© The Pennsylvania State University Excel Homework 6 Tutor.docx
- 1. © The Pennsylvania State University Excel Homework 6 Tutorial Written by Peter Chamberlain Directions for Making a Scatterplot 1. Select the range by highlighting the two columns you wish to analyze. The independent variable must be located to the left of the dependent variable. If necessary, you may need to move a column in order to make the column on the left the independent variable. To make things easier, you can put the columns next to each other and click on the Column Letter for the independent variable and drag to the Column Letter for the dependent variable. This will highlight both columns. 2. Click Insert and then on the image for the Scatterplot in the chart section (circled below). Click the upper left scatterplot when given the option. 3. Excel will default to titling the chart to the name of your independent variable. Click in the title so that you can edit the title and call the chart Scatterplot.
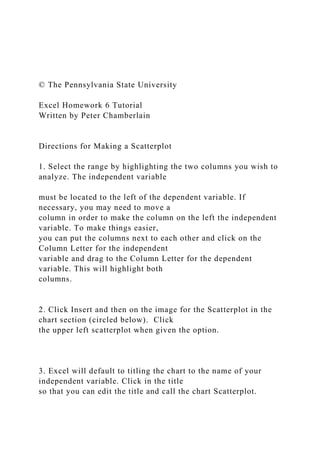
- 2. 4. Clicking in the chart will cause the plus sign, paint brush, and filter on the right-hand side to appear. Click on the plus sign and a menu for Chart Elements such as grid lines, titles, axis titles, etc., will appear. Name your X axis after your independent variable and your Y axis after your dependent variable. 5. If your Scatterplot has a Legend or Gridlines, you can remove those by clicking Legend or Gridlines as appropriate from the plus sign and unchecking any checked boxes for those. 0.000 0.100 0.200 0.300 0.400 0.500 0.600 0.700 0.000 0.100 0.200 0.300 0.400 0.500
- 3. Scatterplot SLG © The Pennsylvania State University Installing the Data Analysis ToolPak (in case it isn’t already installed in your Excel) – see Excel Tutorial 1 Directions for Getting Correlation 1. Open the data set you will need to use for finding correlation. Make sure that your columns are next to each other and that the independent variable column is immediately to the left of the dependent variable column. 2. Highlight both columns by clicking on the Column Letter for the independent variable and dragging to highlight the Column Letter for the dependent variable. 3. Click on Data. 4. Click on Data Analysis. 5. Click on Correlation and click OK.
- 4. 6. Confirm that the Input Range is the same as the columns you have selected. 7. Check the box for Labels in First Row. 8. Click OK. Directions for Running a Regression using Data Analysis 1. Open the data set you will need to use for running regression. 2. Click on Data. 3. Click on Data Analysis. 4. Click on Regression and click OK. The following dialogue box will appear. © The Pennsylvania State University 5. Choose your input and output ranges. The range can only go as far as you have data and the number of rows in your input range must equal the number of rows in your output range. You will select each range individually. You can start at the top of
- 5. the column and scroll down or you can start at the top of the column and use CTRL, Shift, and the Down arrow together to get to the bottom of the column. 6. Check the box for labels if your columns have Labels (they probably will). You can ignore the Confidence Level section. 7. Click OK. If you chose the option to have the output on a New Worksheet Ply, it will show your output on that new ply (or tab if you want to call it that). That option is generally preferred for a cleaner look and also because you may have massively large sets of data that you can work with. 8. Do not check the boxes for Residuals and Normal Probability. Checking these boxes will give you a significant amount of additional output that you will not need. Excel Function: STDEV.S Reminder: Functions start with an equals sign and contain arguments. Functions can be typed into any empty cell. STDEV.S is the function to find the standard deviation of a sample. P-Values in Scientific Notation
- 6. Very small p-values are often written in scientific notation in Excel output. For example, the p-value .000000000043 would be written as 4.3E-11. FINAL REPORT Christophe Bassono Omaha, NE 68182-0694 21st September 2018. Amanda L. Gutierrez, Omaha, NE 68182-0694. Dear Ms. Amanda Gutierrez, SUBJECT: THE TRANSMITTAL LETTER As it can be seen in the present society, many workplaces have
- 7. turned their operationsfrom manual to online. Consequently, this has led to the rise in online workplace scams that are experienced on day to day basis. Therefore, this letter targets to address employees in various institutions to make them aware of the dangers they are exposed to as a result of online scams. On this final draft, I have structure my information in level one and level two. Level one is in red without indent and has size 16. In level two I have black bold with size 14 recent decades, the rise in technological use has led to many organizations transforming from analog to digital. Currently, most organizations carry out their transactions and other communications via online means. It is, therefore, necessary for workers within these organizations to know that they are exposed to various forms of frauds including the friendly fraud, the clean fraud, online intellectual property, identity theft, phishing, credit card fraud, and hacking. In conclusion, it is essential for workers to ensure that they are aware of the dangers theyface while doing business activities online and how they should cope
- 8. with the situations if they become victims. Workers should receive proper training towards the same since such online scams could cost them or their organizations a significant loss. FINAL REPORT How to Avoid Internet Scams at the Workplace Christophe Bassono CIST3000: Advanced Composition IS&T Amanda L. Gutierrez, M.S. & M.A UNO-Fall 2018 FINAL REPORT
- 9. 2 How to Avoid Internet Scams at the Workplace Christophe Bassono CIST3000: Advanced Composition IS&T Amanda L. Gutierrez, M.S. & M.A FINAL REPORT i Contents List of Tables ............................................................................................... ............................................... 5 Executive Summary ...................................................................................... .........
