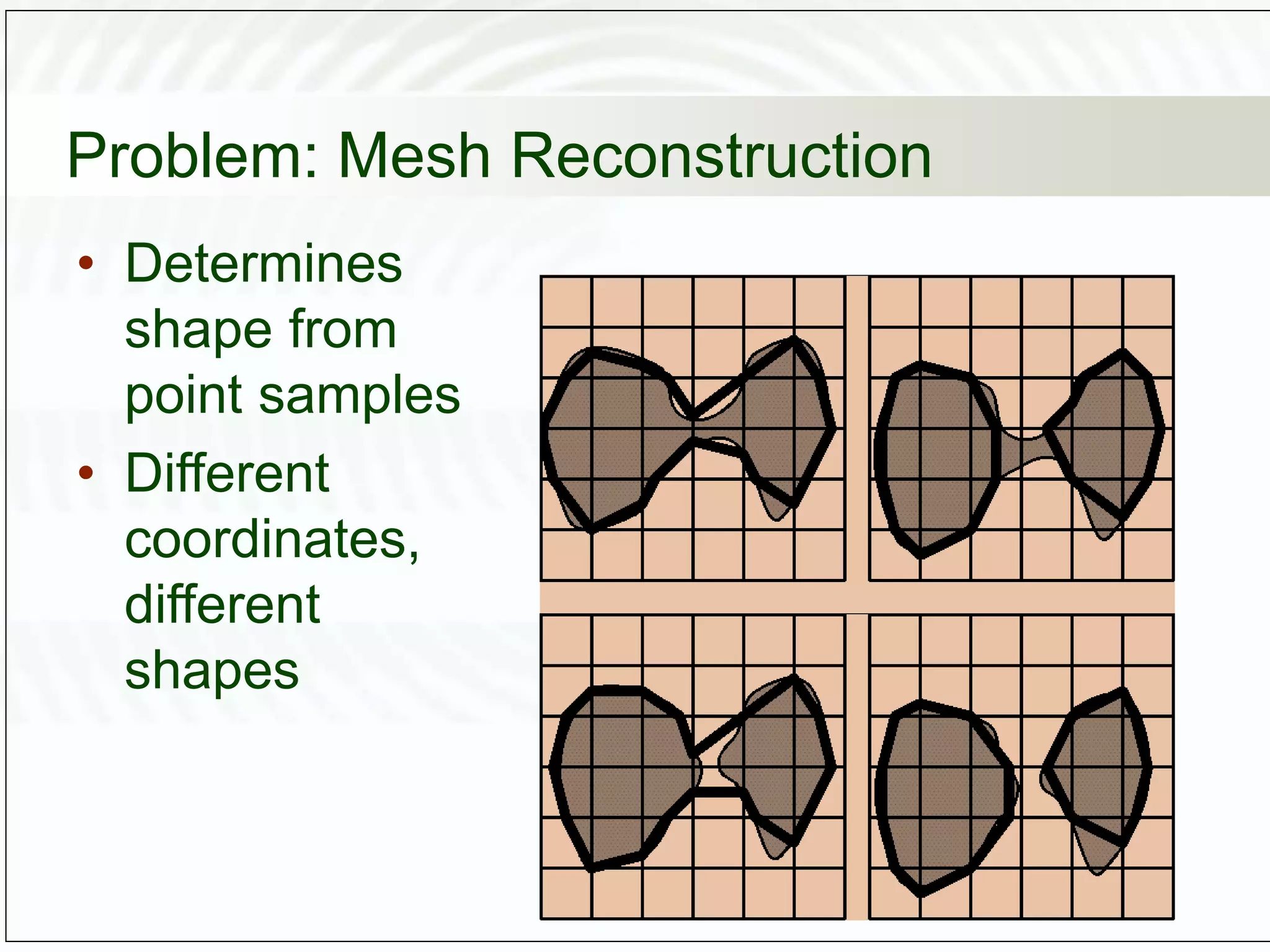
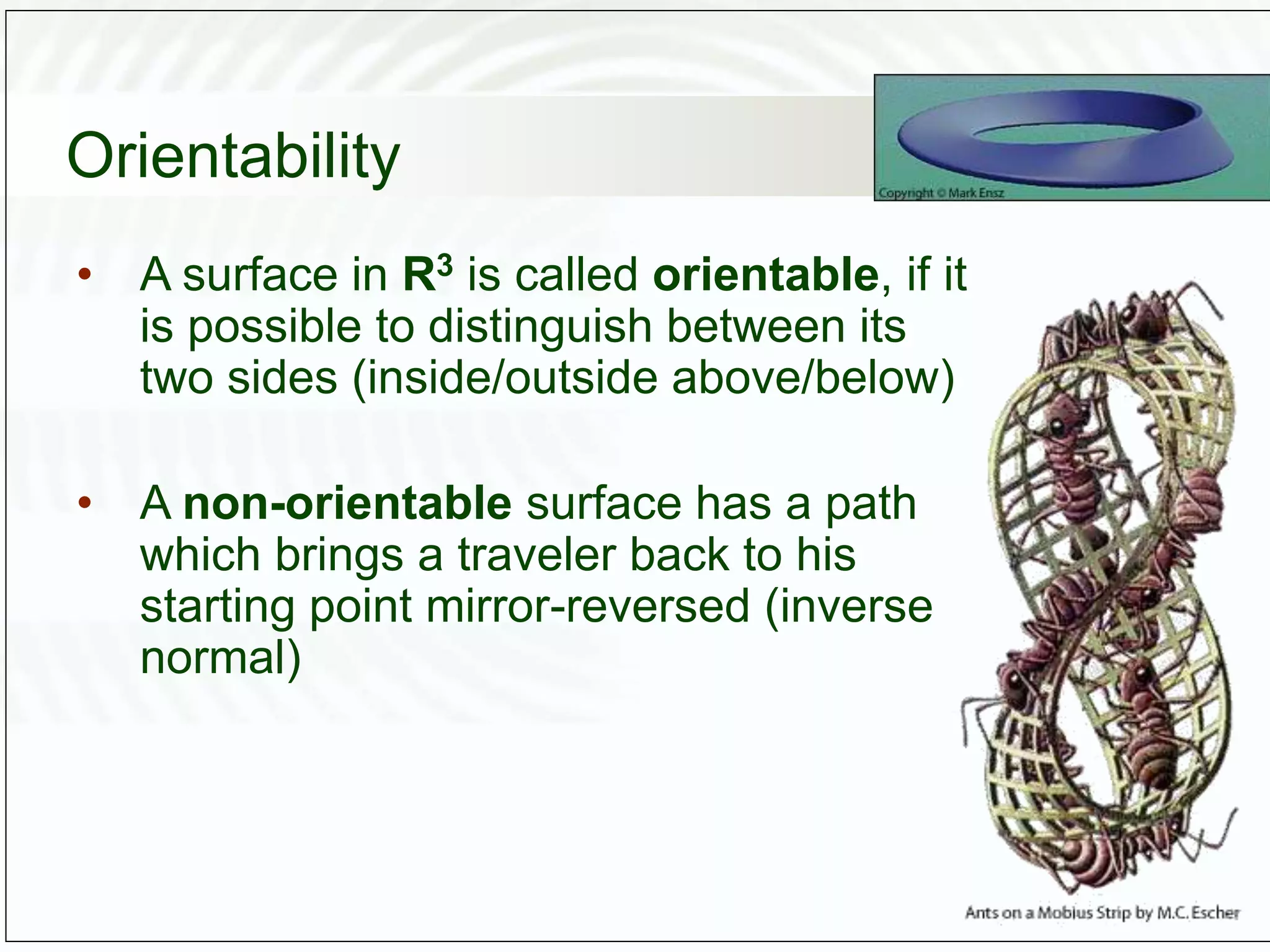
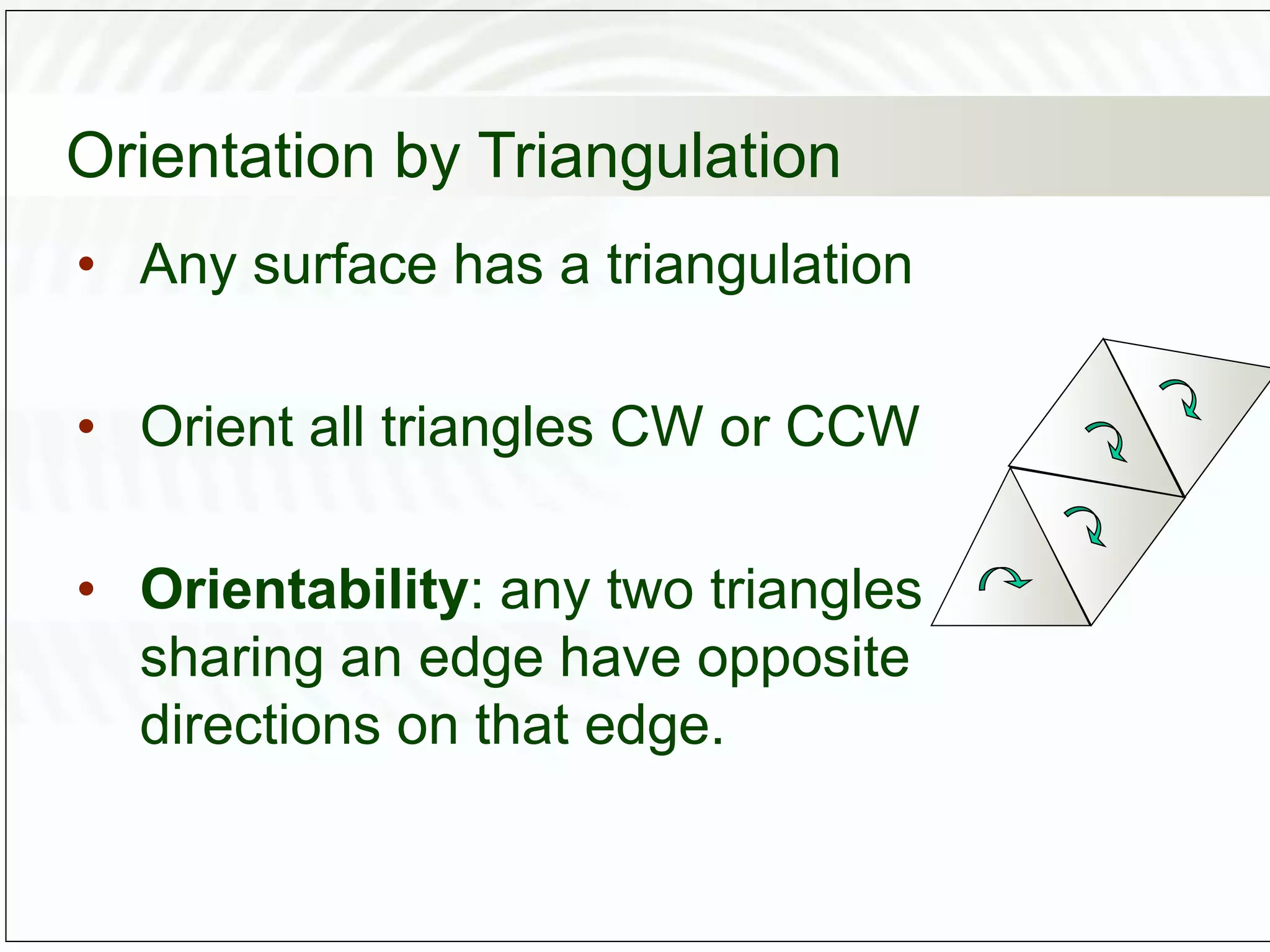
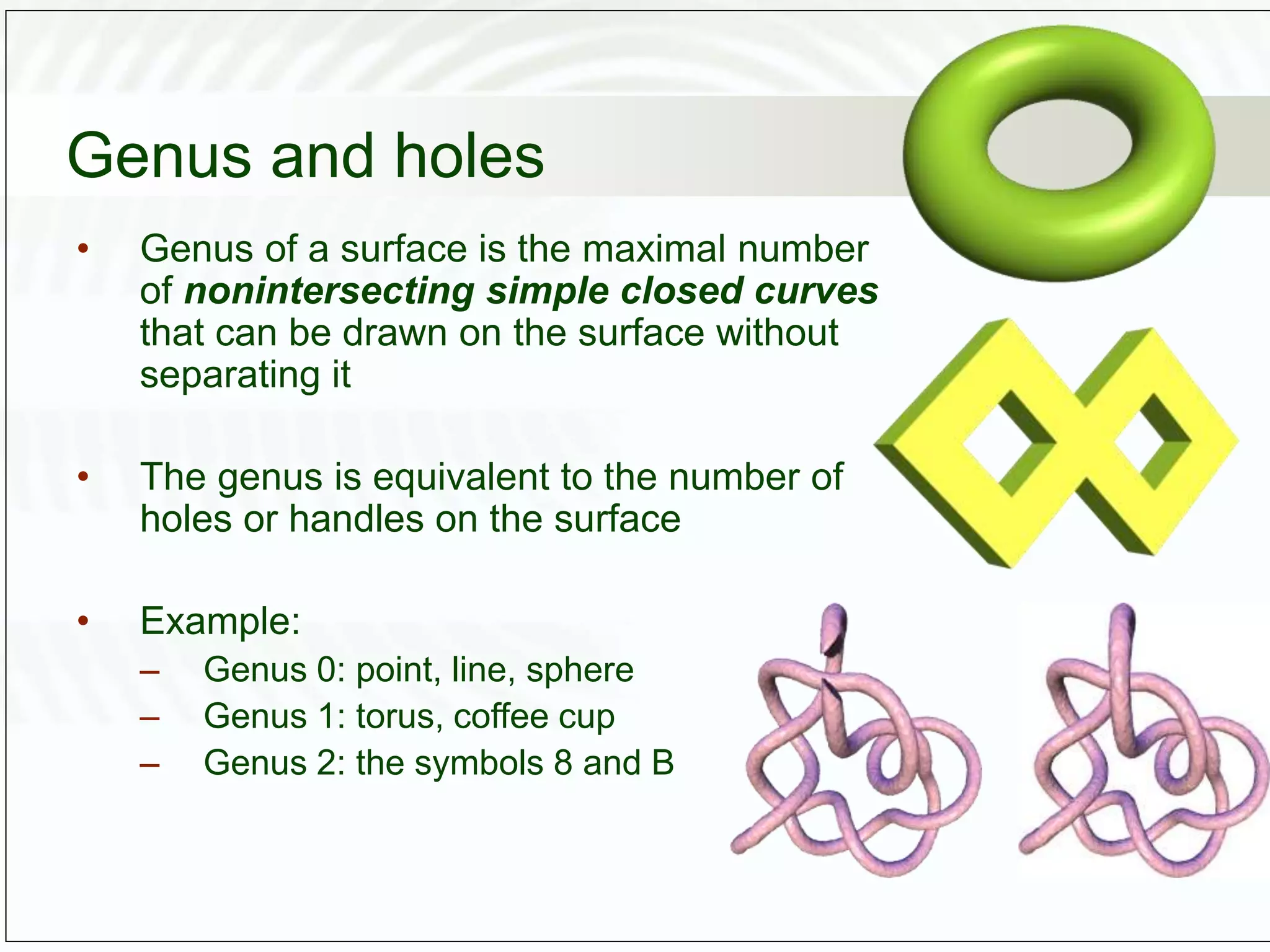
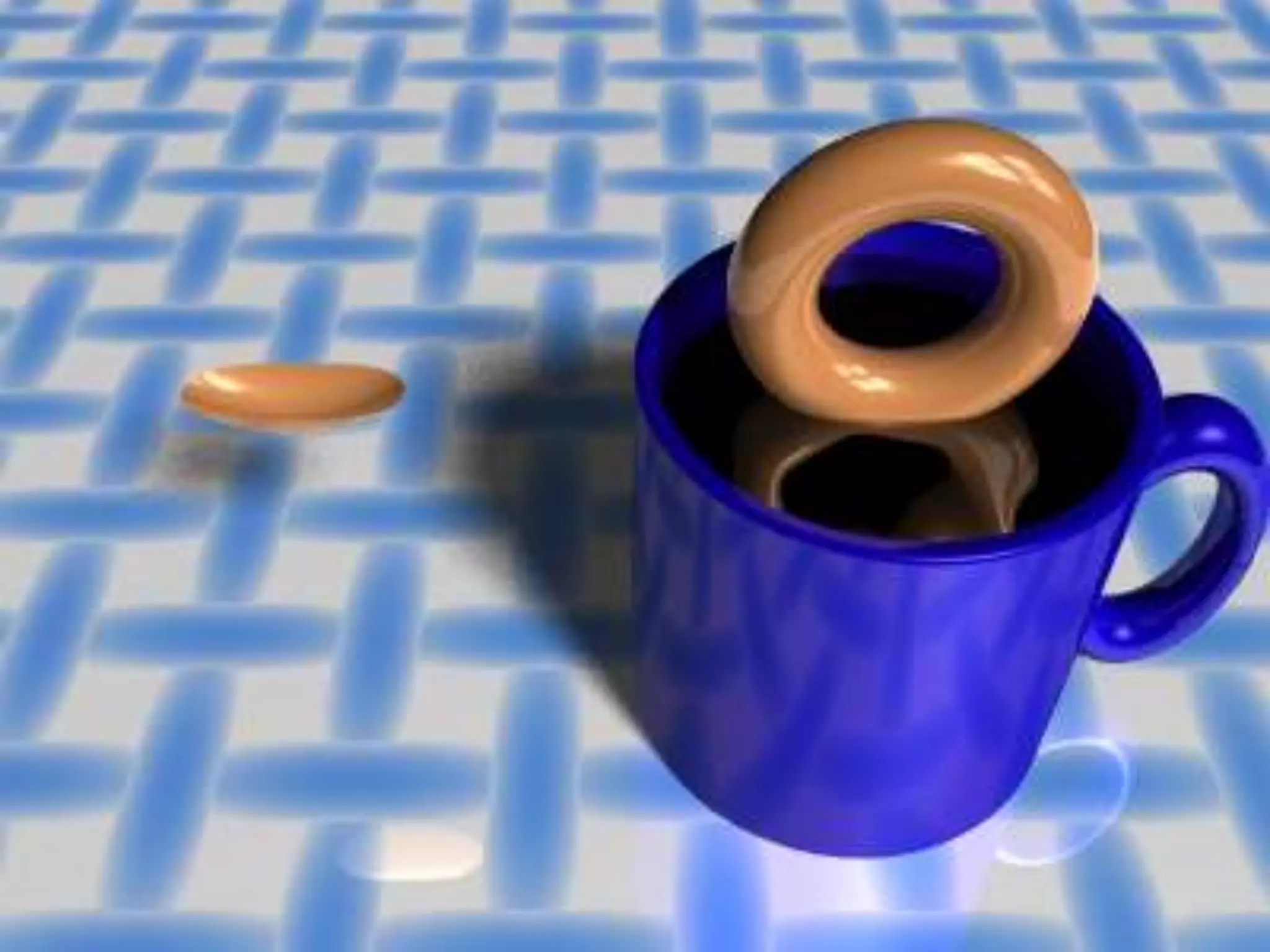
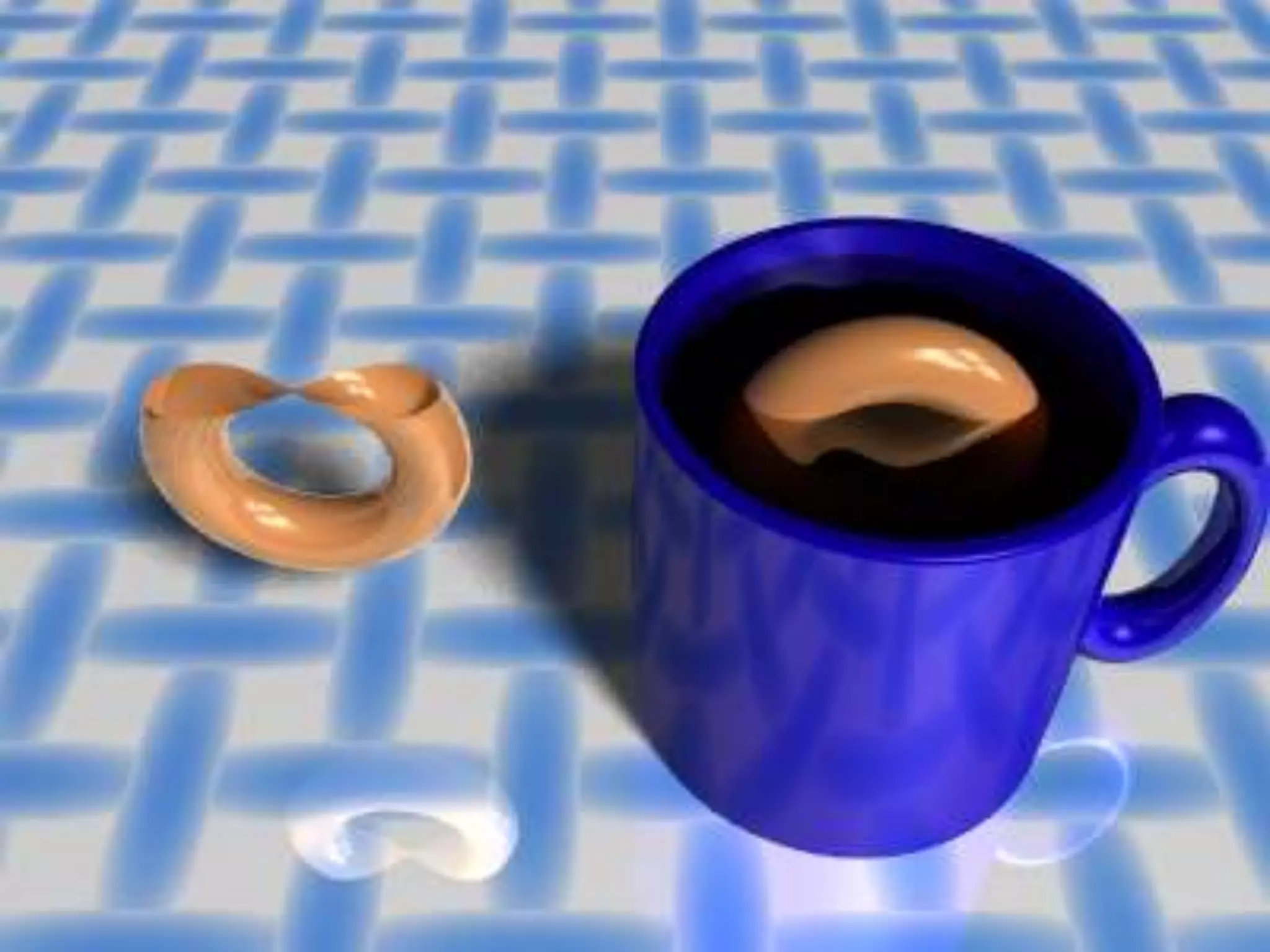
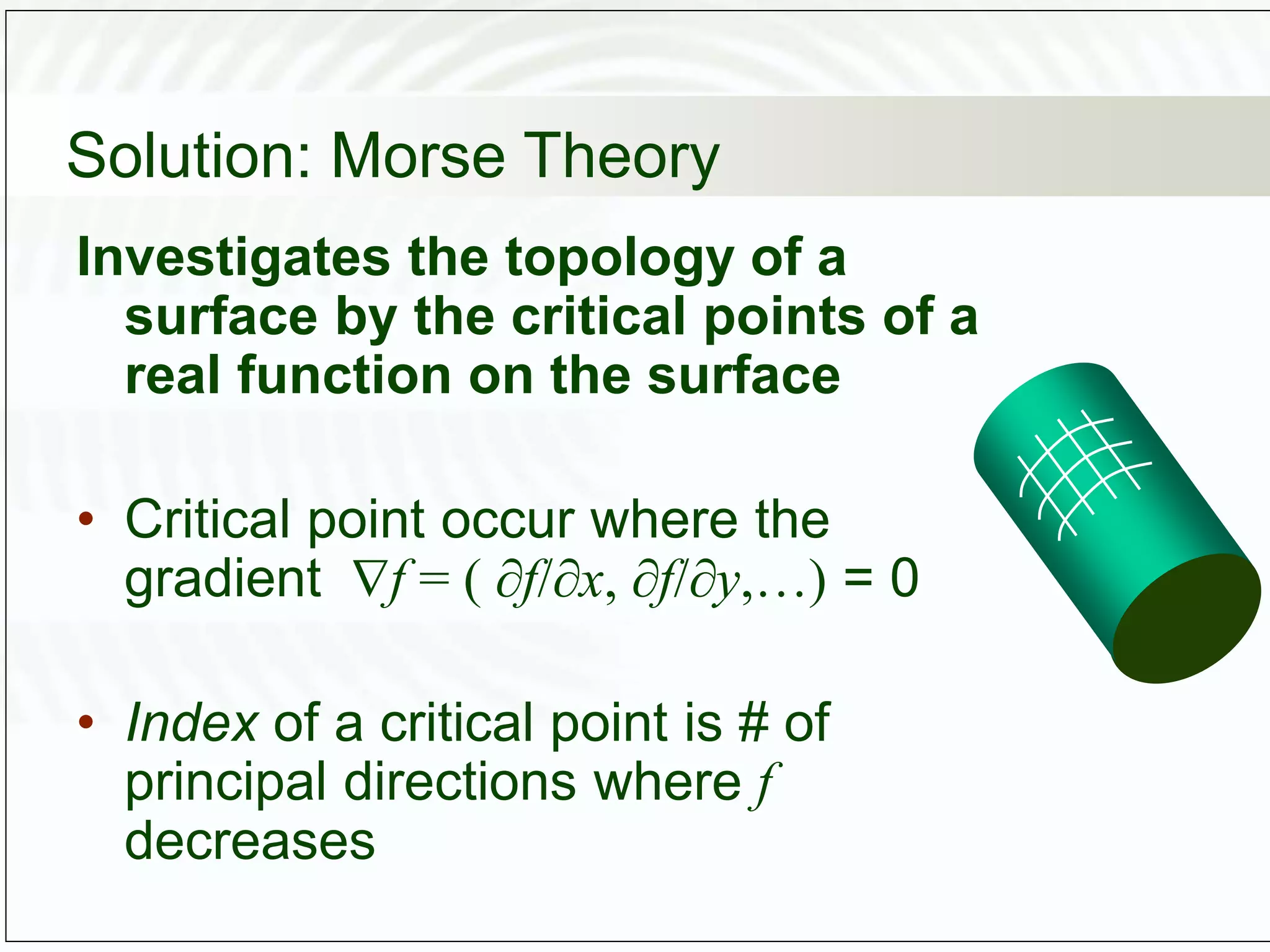
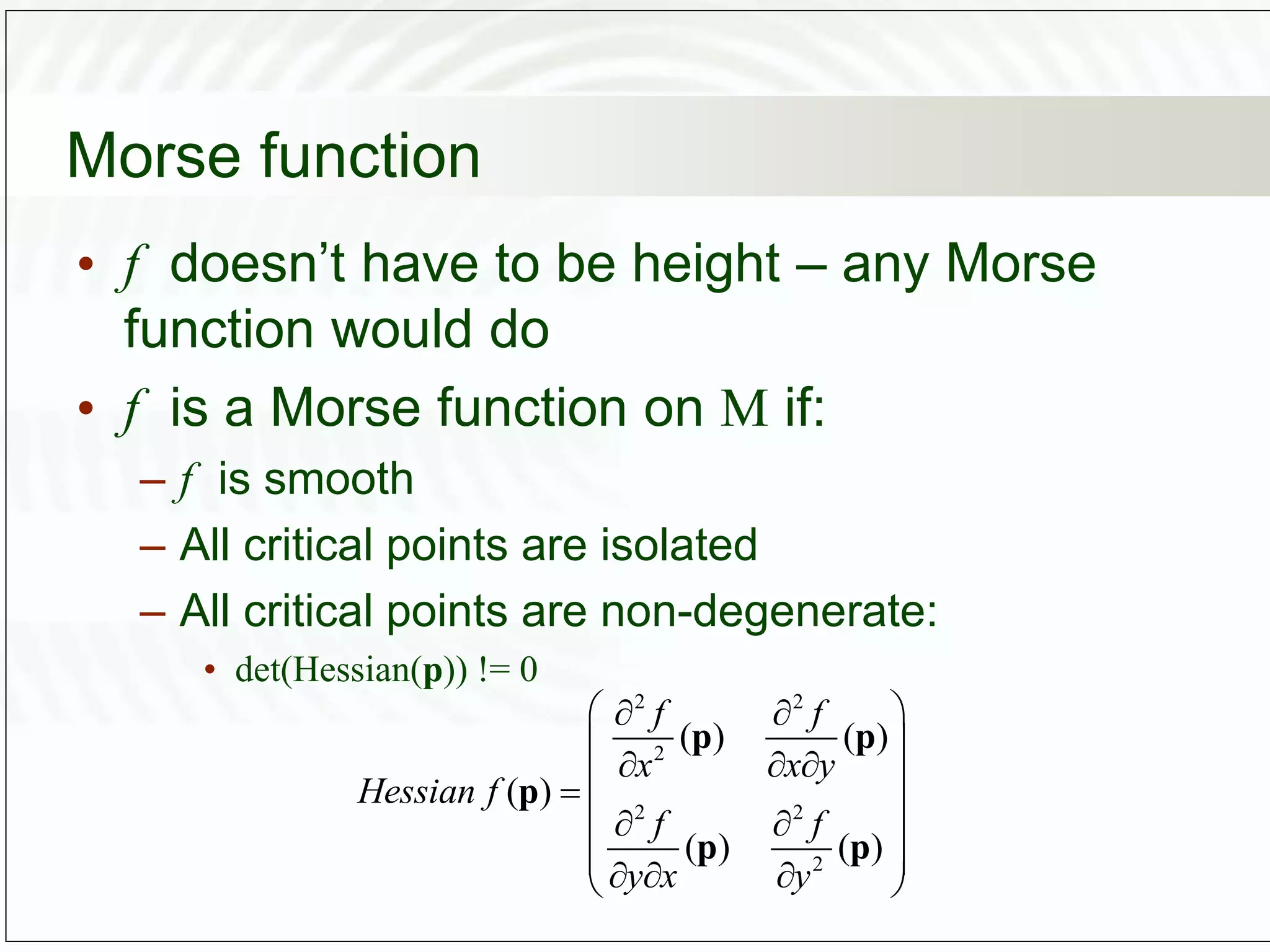
