Secured wireless power
•
0 likes•241 views
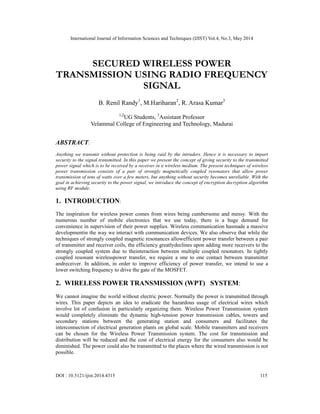
Anything we transmit without protection is being raid by the intruders. Hence it is necessary to impart security to the signal transmitted. In this paper we present the concept of giving security to the transmitted power signal which is to be received by a receiver in a wireless medium. The present techniques of wireless power transmission consists of a pair of strongly magnetically coupled resonators that allow power transmission of tens of watts over a few meters, but anything without security becomes unreliable. With the goal in achieving security to the power signal, we introduce the concept of encryption decryption algorithm using RF module.
Report
Share
Report
Share
Download to read offline
Recommended
Data Transmission Through Inductive Coupled System

https://www.irjet.net/archives/V4/i6/IRJET-V4I6122.pdf
3.3V DC output at -16dBm sensitivity and 77% PCE rectifier for RF energy harv...

3.3V DC output at -16dBm sensitivity and 77% PCE rectifier for RF energy harv...International Journal of Power Electronics and Drive Systems
This paper presents a high voltage conversion at high sensitivity RF energy harvesting system for IoT applications. The harvesting system comprises bulk-to-source (BTMOS) differential-drive based rectifier to produce a high efficiency RF energy harvesting system. Low-pass upward impedance matching network is applied at the rectifier input to increase the sensitivity and output voltage. Dual-oxide-thickness transistors are used in the rectifier circuit to maintain the power efficiency at each stage of the rectifier. The system is designed using 0.18µm Silterra RF in deep n-well process technology and achieves 4.07V output at -16dBm sensitivity without the need of complex auxiliary control circuit and DC-DC charge-pump circuit. The system is targeted for urban environment.A Grid-Connected Photovoltaic Interface System for Delivering Active and Reac...

A Grid-Connected Photovoltaic Interface System for Delivering Active and Reac...International Journal of Power Electronics and Drive Systems
This paper presents a grid-connected photovoltaic (PV) interface for delivering both active and reactive powers. The PV interface employs H-bridge topology DC-DC converter and inverter with analog control technology. The power flow is controlled solely by the adjustable DC output voltage of the DC to DC converter. In order to evaluate the PV interface system’s performances, it is tested by delivering power to the grid with low pawer factor. The experimental results show that at 300W active load, the inverter could deliver the reactive power of 400VAR. The PV interface could also produce very low harmonic voltage and current distorsions. The laboratory measurements show that the total harmonic distortions of inverter output voltage and current are 0.46% and 0.05%, respectively.IRJET- Wireless Power Theft Monitoring System using Zigbee

https://irjet.net/archives/V5/i12/IRJET-V5I1274.pdf
A Novel Configuration of A Microstrip Power Amplifier based on GaAs-FET for I...

Power Amplifiers (PA) are very indispensable components in the design of numerous types of communication transmitters employed in microwave technology. The methodology is exemplified through the design of a 2.45GHz microwave power Amplifier (PA) for the industrial, scientific and medical (ISM) applications using microstrip technology. The main design target is to get a maximum power gain while simultaneously achieving a maximum output power through presenting the optimum impedance which is characteristically carried out per adding a matching circuit between the source and the input of the power amplifier and between the load and the output of the power amplifier. A "T" matching technique is used at the input and the output sides of transistor for assure in band desired that this circuit without reflections and to obtain a maximum power gain. The proposed power amplifier for microwave ISM applications is designed, simulated and optimized by employing Advanced Design System (ADS) software by Agilent. The PA shows good performances in terms of return loss, output power, power gain and stability; the circuit has an input return loss of -38dB and an output return loss of -33.5dB. The 1-dB compression point is 8.69dBm and power gain of the PA is 19.4dBm. The Rollet's Stability measure B1 and the stability factor K of the amplifier is greater than 0 and 1 respectively, which shows that the circuit is unconditionally stable. The total chip size of the PA is 73.5× 36 mm 2 .
Recommended
Data Transmission Through Inductive Coupled System

https://www.irjet.net/archives/V4/i6/IRJET-V4I6122.pdf
3.3V DC output at -16dBm sensitivity and 77% PCE rectifier for RF energy harv...

3.3V DC output at -16dBm sensitivity and 77% PCE rectifier for RF energy harv...International Journal of Power Electronics and Drive Systems
This paper presents a high voltage conversion at high sensitivity RF energy harvesting system for IoT applications. The harvesting system comprises bulk-to-source (BTMOS) differential-drive based rectifier to produce a high efficiency RF energy harvesting system. Low-pass upward impedance matching network is applied at the rectifier input to increase the sensitivity and output voltage. Dual-oxide-thickness transistors are used in the rectifier circuit to maintain the power efficiency at each stage of the rectifier. The system is designed using 0.18µm Silterra RF in deep n-well process technology and achieves 4.07V output at -16dBm sensitivity without the need of complex auxiliary control circuit and DC-DC charge-pump circuit. The system is targeted for urban environment.A Grid-Connected Photovoltaic Interface System for Delivering Active and Reac...

A Grid-Connected Photovoltaic Interface System for Delivering Active and Reac...International Journal of Power Electronics and Drive Systems
This paper presents a grid-connected photovoltaic (PV) interface for delivering both active and reactive powers. The PV interface employs H-bridge topology DC-DC converter and inverter with analog control technology. The power flow is controlled solely by the adjustable DC output voltage of the DC to DC converter. In order to evaluate the PV interface system’s performances, it is tested by delivering power to the grid with low pawer factor. The experimental results show that at 300W active load, the inverter could deliver the reactive power of 400VAR. The PV interface could also produce very low harmonic voltage and current distorsions. The laboratory measurements show that the total harmonic distortions of inverter output voltage and current are 0.46% and 0.05%, respectively.IRJET- Wireless Power Theft Monitoring System using Zigbee

https://irjet.net/archives/V5/i12/IRJET-V5I1274.pdf
A Novel Configuration of A Microstrip Power Amplifier based on GaAs-FET for I...

Power Amplifiers (PA) are very indispensable components in the design of numerous types of communication transmitters employed in microwave technology. The methodology is exemplified through the design of a 2.45GHz microwave power Amplifier (PA) for the industrial, scientific and medical (ISM) applications using microstrip technology. The main design target is to get a maximum power gain while simultaneously achieving a maximum output power through presenting the optimum impedance which is characteristically carried out per adding a matching circuit between the source and the input of the power amplifier and between the load and the output of the power amplifier. A "T" matching technique is used at the input and the output sides of transistor for assure in band desired that this circuit without reflections and to obtain a maximum power gain. The proposed power amplifier for microwave ISM applications is designed, simulated and optimized by employing Advanced Design System (ADS) software by Agilent. The PA shows good performances in terms of return loss, output power, power gain and stability; the circuit has an input return loss of -38dB and an output return loss of -33.5dB. The 1-dB compression point is 8.69dBm and power gain of the PA is 19.4dBm. The Rollet's Stability measure B1 and the stability factor K of the amplifier is greater than 0 and 1 respectively, which shows that the circuit is unconditionally stable. The total chip size of the PA is 73.5× 36 mm 2 .
FIND TRANSMISSION LINE FAULT AND LOCATION DETECTION

In power transmission systems, the majority of voltage and current signal distortions are caused by faults
Mini Project 1 - Amplitude Shift Keying (ASK) Modulator

Course: BEng (Hons) in Electrical and Electronic Engineering
To control the pwm dc motor using ic555 timer

The DC motor is operated by a 555 integrated circuit. The IC 555 in this circuit is being operated in astable mode, which produces a continuous HIGH and LOW pulses. In this mode, the 555 IC can be used as a pulse width modulator with a few small adjustments to the circuit.
During Damping of Low Frequency Oscillations in Power Systems with Fuzzy UPFC...

http://www.ijmer.com/papers/Vol2_Issue6/BR2642154219.pdf
Wireless charging scheme for medium power range application systems

Wireless charging scheme for medium power range application systemsInternational Journal of Power Electronics and Drive Systems
Wireless power transmission (WPT) has attracted a wide variety of subjects in various disciplines and has also become a highly active research field due to its capacity to facilitate charging systems. Wireless power transmission will be compulsory to use soon as this technology enables electrical energy to be transmitted from a power source to an electrical load over an air gap without connecting wires. Wireless power transmission has been developed in the low power (1W to 10W) and high power (100W-500W) region. While the low power region development focuses on powering medical transplants and mobile charging, the higher end of the power spectrum is being developed for the electric vehicle (EV) applications. However medium power range (10W to 100W) is relatively unexplored due to lack of proper applications. The commercial WPT scheme is mainly used for the charging of lithium-ion batteries. Sensitive medium power loads like Lithium Polymer (LiPo) batteries do not have a wireless modular charging system. This paper discusses a proposed scheme for wireless charging of medium-range loads. LiPo batteries are used as the targeted charging load. A minimalistic approach has been considered while designing the electronics for efficiency improvement and a compact, modular scheme. The proposed scheme has been developed for drone and robotics applications and the results are validated.28 GHz balanced pHEMT VCO with low phase noise and high output power performa...

