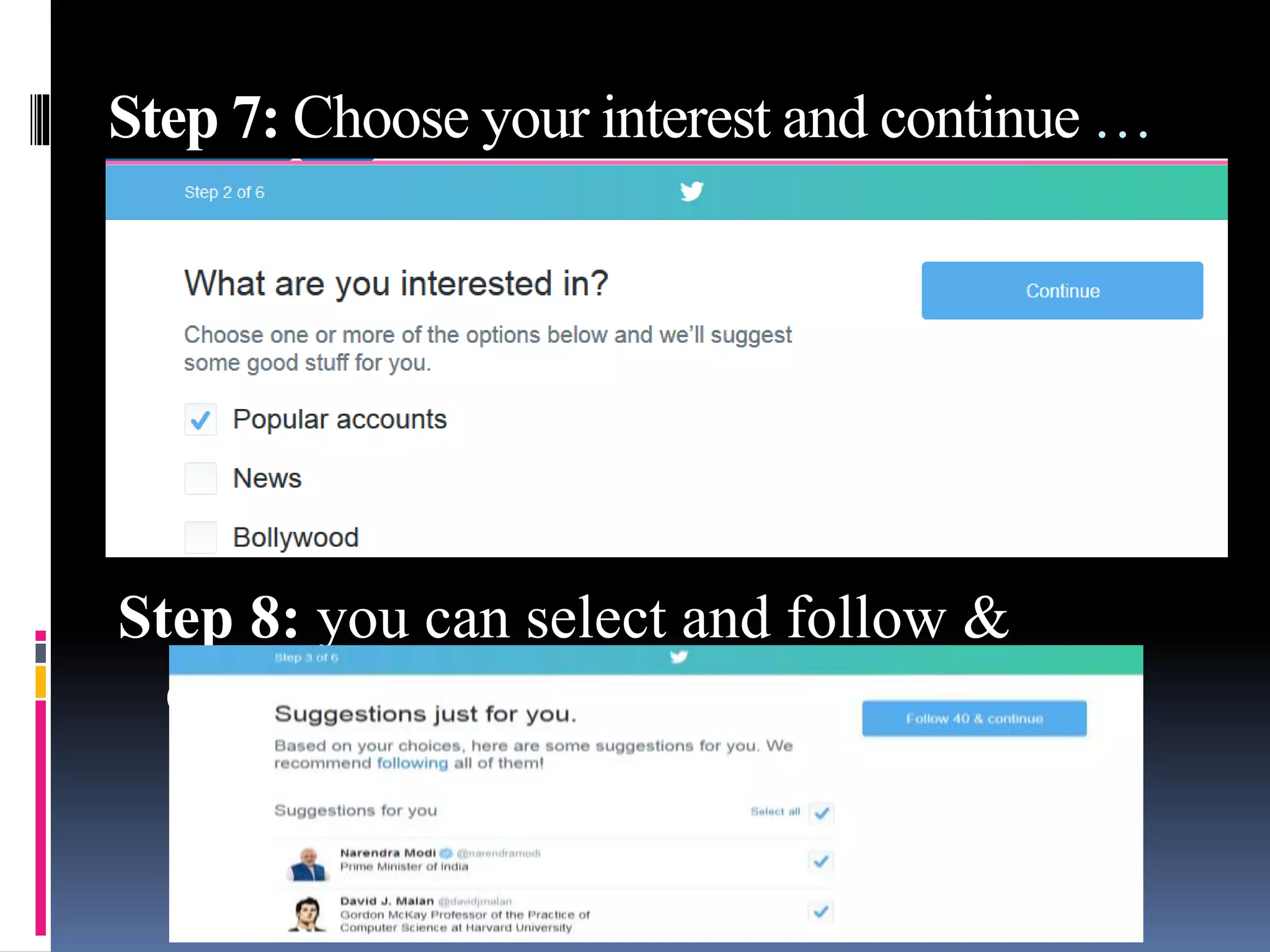
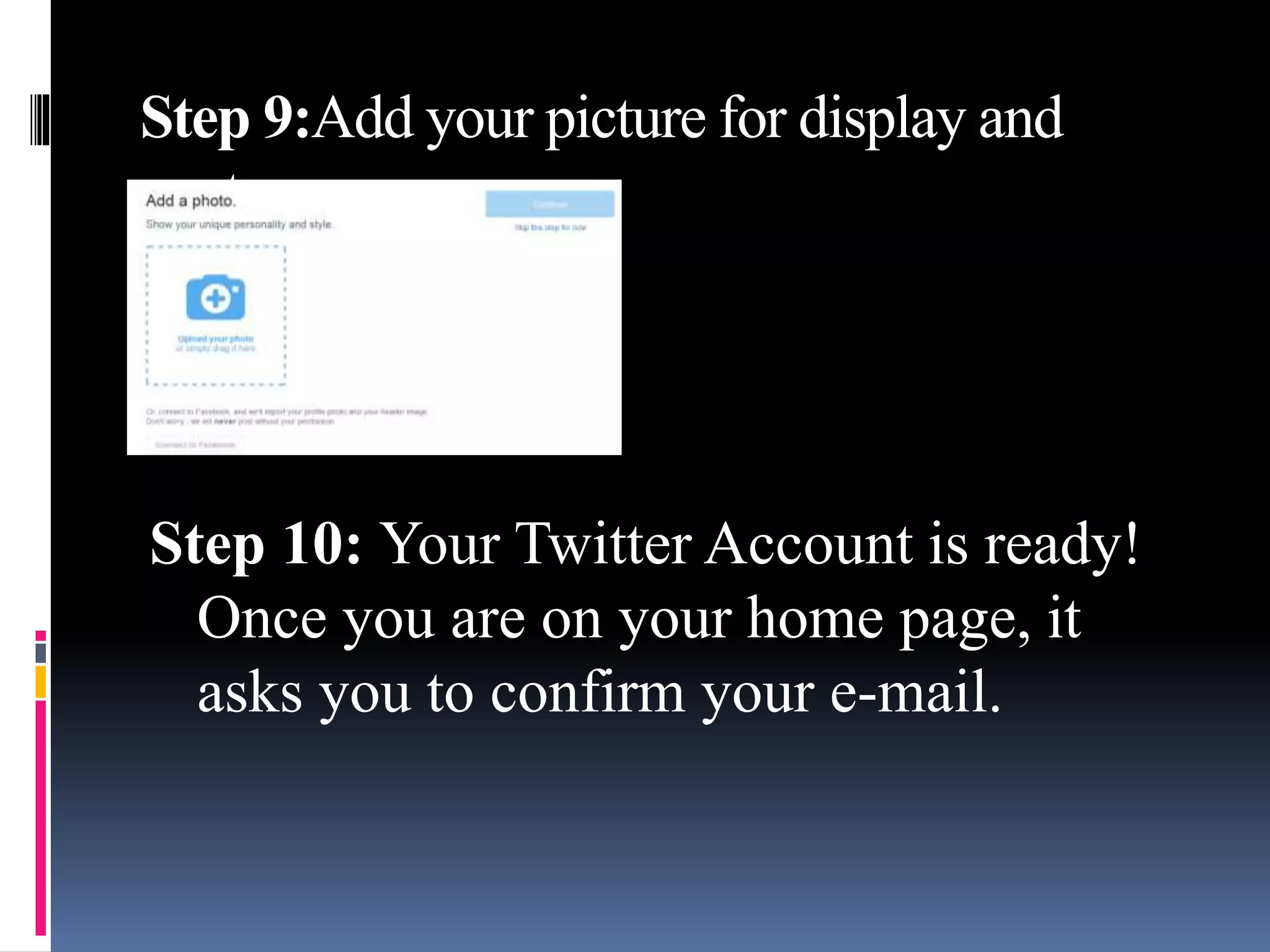
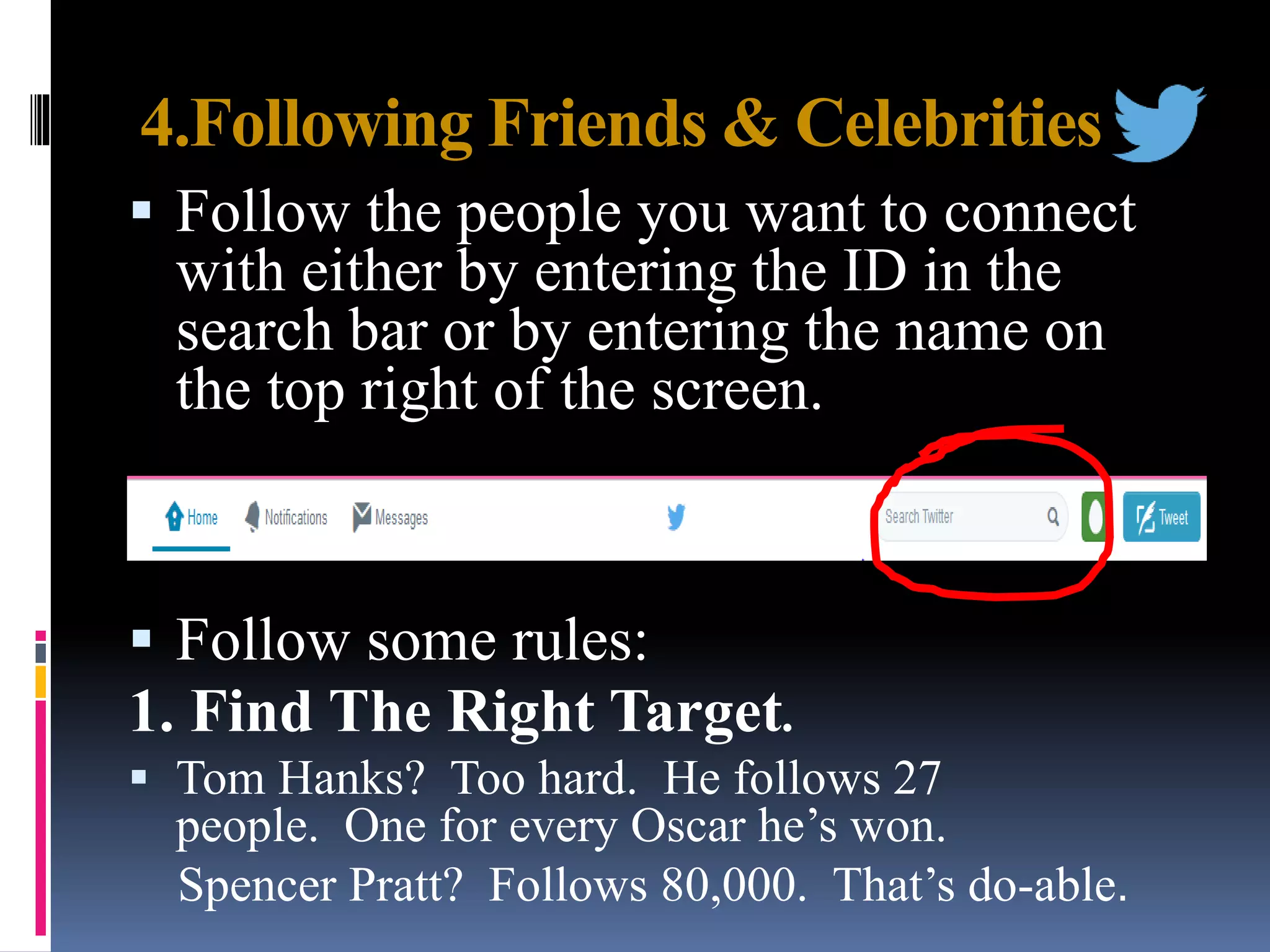
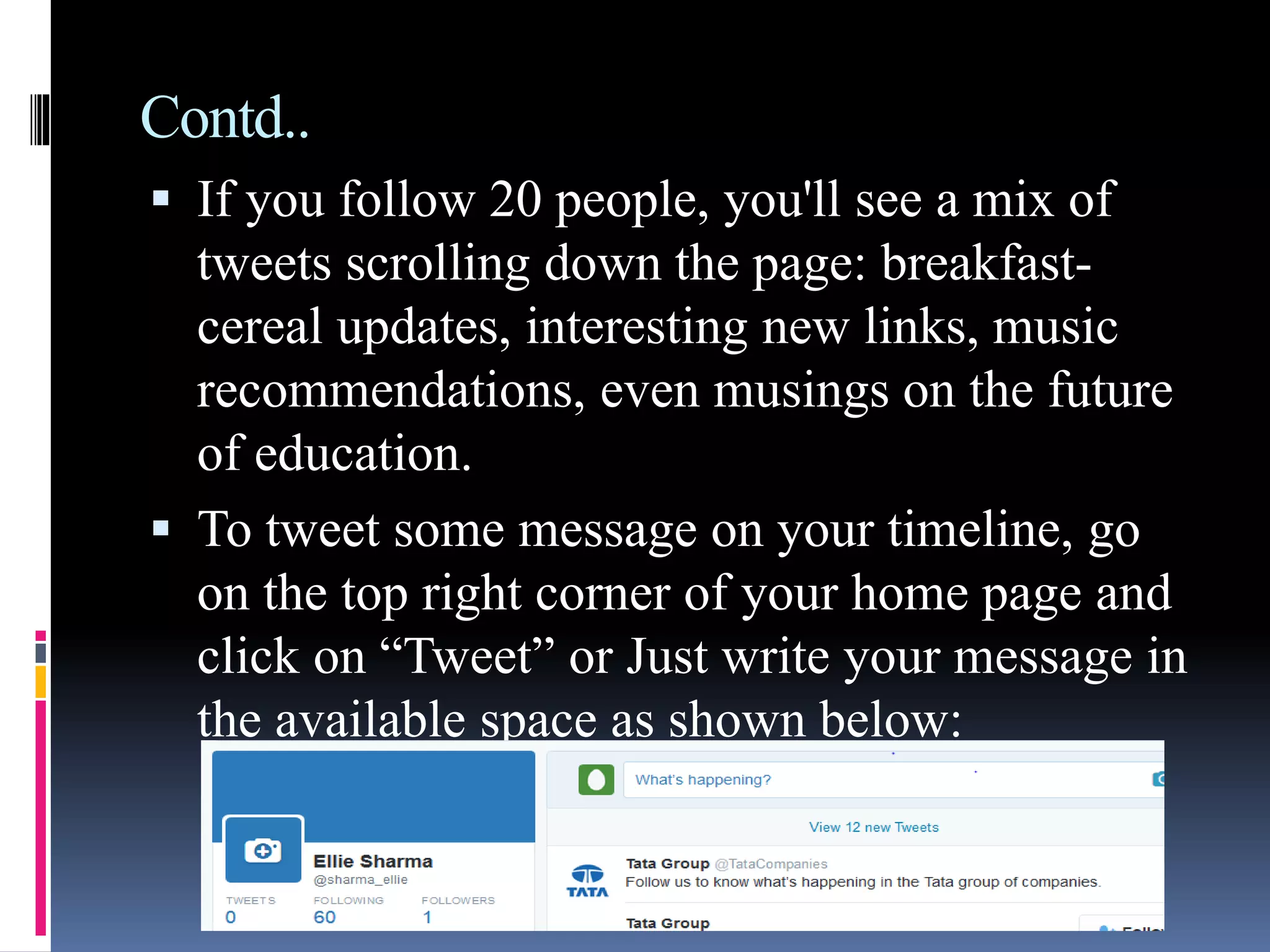
Twitter is a social media platform that allows users to post and read short messages known as tweets. To create a Twitter account, a user provides basic information and chooses a username. They can then follow other accounts and post tweets that may include hashtags to help them be discovered and join relevant conversations. Users can also connect their Twitter account to Facebook, which allows tweets to automatically be posted to their Facebook profile wall.