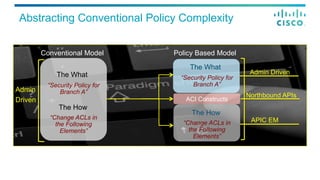
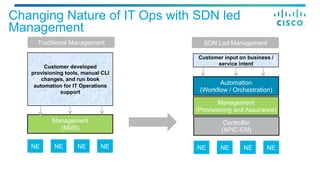
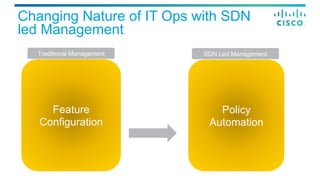
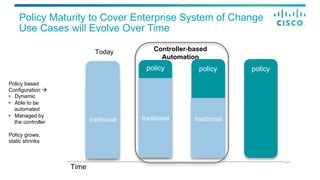
The document discusses Cisco's Application Policy Infrastructure Controller Enterprise Module (APIC-EM). It provides:
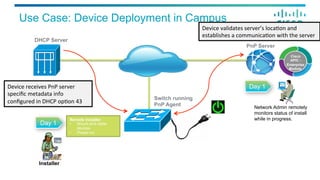
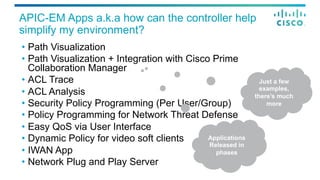
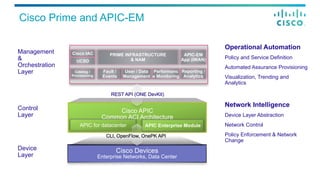
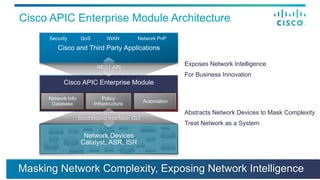
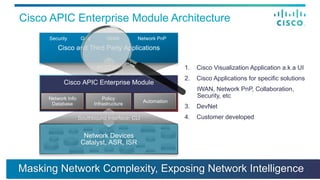
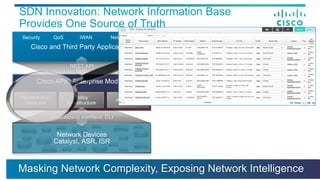
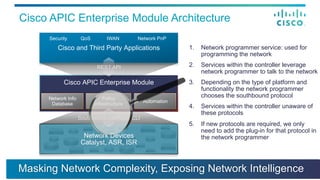
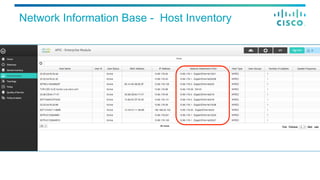
1) An overview of the APIC-EM architecture, which includes Cisco and third party applications, a network information database, policy infrastructure, and automation interfaces to simplify network management and expose network intelligence.
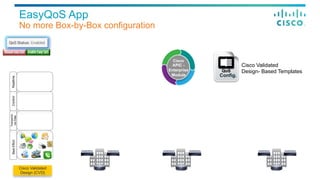
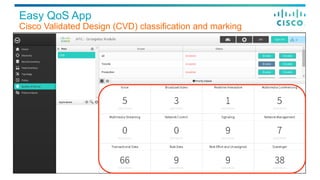
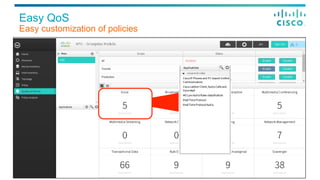
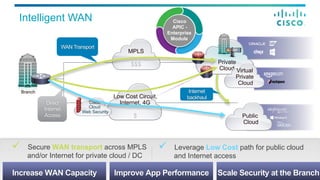
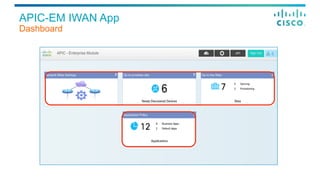
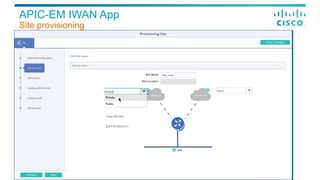
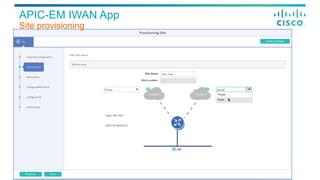
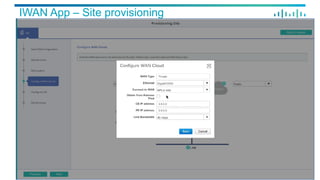
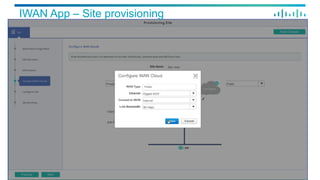
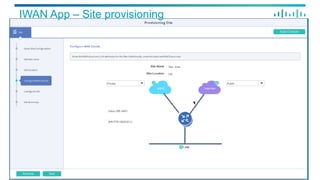
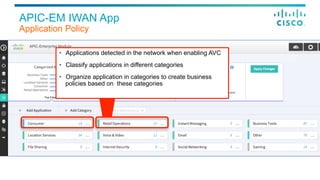
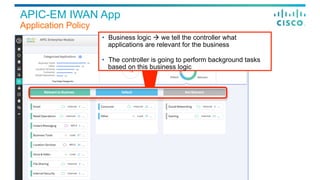
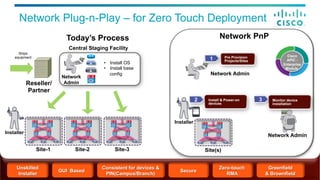
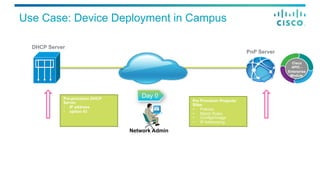
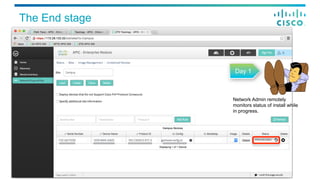
