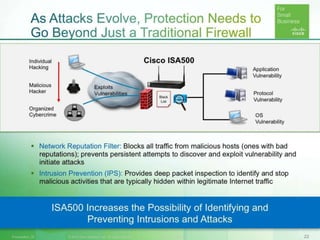
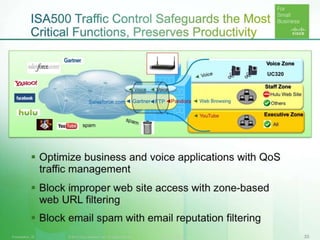
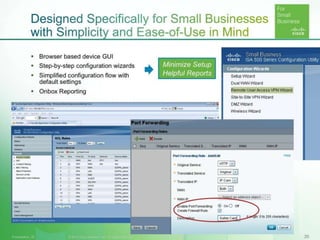
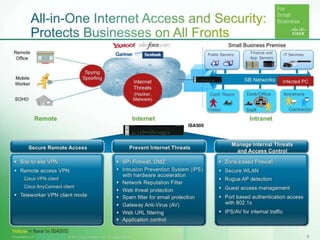
This document discusses taking a comprehensive approach to protecting a home network using Cisco's ISA500 series devices. It was written by Sergey Gashenko of Cisco Small Business Networking and provides resources on Cisco's website for the ISA500 series including an emulator and support forums.