- 10. ..................................... 6 1. Introduction............................................................................ ............................................................. 7 2. Definition ............................................................................................... ............................................. 8 3. Numbers on Online Fraud ............................................................................................... .................. 10 4. Types of Online Fraud and How They Occur ................................................................................... 12 4.1. The Friendly Fraud ............................................................................................... ................. 12 4.2. The Clean Fraud ............................................................................................... ..................... 13 4.3. Online Intellectual Property Theft ......................................................................................... 13 4.4. Identity Theft ............................................................................................... ......................... 14 4.5. Phishing ............................................................................................... ................................. 15
- 11. 4.6. Credit Card Fraud ............................................................................................... ................... 15 4.7. Hacking ............................................................................................... .................................. 15 5. Prevention of Online Fraud ............................................................................................... .................... 16 4.9. Keep Financial Data Separate ............................................................................................... .... 16 4.10. Know who is asking .................................................................................. ............. ............... 17 4.11. Protect your computer ............................................................................................... ............ 17 4.12. Keep your passwords secret ............................................................................................... ... 17 5. Conclusion ............................................................................................... ......................................... 18 6. References.............................................................................. ........................................................... 20
- 12. FINAL REPORT ii List of Tables Fig 1: A table showing growing cases of identity theft and fraud reports in U.S Fig 2: A graph showing the growing cost of frauds in the U.S. from 2010 to 2014
- 13. iii FINAL REPORT Executive Summary The cases of internet scams at the workplaces have increased significantly over the past decades. The sudden increase has been attributed to the technological advancements whereby most organizations prefer carrying on most of their activities via the internet. There are various online frauds that are experienced at the workplace on day to day basis. Examples include, the clean fraud, the friendly fraud, online intellectual property theft, identity theft, phishing, credit card theft, and hacking. Therefore, based on these prevalent figures regarding online fraud at workplaces, institutions that use the internet while offering
- 14. services to their clients need to be aware of the risks they are exposed to. Employers need to inform their workers of their vulnerabilities while dealing with online transactions and other services and then show them some of the ways they can evade these issues. It is also necessary for organizations to educate their workers how to handle such issues in case they become victims. 1 FINAL REPORT
- 15. Introduction The best defense against workplace Internet scamming is to have awareness of the cyberscams that have significantly increased in the modern Internet world (Cacciottolo, & Rees, 2017). It is vital for an individual to be aware of the various vulnerabilities they may be exposed to while using the Internet at the workplace. Just because one is at the workplace does not imply that they are safe from cyber frauds. Most scammers usually spy on organizations to familiarize themselves with the activities and processes that are conducted within these organizations. Someof the cases where Internet scamming is experienced in organizations include Mandate FraudAttacks (Cross, & Kelly, 2016). In this case, the right back specifics of a client can be sent to anoffender. The offender sends an email allegedly containing new bank particulars of a client to theworkplace. The employee at the workplace could then fall into the trap and send back the correctparticulars of the client. Due to such like cases, it is vital that the employee crosschecks
- 16. thestrange payment orders for money transfers. In cases whereby an employee does not have a clearawareness about the transactions, it is necessary that they request for clarification from the management. If it becomes clear that an incorrect transaction has been conducted, the organization should inform the respective bank as soon as possible. Such amongst many others are examples of cyber scam cases that are being experienced at the workplace on a day to day basis. Numerous organizations handle personal and sensitive information of their employees and clients. The organization is mandated to ensuring that this information is kept safe from online hackers and other scammers. Failure of an organization to secure the personal and sensitive information of their clients and workers could lead to negative consequences within its operations. For instance, clients may lose their trust in the organization since no individual could wish her or her information to be lost to fraudsters. Therefore, this report is targeted to educating
- 17. 2 FINAL REPORT organizations regarding the vulnerabilities they are exposed to. The management of any institution should work towards ensuring that they create awareness to their employees regarding the possible scam cases they may come across. Purpose The objective of this report is to create an insight of the numerous cases of internet scams atthe workplace and how these cases could be minimized or scrapped off. This section outlines howthe researcher envisions presenting the report. The outline demonstrates the different sections inwhich the report will be broken into and the information that will be contained in each section.The report starts the definition of terms related to online fraud
- 18. at the workplace. Secondly, ithighlights the history of online fraud at the workplaces whereby it provides the various cases thathave been gathered around the world regarding workplace cyber fraud. After that, the report statesthe numbers of online frauds that have ever been reported at workplaces. Such creates a picture ofhow most workplaces are vulnerable to online frauds (Cross, & Kelly, 2016). The report then goesfurther to state the types of online frauds and how they occur. In this case, it highlights the possibleways online frauds can lure their prey and the names given to these methods. The fifth section ofthe report covers how to prevent online scams at workplaces. The section provides some of themethods that organizations and firms can use to minimize or scrap off the online scams. Lastly,the report ends with a conclusion which summarizes the entire contents outlines in the introductionand the body.
