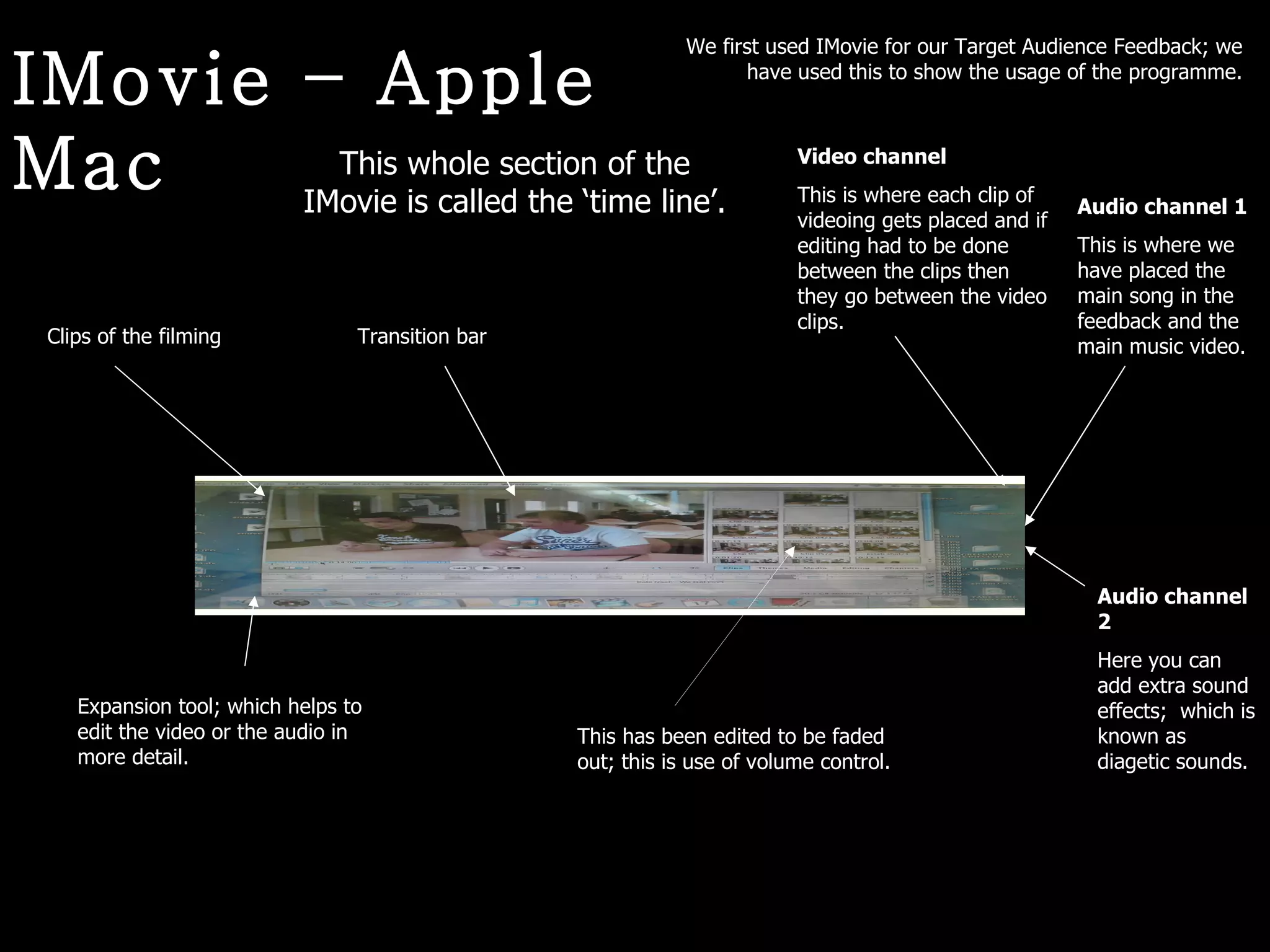
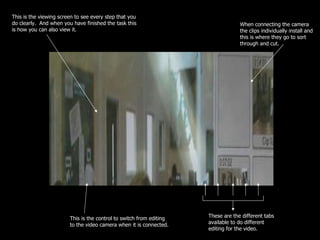
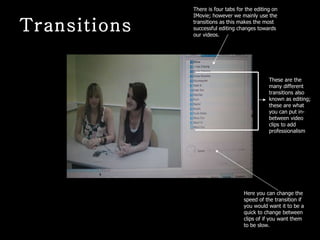
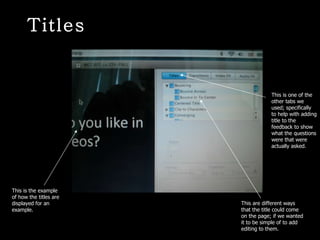
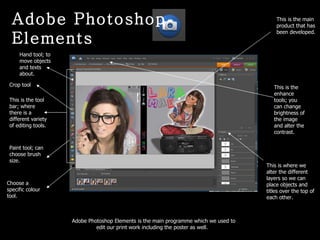
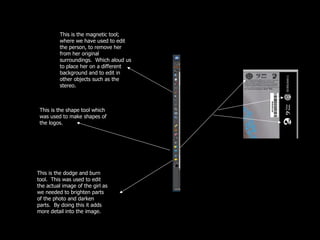
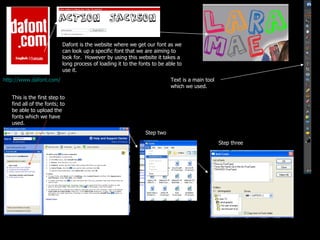
The document discusses various tools and features available in iMovie and Adobe Photoshop Elements for editing video and images. It describes the timeline, audio channels, transition bar, and titles features in iMovie that allow editing of video clips, adding music and sound effects, and customizing transitions between clips. It also outlines tools in Photoshop Elements like the magnetic lasso, dodge and burn tools, and shape tool that enable precise editing and enhancement of images.