This paper presents the study and design of a balanced voltage controlled oscillator VCO for 5G wireless communication systems. This circuit is designed in monolithic microwave integrated circuit (MMIC) technology using PH15 process from UMS foundry. The VCO ensures an adequate tuning range by a single-ended pHEMT varactors configuration. The simulation results show that this circuit delivers a sinusoidal signal of output power around 9 dBm with a second harmonic rejection between 25.87 and 33.83 dB, the oscillation frequency varies between 26.46 and 28.90 GHz, the phase noise is -113.155 and -133.167 dBc/Hz respectively at 1 MHz and 10 MHz offset and the Figure of Merit is -181.06 dBc/Hz. The power consumed by the VCO is 122 mW. The oscillator layout with bias and RF output pads occupies an area of 0.515 mm 2 .
ISLANDING DETECTION TECHNIQUE FOR DISTRIBUTED GENERATION SYSTEM

ISLANDING DETECTION TECHNIQUE FOR DISTRIBUTED GENERATION SYSTEMSiksha 'O' Anusandhan (Deemed to be University )
These slides present about islanding detection techniques in microgrid systems. Later on the classes other aspects of microgrid protection will be discussed in more detailMEMS MICROPHONE INTERFACE

Hearing loss is one of the most common human impairments. It is estimated that by year 2015 more
than 700 million people will suffer mild deafness. Most can be helped by hearing aid devices depending on the
severity of their hearing loss. This paper describes the implementation and characterization details of a dual
channel transmitter front end (TFE) for digital hearing aid (DHA) applications that use novel micro
electromechanical- systems (MEMS) audio transducers and ultra-low power-scalable analog-to-digital
converters (ADCs), which enable a very-low form factor, energy-efficient implementation for next-generation
DHA. The contribution of the design is the implementation of the dual channel MEMS microphones and powerscalable
ADC system.
DESIGN OF HIGH EFFICIENCY TWO STAGE POWER AMPLIFIER IN 0.13UM RF CMOS TECHNOL...

International Journal of VLSI design & Communication Systems (VLSICS)
Negative resistance amplifier circuit using GaAsFET modelled single MESFET

Negative resistance devices have attracted much attention in the wireless communication industry because of their low cost, better performance, high speed, and reduced power requirements. Although negative resistance circuits are non-linear circuits, they are associated with distortion, which may either be amplitude-to-amplitude distortion or amplitude-to-phase distortion. In this paper, a unique way of realizing a negative resistance amplifier is proposed using a single metal-semiconductor field-effect transistor (MESFET). Intermodulation distortion test (IMD) is performed to evaluate the characteristic response of the negative resistance circuit amplifier to different bias voltages using the harmonic balance (HB) of the advanced designed software (ADS 2016). The results obtained are compared to those of a conventional distributed amplifier. The findings of this study showed that the negative resistance amplifier spreads over a wider frequency output with reduced power requirements while the conventional distributed amplifier has a direct current (DC) offset with output voltage of 32.34 dBm.
Frequency Controlled Protection Scheme to Protect the Theft of Electric Power...

http://iosrjournals.org/iosr-jeee/pages/v5i4.html
Performance analysis of gate misaligned triple

In the literature, the misalignment effects in a nanoscale MOSFET is analyzed for dual material Double
gate MOSFET. The analysis is used in the design criterion of the device. In this paper, a two dimensional
analytical model of gate misalignment effects in Triple Material Double Gate (TM-DG) MOSFET is
presented for the first time. The gate misalignment effect in the drain side is considered. Based on the
misaligned gate, the device is split in to six regions. The boundary conditions are obtained considering the
electric flux and the potential. The parameters are derived using region based approach. Parameters like
surface potential and electric field is studied. In general various methods like superposition method,
Fourier series method, Numerical methods are used to analyze the device. In our paper, the parabolic
approximation method is used for analytical modeling of TM-DG MOSFET since it is more accurate than
the other methods available in the literature. The results are simulated and compared with dual material
double gate MOSFET. The device performance is analyzed and it helps in the design scenario.
Reducing handoff delay by adaptive threshold

In wireless networks data are sent and received with impressive speed and ease. Mobile WiMAX is a
broadband wireless solution that enables coverage of mobile and fixed broadband networks with flexible
network architecture. Devised as a truly broadband access solution, the WiMAX technology offers
promising features in terms of high bandwidth, extended coverage area and low cost. Despite having
many advantages, WiMAX faces major research issues like QoS based bandwidth allocation, Roaming,
Internetworking with other technologies, security and handoff. Handoff occurs when a mobile user goes
from one cell to another without interruption of ongoing session. Many approaches have been proposed
for reducing handoff delay. In this paper, we propose a new approach by which a critical area, an area
far away from serving base station but still inside the coverage of serving base station, is found. And then
overlapping area between serving base stations and neighboring base station are found and tabulated.
According to the size of overlapping area, different weights are assigned where handoff threshold is
changed adaptively to reduce handoff delay.
A zigbee and embedded based security

As technology becomes more advanced and modernized; more features are added to the existing system
for the purpose of satisfying the increasing security needs of the people. Deploying wireless technologies
for security and control in home offers attractive benefits along with user friendly interface. In this paper
we present a smart security system comprises of Zigbee, GSM, Sensors and Smartphone for Security
monitoring and control, when the user is at remote premises. Three sensors namely P
IR, vibration and door sensor are installed at windows and doors. Whenever there is a security breach the
sensors sends the signal to the Pic microcontroller. The Max 232 converter provides serial interface
between the microcontroller and the zigbee. The Zigbee end device then transmits the signal to the Zigbee
coordinator. The ZC at the control console communicates with MCU using max 232 converters. MCU
would in turn access and control the GSM module via AT commands and automatically sends SMS to the
owner's mobile phone informing him about the security breach. On receiving the SMS, user can make a
video call using Skype account; Smartphone installed at home will feed us with a live video. On viewing
the video the user can know whether an intruder has entered or not. Then accordingly faint gas valve and
door lock can be controlled by the user. Thus whenever there is an intrusion, our system lets the user to
monitor and control his premises from any part of the world.
Investigational insight on gaussian

The performance based analysis for typical Gaussian and Gaussian-Halo Doped Double Gate MOSFETs
in conjunction with Normal Doped DG MOSFETs, for which different parameters such as Oxide Thickness,
Ambient Temperature, Gate Material Work Function and Substrate Doping Concentration is varied. This
analysis has been carried out using a TCAD Lab simulation.. From the results obtained, it will be quite
clear that the sub-threshold leakage current of the Gaussian and Gaussian-Halo Doped Double Gate Metal
Oxide Semiconductor FET is relatively lesser. Furthermore the results have been plotted with different
Drain voltage values to enhance the understanding of the physics behind various Doping Profiles in
Double Gate MOSFET. Finally the results has been obtained, analysed and compared. The Possession of
higher Drain current Performance is very acceptable through the rigorous analysis using a TCAD Lab.
Force sensitive resistance based heart beat

Heart related problems are the major health issues for the human. Almost 1 in every 4 death is mainly due
to the heart problems. Most of the people death due to heart problems is due to poor monitoring.To address
this issue this project has been designed. The main aim of this project is to measure the heart rate of an
elderly people and to alert the care taker when the heart rate is abnormal. The innovation done in this
project is measuring the force of the heartbeat at the wrist and thereby measuring the heart rate. The
component used to measure this heart rate is FSR(Force Sensitive Resistor).This device can be
implemented by means of wrist watch or wrist band. It also monitors the heart rate of the people for 24
hours.
More Related Content
What's hot
FIND TRANSMISSION LINE FAULT AND LOCATION DETECTION

In power transmission systems, the majority of voltage and current signal distortions are caused by faults
Mini Project 1 - Amplitude Shift Keying (ASK) Modulator

Course: BEng (Hons) in Electrical and Electronic Engineering
To control the pwm dc motor using ic555 timer

The DC motor is operated by a 555 integrated circuit. The IC 555 in this circuit is being operated in astable mode, which produces a continuous HIGH and LOW pulses. In this mode, the 555 IC can be used as a pulse width modulator with a few small adjustments to the circuit.
During Damping of Low Frequency Oscillations in Power Systems with Fuzzy UPFC...

http://www.ijmer.com/papers/Vol2_Issue6/BR2642154219.pdf
Wireless charging scheme for medium power range application systems

Wireless charging scheme for medium power range application systemsInternational Journal of Power Electronics and Drive Systems
Wireless power transmission (WPT) has attracted a wide variety of subjects in various disciplines and has also become a highly active research field due to its capacity to facilitate charging systems. Wireless power transmission will be compulsory to use soon as this technology enables electrical energy to be transmitted from a power source to an electrical load over an air gap without connecting wires. Wireless power transmission has been developed in the low power (1W to 10W) and high power (100W-500W) region. While the low power region development focuses on powering medical transplants and mobile charging, the higher end of the power spectrum is being developed for the electric vehicle (EV) applications. However medium power range (10W to 100W) is relatively unexplored due to lack of proper applications. The commercial WPT scheme is mainly used for the charging of lithium-ion batteries. Sensitive medium power loads like Lithium Polymer (LiPo) batteries do not have a wireless modular charging system. This paper discusses a proposed scheme for wireless charging of medium-range loads. LiPo batteries are used as the targeted charging load. A minimalistic approach has been considered while designing the electronics for efficiency improvement and a compact, modular scheme. The proposed scheme has been developed for drone and robotics applications and the results are validated.28 GHz balanced pHEMT VCO with low phase noise and high output power performa...

This paper presents the study and design of a balanced voltage controlled oscillator VCO for 5G wireless communication systems. This circuit is designed in monolithic microwave integrated circuit (MMIC) technology using PH15 process from UMS foundry. The VCO ensures an adequate tuning range by a single-ended pHEMT varactors configuration. The simulation results show that this circuit delivers a sinusoidal signal of output power around 9 dBm with a second harmonic rejection between 25.87 and 33.83 dB, the oscillation frequency varies between 26.46 and 28.90 GHz, the phase noise is -113.155 and -133.167 dBc/Hz respectively at 1 MHz and 10 MHz offset and the Figure of Merit is -181.06 dBc/Hz. The power consumed by the VCO is 122 mW. The oscillator layout with bias and RF output pads occupies an area of 0.515 mm 2 .
ISLANDING DETECTION TECHNIQUE FOR DISTRIBUTED GENERATION SYSTEM

ISLANDING DETECTION TECHNIQUE FOR DISTRIBUTED GENERATION SYSTEMSiksha 'O' Anusandhan (Deemed to be University )
These slides present about islanding detection techniques in microgrid systems. Later on the classes other aspects of microgrid protection will be discussed in more detailMEMS MICROPHONE INTERFACE

Hearing loss is one of the most common human impairments. It is estimated that by year 2015 more
than 700 million people will suffer mild deafness. Most can be helped by hearing aid devices depending on the
severity of their hearing loss. This paper describes the implementation and characterization details of a dual
channel transmitter front end (TFE) for digital hearing aid (DHA) applications that use novel micro
electromechanical- systems (MEMS) audio transducers and ultra-low power-scalable analog-to-digital
converters (ADCs), which enable a very-low form factor, energy-efficient implementation for next-generation
DHA. The contribution of the design is the implementation of the dual channel MEMS microphones and powerscalable
ADC system.
DESIGN OF HIGH EFFICIENCY TWO STAGE POWER AMPLIFIER IN 0.13UM RF CMOS TECHNOL...

