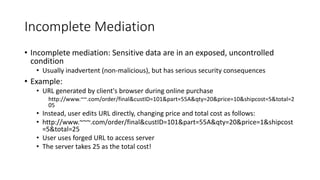
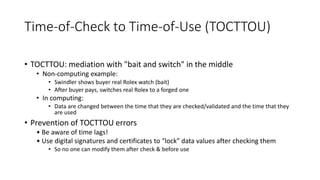
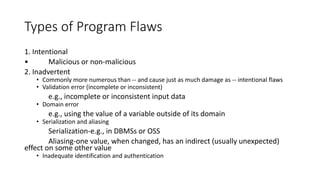
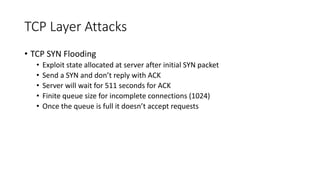
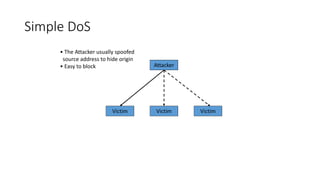
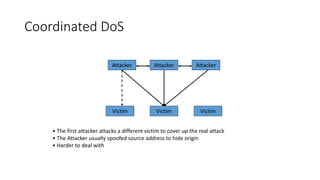
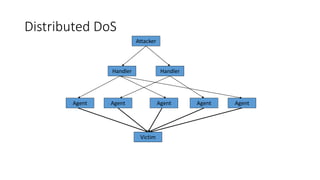
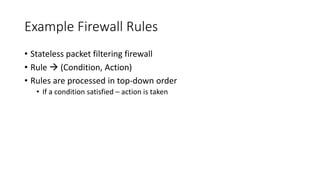
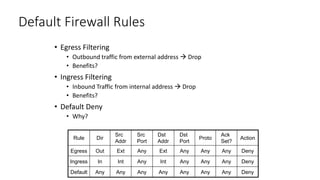
The document discusses the importance of software program security, emphasizing that a program is considered secure if it enforces confidentiality, integrity, and availability. It outlines various issues related to program security, such as incomplete mediation and time-of-check to time-of-use vulnerabilities, along with testing strategies and controls to improve security management. Additionally, it covers types of security attacks and defenses such as firewalls and intrusion detection systems aimed at mitigating risks associated with software and network vulnerabilities.