The Digital Events Experience
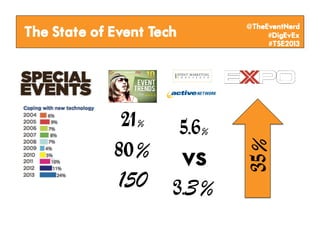
- 1. @TheEventNerd The State of Event Tech #DigEvEx #TSE2013 21% 5.6% 80% vs 35% 150 3.3%
- 2. @TheEventNerd Be afraid. Be not so afraid. #DigEvEx #TSE2013 “It might not work when I need it to…” “It’ll replace the client’s need for me.” “It’s too hard. Where do I start?”
- 3. @TheEventNerd Tech Tidbit #DigEvEx #TSE2013 @StoryMix
- 4. @TheEventNerd #DigEvEx #TSE2013
- 5. @TheEventNerd Trends #DigEvEx #TSE2013
- 6. @TheEventNerd Instagram #DigEvEx #TSE2013 @Instagram Infographic sourced from digitalbuzzblog.com
- 7. @TheEventNerd Tech Tidbits #DigEvEx #TSE2013 @MoxShots
- 8. @TheEventNerd MoxShots #DigEvEx #TSE2013 @MoxShots
- 9. 2007 54% 2009 78% 2006 59% 2008 51% 2010 69% 2007 57% 2009 64% 2011 53% 2008 59% 2010 71% 2012 49% 2009 81% 2011 64% 2013 45% 2010 78% 2012 2011 73% @TheEventNerd Strategery 63% 2013 My own company’s uncertain 2012 69% 68% Shorter lead times finances 2004 17% 2013 61% #DigEvEx 2004 43% 2005 17% An uncertain economy #TSE2013 2005 40% 2006 18% finances 2006 42% 2007 19% 2004 79% 2007 43% 2008 17% 2005 64% 2008 32% 2009 26% 2006 50% 2009 19% 2010 27% 2007 49% 2008 How do you get them to try? 2010 34% 2011 21% 2009 57% 88% 2011 25% 2012 18% 2012 60% 2013 24% 2010 77% 2011 70% 1. Iden=fy the problem/need Dealing with my company’s 2013 32% 2012 69% Labor shortage/lack of procurement/purchasing department 2013 65% skilled labor 2004 29% 2004 n/a Increased competition 2. Iden=fy the real problem/need 2005 28% 2005 2006 16% 14% 2004 42% 2006 26% 2005 39% 2007 30% 2007 14% 2006 41% 2008 23% 2008 13% 2007 49% 2009 6% 3. Define success for the event/technology 2009 14% 2008 39% 2010 19% 2010 9% 2009 25% 2011 18% 2011 10% 2010 31% -‐ How are you tracking that success? 2012 20% 2012 9% 2011 33% 2013 14% 2013 11% 2012 37% Demonstrating the value/ROI Coping with new technology 2013 42% of special events 2004 6% Shorter lead times 2004 n/a 2005 9% 2004 n/a 2005 36% 2006 7% 2005 33% 2006 28% 2007 8% 2006 34% 2007 28% 2008 7% 2007 32% 2008 31% 2009 4% 2008 29% 2009 24% 2010 5% 2009 20% 2010 28% 2011 10% 2010 30% 2011 23% 2012 11% 2011 27% 2012 31% 2013 24% 2012 35% 2013 32% 2013 38%
- 10. isms @TheEventNerd If at first you don’t succeed… #DigEvEx #TSE2013
- 11. isms @TheEventNerd AIM for the puddles! #DigEvEx #TSE2013
- 12. isms @TheEventNerd Be a badass! #DigEvEx #TSE2013 The Badass Creed ( (from UrbanDictionary.com)" 1. A Badass doesn’t talk about being a badass. Period. 2. A badass doesn’t try to be a badass or look tough. They simply are. 3. A badass is true to themselves. 4. A badass does not give up. Badasses always push to be better. 5. A badass is not a jerk. 6. A badass knows their limits. You ain’t Superman! 7. A badass doesn’t make enemies or go looking for fights they can’t win.
- 13. @TheEventNerd RFID #DigEvEx #TSE2013 @FISHtechnology
- 14. @TheEventNerd RFID #DigEvEx #TSE2013 • Collect Content -‐ Guests use RFID tools (such as RFID enabled wristbands or badges) to ac=vely request content which is delivered to them via email, SMS, or Facebook =meline. • Personalized Engagements -‐ Consumers receive content that is based on their interests, age, primary language, etc. • Access -‐ Guests receive special event access as part of a clearly defined value exchange. • Share Experiences -‐ Guests can automa=cally share their experiences with their friends through social media by simply tapping their RFID wristbands. @FISHtechnology @AccessPasses
- 15. @TheEventNerd RFID #DigEvEx #TSE2013 REGISTER AND CHECK IN PHOTO OPPS SOCIAL SHARING/VOTING AUTO POSTS ON SOCIAL MEDIA THEMED PHOTO AREAS
- 16. @TheEventNerd RFID- Metrics #DigEvEx #TSE2013 @FISHtechnology
- 17. @TheEventNerd The Experience Imperative? #DigEvEx #TSE2013 • What’s an “Event?” • What’s an “Experience?” • The difference
- 18. The Digital Event Experience • We are uniquely positioned to do more than create events people forget. • We should strive to create experiences people connect with and hang onto for a lifetime. Technology is just one of the ways we can do that • Try something new today. Step out of the comfort of the events we’ve always done • Feel free to email me with any questions Final Thoughts
- 19. @TheEventNerd Social Seating Experience Imperative The #eiapproved Final Thoughts • Event tech is about the ME in the Media • Personaliza=on is key • It’s an old phrase but…People care about your cool tools when you care about them (AKA don’t just use tech because you can-‐ have a purpose) • May the (crowd)source be with you @TheEventNerd
- 21. The Experience Imperative Thanks to: Special Event Magazine (www.specialevents.com) Event Manager Blog (www.eventmanagerblog.com) Event Marke=ng Ins=tute (www.eventmarke=ng.com) Ac=ve Network (www.ac=venetwork.com) Expo Magazine (www.expoweb.com) Eventbrite (www.eventbrite.com) J. Damany Daniel @TheEventNerd #DigEvEx
- 22. The Experience Imperative Honorable Mentions Social Tables (www.socialtables.com) Bonfyre (www.bonfyreapp.com) PeopleHunt (www.peoplehunt.me) J. Damany Daniel @TheEventNerd #DigEvEx