International Journal of VLSI design & Communication Systems (VLSICS)
Negative resistance amplifier circuit using GaAsFET modelled single MESFET

Negative resistance devices have attracted much attention in the wireless communication industry because of their low cost, better performance, high speed, and reduced power requirements. Although negative resistance circuits are non-linear circuits, they are associated with distortion, which may either be amplitude-to-amplitude distortion or amplitude-to-phase distortion. In this paper, a unique way of realizing a negative resistance amplifier is proposed using a single metal-semiconductor field-effect transistor (MESFET). Intermodulation distortion test (IMD) is performed to evaluate the characteristic response of the negative resistance circuit amplifier to different bias voltages using the harmonic balance (HB) of the advanced designed software (ADS 2016). The results obtained are compared to those of a conventional distributed amplifier. The findings of this study showed that the negative resistance amplifier spreads over a wider frequency output with reduced power requirements while the conventional distributed amplifier has a direct current (DC) offset with output voltage of 32.34 dBm.
Frequency Controlled Protection Scheme to Protect the Theft of Electric Power...

http://iosrjournals.org/iosr-jeee/pages/v5i4.html
What's hot (17)
FIND TRANSMISSION LINE FAULT AND LOCATION DETECTION

FIND TRANSMISSION LINE FAULT AND LOCATION DETECTION
Mini Project 1 - Amplitude Shift Keying (ASK) Modulator

Mini Project 1 - Amplitude Shift Keying (ASK) Modulator
During Damping of Low Frequency Oscillations in Power Systems with Fuzzy UPFC...

During Damping of Low Frequency Oscillations in Power Systems with Fuzzy UPFC...
Wireless charging scheme for medium power range application systems

Wireless charging scheme for medium power range application systems
28 GHz balanced pHEMT VCO with low phase noise and high output power performa...

28 GHz balanced pHEMT VCO with low phase noise and high output power performa...
ISLANDING DETECTION TECHNIQUE FOR DISTRIBUTED GENERATION SYSTEM

ISLANDING DETECTION TECHNIQUE FOR DISTRIBUTED GENERATION SYSTEM
Wcdma p&o-c-en-wireless technology-2-201006-24

Wcdma p&o-c-en-wireless technology-2-201006-24
DESIGN OF HIGH EFFICIENCY TWO STAGE POWER AMPLIFIER IN 0.13UM RF CMOS TECHNOL...

DESIGN OF HIGH EFFICIENCY TWO STAGE POWER AMPLIFIER IN 0.13UM RF CMOS TECHNOL...
Negative resistance amplifier circuit using GaAsFET modelled single MESFET

Negative resistance amplifier circuit using GaAsFET modelled single MESFET
Frequency Controlled Protection Scheme to Protect the Theft of Electric Power...

Frequency Controlled Protection Scheme to Protect the Theft of Electric Power...
Viewers also liked
Performance analysis of gate misaligned triple

In the literature, the misalignment effects in a nanoscale MOSFET is analyzed for dual material Double
gate MOSFET. The analysis is used in the design criterion of the device. In this paper, a two dimensional
analytical model of gate misalignment effects in Triple Material Double Gate (TM-DG) MOSFET is
presented for the first time. The gate misalignment effect in the drain side is considered. Based on the
misaligned gate, the device is split in to six regions. The boundary conditions are obtained considering the
electric flux and the potential. The parameters are derived using region based approach. Parameters like
surface potential and electric field is studied. In general various methods like superposition method,
Fourier series method, Numerical methods are used to analyze the device. In our paper, the parabolic
approximation method is used for analytical modeling of TM-DG MOSFET since it is more accurate than
the other methods available in the literature. The results are simulated and compared with dual material
double gate MOSFET. The device performance is analyzed and it helps in the design scenario.
Reducing handoff delay by adaptive threshold

In wireless networks data are sent and received with impressive speed and ease. Mobile WiMAX is a
broadband wireless solution that enables coverage of mobile and fixed broadband networks with flexible
network architecture. Devised as a truly broadband access solution, the WiMAX technology offers
promising features in terms of high bandwidth, extended coverage area and low cost. Despite having
many advantages, WiMAX faces major research issues like QoS based bandwidth allocation, Roaming,
Internetworking with other technologies, security and handoff. Handoff occurs when a mobile user goes
from one cell to another without interruption of ongoing session. Many approaches have been proposed
for reducing handoff delay. In this paper, we propose a new approach by which a critical area, an area
far away from serving base station but still inside the coverage of serving base station, is found. And then
overlapping area between serving base stations and neighboring base station are found and tabulated.
According to the size of overlapping area, different weights are assigned where handoff threshold is
changed adaptively to reduce handoff delay.
A zigbee and embedded based security

As technology becomes more advanced and modernized; more features are added to the existing system
for the purpose of satisfying the increasing security needs of the people. Deploying wireless technologies
for security and control in home offers attractive benefits along with user friendly interface. In this paper
we present a smart security system comprises of Zigbee, GSM, Sensors and Smartphone for Security
monitoring and control, when the user is at remote premises. Three sensors namely P
IR, vibration and door sensor are installed at windows and doors. Whenever there is a security breach the
sensors sends the signal to the Pic microcontroller. The Max 232 converter provides serial interface
between the microcontroller and the zigbee. The Zigbee end device then transmits the signal to the Zigbee
coordinator. The ZC at the control console communicates with MCU using max 232 converters. MCU
would in turn access and control the GSM module via AT commands and automatically sends SMS to the
owner's mobile phone informing him about the security breach. On receiving the SMS, user can make a
video call using Skype account; Smartphone installed at home will feed us with a live video. On viewing
the video the user can know whether an intruder has entered or not. Then accordingly faint gas valve and
door lock can be controlled by the user. Thus whenever there is an intrusion, our system lets the user to
monitor and control his premises from any part of the world.
Investigational insight on gaussian

The performance based analysis for typical Gaussian and Gaussian-Halo Doped Double Gate MOSFETs
in conjunction with Normal Doped DG MOSFETs, for which different parameters such as Oxide Thickness,
Ambient Temperature, Gate Material Work Function and Substrate Doping Concentration is varied. This
analysis has been carried out using a TCAD Lab simulation.. From the results obtained, it will be quite
clear that the sub-threshold leakage current of the Gaussian and Gaussian-Halo Doped Double Gate Metal
Oxide Semiconductor FET is relatively lesser. Furthermore the results have been plotted with different
Drain voltage values to enhance the understanding of the physics behind various Doping Profiles in
Double Gate MOSFET. Finally the results has been obtained, analysed and compared. The Possession of
higher Drain current Performance is very acceptable through the rigorous analysis using a TCAD Lab.
Force sensitive resistance based heart beat

Heart related problems are the major health issues for the human. Almost 1 in every 4 death is mainly due
to the heart problems. Most of the people death due to heart problems is due to poor monitoring.To address
this issue this project has been designed. The main aim of this project is to measure the heart rate of an
elderly people and to alert the care taker when the heart rate is abnormal. The innovation done in this
project is measuring the force of the heartbeat at the wrist and thereby measuring the heart rate. The
component used to measure this heart rate is FSR(Force Sensitive Resistor).This device can be
implemented by means of wrist watch or wrist band. It also monitors the heart rate of the people for 24
hours.
Identifying the semantic relations on

Ontologisms have been applied to many applications in recent years, especially on Sematic Web, Information
Retrieval, Information Extraction, and Question and Answer. The purpose of domain-specific ontology
is to get rid of conceptual and terminological confusion. It accomplishes this by specifying a set of generic
concepts that characterizes the domain as well as their definitions and interrelationships. This paper will
describe some algorithms for identifying semantic relations and constructing an Information Technology
Ontology, while extracting the concepts and objects from different sources. The Ontology is constructed
based on three main resources: ACM, Wikipedia and unstructured files from ACM Digital Library. Our
algorithms are combined of Natural Language Processing and Machine Learning. We use Natural Language
Processing tools, such as OpenNLP, Stanford Lexical Dependency Parser in order to explore sentences.
We then extract these sentences based on English pattern in order to build training set. We use a
random sample among 245 categories of ACM to evaluate our results. Results generated show that our
system yields superior performance.
An embedded module as “virtual tongue”

There are several human disabilities in nature of which speech impaired people find difficulty in
communicating with others, which is very important to convey their messages without speech. In this
paper, to make them self reliable and independent, with the advent of embedded systems technology an
embedded handheld icon based assistive device as “Virtual Tongue” for Voiceless, which speaks for
severely speech disordered people by simply pressing icons appropriately to fulfill their needs, is proposed.
This proposed module comprises a microcontroller based player to play voice messages, Secure Digital
(SD) card reader, Universal Serial Bus (USB) port, icon based remote keypad, audio amplifier and speaker
along with the benefits like portable, reliable, user friendly, affordable cost, low power consumption and of
course speech in regional language with good clarity. The proposed system is designed to produce speech
regardless of time length, audible to the neighbors, based on the request from the user by pressing the icons
thereby this module deserves inarticulate people. An extended version with a feature of converting text into
voice by adding a circuit, with which any text fed through a keyboard can be converted into speech, is also
discussed.
Uwb localization of nodes for