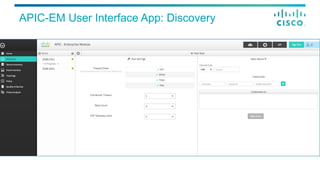
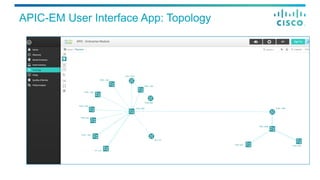
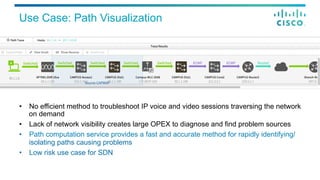
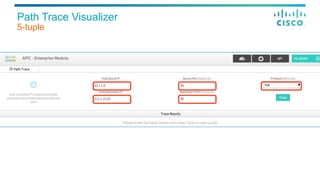
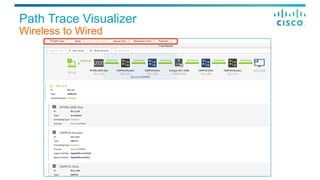
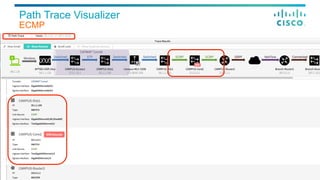
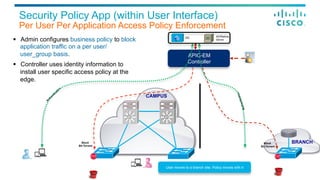
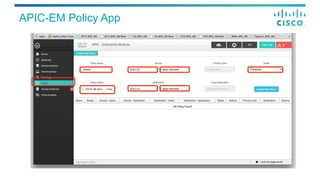
2) Examples of APIC-EM applications like path visualization, policy analysis, EasyQoS, Intelligent WAN, and Network Plug and Play that provide simplified management of networks, applications, and policies through an intuitive user interface and programming interfaces.
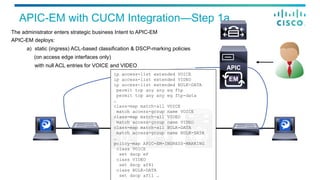
3) Details on how APIC-EM can integrate with Cisco Call Manager to dynamically insert and remove access control lists for voice and video calls to prioritize that traffic
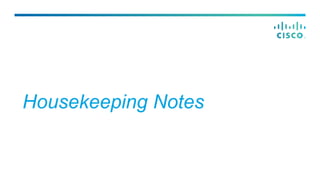
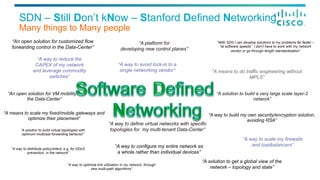





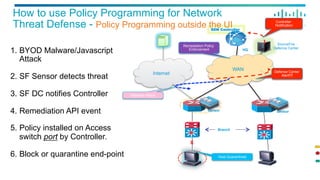
![How to use Policy Programming for Network
Threat Defense - Policy Programming outside the UI
Branch
SourceFire
Defence Center
SDN Controller
ISR
Sensor
X
Sensor
WAN
ISR
Internet
HQ
Controller
Notification
Host Quarantined
Defense Center
/api/v0/policy POST!
{"actions": ["DENY"],
"policyOwner":"admin”,
"policyName": "deny_all”,
"networkUser":
{"userIdentifiers”:
["10.10.20.7"]}}!](https://image.slidesharecdn.com/t-enm-01-ilrousseaszigeti-150520165539-lva1-app6891/85/SDN-in-the-Enterprise-APIC-Enterprise-Module-37-320.jpg)