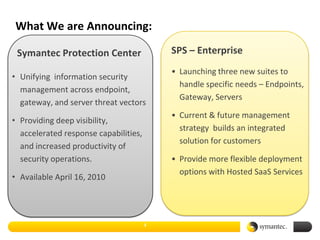
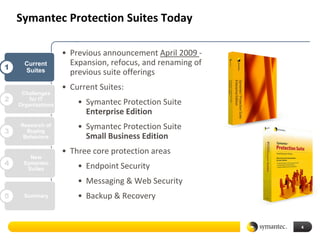
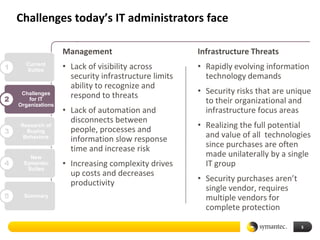
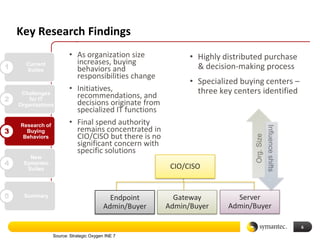
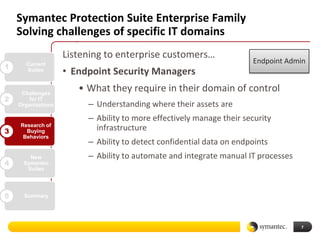
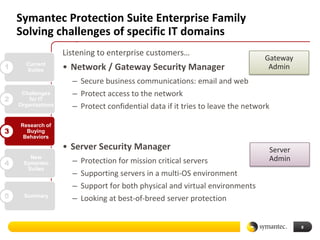
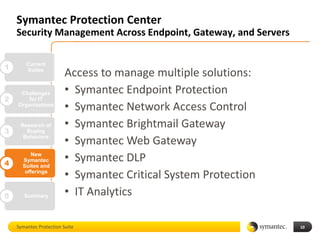
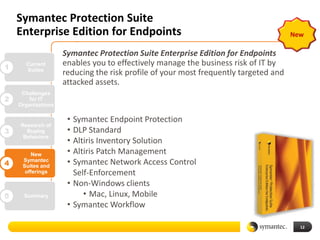
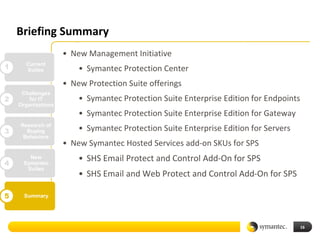
Symantec announced the launch of three new protection suites tailored for enterprise needs, focusing on endpoints, gateways, and servers as part of their unified information security management strategy. These solutions aim to enhance visibility, accelerate response times, and provide flexible deployment options, with availability starting April 16, 2010. The initiative is designed to address current IT challenges and improve overall management efficiency for organizations.