Localization of nodes in an infrastructure less network serves many purposes. Several issues relating to
security, routing, etc it can be solved if only the actual location of nodes were known. Existing approaches
estimate the location of a node in a network by using received signal strength indicator (RSSI), Time of
Arrival, Time difference of Arrival and, if directional antennas are available, Direction of Arrival. In these
methods the localization accuracy is less (in the order of 20cm). The aim of this paper is to localize nodes
in adhoc networks with improved accuracy using ultra wide band.The proposed method uses a train of low
amplitude pulses of high bandwidth, which reduces the energy consumption, effects due to small scale
fading, and dispersion in time and frequency. The network was simulated in NS-2 with UWB extension and
the localization accuracy was found to be improved (upto 1cm).
Sidelobe suppression and papr

Orthogonal Frequency Division Multiplexing (OFDM) is deployed to overcome the interference. However,
OFDM has a relatively large OOB emissions. In spectrum sharing approaches such as dynamic spectrum
access networks, the OOB power levels of secondary transmissions should be kept below a certain level, in
order not to interfere with primary transmissions. . The difficulties such as sidelobes and PAPR caused by
OFDM is reduced by convex optimization and PTS technique respectively. In this technique each OFDM
subcarrier is multiplied with a real-valued weight that is determined in order not to interfere with adjacent
users. The problem with the SW technique is involving a very complex optimization. We propose a heuristic
approach called convex optimization. It can achieve considerable sidelobe suppression while requiring
significantly less computational resources than the optimal solution. Implementation results prove that it
can be introduced for real-time transmissions. Optimizing the subcarrier weights and SINR is complex, for
which we use the technique of convex optimization. For reducing the PAPR we use Partial Transmit
Sequence (PTS) technique.
Index terms : OFDM (Orthogonal Frequency Division Multiplexing), PAPR (Peak Average Power
Ratio), OOB (Out Of Band), IFFT (Inverse Fast Fourier Transform).
Viewers also liked (10)
Similar to Secured wireless power
speed control of three phase induction motor using IOT

The main aim is to control and monitor the speed of the three-phase induction motor by using the Arduino, node MCU controller and 3-phase inverter circuits.
Microwave wireless power transmission

One of the major issue in power system is the losses occurs during the transmission and distribution of electrical power. As the demand increases day by day, the power generation increases and the power loss is also increased. The major amount of power loss occurs during transmission and distribution. The percentage of loss of power during transmission and distribution is approximated as 26%. The main reason for power loss during transmission and distribution is the resistance of wires used for grid. The efficiency of power transmission can be improved to certain level by using high strength composite overhead conductors and underground cables that use high temperature super conductor. But, the transmission is still inefficient. According to the World Resources Institute (WRI), India’s electricity grid has the highest transmission and distribution losses in the world – a whopping 27%. Numbers published by various Indian government agencies put that number at 30%,40% and greater than 40%. This is attributed to technical losses (grid’s inefficiencies) and theft. Any problem can be solved by state of the art technology. The above discussed problem can be solvedby choose an alternative option for power transmission which could provide much higher efficiency, low transmission cost and avoid power theft. Microwave Power Transmission is one of the promising technologies and may be the righteous alternative for efficient power transmission.
A novel hybrid communication technique involving power line communication and...

A novel hybrid communication technique involving power line communication and...eSAT Publishing House
IJRET : International Journal of Research in Engineering and Technology is an international peer reviewed, online journal published by eSAT Publishing House for the enhancement of research in various disciplines of Engineering and Technology. The aim and scope of the journal is to provide an academic medium and an important reference for the advancement and dissemination of research results that support high-level learning, teaching and research in the fields of Engineering and Technology. We bring together Scientists, Academician, Field Engineers, Scholars and Students of related fields of Engineering and TechnologyA novel hybrid communication technique involving power line communication and...

A novel hybrid communication technique involving power line communication and...eSAT Publishing House
IJRET : International Journal of Research in Engineering and Technology is an international peer reviewed, online journal published by eSAT Publishing House for the enhancement of research in various disciplines of Engineering and Technology. The aim and scope of the journal is to provide an academic medium and an important reference for the advancement and dissemination of research results that support high-level learning, teaching and research in the fields of Engineering and Technology. We bring together Scientists, Academician, Field Engineers, Scholars and Students of related fields of Engineering and TechnologyA Novel Configuration of a Microstrip Microwave Wideband Power Amplifier for ...

RF/microwave power amplifier (PA) is one of the components that has a large effect on the
overall performance of communication system especially in transmitter system and their design is decided
by the parameters of transistor selected. This letter presents a new concept of a wide-band microwave
amplifier using scattering parameters that is often used in the radio frequency communication systemas an
application of the active integrated antenna[1- 2]. This power amplifier operates from 1.75 GHz to 2.15GHz
frequency and it is based on AT-41410 NPN transistor that has a high transition frequency of 10GHz. The
proposed Single Stage PA is designed by microstrip technology and simulated with Advanced Design
System (ADS) software. The simulation results indicate good performances; the small power gain (S21) is
changed between 11.8 and 10dB. For the input reflection coefficient (S11) is varied between -11 and -
22.5dB. Regarding the output reflection coefficient (S22) is varied between -13.1 and -18.7dB over the
wide frequency band of 1.75-2.15GHz and stability without oscillating over a wide range of frequencies.
Effect of DC voltage source on the voltage and current of transmitter and rec...

A solenoid supplied by alternating current (AC) voltage generates electromagnetic which has a field area depends on the level of supplied voltage and current flows through the solenoid. The electromagnetic filed can be captured by the other solenoid in the field area. This concept can be applied in a wireless power transfer (WPT) as presented in this paper. The WPT has transmitter coil and receiver coil which each has form of solenoid. The transmitter coil is connected a half bridge circuit to generate AC voltage on the transmitter coil which transferred to the receiver coil. In the experimental set up, the receiver coil is supplied by DC voltage source and it is changed to observe its effect on the voltage and current on the transmitter and receiver coil of the WPT system.
Designing an Antenna System That Can Perform Conditional RF to DC Harnessing ...

Electromagnetic energy or RF energy will play a pivotal role in wireless technology and wireless communication in the impending future. The paper proposes a concept for a patch antenna based system that can harness RF energy upon triggering and can convert the harnessed RF to DC from the radio frequency of 1 GHz to 3 GHz, the design frequency is 2.4GHz. The patch antenna system contains a high gain patch antenna along with a wireless communicating module and a conversion circuit. The return loss of the antenna is approximately 27.1dB. The power gain is 30.1 dBm .The converter circuit is designed in), Multi-Sim to get an output voltage of around 5V that can be used to power a mobile-device or maybe stored in a battery. The triggering part is done with the help of a T-mote which is simulated in a network simulator, Cooja. The patch antenna is simulated in High Frequency Structural Simulator
IRJET- Wireless Charging of Mobile Phones with Microwaves- A Review

https://irjet.net/archives/V7/i1/IRJET-V7I1317.pdf
“Microcontroller Based Substation Monitoring system with gsm modem”.

• The system is used for transmitting the message to predefined number about the
status of electrical parameters such as voltage, current, temperature etc., to improve
the quality of power.
• Studied about the protection, monitoring and control of a power system.
WIRELESS POWER THEFT MONITORING SYSTEM

Power larceny is the sizably voluminous quandary now days which causes immensely colossal loss to electricity boards. And to surmount these losses prices are incremented. So if we can obviate this larceny we can preserve lots of potency. The mundane practice for power larceny is to short input output terminals or to place magnet on the wheel in case of old meters. In this system a micro controller is interfaced with an energy metering circuit current sensing circuit, RF communication & a contactor to make or break power line. If current is drawing & energy pulses are mundane then no puissance is larceny. If current is drawing & energy pulses are not coming then it designates power larceny. So microcontroller trip the o/p utilizing relay. This information is sent to substation utilizing wireless communication. Line faults may be caused due to over current or earth fault. If there transpires to be a connection between two phase lines then over current fault occurs. Earth fault occurs due to the earthing of phase line through cross arm or any other way.
Wireless Mobile Charger Design Based on Inductive Coupling

This research described the construction and implementation of the contactless wireless mobile phone battery charging which becomes popularity nowadays. The power was transferred to the destination by means of inductive coupling between two coils. In transmitter part, the desired frequency was produced from Arduino by means of PWM Pulse Width Modulation . This frequency was used to drive the induction coil by using MOSFET driver. The MOSFET operated as a switch in terms of T on and T off. The power in transmitter coil was transmitted to surroundings by means of electromagnetic field. The receiver coil was induced by electromagnetic field and produces DC voltage. That converted DC voltage was filtered by capacitor and then regulates to required voltage by using voltage regulator. Optimal frequency range for maximum power transfer is gained by performing theatrical approach and experimental test. Zaw Min Min Htun | Htay Win Mar "Wireless Mobile Charger Design Based on Inductive Coupling" Published in International Journal of Trend in Scientific Research and Development (ijtsrd), ISSN: 2456-6470, Volume-3 | Issue-5 , August 2019, URL: https://www.ijtsrd.com/papers/ijtsrd27882.pdfPaper URL: https://www.ijtsrd.com/engineering/electronics-and-communication-engineering/27882/wireless-mobile-charger-design-based-on-inductive-coupling/zaw-min-min-htun
DESIGN & ANALYSIS OF RF ENERGY HARVESTING SYSTEM FOR CHARGING LOW POWER DEVICES

Finite electrical battery life is encouraging the companies and researchers to come up with new ideas and technologies to drive wireless mobile devices for an infinite or enhance period of time. Common resource constrained wireless devices when they run out of battery they should be recharged. For that purpose main supply & charger are needed to charge drained mobile phone batteries or any portable devices. Practically it is not possible to carry charger wherever we go and also to expect availability of power supply everywhere. To avoid such disadvantages some sort of solution should be given and that can be wireless charging of mobile phones.[4] If the mobile can receive RF power signals from the mobile towers, why can’t we extract the power from the received signals? This can be done by the method or technology called RF energy harvesting. RF energy harvesting holds a promise able future for generating a small amount of electrical power to drive partial circuits in wirelessly communicating electronics devices. RF power harvesting is one of the diverse fields where still research continues. The energy of RF waves used by devices can be harvested and used to operate in more effective and efficient way.
Wireless Power Transmission Using Solar Power System 

The main function of wireless power transfer is to allow electrical devices to be continuously
charged and lose the constraint of a power cord. This whole idea was developed by Nicolas
Tesla in 1893, where he developed a system of illuminating vacuum bulbs using wireless
transmission technique.
paper on Wireless power transmission using magnetic resonance

Wireless power transmission using magnetic resonance
Similar to Secured wireless power (20)
speed control of three phase induction motor using IOT

speed control of three phase induction motor using IOT
Optical Fiber Communication ECE Practical File.pdf

Optical Fiber Communication ECE Practical File.pdf
A novel hybrid communication technique involving power line communication and...

