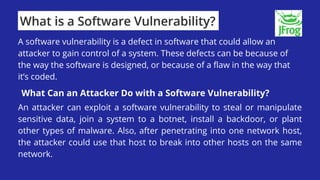
Vulnerabilities refer to flaws in a system that can be exploited by attackers. Software vulnerabilities are defects that allow attackers to gain control of systems by stealing or manipulating data. Zero-day vulnerabilities are unknown flaws without available patches, making them very dangerous for attackers to exploit. Vulnerability scanning tools inspect systems for vulnerabilities, while proper patch management is needed to fix bugs and remove vulnerabilities. Weak host configurations like default settings, open ports and unsecured accounts also pose threats. Supply chain risks include compromised third-party software and vulnerability in supplier systems. Strong security practices and certification are needed across all organizations and suppliers to minimize cyber attacks.