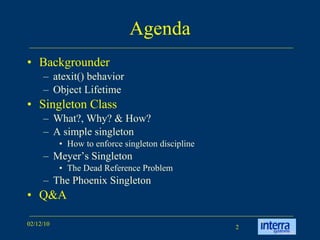
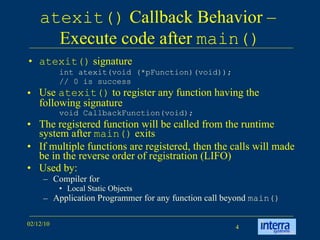
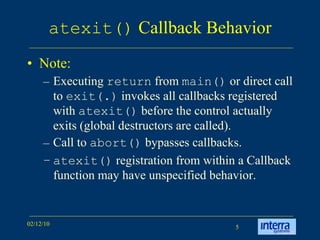
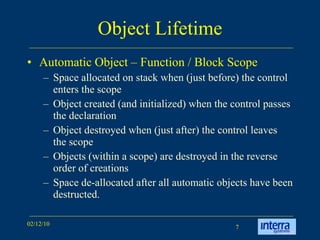
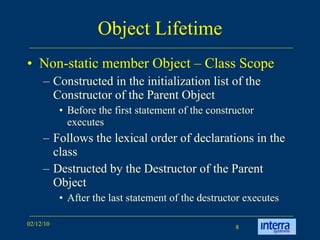
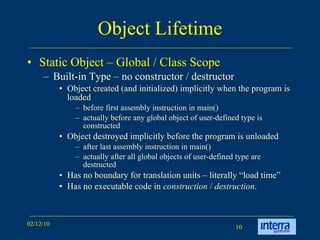
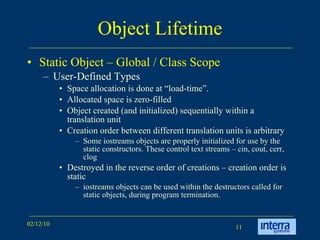
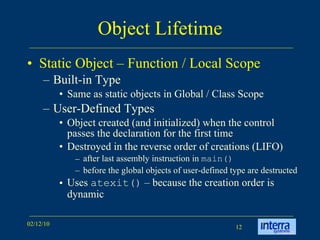
The document discusses singleton object management, detailing the behavior of atexit() for managing object lifetime in programming. It defines the singleton class, its significance as a design pattern, and how to implement it properly while avoiding common issues like dead references. Additionally, it covers examples and references relevant literature on object lifetime and design patterns.












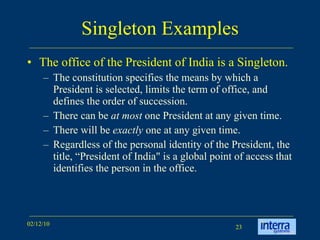
![Singleton Examples Purify license in a network can be a Singleton. A Singleton connection objects can ensure that only one connection can be made at any time. Printer can be a singleton in a network. Keyboard, Display, Log, … [MFC] – The global instance of the CWinApp-derived application class is the singleton. In EDAObjects™ Memory Manager Message Handler Command Line Processor](https://image.slidesharecdn.com/singletonobjectmanagement-1265995299334-phpapp02/85/Singleton-Object-Management-24-320.jpg)

