A novel hybrid communication technique involving power line communication and...
A novel hybrid communication technique involving power line communication and...

A novel hybrid communication technique involving power line communication and...
A Novel Configuration of a Microstrip Microwave Wideband Power Amplifier for ...

A Novel Configuration of a Microstrip Microwave Wideband Power Amplifier for ...
Effect of DC voltage source on the voltage and current of transmitter and rec...

Effect of DC voltage source on the voltage and current of transmitter and rec...
Designing an Antenna System That Can Perform Conditional RF to DC Harnessing ...

Designing an Antenna System That Can Perform Conditional RF to DC Harnessing ...
IRJET- Wireless Charging of Mobile Phones with Microwaves- A Review

IRJET- Wireless Charging of Mobile Phones with Microwaves- A Review
“Microcontroller Based Substation Monitoring system with gsm modem”.

“Microcontroller Based Substation Monitoring system with gsm modem”.
Wireless Mobile Charger Design Based on Inductive Coupling

Wireless Mobile Charger Design Based on Inductive Coupling
DESIGN & ANALYSIS OF RF ENERGY HARVESTING SYSTEM FOR CHARGING LOW POWER DEVICES

DESIGN & ANALYSIS OF RF ENERGY HARVESTING SYSTEM FOR CHARGING LOW POWER DEVICES
Wireless Power Transmission Using Solar Power System 

Wireless Power Transmission Using Solar Power System
paper on Wireless power transmission using magnetic resonance

paper on Wireless power transmission using magnetic resonance
More from ijistjournal
Call for Research Articles - 5th International Conference on Artificial Intel...

5th International Conference on Artificial Intelligence and Machine Learning (CAIML 2024) will provide an excellent international forum for sharing knowledge and results in theory, methodology and applications of Artificial Intelligence and Machine Learning. The Conference looks for significant contributions to all major fields of the Artificial Intelligence, Machine Learning in theoretical and practical aspects. The aim of the Conference is to provide a platform to the researchers and practitioners from both academia as well as industry to meet and share cutting-edge development in the field.
Authors are solicited to contribute to the conference by submitting articles that illustrate research results, projects, surveying works and industrial experiences that describe significant advances in the areas of Computer Science, Engineering and Applications.
Online Paper Submission - International Journal of Information Sciences and T...

The International Journal of Information Science & Techniques (IJIST) focuses on information systems science and technology coercing multitude applications of information systems in business administration, social science, biosciences, and humanities education, library sciences management, depiction of data and structural illustration, big data analytics, information economics in real engineering and scientific problems.
This journal provides a forum that impacts the development of engineering, education, technology management, information theories and application validation. It also acts as a path to exchange novel and innovative ideas about Information systems science and technology.
SYSTEM IDENTIFICATION AND MODELING FOR INTERACTING AND NON-INTERACTING TANK S...

System identification from the experimental data plays a vital role for model based controller design. Derivation of process model from first principles is often difficult due to its complexity. The first stage in the development of any control and monitoring system is the identification and modeling of the system. Each model is developed within the context of a specific control problem. Thus, the need for a general system identification framework is warranted. The proposed framework should be able to adapt and emphasize different properties based on the control objective and the nature of the behavior of the system. Therefore, system identification has been a valuable tool in identifying the model of the system based on the input and output data for the design of the controller. The present work is concerned with the identification of transfer function models using statistical model identification, process reaction curve method, ARX model, genetic algorithm and modeling using neural network and fuzzy logic for interacting and non interacting tank process. The identification technique and modeling used is prone to parameter change & disturbance. The proposed methods are used for identifying the mathematical model and intelligent model of interacting and non interacting process from the real time experimental data.
Call for Research Articles - 4th International Conference on NLP & Data Minin...

4th International Conference on NLP & Data Mining (NLDM 2024) will provide an excellent international forum for sharing knowledge and results in theory, methodology and applications of Natural Language Computing and Data Mining.
Authors are solicited to contribute to the conference by submitting articles that illustrate research results, projects, surveying works and industrial experiences that describe significant advances in the following areas, but are not limited to.
Research Article Submission - International Journal of Information Sciences a...

The International Journal of Information Science & Techniques (IJIST) focuses on information systems science and technology coercing multitude applications of information systems in business administration, social science, biosciences, and humanities education, library sciences management, depiction of data and structural illustration, big data analytics, information economics in real engineering and scientific problems.
This journal provides a forum that impacts the development of engineering, education, technology management, information theories and application validation. It also acts as a path to exchange novel and innovative ideas about Information systems science and technology.
Call for Papers - International Journal of Information Sciences and Technique...

The International Journal of Information Science & Techniques (IJIST) focuses on information systems science and technology coercing multitude applications of information systems in business administration, social science, biosciences, and humanities education, library sciences management, depiction of data and structural illustration, big data analytics, information economics in real engineering and scientific problems.
This journal provides a forum that impacts the development of engineering, education, technology management, information theories and application validation. It also acts as a path to exchange novel and innovative ideas about Information systems science and technology.
Implementation of Radon Transformation for Electrical Impedance Tomography (EIT)

Radon Transformation is generally used to construct optical image (like CT image) from the projection data in biomedical imaging. In this paper, the concept of Radon Transformation is implemented to reconstruct Electrical Impedance Topographic Image (conductivity or resistivity distribution) of a circular subject. A parallel resistance model of a subject is proposed for Electrical Impedance Topography(EIT) or Magnetic Induction Tomography(MIT). A circular subject with embedded circular objects is segmented into equal width slices from different angles. For each angle, Conductance and Conductivity of each slice is calculated and stored in an array. A back projection method is used to generate a two-dimensional image from one-dimensional projections. As a back projection method, Inverse Radon Transformation is applied on the calculated conductance and conductivity to reconstruct two dimensional images. These images are compared to the target image. In the time of image reconstruction, different filters are used and these images are compared with each other and target image.
Online Paper Submission - 6th International Conference on Machine Learning & ...

6th International Conference on Machine Learning & Applications (CMLA 2024) will provide an excellent international forum for sharing knowledge and results in theory, methodology and applications of on Machine Learning & Applications.
Authors are solicited to contribute to the conference by submitting articles that illustrate research results, projects, surveying works and industrial experiences that describe significant advances in the following areas, but are not limited to.
Submit Your Research Articles - International Journal of Information Sciences...

The International Journal of Information Science & Techniques (IJIST) focuses on information systems science and technology coercing multitude applications of information systems in business administration, social science, biosciences, and humanities education, library sciences management, depiction of data and structural illustration, big data analytics, information economics in real engineering and scientific problems.
This journal provides a forum that impacts the development of engineering, education, technology management, information theories and application validation. It also acts as a path to exchange novel and innovative ideas about Information systems science and technology.
BER Performance of MPSK and MQAM in 2x2 Almouti MIMO Systems

Almouti published the error performance of the 2x2 space-time transmit diversity scheme using BPSK. One of the key techniques employed for correcting such errors is the Quadrature amplitude modulation (QAM) because of its efficiency in power and bandwidth.. In this paper we explore the error performance of the 2x2 MIMO system using the Almouti space-time codes for higher order PSK and M-ary QAM. MATLAB was used to simulate the system; assuming slow fading Rayleigh channel and additive white Gaussian noise. The simulated performance curves were compared and evaluated with theoretical curves obtained using BER tool on the MATLAB by setting parameters for random generators. The results shows that the technique used do find a place in correcting error rates of QAM system of higher modulation schemes. The model can equally be used not only for the criteria of adaptive modulation but for a platform to design other modulation systems as well.
Online Paper Submission - International Journal of Information Sciences and T...

The International Journal of Information Science & Techniques (IJIST) focuses on information systems science and technology coercing multitude applications of information systems in business administration, social science, biosciences, and humanities education, library sciences management, depiction of data and structural illustration, big data analytics, information economics in real engineering and scientific problems.
This journal provides a forum that impacts the development of engineering, education, technology management, information theories and application validation. It also acts as a path to exchange novel and innovative ideas about Information systems science and technology.
Call for Papers - International Journal of Information Sciences and Technique...

The International Journal of Information Science & Techniques (IJIST) focuses on information systems science and technology coercing multitude applications of information systems in business administration, social science, biosciences, and humanities education, library sciences management, depiction of data and structural illustration, big data analytics, information economics in real engineering and scientific problems.
This journal provides a forum that impacts the development of engineering, education, technology management, information theories and application validation. It also acts as a path to exchange novel and innovative ideas about Information systems science and technology.
International Journal of Information Sciences and Techniques (IJIST)

The International Journal of Information Science & Techniques (IJIST) focuses on information systems science and technology coercing multitude applications of information systems in business administration, social science, biosciences, and humanities education, library sciences management, depiction of data and structural illustration, big data analytics, information economics in real engineering and scientific problems.
This journal provides a forum that impacts the development of engineering, education, technology management, information theories and application validation. It also acts as a path to exchange novel and innovative ideas about Information systems science and technology.
BRAIN TUMOR MRIIMAGE CLASSIFICATION WITH FEATURE SELECTION AND EXTRACTION USI...

