Embed presentation
Download as PDF, PPTX


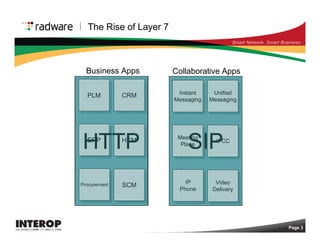

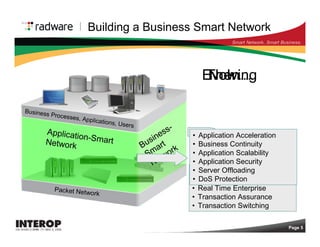
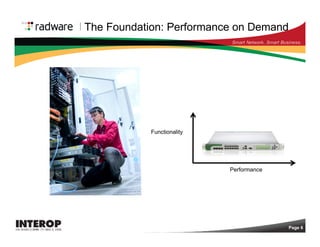
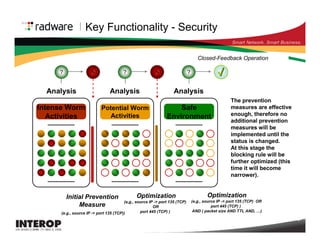
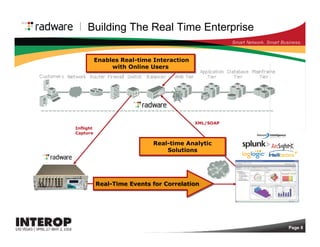
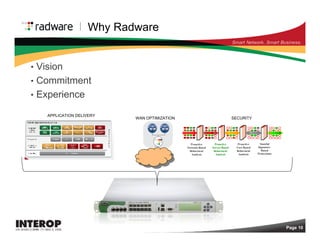
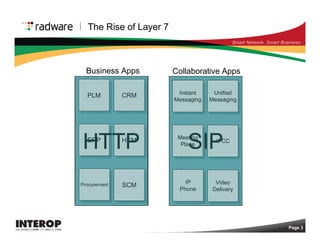
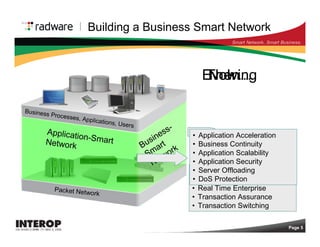
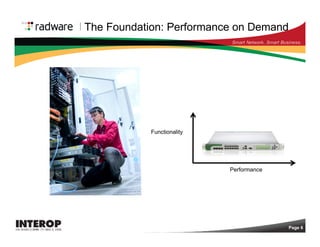
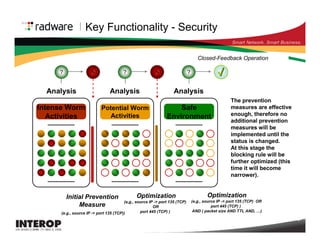
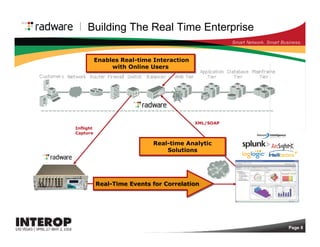
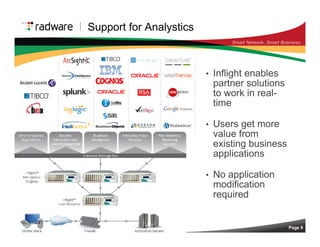
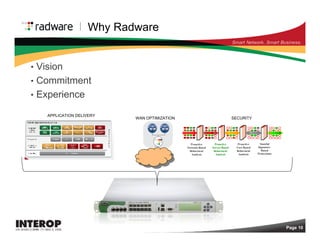
The document discusses the future of application delivery, highlighting the importance of Layer 7 technologies for enhancing business agility and addressing market challenges. It emphasizes the need for new services and compliance while noting that operational costs and integration issues hinder the ability to innovate. Overall, it suggests that advancements in infrastructure are crucial for effectively implementing new business strategies.