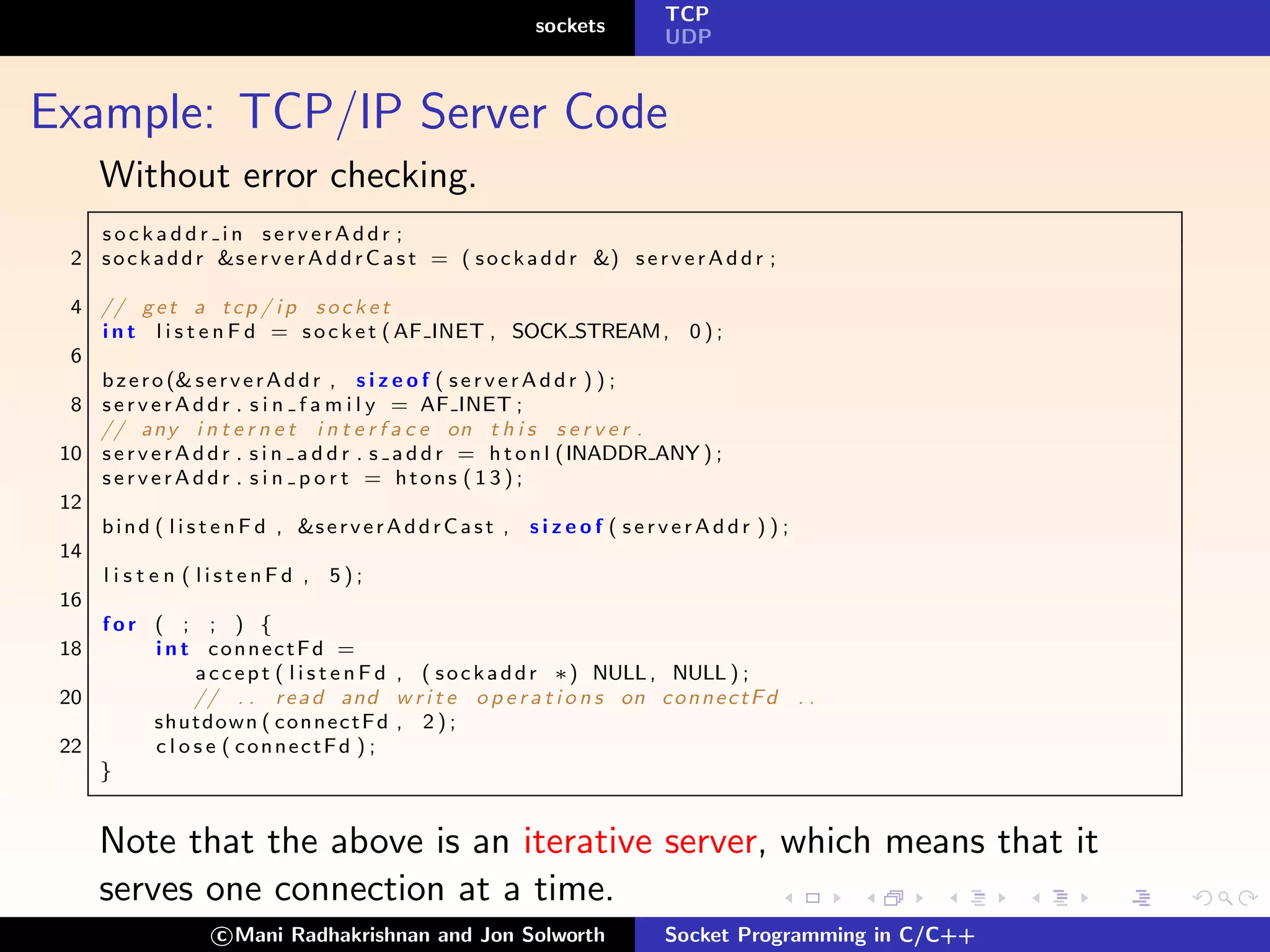
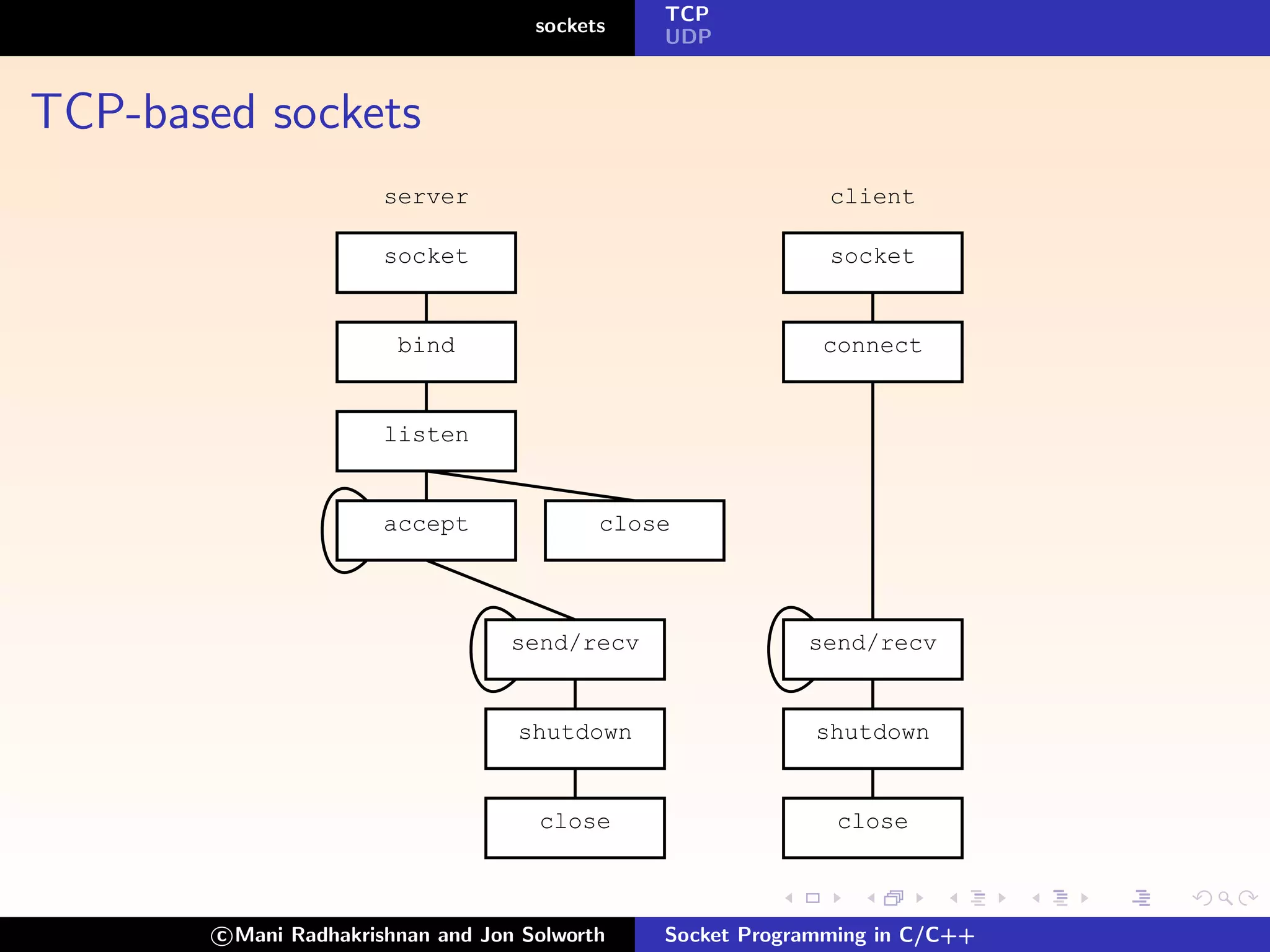
This document discusses socket programming in C/C++. It describes sockets as a protocol-independent method of connecting processes. Sockets can be connection-based or connectionless, packet-based or stream-based, and reliable or unreliable. The document outlines common socket domains, types, and protocols. It provides details on key socket APIs like socket(), bind(), listen(), accept(), and how they are used for connection-based communication between a TCP client and server.
![TCP
sockets
UDP
bind
#i n c l u d e <s y s / t y p e s . h>
2 #i n c l u d e <s y s / s o c k e t . h>
4 i n t bind ( i n t sid , s t r u c t sockaddr ∗addrPtr , i n t l e n )
Where
sid: is the socket id
addrPtr: is a pointer to the address family dependent
address structure
len: is the size of *addrPtr
Associates a socket id with an address to which other processes
can connect. In internet protocol the address is [ipNumber,
portNumber]
c Mani Radhakrishnan and Jon Solworth Socket Programming in C/C++](https://image.slidesharecdn.com/sockets-130104083624-phpapp01/75/Sockets-11-2048.jpg)
![TCP
sockets
UDP
sockaddr
For the internet family:
struct sockaddr in {