- 19. Definition Online fraud refers to deceitful schemes that are done using the internet. Online fraud maycome in the form of financial theft, identity theft or a combination of both. 3 FINAL REPORT History of Online Fraud An influx of online fraud began to be experienced in the 1990s with the increased technology use and e-commerce. In the beginning, online fraud was done by using the names of famous celebrities of the time to commit internet crimes. Over time, more technical and sophisticated plans were developed such as creating card- generator applications with real credit card numbers, setting up dummy merchant websites and mass identity theft. Today, despite attempts by various governments to regulate and mitigate online fraud, more sophisticated online
- 20. fraud schemes have been established ranging from credit card fraud to phishing, hacking, and identity theft (Saeger & Probert, 2015). In the recent past, computer fraud has evolved through a series of advancements outplaying the traditional security defenses such as the two-factor authentication, antivirus, and SSL encryption in the process. Zeus and SpyEye are the most common attack tools used by hackers since they support the gathering of vast volumes of extremely sensitive authentication data. It has been established that no single application is immune to attacks and the malicious attackers are focusing more on online banking accounts because they offer most direct payoff. Online fraud is based on three core technologies: the botnet controllers capable of handling hundreds of thousands of bots, highly effective data collection, and sophisticated Trojans that are updateable. Form grabbing for PCs running IE/Windows has been a simplified approach for fraud. The technique helps attackers to extract data within browsers. The deployment of form grabbing on compromised
- 21. PCs allowed hackers to obtain numerous numbers of online bank account IDs and passwords. The password-based authentication was termed no longer safe for online banking prompting the introduction of two-factor authentication (Mellinger, 2011). Nevertheless, criminals still found the loophole that helps them to challenge the security of two-factor authentication through web injects. 4 FINAL REPORT Malicious attackers that promote online fraud have created various techniques. As a result, efforts to combat crime ware have been put into place. Computer fraud jeopardizes our security, privacy, and anonymity. There is the need for cybercrime analysts to find out the extent to which malware attacks and viruses have affected our technologies to ensure damage control (Mellinger, 2011). Moreover, they should develop new approaches to controlling the spreading of computer fraud in
- 22. daily operations. Besides, government agencies need to increase their accountability by bankrolling an anti-crimeware program and detecting all forms of online fraud. Numbers on Online Fraud The numbers of online fraud have reached a record high as of the year 2017. The top fraudof 2017 has been reported to online imposters with at least one in every five people having been duped by fraudsters. A whopping three hundred and twenty-eight million has been lost through this form of online fraud (Vaca, 2018). Identity theft and credit card theft has also been reported to be among the top forms of online fraud. Sixty-three thousand people reported tax fraud in 2017. In 2017, the total amount of money lost to online fraudsters in the United States was recorded as nine hundred million dollars, a seven percent increase from the amount lost in 2016. Cacciottolo and Rees (2017) report that in the United Kingdom, over three thousand eight hundred online dating fraud victims had lost over
- 23. thirty-nine million dollars in 2016 to online fraudsters. Recent studies have illustrated that cases of internet scam are on the rise. These cases have accounted to loss of more than $100 billion by companies and individuals. Internet scammers continue to develop diverse ways to blackmail or defraud individuals without their knowledge. Both professionals and non-professionals are susceptible to online fraud and this complicates the issue. According to the Scam Tracker by the Better Bureau reports, computer fraud has continued to escalate in the recent past with over 46,000 cases reported in 2007 in the United States and more than 30,000 cases had been reported by mid-August in 2018 (Wagner, 2018). FINAL REPORT 5
- 24. The graph below illustrates the growing cases of internet fraud in the U.S. (Wagner, 2018) Fig 1.A graph showing growing cases of internet frauds in U.S. Source: Facts + Statistics Fig 2.A graph showing the growing cost of frauds in the U.S. from 2010 to 2014. Source: Facts + Statistics 6 FINAL REPORT Types of Online Fraud and How They Occur According to Rampton (2015), online payment fraud is continuously growing. A significant share of the fraudulent transactions emanates
- 25. from mobile commerce. E-commerce fraud also referred to as purchase fraud happens when a fraudster approaches an innocent party and recommends a business transaction by application of fraudulent means such as fake or stolen credit card. In the process, the merchant is left unpaid during the business transaction. Online store owners are more exposed to online fraud. The continuing advancement of technology jeopardizes payment methods and the data processing systems in most institutions. Often, online fraud occurred when a credit card got lost or its information was not stored securely, but the card-not- present (CNP) frauds have continued to grow recently. Fraudulent orders have increased from 1.58% in 2017 to 1.8% in 2018 in terms of the percentage of total revenue loss in online stores. The most common types of e-commerce fraud include friendly fraud and clean fraud. The Friendly Fraud The friendly fraud occurs when a client buys a product or pays for some services with their personal credit card, and issues a deliberate chargeback arguing that the product or services
- 26. were never received or claims that they never made these charges. Online business supports friendly fraud as it allows customers to perform reverse transactions (Bumbiere, 2018). In most cases, chargebacks are allowed to safeguard clients from online scams, but customers have started taking advantage by using it in place of refunds. The credit card companies continue to suffer from the narrative that the customer is always right as they place the burden of proof on retailers during these dubious transactions. Friendly Fraud can be prevented through various means. The client must take responsibility by ensuring that the credit card distributor matches the business name. 7
- 27. FINAL REPORT Most often, the chargeback fraud takes place when customers fail to identify the name of thecompany on their card statements. Customers are advised to use shipping with tracking since itmakes it easier to provide evidence where the products were delivered. Moreover, it is vital to ensure there are clear reshipping, return, and refunds policies before making any transactions. The Clean Fraud The clean fraud takes place when a stolen credit card is used to make a purchase. It needsa high skill and expertise to happen. The clean fraud is regarded as the ultimate doppelganger sinceit appears like a genuine transaction with good billing, shipping, and IP addresses together withcomplete and verified card data (Bumbiere, 2018). The clean fraud entails four steps. First, thecriminals obtain the cardholder information through data breaches and card skimming. Second,during the purchase, the fraudsters
- 28. utilize the card’s information by impersonating the cardholdermaking online purchases. Thirdly, believing the transaction is legitimate; the merchant accepts thesale and processes payment. Lastly, the merchant is pressurized for chargebacks and lostmerchandise when the fraud is found out. For small retailers, avoiding clean fraud will requireregular software updates since it can bypass the fraud detection tools easily. Smaller retailers areadvised to use the free trial plans of the fraud detection software during holidays from companiessuch as Kount, Signifyd, and Sift Science. Huge retailers have the resources required to purchasethe fraud detection software, and they need to buy them even though they are extremely pricey.Retailers must be keen during any transactions, and this can help to detect some of the cases. Online fraud occurs in various ways. Some of these include online intellectual property theft, identity theft, phishing, untrustworthy websites, credit card fraud, and hacking.
- 29. 8 FINAL REPORT Any author or creator of information has intellectual property rights to their material, whichprohibits other users from using or publishing the material without the owner’s consent. Today,online fraudsters use this material on their own sites without the owner’s permission. This is calledonline intellectual theft. It can therefore be argued that most of the online stores for books andother publications lose the materials with intellectual property rights to fraudsters who access themwithout the authors’ permissions.
- 30. Online Intellectual Property Theft has emerged a threat to many authors whose publications have been stored on online bookshelves. Identity Theft Identity theft occurs when a fraudster steals another person’s personal information such as names, address, birth-date, and account details and uses the stolen information to create an identity under which they hide when committing fraud. It is mostly experienced in organizations which store their clients’ details such as banks, insurance companies, and so on. The fraudsters could use this information to access the client’s bank accounts and other sensitive stuff that could bring a big loss to the client and the company. Identity theft is categorized into two groups including account takeover and true name identity. True name identity implies that the fraudster uses personal info to create new accounts. On the other hand, account takeover implies that the scammer uses personal info to access one’s existing accounts.
