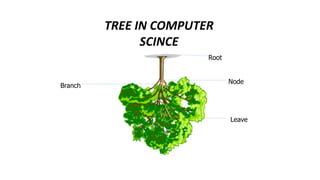
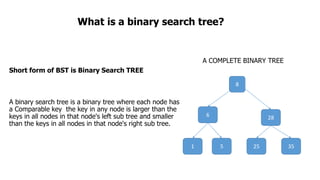
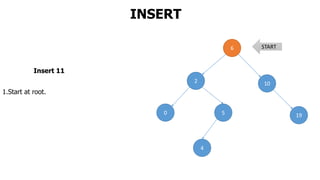
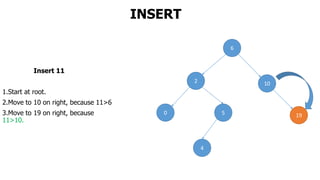
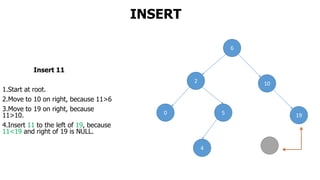
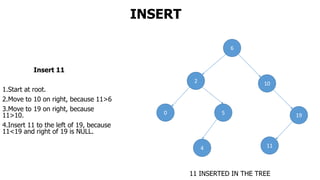
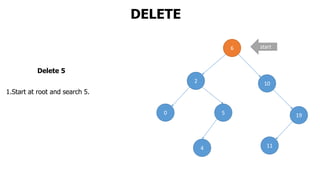
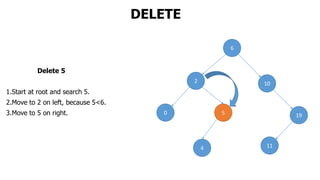
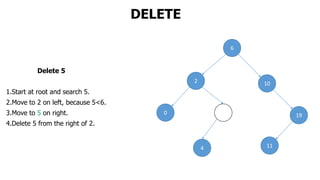
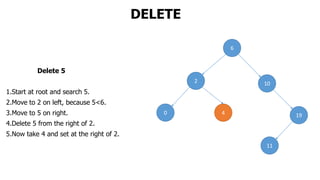
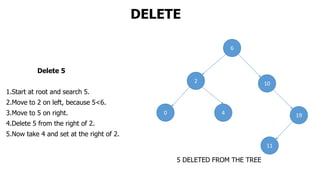
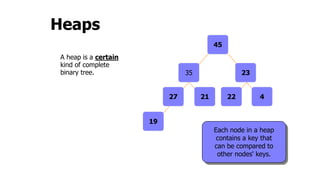
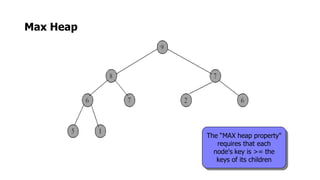
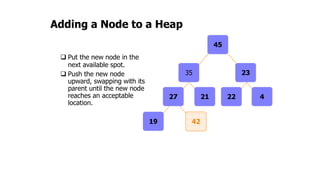
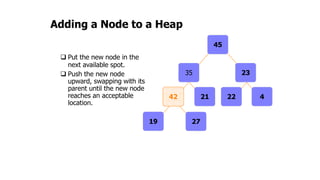
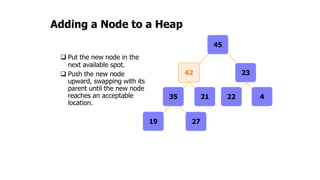
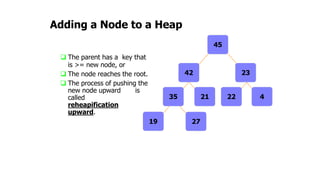
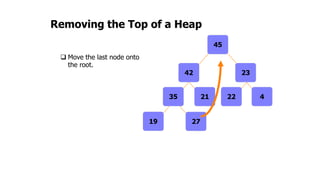
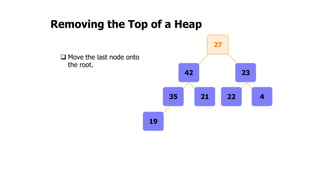
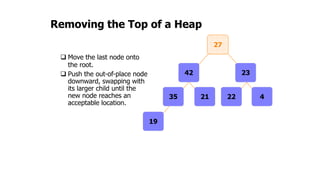
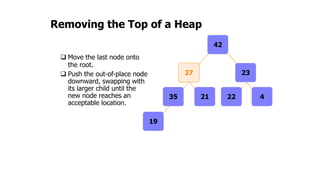
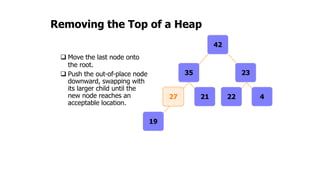
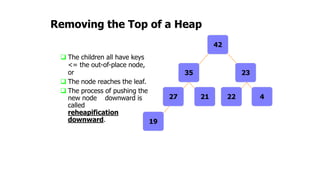
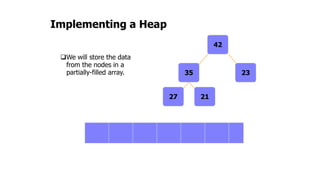
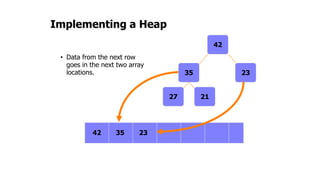
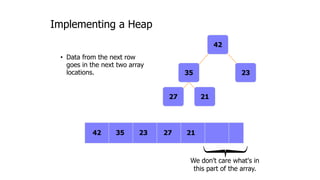
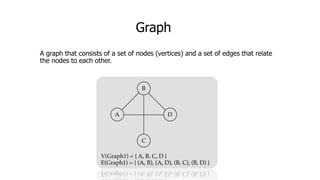
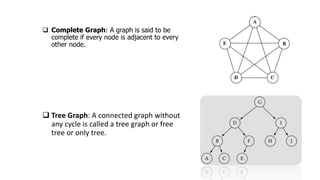
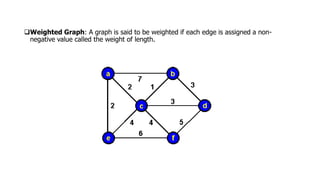
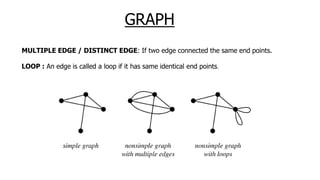
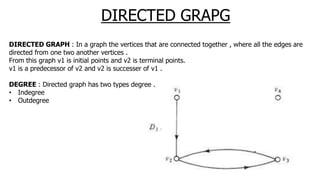
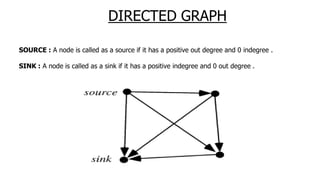
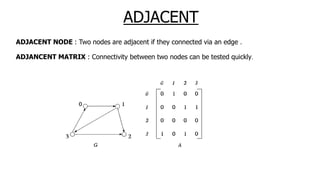
The document provides an overview of various data structures in computer science, including trees, binary search trees, heaps, and graphs. It explains key concepts such as node types, tree operations, heap properties, and graph characteristics like connected and complete graphs. Additionally, it covers insertion and deletion operations for binary search trees and heaps, as well as various representations of graphs.