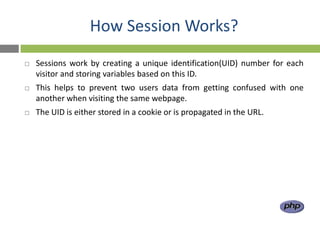
Cookies and sessions allow servers to store and retrieve information about users across multiple page requests that would otherwise be stateless. Cookies store data in the user's browser, while sessions store data on the server. Cookies have limits on size and number, while sessions can store larger objects but expire when the browser closes. PHP provides functions like setcookie() and $_SESSION to easily manage cookies and sessions for maintaining state in web applications.




![Set a cookie
setcookie(name [,value [,expire [,path [,domain [,secure]]]]])
name = cookie name
value = data to store (string)
expire = UNIX timestamp when the cookie expires. Default is that cookie
expires when browser is closed.
path = Path on the server within and below which the cookie is available on.
domain = Domain at which the cookie is available for.
secure = If cookie should be sent over HTTPS connection only. Default false.](https://image.slidesharecdn.com/sessionsandcookies-120221235703-phpapp01/85/Sessions-and-cookies-10-320.jpg)

![Read cookie data
All cookie data is available through the superglobal
$_COOKIE:
$variable = $_COOKIE[‘cookie_name’]
or
$variable = $HTTP_COOKIE_VARS[‘cookie_name’];
e.g.
$age = $_COOKIE[‘age’]](https://image.slidesharecdn.com/sessionsandcookies-120221235703-phpapp01/85/Sessions-and-cookies-14-320.jpg)


![Storing a Session Variable
The correct way to store and retrieve session variables is to use the PHP
$_SESSION variable.
<?php
session_start();
// store session data
$_SESSION['views']=1;
?>
<html>
<body
</body>
</html>](https://image.slidesharecdn.com/sessionsandcookies-120221235703-phpapp01/85/Sessions-and-cookies-20-320.jpg)
![Retrieving a Session Variable
<html>
<body>
<?php
//retrieve session data
echo "Pageviews=". $_SESSION['views'];
?>
</body>
</html>
Display:
Pageviews = 1](https://image.slidesharecdn.com/sessionsandcookies-120221235703-phpapp01/85/Sessions-and-cookies-21-320.jpg)
![Destroying a Session
The unset() function is used to free the specified session variable.
<?php
unset($_SESSION['views']);
?>
You can also completely destroy the session by calling the
session_destroy() function:
<?php
session_destroy();
?>
session_destroy() will reset your session and you will lose all your stored
session data.](https://image.slidesharecdn.com/sessionsandcookies-120221235703-phpapp01/85/Sessions-and-cookies-22-320.jpg)