- 31. FINAL REPORT 9 Phishing Phishing is a fraudulent activity that attempts to obtain access a person’s sensitive info includingpasswords, credit cards, account information, and usernames. It occurs through deceive emails orwebsites that are created by the fraudsters to lure people into producing their personal information..Fraudsters may trick organizations into providing their client’s particulars by pretending to be theowners of the information to be sent. The fraudsters then use this information unlawfully by defrauding the unsuspecting users (Cassim, 2014).
- 32. Credit Card Fraud This fraud occurs once a person enters their credit card details on deceitful websites. Fraudsters create deceitful cites which appear like genuine cites that lure persons into entering their confidential information into the cites and thus obtain their details illegally. Fraudsters then use this information to make unlawful purchases without the owner’s permission 10 FINAL REPORT Hacking
- 33. This entails gaining illegal entry into a computer system. Hackers use unauthorized meansto access various databases or networks in organizations to retrieve information from clients andother workers. This enables the hacker to steal money or carry out other unlawful dealings without exposing their actual identity. 11 FINAL REPORT Prevention of Online Fraud Various things can be conducted by organizations and workers to avoiding becoming victims of internet fraud.First,employees in an organization should
- 34. monitor and be conscious of people should use different passwords for their accounts and choose long strong passwords, which may not be hacked easily. Secondly, even though there may be many legitimate sellers online, one should be keen on whom they give their information. Before clicking on any linkd, one should make the habit of running a full scan with their antivirus software . Know who is asking Financial institutions such as banks do not send sensitive emails or messages asking for personal information such as social security numbers. These institutions disapprove any attempts to verify account information using this approach. People should understand the safety associated with not sharing personal information such as account numbers, social security or tax ID numbers,passwords or log in information through email or text. An individual can only share his/hersensitive information to a bank through the bank’s secure online banking platform. Any email that asks for sensitive
- 35. information is illegitimate and people should verify its authenticity before replying or sending personal details. Protect your computer Cyber-attacks have been on the rise recently. Installing antivirus software, therefore, is important to any computer or network. Users should regularly update their software to safeguard their computers from computer viruses. Software such as anti-spam software aids in preventing spam and junk email from entering into the inbox of emails and this protect against phishing emails. Besides, every computer should be installed with a firewall as it avoids unauthorized persons, viruses, or malware, from access. The anti-spyware software, nonetheless, blocks the spyware installation on your computer thus redirecting malicious websites or pop-ups.
- 36. 12 FINAL REPORT Passwords Protection Computers users should avoid sharing their passwords. Additionally, always leave any documents with financial data in a secureplace. Changing passwords on a regular basis help to improve the protection and it is necessary to combine numbers, letters, and special characters. Administrators should change password and the default SSID of the wireless network on a regular basis. 13 FINAL REPORT
- 37. Conclusion Evidently, online fraud poses a big threat to organizations as well as individuals. The vice has caused businesses and individuals millions of dollars each year. With increased internet usage,fraudsters continue to device newer and more sophisticated ways of committing online fraud.Advancement in the technologicaluse has led to numerous organizations conducting most of theirtransactions through online means. Such implies that they also face big risks of experiencing onlinescams.It is, therefore, important for every individual to be more aware of the various forms inwhich online fraud may occur. This way, they are in a better position to save themselves frombeing victims of online fraud. Apart from increased consciousness whileusing the internet andmonitoring where their personal information goes, it is also important that organizations invest ina current security system which is able to protect their information from hackers and
- 38. fraudsters.Furthermore, organizations shouldmake their employees understand the various kinds of onlinefrauds they maycome acrossin the midst of their jobs to prepare them andahead of thesescamsand make them ready to tackle such issues whenever they arise(Cross,& Kelly,2016).Businesscorporations should implement measures to prevent the online fraud cases because of the damagesand losses that they can cause. As illustrated, companiescan adhere to various approaches such asinstalling the anti-virus software, adware software, and anti-spyware for protection. Nevertheless,firewall installation allows necessary connections and protects computers from viruses, malware,and hackers. Regular updates of software help in maintenance and increase thinformation of clients and destroy the reputation of companies. Businesses should create atrustworthy environment if they want to succeed both in the short-term and long-term. However,this can only be attained if organizations ensure that they do not become
- 39. preys to the numerousonline attacks that are increasing with the enhancement in technology. FINAL REPORT References 14 Bumbiere, E. (2018, October 23). The Basics of Ecommerce Fraud - What It Is and How To Manage It | Blog - Printful. Retrieved from https://www.printful.com/blog/the-basics-of- ecommerce-fraud-what-is-it-and-how-to-manage-it/ Cacciottolo, M. & Rees, N. (2017). Online dating fraud victim numbers at record high. Retrieved from https://www.bbc.com/news/uk-38678089 Cassim, F. (2014). Addressing the specter of phishing: are adequate measures in place to protect victims of phishing? The Comparative and International Law Journal of Southern Africa, 47(3), 401-428.
