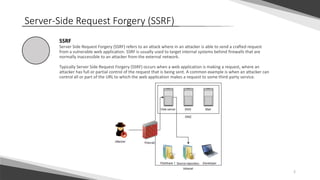
Server-Side Request Forgery (SSRF) refers to an attack where an attacker is able to send a crafted request from a vulnerable web application to target internal systems normally inaccessible from outside. SSRF typically occurs when an attacker has partial or full control over a request being sent by the web application, such as controlling the URL a request is made to. To prevent SSRF, applications should whitelist allowed domains and protocols for requests, and avoid directly using untrusted user input in functions making external requests on the server's behalf.