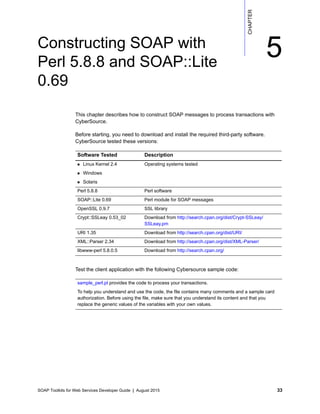
This chapter describes how to construct SOAP messages to process transactions with CyberSource using PHP 5.2.1. It provides instructions for downloading required third-party software, extending the SoapClient class to add WS-Security headers, and testing transactions using sample code provided. Developers can then modify the script and client code to integrate it with their application.