- 40. Cross, C., & Kelly, M. (2016). The problem of "white noise": examining current prevention approaches to online fraud. Journal of Financial Crime, 23(4), 806-818. Goldsmith, J. (2007). Who controls the Internet? Illusions of a borderless world. Strategic Direction, 23(11). Insurance Information Institute. (2018). Facts + Statistics: Identity theft and cybercrime | III. Retrieved from https://www.iii.org/fact-statistic/facts-statistics- identity-theft-and- cybercrime Mellinger, P. (2011, November 7). Crime and malware: A short history of computer fraud. Retrieved from https://www.computerworlduk.com/security/crime-and- malware-a-short- history-of-computer-fraud-3316463/ https://www.printful.com/blog/the-basics-of-ecommerce-fraud- what-is-it-and-how-to-manage-it/ https://www.printful.com/blog/the-basics-of-ecommerce-fraud- what-is-it-and-how-to-manage-it/ https://www.computerworlduk.com/security/crime-and- malware-a-short-history-of-computer-fraud-3316463/ https://www.computerworlduk.com/security/crime-and- malware-a-short-history-of-computer-fraud-3316463/
- 41. FINAL REPORT 15 Rampton, J. (2015, April 14). How Online Fraud is a Growing Trend. Retrieved from https://www.forbes.com/sites/johnrampton/2015/04/14/how- online-fraud-is-a-growing- trend/#c596a495f7f7 Saeger, D. A., & Probert, C. (2015). Ponzi scheme: Learn to detect scams and take care of your money. Vaca, M. (2018). The top frauds of 2017. Retrieved from https://www.consumer.ftc.gov/blog/2018/03/top-frauds-2017 Wagner, P. (2018, August 14). Infographic: Internet Scamming is on The Rise. Retrieved from https://www.statista.com/chart/15069/number-of-internet- scams-in-the-us/
- 42. https://www.forbes.com/sites/johnrampton/2015/04/14/how- online-fraud-is-a-growing-trend/#c596a495f7f7 https://www.forbes.com/sites/johnrampton/2015/04/14/how- online-fraud-is-a-growing-trend/#c596a495f7f7 https://www.statista.com/chart/15069/number-of-internet- scams-in-the-us/ CIST 3000: Advanced Writing for IS&T Specifications for Assignment 7: Presentation DUE DATE: Week ____/Date ________ Outline (20 Points) & Presentation (100 Points) 120 Points TOTAL OVERVIEW In this seventh and final assignment, you will create a presentation from the key contents of your report. The presentation is for an audience of professionals. The outline is an outline of your presentation (not of the report itself). The lecture on Presenting a Technical Report is essential to understanding what is required for this deliverable. Review the lecture notes from class and read Chapter 23 before starting on your presentation. You will deliver your presentation and turn in the outline on the due date. PART 1: PRESENTATION Format and Timing Create an oral presentation of your report that is of professional quality and accompanied by slides. Create the presentation for the audience that you have identified in your report, for your professor, and for your class colleagues (who are stand-ins for professional colleagues in a workplace setting).
- 43. Design your presentation appropriately. Design your slides to be clear and appealing. Use visuals in your slides. Review guidelines for developing slides in Chapter 23 and the accompanying lecture. Use your judgment and keep your audience in mind. Time the presentation to be from 5-7 minutes long. Professional presentations often have very tight time windows, and learning to stay within that timing is an important skill. A presentation that is shorter or longer than 5-7 minutes will lose points. Use the extemporaneous method to deliver the presentation (see Table 23.2, p. 580 of text). Practice the presentation before you present it. Do not read from a script, though you may use note cards or your outline to remind yourself of major points. Think of the presentation as something you would do in a workplace setting, before a group of people who expect you to speak knowledgeably about your subject with support from accompanying slides. Citation of Sources on Slides Cite your sources on the slides. Use parenthetical citations at the bottom of a slide as appropriate and include a complete list of citations used in the talk on a separate slide at the end of the presentation. Use APA format for citations. You should have a references slide at the end of your presentation. Cite the source of each visual used on the slides. Do not use copyrighted visuals unless you have written permission from the copyright owner and hand in that permission with the presentation, just as you did with the report. PART 2: OUTLINE Develop a written, detailed outline of your presentation. The
- 44. outline is not a verbatim script of the presentation, but an outline of the points to be made during the delivery of material. The outline is a planning tool for you and it should include enough information that someone else can read it and understand the presentation. That means that the outline provides more information than just bullet points on a slide, but not as much as you actually say during the presentation itself. The outline should match what you actually say. It can happen that a presenter starts with an outline and then ends up saying something completely different. Start with your outline, but then update the outline after you have practiced your final presentation to ensure that one matches the other. Look again at Chapter 10, Chapter 23 (pp. 581-583), and our previous guidelines for outlining. Use an acceptable format, proofread, and apply all our usual writing standards. Simply use an APA style heading at the top of your outline. The outline does not require a cover letter. SUBMISSION OF DELIVERABLES Submit the outline as a PDF file on Canvas. Bring ONE hard copy to class on the due date. Save the file as LastNameA6 prior to submitting. GRADING The folder for Assignment 7 contains the grading rubric for the presentation and outline. The dimensions and the details for each dimension are different from previous assignments. Please review the rubric carefully so that you have a good understanding of what it takes to succeed.