Feature extraction is a method of capturing visual content of an image. The feature extraction is the process to represent raw image in its reduced form to facilitate decision making such as pattern classification. We have tried to address the problem of classification MRI brain images by creating a robust and more accurate classifier which can act as an expert assistant to medical practitioners. The objective of this paper is to present a novel method of feature selection and extraction. This approach combines the Intensity, Texture, shape based features and classifies the tumor as white matter, Gray matter, CSF, abnormal and normal area. The experiment is performed on 140 tumor contained brain MR images from the Internet Brain Segmentation Repository. The proposed technique has been carried out over a larger database as compare to any previous work and is more robust and effective. PCA and Linear Discriminant Analysis (LDA) were applied on the training sets. The Support Vector Machine (SVM) classifier served as a comparison of nonlinear techniques Vs linear ones. PCA and LDA methods are used to reduce the number of features used. The feature selection using the proposed technique is more beneficial as it analyses the data according to grouping class variable and gives reduced feature set with high classification accuracy.
Research Article Submission - International Journal of Information Sciences a...

The International Journal of Information Science & Techniques (IJIST) focuses on information systems science and technology coercing multitude applications of information systems in business administration, social science, biosciences, and humanities education, library sciences management, depiction of data and structural illustration, big data analytics, information economics in real engineering and scientific problems.
This journal provides a forum that impacts the development of engineering, education, technology management, information theories and application validation. It also acts as a path to exchange novel and innovative ideas about Information systems science and technology.
A MEDIAN BASED DIRECTIONAL CASCADED WITH MASK FILTER FOR REMOVAL OF RVIN

In this paper A Median Based Directional Cascaded with Mask (MBDCM) filter has been proposed, which is based on three different sized cascaded filtering windows. The differences between the current pixel and its neighbors aligned with four main directions are considered for impulse detection. A direction index is used for each edge aligned with a given direction. Minimum of these four direction indexes is used for impulse detection under each masking window. Depending on the minimum direction indexes among these three windows new value to substitute the noisy pixel is calculated. Extensive simulations showed that the MBDCM filter provides good performances of suppressing impulses from both gray level and colored benchmarked images corrupted with low noise level as well as for highly dense impulses. MBDCM filter gives better results than MDWCMM filter in suppressing impulses from highly corrupted digital images.
DECEPTION AND RACISM IN THE TUSKEGEE SYPHILIS STUDY

During the twentieth century (1932-1972), white physicians representing the United States government
conducted a human experiment known as the Tuskegee Syphilis Study on black syphilis patients in Macon
County, Alabama. The creators of the study, who supported the idea of black inferiority and the concept
that black people’s bodies functioned differently from white people’s, observed the effects of a disease
called syphilis on untreated black patients in order to collect data for further research on syphilis. Black
individuals involved with the study believed that they were receiving treatment, although in truth,
treatments for syphilis were purposely held back from them. Not only this, but fluids from their bodies, such
as blood and spinal fluid, were extracted to serve as research material without their awareness of the
purpose of the collection. The physicians justified their approach by positioning it as mere observation,
asserting that they were not actively intervening with the patients participating in the experiment. However,
despite their claims of passivity, these white physicians engaged in various morally improper actions,
including deceit, which ultimately resulted in the deaths of numerous black patients who might have had a
chance at survival.
Online Paper Submission - International Journal of Information Sciences and T...

The International Journal of Information Science & Techniques (IJIST) focuses on information systems science and technology coercing multitude applications of information systems in business administration, social science, biosciences, and humanities education, library sciences management, depiction of data and structural illustration, big data analytics, information economics in real engineering and scientific problems.
This journal provides a forum that impacts the development of engineering, education, technology management, information theories and application validation. It also acts as a path to exchange novel and innovative ideas about Information systems science and technology.
A NOVEL APPROACH FOR SEGMENTATION OF SECTOR SCAN SONAR IMAGES USING ADAPTIVE ...

The SAR and SAS images are perturbed by a multiplicative noise called speckle, due to the coherent nature of the scattering phenomenon. If the background of an image is uneven, the fixed thresholding technique is not suitable to segment an image using adaptive thresholding method. In this paper a new Adaptive thresholding method is proposed to reduce the speckle noise, preserving the structural features and textural information of Sector Scan SONAR (Sound Navigation and Ranging) images. Due to the massive proliferation of SONAR images, the proposed method is very appealing in under water environment applications. In fact it is a pre- treatment required in any SONAR images analysis system. The results obtained from the proposed method were compared quantitatively and qualitatively with the results obtained from the other speckle reduction techniques and demonstrate its higher performance for speckle reduction in the SONAR images.
Call for Papers - International Journal of Information Sciences and Technique...

The International Journal of Information Science & Techniques (IJIST) focuses on information systems science and technology coercing multitude applications of information systems in business administration, social science, biosciences, and humanities education, library sciences management, depiction of data and structural illustration, big data analytics, information economics in real engineering and scientific problems.
This journal provides a forum that impacts the development of engineering, education, technology management, information theories and application validation. It also acts as a path to exchange novel and innovative ideas about Information systems science and technology.
More from ijistjournal (20)
Call for Research Articles - 5th International Conference on Artificial Intel...

Call for Research Articles - 5th International Conference on Artificial Intel...
Online Paper Submission - International Journal of Information Sciences and T...

Online Paper Submission - International Journal of Information Sciences and T...
SYSTEM IDENTIFICATION AND MODELING FOR INTERACTING AND NON-INTERACTING TANK S...

SYSTEM IDENTIFICATION AND MODELING FOR INTERACTING AND NON-INTERACTING TANK S...
Call for Research Articles - 4th International Conference on NLP & Data Minin...

Call for Research Articles - 4th International Conference on NLP & Data Minin...
Research Article Submission - International Journal of Information Sciences a...

Research Article Submission - International Journal of Information Sciences a...
Call for Papers - International Journal of Information Sciences and Technique...

Call for Papers - International Journal of Information Sciences and Technique...
Implementation of Radon Transformation for Electrical Impedance Tomography (EIT)

Implementation of Radon Transformation for Electrical Impedance Tomography (EIT)
Online Paper Submission - 6th International Conference on Machine Learning & ...

Online Paper Submission - 6th International Conference on Machine Learning & ...
Submit Your Research Articles - International Journal of Information Sciences...

Submit Your Research Articles - International Journal of Information Sciences...
BER Performance of MPSK and MQAM in 2x2 Almouti MIMO Systems

BER Performance of MPSK and MQAM in 2x2 Almouti MIMO Systems
Online Paper Submission - International Journal of Information Sciences and T...

Online Paper Submission - International Journal of Information Sciences and T...
Call for Papers - International Journal of Information Sciences and Technique...

Call for Papers - International Journal of Information Sciences and Technique...
International Journal of Information Sciences and Techniques (IJIST)

International Journal of Information Sciences and Techniques (IJIST)
BRAIN TUMOR MRIIMAGE CLASSIFICATION WITH FEATURE SELECTION AND EXTRACTION USI...

BRAIN TUMOR MRIIMAGE CLASSIFICATION WITH FEATURE SELECTION AND EXTRACTION USI...
Research Article Submission - International Journal of Information Sciences a...

Research Article Submission - International Journal of Information Sciences a...
A MEDIAN BASED DIRECTIONAL CASCADED WITH MASK FILTER FOR REMOVAL OF RVIN

A MEDIAN BASED DIRECTIONAL CASCADED WITH MASK FILTER FOR REMOVAL OF RVIN
DECEPTION AND RACISM IN THE TUSKEGEE SYPHILIS STUDY

DECEPTION AND RACISM IN THE TUSKEGEE SYPHILIS STUDY
Online Paper Submission - International Journal of Information Sciences and T...

Online Paper Submission - International Journal of Information Sciences and T...
A NOVEL APPROACH FOR SEGMENTATION OF SECTOR SCAN SONAR IMAGES USING ADAPTIVE ...

A NOVEL APPROACH FOR SEGMENTATION OF SECTOR SCAN SONAR IMAGES USING ADAPTIVE ...
Call for Papers - International Journal of Information Sciences and Technique...

Call for Papers - International Journal of Information Sciences and Technique...
Recently uploaded
Slack (or Teams) Automation for Bonterra Impact Management (fka Social Soluti...

Sidekick Solutions uses Bonterra Impact Management (fka Social Solutions Apricot) and automation solutions to integrate data for business workflows.
We believe integration and automation are essential to user experience and the promise of efficient work through technology. Automation is the critical ingredient to realizing that full vision. We develop integration products and services for Bonterra Case Management software to support the deployment of automations for a variety of use cases.
This video focuses on the notifications, alerts, and approval requests using Slack for Bonterra Impact Management. The solutions covered in this webinar can also be deployed for Microsoft Teams.
Interested in deploying notification automations for Bonterra Impact Management? Contact us at sales@sidekicksolutionsllc.com to discuss next steps.
GenAISummit 2024 May 28 Sri Ambati Keynote: AGI Belongs to The Community in O...

“AGI should be open source and in the public domain at the service of humanity and the planet.”
Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head...

Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head of Product, Amazon Games
PHP Frameworks: I want to break free (IPC Berlin 2024)

In this presentation, we examine the challenges and limitations of relying too heavily on PHP frameworks in web development. We discuss the history of PHP and its frameworks to understand how this dependence has evolved. The focus will be on providing concrete tips and strategies to reduce reliance on these frameworks, based on real-world examples and practical considerations. The goal is to equip developers with the skills and knowledge to create more flexible and future-proof web applications. We'll explore the importance of maintaining autonomy in a rapidly changing tech landscape and how to make informed decisions in PHP development.
This talk is aimed at encouraging a more independent approach to using PHP frameworks, moving towards a more flexible and future-proof approach to PHP development.
Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf

91mobiles recently conducted a Smart TV Buyer Insights Survey in which we asked over 3,000 respondents about the TV they own, aspects they look at on a new TV, and their TV buying preferences.
State of ICS and IoT Cyber Threat Landscape Report 2024 preview

The IoT and OT threat landscape report has been prepared by the Threat Research Team at Sectrio using data from Sectrio, cyber threat intelligence farming facilities spread across over 85 cities around the world. In addition, Sectrio also runs AI-based advanced threat and payload engagement facilities that serve as sinks to attract and engage sophisticated threat actors, and newer malware including new variants and latent threats that are at an earlier stage of development.
The latest edition of the OT/ICS and IoT security Threat Landscape Report 2024 also covers:
State of global ICS asset and network exposure
Sectoral targets and attacks as well as the cost of ransom
Global APT activity, AI usage, actor and tactic profiles, and implications
Rise in volumes of AI-powered cyberattacks
Major cyber events in 2024
Malware and malicious payload trends
Cyberattack types and targets
Vulnerability exploit attempts on CVEs
Attacks on counties – USA
Expansion of bot farms – how, where, and why
In-depth analysis of the cyber threat landscape across North America, South America, Europe, APAC, and the Middle East
Why are attacks on smart factories rising?
Cyber risk predictions
Axis of attacks – Europe
Systemic attacks in the Middle East
Download the full report from here:
https://sectrio.com/resources/ot-threat-landscape-reports/sectrio-releases-ot-ics-and-iot-security-threat-landscape-report-2024/
Essentials of Automations: Optimizing FME Workflows with Parameters

Are you looking to streamline your workflows and boost your projects’ efficiency? Do you find yourself searching for ways to add flexibility and control over your FME workflows? If so, you’re in the right place.
Join us for an insightful dive into the world of FME parameters, a critical element in optimizing workflow efficiency. This webinar marks the beginning of our three-part “Essentials of Automation” series. This first webinar is designed to equip you with the knowledge and skills to utilize parameters effectively: enhancing the flexibility, maintainability, and user control of your FME projects.
Here’s what you’ll gain:
- Essentials of FME Parameters: Understand the pivotal role of parameters, including Reader/Writer, Transformer, User, and FME Flow categories. Discover how they are the key to unlocking automation and optimization within your workflows.
- Practical Applications in FME Form: Delve into key user parameter types including choice, connections, and file URLs. Allow users to control how a workflow runs, making your workflows more reusable. Learn to import values and deliver the best user experience for your workflows while enhancing accuracy.
- Optimization Strategies in FME Flow: Explore the creation and strategic deployment of parameters in FME Flow, including the use of deployment and geometry parameters, to maximize workflow efficiency.
- Pro Tips for Success: Gain insights on parameterizing connections and leveraging new features like Conditional Visibility for clarity and simplicity.
We’ll wrap up with a glimpse into future webinars, followed by a Q&A session to address your specific questions surrounding this topic.
Don’t miss this opportunity to elevate your FME expertise and drive your projects to new heights of efficiency.
Leading Change strategies and insights for effective change management pdf 1.pdf

Leading Change strategies and insights for effective change management pdf 1.pdf
GraphRAG is All You need? LLM & Knowledge Graph

Guy Korland, CEO and Co-founder of FalkorDB, will review two articles on the integration of language models with knowledge graphs.
1. Unifying Large Language Models and Knowledge Graphs: A Roadmap.
https://arxiv.org/abs/2306.08302
2. Microsoft Research's GraphRAG paper and a review paper on various uses of knowledge graphs:
https://www.microsoft.com/en-us/research/blog/graphrag-unlocking-llm-discovery-on-narrative-private-data/
Empowering NextGen Mobility via Large Action Model Infrastructure (LAMI): pav...

Empowering NextGen Mobility via Large Action Model Infrastructure (LAMI)
Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024

As AI technology is pushing into IT I was wondering myself, as an “infrastructure container kubernetes guy”, how get this fancy AI technology get managed from an infrastructure operational view? Is it possible to apply our lovely cloud native principals as well? What benefit’s both technologies could bring to each other?
Let me take this questions and provide you a short journey through existing deployment models and use cases for AI software. On practical examples, we discuss what cloud/on-premise strategy we may need for applying it to our own infrastructure to get it to work from an enterprise perspective. I want to give an overview about infrastructure requirements and technologies, what could be beneficial or limiting your AI use cases in an enterprise environment. An interactive Demo will give you some insides, what approaches I got already working for real.
Mission to Decommission: Importance of Decommissioning Products to Increase E...

Mission to Decommission: Importance of Decommissioning Products to Increase Enterprise-Wide Efficiency by VP Data Platform, American Express
AI for Every Business: Unlocking Your Product's Universal Potential by VP of ...

AI for Every Business: Unlocking Your Product's Universal Potential by VP of Product, Slack
Search and Society: Reimagining Information Access for Radical Futures

The field of Information retrieval (IR) is currently undergoing a transformative shift, at least partly due to the emerging applications of generative AI to information access. In this talk, we will deliberate on the sociotechnical implications of generative AI for information access. We will argue that there is both a critical necessity and an exciting opportunity for the IR community to re-center our research agendas on societal needs while dismantling the artificial separation between the work on fairness, accountability, transparency, and ethics in IR and the rest of IR research. Instead of adopting a reactionary strategy of trying to mitigate potential social harms from emerging technologies, the community should aim to proactively set the research agenda for the kinds of systems we should build inspired by diverse explicitly stated sociotechnical imaginaries. The sociotechnical imaginaries that underpin the design and development of information access technologies needs to be explicitly articulated, and we need to develop theories of change in context of these diverse perspectives. Our guiding future imaginaries must be informed by other academic fields, such as democratic theory and critical theory, and should be co-developed with social science scholars, legal scholars, civil rights and social justice activists, and artists, among others.
When stars align: studies in data quality, knowledge graphs, and machine lear...

Keynote at DQMLKG workshop at the 21st European Semantic Web Conference 2024
UiPath Test Automation using UiPath Test Suite series, part 3

Welcome to UiPath Test Automation using UiPath Test Suite series part 3. In this session, we will cover desktop automation along with UI automation.
Topics covered:
UI automation Introduction,
UI automation Sample
Desktop automation flow
Pradeep Chinnala, Senior Consultant Automation Developer @WonderBotz and UiPath MVP
Deepak Rai, Automation Practice Lead, Boundaryless Group and UiPath MVP
Recently uploaded (20)
Slack (or Teams) Automation for Bonterra Impact Management (fka Social Soluti...

Slack (or Teams) Automation for Bonterra Impact Management (fka Social Soluti...
GenAISummit 2024 May 28 Sri Ambati Keynote: AGI Belongs to The Community in O...

GenAISummit 2024 May 28 Sri Ambati Keynote: AGI Belongs to The Community in O...
Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head...

Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head...
PHP Frameworks: I want to break free (IPC Berlin 2024)

PHP Frameworks: I want to break free (IPC Berlin 2024)
Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf

Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf
State of ICS and IoT Cyber Threat Landscape Report 2024 preview

State of ICS and IoT Cyber Threat Landscape Report 2024 preview
Essentials of Automations: Optimizing FME Workflows with Parameters

Essentials of Automations: Optimizing FME Workflows with Parameters
FIDO Alliance Osaka Seminar: Passkeys and the Road Ahead.pdf

FIDO Alliance Osaka Seminar: Passkeys and the Road Ahead.pdf
Leading Change strategies and insights for effective change management pdf 1.pdf

Leading Change strategies and insights for effective change management pdf 1.pdf
Empowering NextGen Mobility via Large Action Model Infrastructure (LAMI): pav...

Empowering NextGen Mobility via Large Action Model Infrastructure (LAMI): pav...
Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024

Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024
Mission to Decommission: Importance of Decommissioning Products to Increase E...

Mission to Decommission: Importance of Decommissioning Products to Increase E...
AI for Every Business: Unlocking Your Product's Universal Potential by VP of ...

AI for Every Business: Unlocking Your Product's Universal Potential by VP of ...
Search and Society: Reimagining Information Access for Radical Futures

Search and Society: Reimagining Information Access for Radical Futures
When stars align: studies in data quality, knowledge graphs, and machine lear...

When stars align: studies in data quality, knowledge graphs, and machine lear...
FIDO Alliance Osaka Seminar: Passkeys at Amazon.pdf

FIDO Alliance Osaka Seminar: Passkeys at Amazon.pdf
UiPath Test Automation using UiPath Test Suite series, part 3