2 sa family t s i n f a m i l y ; // = AF INET
in port t sin port ; // i s a p o r t number
4 struct in addr sin addr ; // an I P a d d r e s s
}
For unix sockets (only works between processes on the same
machine)
struct sockaddr un {
2 uint8 t sun length ; //
short sun family ; // = AF LOCAL
4 char sun path [ 1 0 0 ] ; // n u l l t e r m i n a t e d pathname
// ( 1 0 0 i s p o s i x 1 . g minimum )
6 }
When using internet sockets, the second parameter of bind (of
type sockaddr in *) must be cast to (sockaddr *).
c Mani Radhakrishnan and Jon Solworth Socket Programming in C/C++](https://image.slidesharecdn.com/sockets-130104083624-phpapp01/75/Sockets-12-2048.jpg)



![TCP
sockets
UDP
Gethostbyname
Auxiliary functions
#i n c l u d e <n e t d b . h>
2
s t r u c t h o s t e n t ∗ g e t h o s t b y n a m e ( c o n s t c h a r ∗hostname )
Translates a DNS name into a hostent.
Example:
struct hostent ∗hostEntity =
2 g e t h o s t b y n a m e ( ” b e r t . c s . u i c . edu ” ) ;
memcpy ( s o c k e t A d d r− i n a d d r ,
>s
4 hostEntity− >h a d d r l i s t [ 0 ] ,
hostEntity− >h l e n g t h ) ;
c Mani Radhakrishnan and Jon Solworth Socket Programming in C/C++](https://image.slidesharecdn.com/sockets-130104083624-phpapp01/75/Sockets-26-2048.jpg)