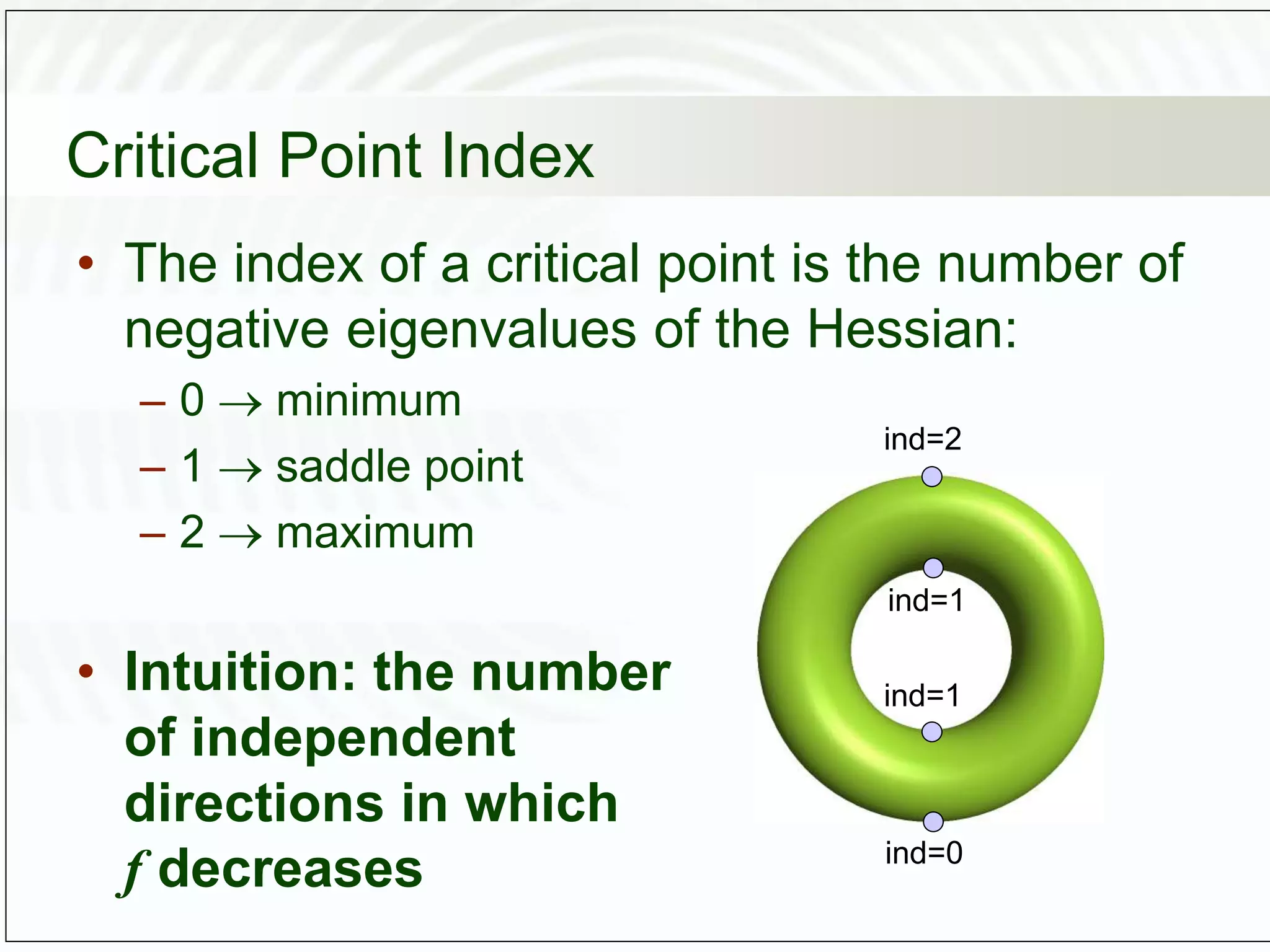
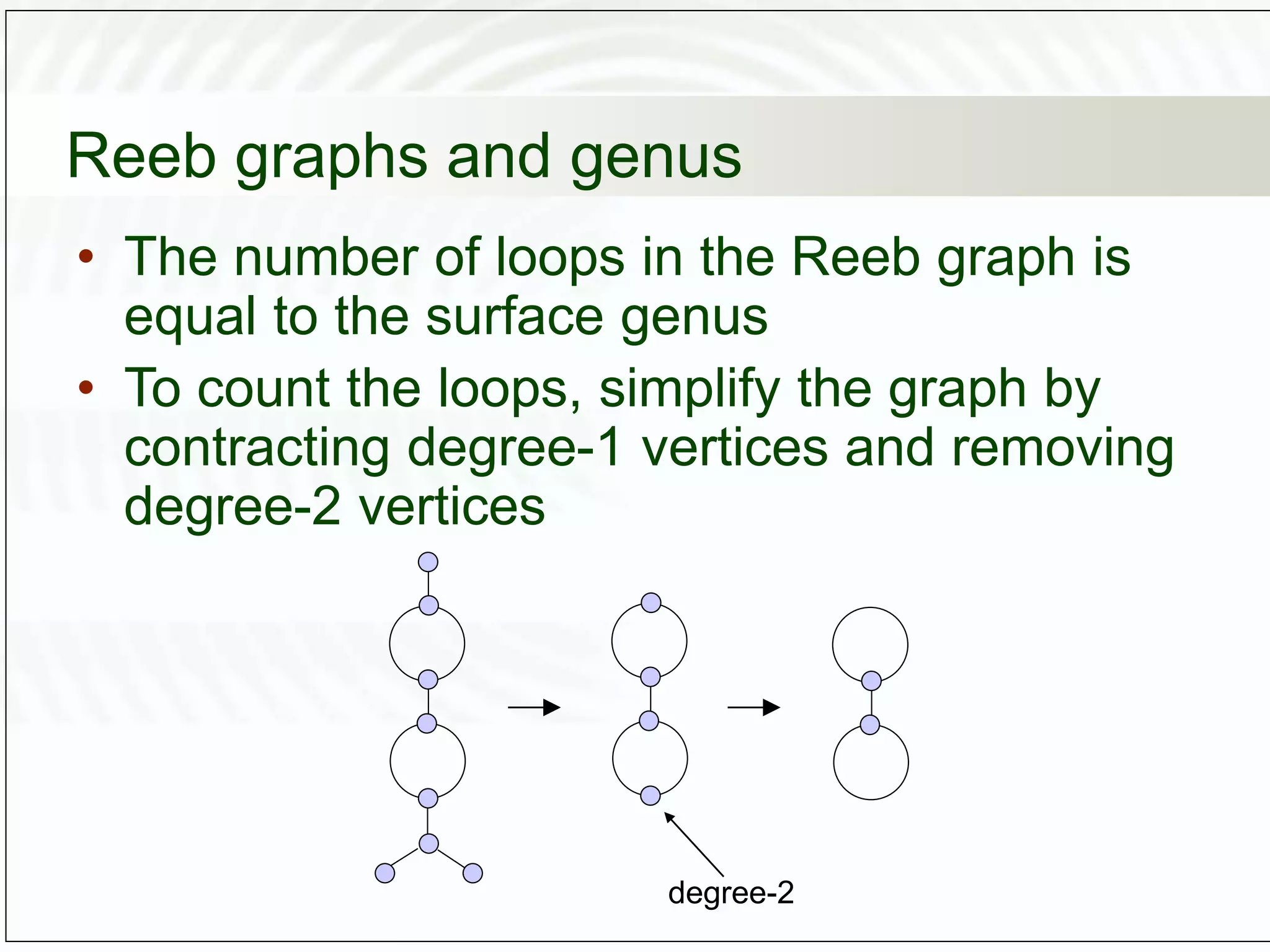
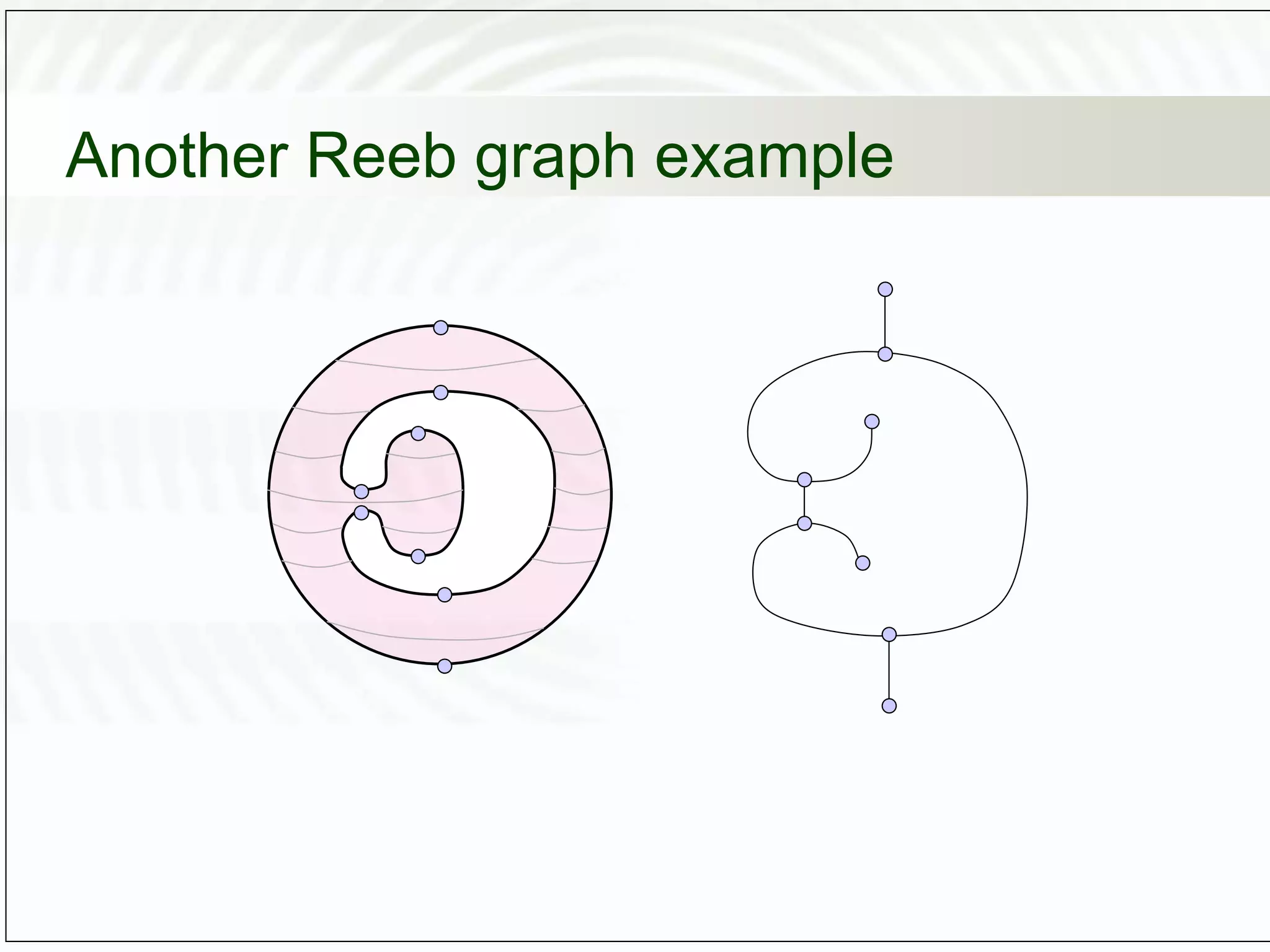
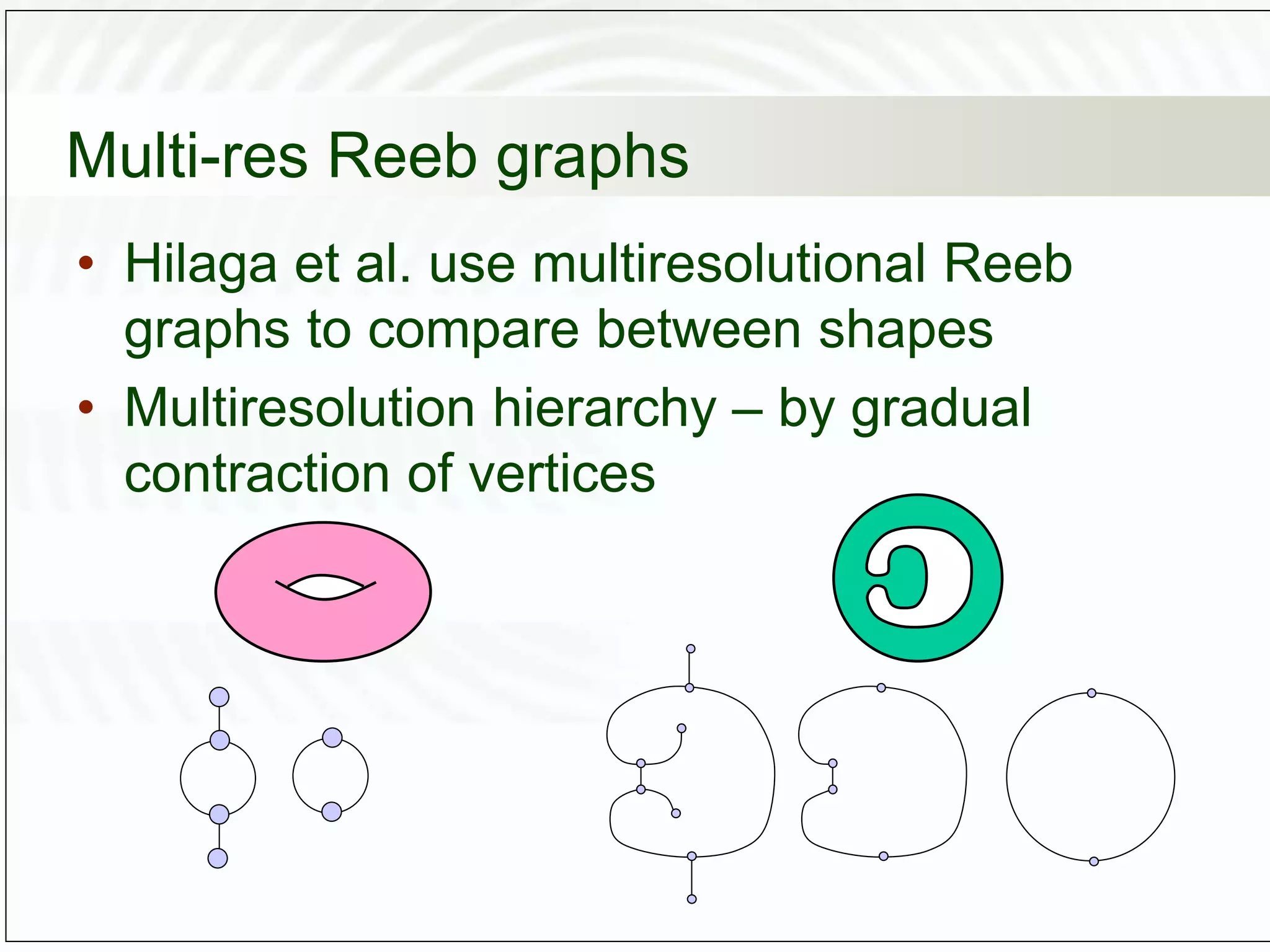
This document discusses computational topology and its applications in computer graphics. It introduces key concepts in topology