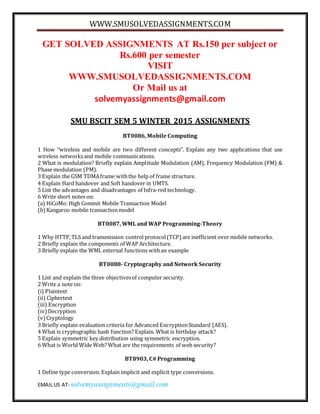
Smu bscit sem 5 winter 2015 assignments
- 1. WWW.SMUSOLVEDASSIGNMENTS.COM EMAIL US AT- solvemyassignments@gmail.com GET SOLVED ASSIGNMENTS AT Rs.150 per subject or Rs.600 per semester VISIT WWW.SMUSOLVEDASSIGNMENTS.COM Or Mail us at solvemyassignments@gmail.com SMU BSCIT SEM 5 WINTER 2015 ASSIGNMENTS BT0086, Mobile Computing 1 How “wireless and mobile are two different concepts”. Explain any two applications that use wireless networksand mobile communications. 2 What is modulation? Briefly explain Amplitude Modulation (AM), Frequency Modulation (FM) & Phase modulation (PM). 3 Explain the GSM TDMAframe withthe help of frame structure. 4 Explain Hard handover and Soft handover in UMTS. 5 List the advantages and disadvantages of Infra-red technology. 6 Write short notes on: (a) HiCoMo: High Commit Mobile Transaction Model (b)Kangaroo mobile transaction model BT0087, WML and WAP Programming-Theory 1 Why HTTP,TLS and transmission control protocol(TCP) are inefficient over mobile networks. 2 Briefly explain the components of WAP Architecture. 3 Briefly explain the WML external functions withan example BT0088- Cryptography and Network Security 1 List and explain the three objectivesof computer security. 2 Write a note on: (i) Plaintext (ii) Ciphertext (iii) Encryption (iv)Decryption (v)Cryptology 3 Briefly explain evaluation criteria for Advanced EncryptionStandard (AES). 4 What is cryptographic hash function? Explain. What is birthday attack? 5 Explain symmetric key distribution using symmetric encryption. 6 What is World Wide Web? What are the requirements of web security? BT8903, C# Programming 1 Define type conversion. Explain implicit and explicit type conversions.
- 2. WWW.SMUSOLVEDASSIGNMENTS.COM EMAIL US AT- solvemyassignments@gmail.com 2 Write a note on the following: 1. Mutable strings 2. Arrays of strings 3. Regular expressions 3 Explain the followingin context of methods in C# with examples: 1. Invoking methods 2. Nesting of methods 4 Define members. Explain constant members and read only members. 5 Define and explain the class visibility and class members’ visibility. 6 Describe the methods used to handle exceptions. Provide examples. BT9003, Data Storage management 1 Explain the practices and techniques to consider when developing a data protection strategy 2 Explain RAID 0, RAID1 and RAID 0+1. 3 How ILM supports implementation of regulatory concerns? Explain with an example. 4 Describe the twomajor product classes in storage networking. 5 Briefly explain redundant I/O path elements. 6 Describe filesystem hierarchy and parsing the file system. GET SOLVED ASSIGNMENTS AT Rs.150 per subject or Rs.600 per semester VISIT WWW.SMUSOLVEDASSIGNMENTS.COM Or Mail us at solvemyassignments@gmail.com