- 45. CIST 3000: Advanced Writing for IS&T Specifications for Assignment 7 : Presentation DUE DATE: Week ____/Date ________ Outline (20 Points ) & Presentation (100 Points) 120 Points TOTAL OVERVIEW In this seventh and final assignment, you will create a
- 46. presentation from the key contents of your report . The presentation is for an audience of professionals. The outline is an outline of your presentation ( not of the report itself ) . The lecture on Presenting a Technical Report is essential to understanding what is required for this deliverable. Review the lecture notes from class and read Chapter 2
- 47. 3 before starting on your presentation . You will deliver your presentation and turn in the outline on the due date. PAR T 1 : PRESENTATION Format and Timing Create a n oral presentation of your report that is of professional quality and accompanied by slides . Create the presentation for the audience that you have identified in your report
- 48. , for your professor , and for your c lass colleagues ( who are stand - ins for professional colleagues in a workplace setting). Design your presentation appropriately. Design your slid es to be clear and appealing. Use visuals in your slides. Review guidelines for developing slides in Chapter 2 3 and the accompanying lecture . Use your judgment and keep your audience in mind. Time the presentation to
- 49. be from 5 - 7 minutes long. Professional presentations often have very tight time windows, and learning to stay within that timing is an important skill. A presentation that is shorter or longer than 5 - 7 minutes will lose points. Use the extemporaneous method to deliver the presentation (see Table 2 3 .2, p. 580 of text). Practice the presentation before you present it. Do not read from a script , though you may use note cards or your outline to remind yourself of major points
- 50. . Think of the presentation as something you would do in a workplace setting, before a group of people who expect you to speak kn owledgeably about your subject with support from accompanying slides . Citation of Sources on Slides Cite your sources on the slides. Use parenthetical citations at th e bottom of a slide as appropriate and include a complete list of citations used in the talk on a separate slide at the end of the presentation. Use APA format for citations. You should have a references slide at the end of your presentation. Cite the source of each visual used on the slides. Do not use
- 51. copyrighted visuals unless you have written permission from the copyright owner and hand in that permission with the presen tation, just as you did with the report. PART 2 : OUTLINE Develop a written, detailed outline of your presentation. The outline is not a verbatim script of the presentation, but an outline of the p oints to be made during the delivery of material . The ou tline is a planning tool for you and it should include enough information that someone else can read it and understand the presentation. That means that the outline provides more information than just bullet points on a slide, but not as much as you actual ly say during the presentation itself. CIST 3000: Advanced Writing for IS&T
- 52. Specifications for Assignment 7: Presentation DUE DATE: Week ____/Date ________ Outline (20 Points) & Presentation (100 Points) 120 Points TOTAL OVERVIEW In this seventh and final assignment, you will create a presentation from the key contents of your report. The presentation is for an audience of professionals. The outline is an outline of your presentation (not of the report itself). The lecture on Presenting a Technical Report is essential to understanding what is required for this deliverable. Review the lecture notes from class and read Chapter 23 before starting on your presentation. You will deliver your presentation and turn in the outline on the due date. PART 1: PRESENTATION Format and Timing Create an oral presentation of your report that is of professional quality and accompanied by slides. Create the presentation for the audience that you have identified in your report, for your professor, and for your class colleagues (who are stand-ins for professional colleagues in a workplace setting). Design your presentation appropriately. Design your slides to be clear and appealing. Use visuals in your slides. Review guidelines for developing slides in Chapter 23 and the accompanying lecture. Use your judgment and keep your audience in mind. Time the presentation to be from 5-7 minutes long. Professional presentations often have very tight time windows,
- 53. and learning to stay within that timing is an important skill. A presentation that is shorter or longer than 5-7 minutes will lose points. Use the extemporaneous method to deliver the presentation (see Table 23.2, p. 580 of text). Practice the presentation before you present it. Do not read from a script, though you may use note cards or your outline to remind yourself of major points. Think of the presentation as something you would do in a workplace setting, before a group of people who expect you to speak knowledgeably about your subject with support from accompanying slides. Citation of Sources on Slides Cite your sources on the slides. Use parenthetical citations at the bottom of a slide as appropriate and include a complete list of citations used in the talk on a separate slide at the end of the presentation. Use APA format for citations. You should have a references slide at the end of your presentation. Cite the source of each visual used on the slides. Do not use copyrighted visuals unless you have written permission from the copyright owner and hand in that permission with the presentation, just as you did with the report. PART 2: OUTLINE Develop a written, detailed outline of your presentation. The outline is not a verbatim script of the presentation, but an outline of the points to be made during the delivery of material. The outline is a planning tool for you and it should include enough information that someone else can read it and understand the presentation. That means that
- 54. the outline provides more information than just bullet points on a slide, but not as much as you actually say during the presentation itself. Name Professor Gutierrez CIST 3000 Date CIST 3000: Advanced Writing for IS&T Presentation Outline: Rough Draft I. Introduction: _______________________ A. _____________________________________________________ ____________________________ B. _____________________________________________________ ____________________________ C. _____________________________________________________ ____________________________ D. _____________________________________________________ ____________________________ II. Body: ____________________________ A. _____________________________________________________ ____________________________ 1. _____________________________________________________ ______________________________ 2. _____________________________________________________ ______________________________
- 59. B. _____________________________________________________ ____________________________ C. _____________________________________________________ ____________________________ D. _____________________________________________________ ____________________________ *While you may use bullet points on this rough draft, a final outline should include complete sentences and ideas. See an example on pages 582-583 in your textbook. Name Professor Gutierrez CIST 3000 Date CIST 3000: Advanced Writing for IS&T Presentation Outline: Rough Draft I. Introduction: _______________________ A. _____________________________________________________ ____________________________
- 60. B. _____________________________________________________ ____________________________ C. _____________________________________________________ ____________________________ D . _____________________________________________________ ____________________________ II. Body: ____________________________ A. _____________________________________________________ ____________________________ 1. _________________________________________ __________________________________________ 2. _____________________________________________________ ______________________________ B.
