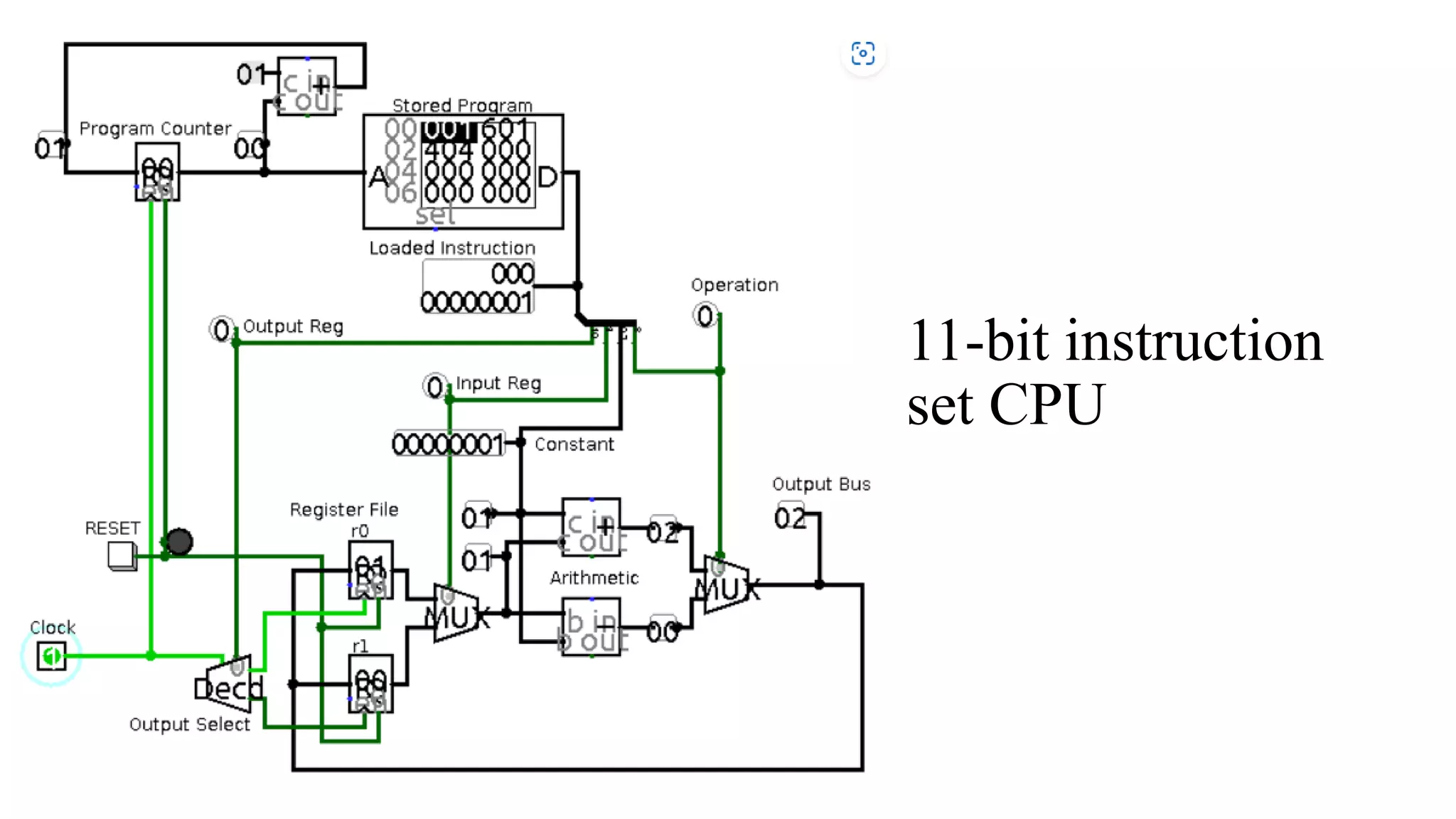
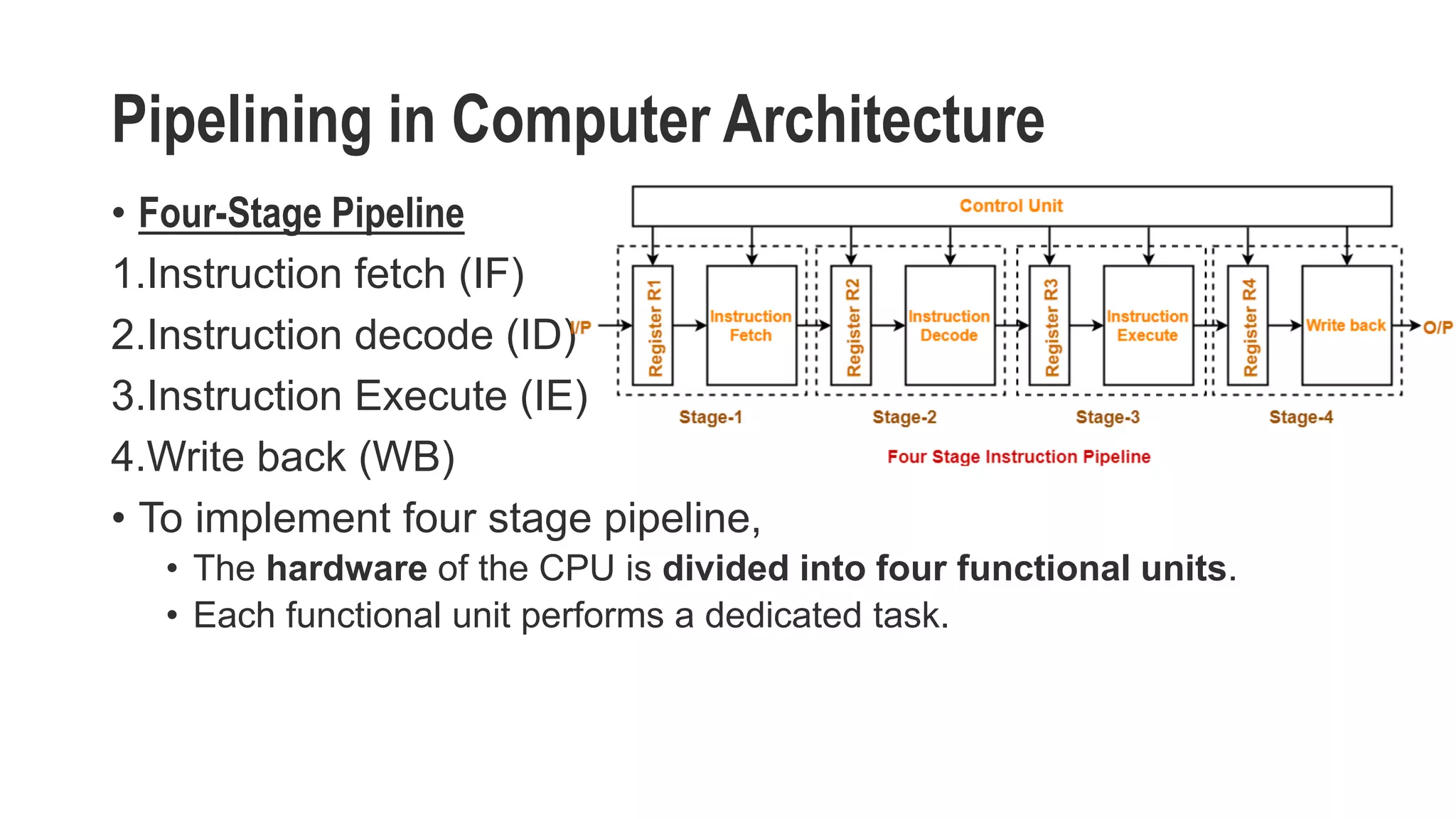
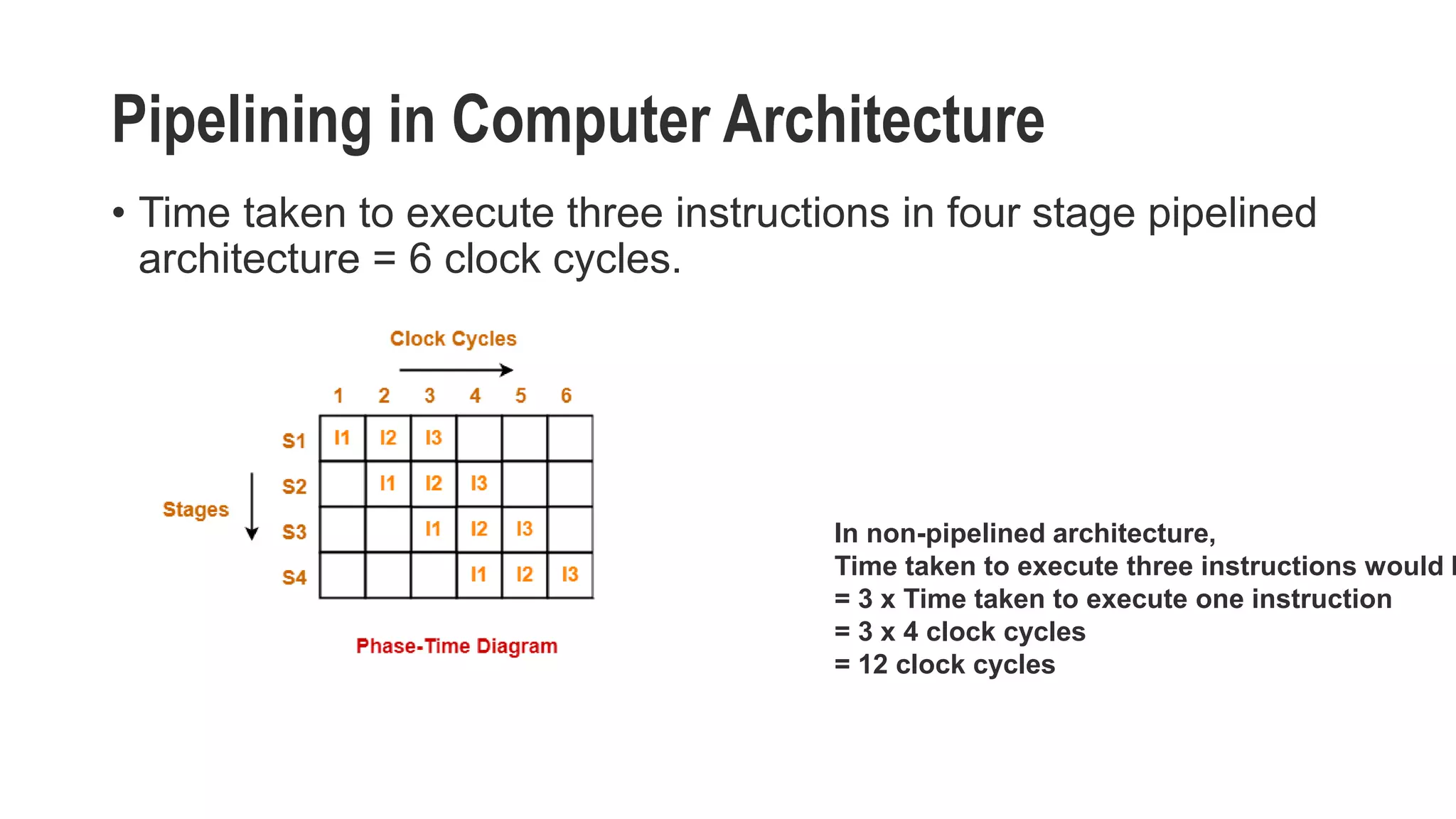
This document discusses CPU instruction set design and pipelining in computer architecture. It describes a simple CPU design with an instruction fetch unit, register file, and arithmetic unit. It also explains the key concepts of pipelining, including splitting a CPU into stages, executing multiple instructions simultaneously by having different stages work on different instructions, and improving efficiency over non-pipelined execution. Pipelining can reduce the time to complete a series of instructions by allowing new instructions to begin processing before previous ones are finished.