UiPath Test Automation using UiPath Test Suite series, part 3
Secured wireless power
- 1. International Journal of Information Sciences and Techniques (IJIST) Vol.4, No.3, May 2014 DOI : 10.5121/ijist.2014.4315 115 SECURED WIRELESS POWER TRANSMISSION USING RADIO FREQUENCY SIGNAL B. Renil Randy1 , M.Hariharan2 , R. Arasa Kumar3 1,2 UG Students, 3 Assistant Professor Velammal College of Engineering and Technology, Madurai ABSTRACT: Anything we transmit without protection is being raid by the intruders. Hence it is necessary to impart security to the signal transmitted. In this paper we present the concept of giving security to the transmitted power signal which is to be received by a receiver in a wireless medium. The present techniques of wireless power transmission consists of a pair of strongly magnetically coupled resonators that allow power transmission of tens of watts over a few meters, but anything without security becomes unreliable. With the goal in achieving security to the power signal, we introduce the concept of encryption decryption algorithm using RF module. 1. INTRODUCTION: The inspiration for wireless power comes from wires being cumbersome and messy. With the numerous number of mobile electronics that we use today, there is a huge demand for convenience in supervision of their power supplies. Wireless communication hasmade a massive developmentin the way we interact with communication devices. We also observe that while the techniques of strongly coupled magnetic resonances allowefficient power transfer between a pair of transmitter and receiver coils, the efficiency greatlydeclines upon adding more receivers to the strongly coupled system due to theinteraction between multiple coupled resonators. In tightly coupled resonant wirelesspower transfer, we require a one to one contact between transmitter andreceiver. In addition, in order to improve efficiency of power transfer, we intend to use a lower switching frequency to drive the gate of the MOSFET. 2. WIRELESS POWER TRANSMISSION (WPT) SYSTEM: We cannot imagine the world without electric power. Normally the power is transmitted through wires. This paper depicts an idea to eradicate the hazardous usage of electrical wires which involve lot of confusion in particularly organizing them. Wireless Power Transmission system would completely eliminate the dynamic high-tension power transmission cables, towers and secondary stations between the generating station and consumers and facilitates the interconnection of electrical generation plants on global scale. Mobile transmitters and receivers can be chosen for the Wireless Power Transmission system. The cost for transmission and distribution will be reduced and the cost of electrical energy for the consumers also would be diminished. The power could also be transmitted to the places where the wired transmission is not possible.
- 2. International Journal of Information Sciences and Techniques (IJIST) Vol.4, No.3, May 2014 116 2.1.VARIOUS SCHEMES OF WIRELESS POWER TRANSFER: There are many techniques which are being used to achieve wireless power transfer. Some of the methods are being discussed below. 2.1.1. WPT using Microwaves: In the transmission side, the microwave power source generates microwave power and the output power is managed by electronic restrain circuits. The purpose of the tuner is to match the impedance between the transmitting antenna and the microwave source. The attenuated signals gets divided based on the direction of signal propagation by Directional Coupler. The transmitting antenna emits the power uniformly through free space to the rectenna. In the receiving section, a rectenna receives the transmitted power and translates the microwave power to DC power. The impedance matching circuit and the filter is provided for setting the output impedance of a signal source equal to the rectifying circuit. The rectifying circuit haveSchottky barrier diodes which converts the received microwave power into DC power. 2.1.2. WPT using Magnetic Resonance: In this technique, at first we design an oscillator, which generates the carrier signal to transmit the power. Oscillators are not usually designed to deliver power, thus a power amplifier is added to the oscillator to amplify the oscillating signal. The power amplifier would hand over the output power to the transmission coil. Next, a receiver coil is constructed to receive the transmitted power. However, the power received in the receiver side have an alternating current. Thus, a rectifier is needed to rectify the AC voltage. Finally, an electric load is attached to finish the entire circuit design. Figure1. WPT using Magnetic Resonance 2.1.3WPT using Space Solar power (SSP)Satellites: In this method, there are two basic WPT options, one is using radio waves and the other is using light waves, are considered for both long term and short term Space Solar power applications. In the long term, power is transferred to Earth from Geostationary earth orbit (GEO), or further distances in the space. In the near term the power is being transmitted to the moderate distances. By using SSP and WPT technology in near term space science and exploration missions, larger systems are being designed and developed to send power from space to Earth.
- 3. International Journal of Information Sciences and Techniques (IJIST) Vol.4, No.3, May 2014 117 3. BLOCK DIAGRAM: The block diagram for the overall wireless power transceiver is given in the following figure(Fig. 1) Figure 2. Overall Block Diagram of Wireless power Transceiver 4. TRANSMITTER: The following diagram gives the entire transmitter section of the Wireless Power Transmission. The 230V alternating current is fed to the transformer is rectified with bridge rectifier in which the alternating current is converted to Direct Currentand it is filtered and regulated with the voltage regulator. The flow of the signal without any interrupt to the transmitter input is denoted by an LED. It consists of a RESET switch denoted by which is used to reset the programming codes in the picmicrocontroller. The signal is given to the PIC microcontroller PIC16F877A which has 40 pins and it has 5 input output pins and fifteen interrupts and its stability is maintained with a crystal oscillator circuit. This signal will be controlled by the pic microcontroller and the status of the signal is being informed with a help of an LCD display. This signal is being transferred to the RF module through MAX 232. Four MOSFET switches are being connected to each other so that current can pass through, by the switching between the ON and OFF states and the passcode will be generated in MAX 232 and sent through RFtransmitter.
- 4. International Journal of Information Sciences and Techniques (IJIST) Vol.4, No.3, May 2014 118 Figure 3. Transmitter diagram 5. RECEIVER: The receiver operation is just the vice versa of the transmitter. The signal is being received to the receiving antenna from the transmitting antenna. The signalthat transmitted from the RF transmitter will reachesthe RF module at the receiver. There is no separate power supply for the receiver section. The current induced in the induction coil is given to the secondary coil of the transformer. In the receiver section, only one MOSFET switch is used which allows current only in the ON state ie, when the signal reaches the RF receiver it will send the passcode to the MAX 232 when the passcode matches then it will trigger the circuit and makes MOSFET switch in ON condition. The current passes to ensure that only the authenticated receiver receives the power signal. Figure 4. Receiver diagram 6. RESULTS: From the plots given, we come to infer that efficiency of the system has been increased using various parameters when compared to that of the efficiencies of the existing system. Thus the International Journal of Information Sciences and Techniques (IJIST) Vol.4, No.3, May 2014 118 Figure 3. Transmitter diagram 5. RECEIVER: The receiver operation is just the vice versa of the transmitter. The signal is being received to the receiving antenna from the transmitting antenna. The signalthat transmitted from the RF transmitter will reachesthe RF module at the receiver. There is no separate power supply for the receiver section. The current induced in the induction coil is given to the secondary coil of the transformer. In the receiver section, only one MOSFET switch is used which allows current only in the ON state ie, when the signal reaches the RF receiver it will send the passcode to the MAX 232 when the passcode matches then it will trigger the circuit and makes MOSFET switch in ON condition. The current passes to ensure that only the authenticated receiver receives the power signal. Figure 4. Receiver diagram 6. RESULTS: From the plots given, we come to infer that efficiency of the system has been increased using various parameters when compared to that of the efficiencies of the existing system. Thus the International Journal of Information Sciences and Techniques (IJIST) Vol.4, No.3, May 2014 118 Figure 3. Transmitter diagram 5. RECEIVER: The receiver operation is just the vice versa of the transmitter. The signal is being received to the receiving antenna from the transmitting antenna. The signalthat transmitted from the RF transmitter will reachesthe RF module at the receiver. There is no separate power supply for the receiver section. The current induced in the induction coil is given to the secondary coil of the transformer. In the receiver section, only one MOSFET switch is used which allows current only in the ON state ie, when the signal reaches the RF receiver it will send the passcode to the MAX 232 when the passcode matches then it will trigger the circuit and makes MOSFET switch in ON condition. The current passes to ensure that only the authenticated receiver receives the power signal. Figure 4. Receiver diagram 6. RESULTS: From the plots given, we come to infer that efficiency of the system has been increased using various parameters when compared to that of the efficiencies of the existing system. Thus the
- 5. 119 concept of presenting the idea of providing security to the transmitted signal in the wireless medium and receiving is attained is done for a limited space in small scale. This would also become base for the further research in transmitting and receiving signals in a large scale through anyone one of the above listed techniques. Table 1. Result of current by varying distance of receiver Distance (feet) Voltage (Volts) Current (mA) 3 4 500 2 4.5 550 1 5 600 0.5 5.5 750 Maximum closest position 6 1000 From the above observations, the power transferred from the transmitter to the receiver is maximum at the closest position and when the distance between them is increased, the power received in the receiver gets reduced. When the transmitter is switched to the port of the receiver A, we are able to observe that the LED on the receiver A glows and the LED in the receiver coil B doesn’t glow since receive B is not the authenticated user to use the power signal. Any metal sheet obstacle when placed between
- 6. 120 the transmitter and the receiver, it is found that the power is transmitted to the authenticated user as the metal sheet is a conductor. Table 2. Result of temperature with varying distance Distance (feet) Temperature (°C) 3 27 2 27.7 1 28.2 0.5 29.5 Maximum closest position 30 From the above tabulation, we find that the temperature in the receiver coil gets increased when the when the distance the distance between the transmitter and the receiver is decreased Table 3. Result on transmitter coil heating PWM On duty Time Transmitter coil heating (°C) 100% 45 90% 43 80% 41 70% 40 60% 38 From the above observations, we find that at the temperature of the transmitter coil is high when the ON duty time of the Pulse width modulation (PWM) is maximum.
- 7. 121 When the transmitter is neither switched to the receiver of port A nor port B ie, the switch is held in the middle. Then both the receiver A and B can't receive the power since both the receivers are not authenticated even though the power is transmitted in the air and the coil induces it. The four MOSFET which is being connected in series helps in switching the current. The amount of power received in the receiver varies when the distance between the transmitter and the receiver varies as discussed. 7. CONCLUSION: We have placed two receivers with decoders which decodes the passcode given as coding to the RF module in the transmitter section. The receiver which has the matched passcode decoded has received the power signal successfully. The receiver with the decoder decoding a passcode mismatch failed to receive the power signal. Our project can also be implemented in Online Electric Vehicle (OLEV). OLEV wireless charging system consists of a road-side Power Inverter to bring electricity from the grid to the road embedded power tracks. A proprietary Roadway Infrastructure consisting of Road-embedded Power tracks installed at selected locations of the route.A proprietary Pick-Up and Regulator kit for the wireless power transfer installed in or under the electric vehicle. Hence in this system the unauthorised users are denied permission to use the power source using the key idea of the project.
- 8. 122 REFERENCES: [1] S. Kopparthi, Pratul K. Ajmera, "Power delivery for remotely located Microsystems," [2] Proc. of IEEE Region 5, 2004 Annual Tech. Conference, 2004 April 2, pp. 31-39. [3] Nikola Tesla, “The Transmission of Electrical Energy Without Wires as a Means for Furthering Peace,” Electrical World and Engineer. Jan. 7, p. 21, 1985. [4] T. Deyle and M. Reynolds, “Surface based wireless power transmission and bidirectional communication for autonomous robot swarms” in Proceedings IEEE Conference on Robotics, 2008. [5] M. Ghovanloo, et al., “A Wide-band Power-efficient Inductive Wireless Link for Implantable Microelectronic Devices Using Multiple Carriers,” IEEE Trans. Circuits and Systems, vol. 54, no. 10, October 2007. [6] K. M. Silay, et al., “Improvement of Power Efficiency of Inductive Links for Implantable Devices,” Research in Microelectronics and Electronics, pp. 229-232, June 2008. AUTHORS: B. Renil Randy is doing his B.E. degree in Velammal College of Engineering and Technology, Madurai, India. He is interested in the area of Wireless Communication and Signal Processing. M. Hariharanis doing his B.E. degree in Velammal College of Engineering and Technology, Madurai, India. He is intere sted in the area of Wireless Communication and specialized in Wireless Power Transmission. R. Arasa Kumar,M.E.is working as Assistant Professor in Velammal College of Engineering and Technology, Madurai. He also has teachin g experience at Kalasalingam Institute of Technology, Krishnakoil. He was graduated at MepcoSchlenk Engineering College, Sivakasi.