- 62. 1. ___________________ _____________________________________________________ ___________ 2. _____________________________________________________ ______________________________ III. Body: ____________________________ A. _____________________________________________________ ____________________________ 1. _____________________________________________________ ______________________________ 2. _____________________________________________________ ______________________________ B. _____________________________________________________ ____________________________ 1. _____________________________________________________
- 63. ______________________________ 2. _____________________________________________________ ______________________________ C. _____________________________________________________ ____________________________ 1. _____________________________________________________ ______________________ ________ 2. _____________________________________________________ ______________________________ Name Professor Gutierrez CIST 3000 Date CIST 3000: Advanced Writing for IS&T Presentation Outline: Rough Draft I. Introduction: _______________________ A. _____________________________________________________
- 66. _____________________________________________________ ______________________________ 2. _____________________________________________________ ______________________________ DataGPABRH2B3BHRRBITBBBSOSBBAOBPSLGOPSOWARS t. Louis CardinalsAdron Chambers18823010450100.3750.3750.6251.0000.1Allen Craig7520033631501140111154050.3150.3620.5550.9172Edwin Jackson†132628000281800.3080.3210.3080.6290.2Yadier Molina139475551453211465221334440.3050.3490.4650.8143L ance Berkman145488901472323194267929320.3010.4120.5470.9595 Albert Pujols1475791051732903799313615890.2990.3660.5410.9064D avid Freese9733341991611055147247510.2970.3500.4410.7911.7Jon Jay159455561352421037193288160.2970.3440.4240.7681.5Mat t Holliday124446831323602275234609320.2960.3880.5250.9123. 7Skip Schumaker11736734104190238129275000.2830.3330.3510.685 0.6Nick Punto6313321378412056252110.2780.3880.4210.8091.1Ryan Theriot13244246120261147151294140.2710.3210.3420.6620.6 Daniel Descalso1483263586203128115336520.2640.3340.3530.6871.3 Tony Cruz386581750062261300.2620.3330.3380.6720.1Rafael Furcal†50196295011071682171840.2550.3160.4180.7351.3Colb y Rasmus†9433861831461140142457750.2460.3320.4200.7531.6 Gerald Laird37951122711123491910.2320.3020.3580.660- 0.1Mark Hamilton384751030041341600.2130.2750.2770.551- 0.1Tyler Greene58104222250111301331110.2120.3220.2880.6110.6Andr
- 68. s Snyder349613263031738172300.2710.3760.3960.7720.8Eric Fryer102657000073710.2690.3450.2690.6140Jose Tabata9133453891814211214061160.2660.3490.3620.7110.3Ma tt Diaz†100216145612101970114440.2590.3030.3240.627- 0.5Andrew McCutchen15857287148345238926189126230.2590.3640.4560. 8204.7Xavier Paul†121232305965220811357160.2540.2930.3490.642-0.1Matt Pagnozzi†5802000120200.2500.2500.2500.500-0.1Ronny Cedeno12841343103253232140309320.2490.2970.3390.6360.2 Garrett Jones1484235110330116581834810460.2430.3210.4330.7530.8 John Bowker†191704100252400.2350.3160.2940.6100Ryan Ludwick†3811214265021137193700.2320.3410.3300.6710.2Lyl e Overbay†1033524080171837123367710.2270.3000.3490.649- 0.4Michael McKenry58180174012021158144900.2220.2760.3220.598- 0.3Brandon Wood†9923625529073182196500.2200.2770.3470.6250Chase d'Arnaud481431731620641436120.2170.2420.2870.528-0.2Ross Ohlendorf91423001460700.2140.2140.4290.6430.2Steve Pearce5094819201102472100.2020.2600.2550.515-0.7Pedro Alvarez7423518459141968248010.1910.2720.2890.561-1Paul Maholm2646150001532200.1090.1630.1090.2720Dusty Brown1128230000311010.1070.1380.1070.245-0.4Jeff Karstens3048251002632800.1040.1570.1250.282-0.1James McDonald3155351003632900.0910.1380.1090.247-0.3Kevin Correia2746042003611900.0870.1060.1300.237-0.2Josh Rodriguez71211000111800.0830.2140.0830.298-0.1Brad Lincoln131211100121500.0830.1540.1670.3210Charlie Morton2950043002712900.0800.0940.1400.234-0.3Daniel McCutchen73500000000000.0000.0000.0000.000-0.1Jeff Locke4500000000400.0000.0000.0000.000-0.1Wyatt Toregas3400000000100.0000.0000.0000.000-0.1Brian Burres5300000000100.0000.0000.0000.0000Jason Grilli28100000000100.0000.0000.0000.0000Joe
- 72. Saito30000000000000.0000.0000.0000.0000Sean Green14000000000000.0000.0000.0000.0000Frankie De La Cruz11000000000000.0000.0000.0000.0000Mitch Stetter16000000000000.0000.0000.0000.0000Mark DiFelice3000000000000.0000.0000.0000.0000Tim Dillard24000000000000.0000.0000.0000.0000Danny Herrera†2000000000000.0000.0000.0000.0000John Axford74000000000000.0000.0000.0000.0000Zach Braddock25000000000000.0000.0000.0000.0000Mike Fiers2000000000000.0000.0000.0000.0000Mike McClendon9000000000000.0000.0000.0000.0000Chicago CubsCarlos Zambrano254481420252221400.3180.3480.5000.8480.8Reed Johnson111246337622152811556320.3090.3480.4670.8161.3Sta rlin Castro1586749120736910662913596220.3070.3410.4320.7734A ramis Ramirez149565801733512693288436910.3060.3610.5100.8714. 4Bryan LaHair205991751263091800.2880.3770.5080.8850.3Darwin Barney14352966146236243187226790.2760.3130.3530.6661.2 Marlon Byrd11944651123222935176257830.2760.3240.3950.7191.6Kos uke Fukudome†872933380152313108465720.2730.3740.3690.7421J eff Baker81201205412132377104600.2690.3020.3830.6850.2Blake DeWitt121230216111452695123110.2650.3050.4130.7180.5Ton y Campana951432437301643830240.2590.3030.3010.6030.3DJ LeMahieu376031520041711200.2500.2620.2830.546-0.3Steve Clevenger2411100020000.2500.4000.5000.9000.1Alfonso Soriano1374755011627126882232711320.2440.2890.4690.7590 .7Geovany Soto125421469626017541734512400.2280.3100.4110.7211.6Ca rlos Pena15349372111273288022810116120.2250.3570.4620.8192.3
