Embed presentation
Downloaded 46 times
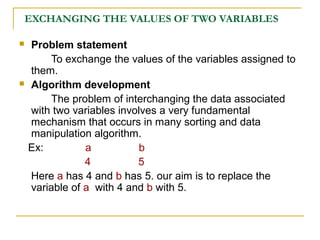
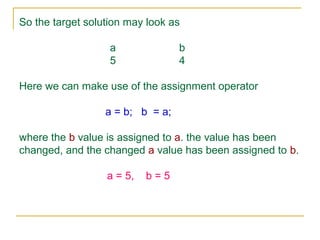
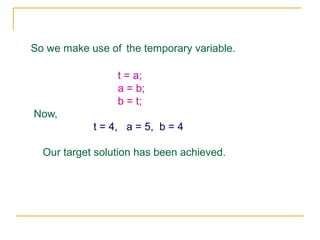
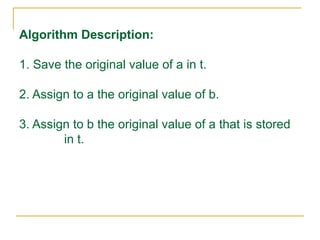
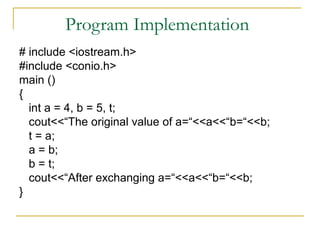

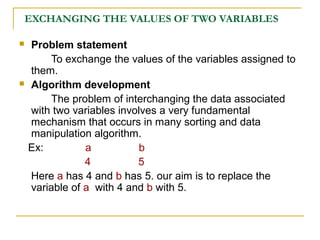
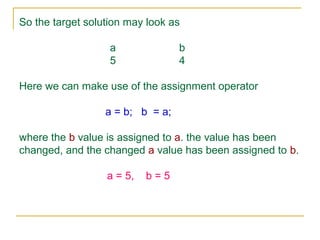
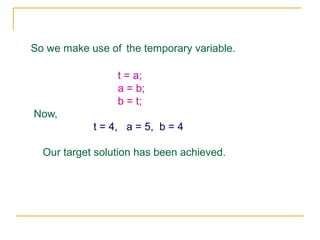
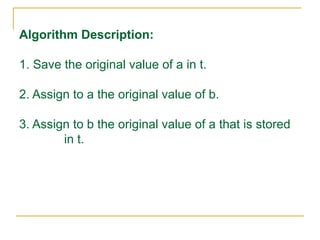
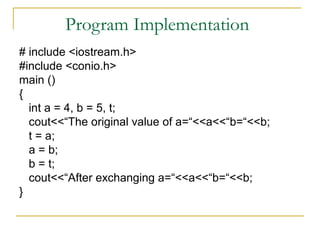
This document describes an algorithm for exchanging the values of two variables. It involves: 1) Saving the original value of the first variable (a) in a temporary variable (t) 2) Assigning the value of the second variable (b) to the first variable (a) 3) Assigning the value stored in the temporary variable (t), which contains the original value of the first variable, to the second variable (b) This exchanges the values stored in the two variables.