such as homeomorphisms, genus, orientability, and Morse theory. Topology studies properties of shapes that are preserved under continuous deformations. Morse theory analyzes the topology of a surface by investigating the critical points of functions defined on the surface, such as the height function. Reeb graphs provide a way to schematically represent a Morse function and reveal topological properties of the shape like its genus. Computational topology techniques can be used for applications like shape matching, surface reconstruction from point clouds, and mesh partitioning.












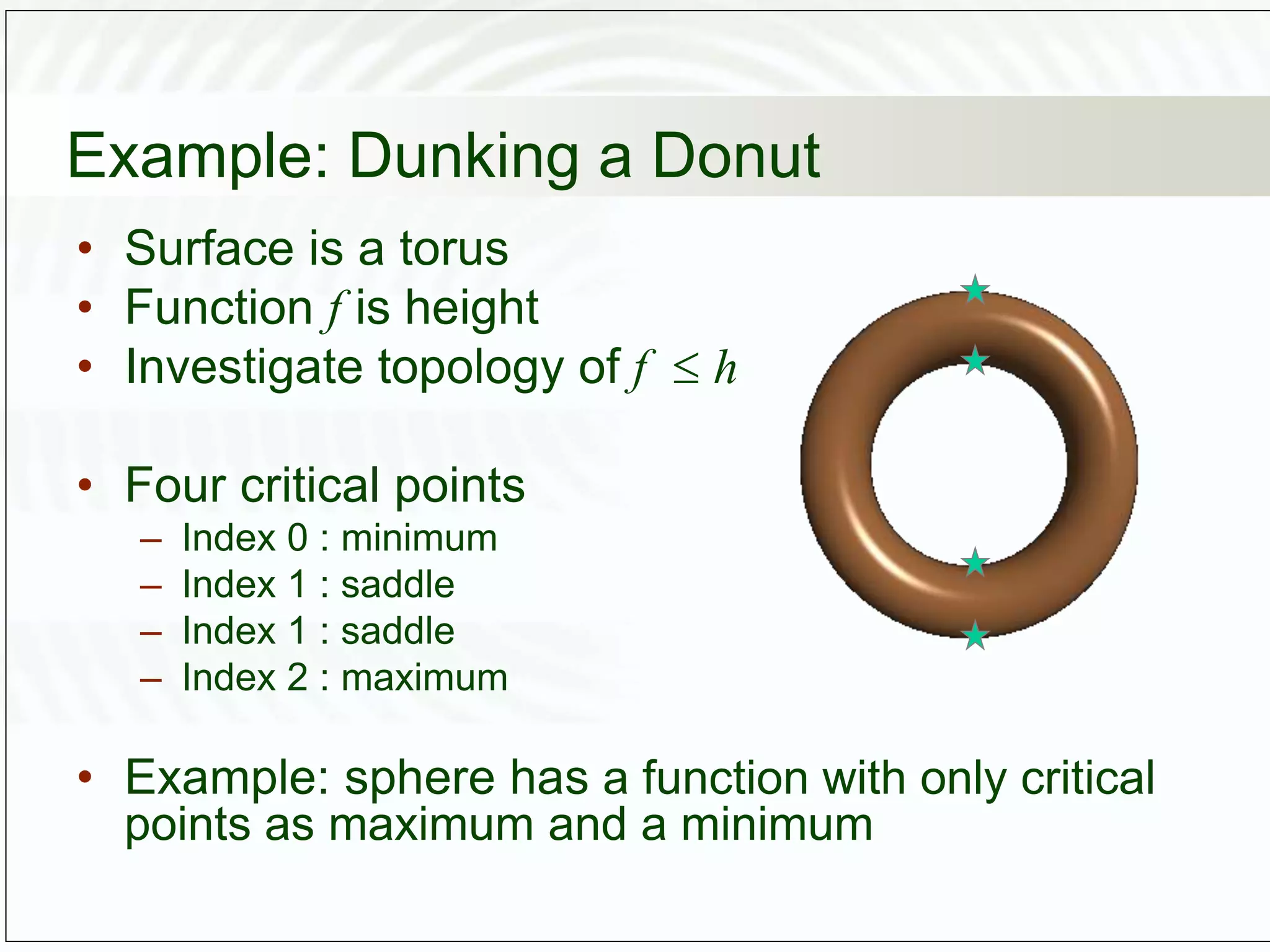

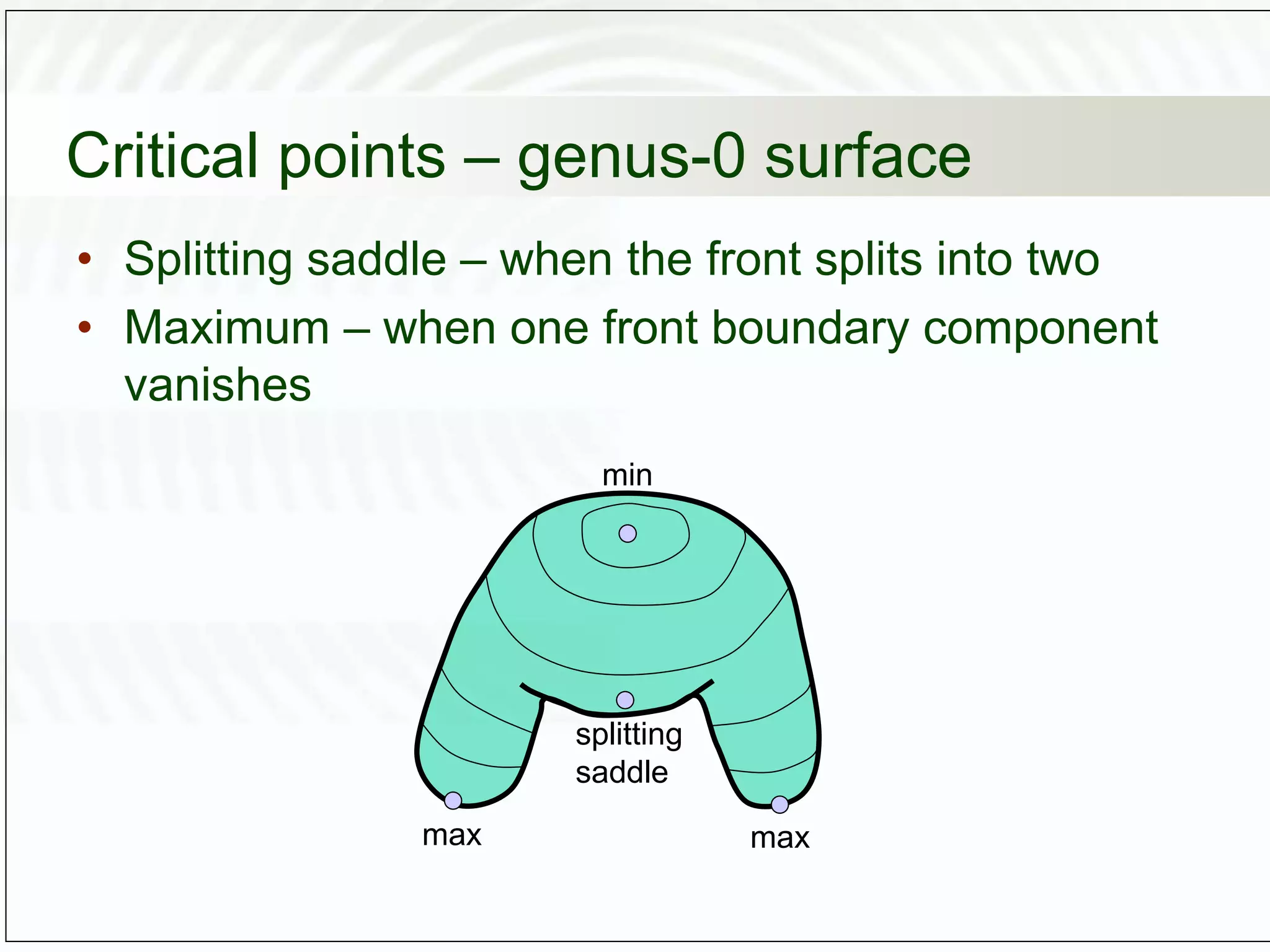
![If sweep doesn’t pass critical point
[Milnor 1963]
• Denote Ma
= {p M | f(p) a} (the sweep
region up to value a of f )
• Suppose f 1
[a, b] is compact and doesn’t
contain critical points of f. Then Ma
is
homeomorphic to Mb
.](https://image.slidesharecdn.com/topology-230210163904-725d62c8/75/Topology-ppt-31-2048.jpg)
![Sweep passes critical point
[Milnor 1963]
• p is critical point of f with index , is
sufficiently small. Then Mc+
has the same
homotopy type as Mc
with -cell attached.
Mc
Mc+
Mc Mc
with -cell
attached
~
Mc+](https://image.slidesharecdn.com/topology-230210163904-725d62c8/75/Topology-ppt-32-2048.jpg)






![Average geodesic distance
• The idea of [Hilaga et al. 01]: use geodesic
distance for the Morse function!
( ) geodist( , )
( ) min ( )
( )
max ( )
M
M
M
g dS
g g
f
g
q
q
p p q
p q
p
q](https://image.slidesharecdn.com/topology-230210163904-725d62c8/75/Topology-ppt-41-2048.jpg)
![Mesh Partitioning
• Now we get to [Zhang et al. 03]
• They use almost the same f as [Hilaga et al.
01]
• Want to find features = long protrusions
• Find local maxima of f !](https://image.slidesharecdn.com/topology-230210163904-725d62c8/75/Topology-ppt-43-2048.jpg)