- 73. Luis Montanez36546124019192900.2220.2630.3520.615- 0.3Koyie Hill461341526312937144010.1940.2680.2760.545- 0.6Casey Coleman212514110070600.1600.1600.2800.4400.1Welington Castillo41302000020400.1540.1540.1540.308-0.1Tyler Colvin8020617318362063145800.1500.2040.3060.509- 1.7Randy Wells2343260001611300.1400.1590.1400.299- 0.1James Russell64801000010300.1250.1250.1250.2500Brad Snyder8911000010600.1110.1110.1110.222-0.2Matt Garza3164260001614200.0940.1210.0940.215-0.4Ryan Dempster3558150000511900.0860.1020.0860.188-0.5Rodrigo Lopez2630120000211100.0670.0970.0670.163-0.3Doug Davis91000000000400.0000.0000.0000.000-0.2Jeff Samardzija75400000000300.0000.0000.0000.000-0.1Ramon Ortiz22200000000200.0000.0000.0000.0000.1Jeff Stevens4200000000100.0000.0000.0000.0000Justin Berg8200000000100.0000.0000.0000.0000Marcos Mateo23100000000000.0000.0000.0000.0000Andrew Cashner7100000000100.0000.0000.0000.0000Kerry Wood55000000000000.0000.0000.0000.0000John Grabow58000000000000.0000.0000.0000.0000Sean Marshall78000000000000.0000.0000.0000.0000Carlos Marmol75000000000000.0000.0000.0000.0000John Gaub4000000000000.0000.0000.0000.0000Rafael Dolis1000000000000.0000.0000.0000.0000Scott Maine7000000000000.0000.0000.0000.0000Chris Carpenter10000000000000.0000.0000.0000.0000http://espn.go.c om/mlb/player/_/id/30811/adron- chambershttp://espn.go.com/mlb/player/_/id/6307/skip- schumakerhttp://espn.go.com/mlb/player/_/id/28668/homer- baileyhttp://espn.go.com/mlb/player/_/id/4097/ramon- hernandezhttp://espn.go.com/mlb/player/_/id/30298/chris- valaikahttp://espn.go.com/mlb/player/_/id/28899/ryan- haniganhttp://espn.go.com/mlb/player/_/id/3425/miguel- cairohttp://espn.go.com/mlb/player/_/id/29601/juan- franciscohttp://espn.go.com/mlb/player/_/id/28954/jay-
- 80. Homework 6 Tutorial or any other sources, answer all of the questions below. This portion of the homework must be attached after the non-Excel portion of Homework 6. All pages of Homework 6 and Excel Homework 6 must be stapled together. Terms: Batting Average (BA) – number of hits/number of at-bats On Base Percentage (OBP) – number of times a player gets on base/number of plate appearances Problem: We would like to see if there is a relationship between the Batting Average (BA) of players in the National League Central with the On Base Percentage (OBP) of the players. If we conclude there is a relationship, then we can use Batting Average to predict On Base Percentage. Follow all the steps in the tutorial to make a scatterplot of Batting Average (BA) and On Base Percentage (OBP). BA will be your independent variable and OBP will be your dependent variable. You do not need to include the Scatterplot with your homework. 1. Write a short description of what kind of relationship, if any, you see in your scatterplot. (.1) Using Data Analysis in Excel, find the correlation coefficient for BA and OBP by creating a correlation matrix. (If Data Analysis is not loaded in your Excel, follow the instructions in Excel Tutorial 1 to install Data Analysis Toolpak.) This correlation matrix may not be able to be done on a Mac without using the webapp. You do not need to include the correlation matrix with your homework.
- 81. 2. What is the value of the correlation coefficient found in your correlation matrix? (.1) 3. Using the value of the correlation coefficient found in Question 2, write a statement about the strength and direction of the data set. (.1) (Questions 1-3 can be completed after Lecture 27.) Use Data Analysis to run a regression of BA (independent variable) and OBP (dependent variable). (If Data Analysis is not loaded in your Excel, follow the instructions in Excel Tutorial 1 to install Data Analysis Toolpak.)This regression may not be able to be run on a Mac without using the webapp. You will be using this output for the remainder of the questions. You do not need to turn the output in with your homework. 4. Using the appropriate functions, find the sample standard deviation of both BA and OBP. You must handwrite or type the entire function equations (including the equals signs, the function names, and the arguments) and the answers. No credit will be given without the entire equations and the answers. (.1 for BA sample standard deviation, .1 for OBP sample standard deviation) 5. Using the value of r found in Question 2, hand calculate b1. You must show all work. (.1)
- 82. 6. Write an interpretation of the slope beginning with the phrase “On average…”. You must use the phrase on average and follow the pattern given in class in order to get credit. (.1) 7. How does the slope you calculated by hand in Question 5 compare to the slope found in the regression output? (.1) 8. Using the regression output, write the regression equation. (.1) 9. What On Base Percentage would you predict if the Batting Average was .206? As always, you must show all work. (.1) 10. Is Batting Average a significant predictor of On Base Percentage? Why or why not? Alpha for this problem is .05. (.1 for answer, .1 for why) 11. What is the value of R-Square? (.1) 12. Write a statement to interpret the R-square value. (.1) SCMYOU MUST SHOW WORK TO GET CREDIT.1. Fill in the following chart for the correlation coefficient. No credit will be given unless the entire chart is filled in.NameSymbolWhat it Tells UsAbs. or Rel.?
- 83. (give units if absolute)BoundariesWhat Extremes SignifyPopulation Correlation Coefficient Sample Correlation Coefficient rStrength + direction in sample None Relative measure- 1+1Perfect rel.2. Fill in the following chart for the coefficient of determination. No credit will be given unless the entire chart is filled in.NameSymbolWhat it Tells UsAbs. or Rel.? (give units if absolute)BoundariesWhat Extremes SignifyPopulationCoefficient of Determination Sample Coefficient of Determination 3. Fill in the following chart for the standard error of the estimate. No credit will be given unless the entire chart is filled in.NameSymbolWhat it MeasuresAbs. or Rel.? (give units if absolute)BoundariesWhat Extremes SignifyStandard Error of the Estimate 4. Fill in the following chart for the regression coefficients. No credit will be given unless the entire chart is filled in.NameSymbolWhat it Tells UsAbs. or Rel.? (give units if absolute)BoundariesPopulation Intercept Sample Intercept Population Slope Sample Slope 5. The standard deviation of advertising = $18.25. The
- 84. standard deviation of sales = $2.57. The correlation is .79. If we are predicting advertising from sales, compute the regression coefficient. Using the phrase given in class (On average, …) and following the pattern given in class, interpret this slope. You must use the phrase on average and follow the pattern given in class to get any credit.6. List what we are concluding if we accept the null in a regression problem (p. 179 in the course packet). Then list what we are concluding if we reject the null in a regression problem. You must list all the statements presented in the entire slide (four for the null and five for the alternative) in class in order to get credit. 7. Write a scenario for a simple regression problem. You must include what the two variables are, stating which one is x and which one is y. Remember, y must be quantitative. Do not use the scenarios that are included in the course packet. If you base your idea off of another source, you must state the source.