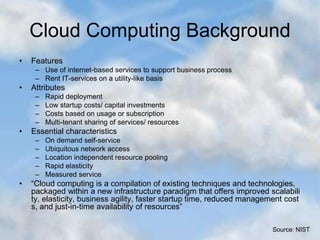
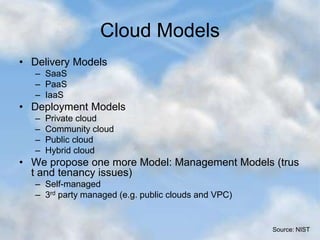
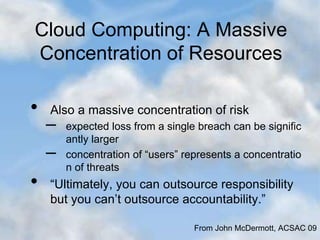
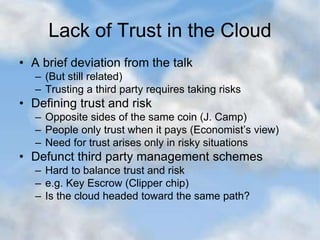
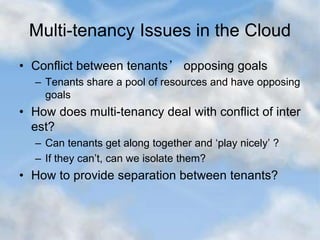
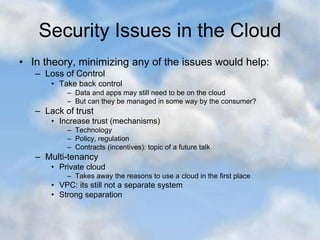
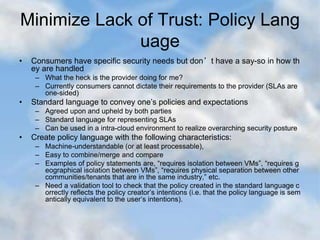
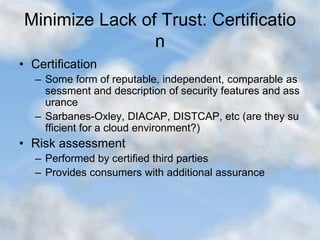
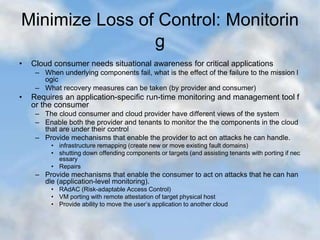
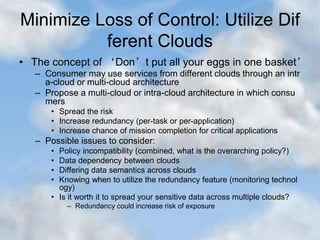
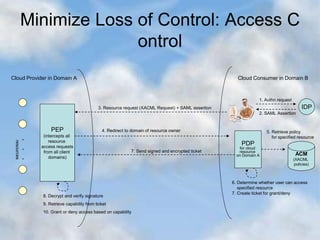
This document discusses security issues in cloud computing. It begins with an overview of cloud computing characteristics such as on-demand self-service, ubiquitous network access, and resource pooling. It then discusses some common security problems in cloud computing including loss of control, lack of trust, and multi-tenancy issues that stem from sharing resources with multiple tenants. Approaches proposed to address these issues include increasing monitoring and control for customers, utilizing multiple clouds to spread risk, developing standardized policy languages and certification processes to build trust, and enhancing isolation between tenants. The document provides references and concludes by emphasizing the need to consider security at both the cloud provider level and on local devices used to access cloud services.