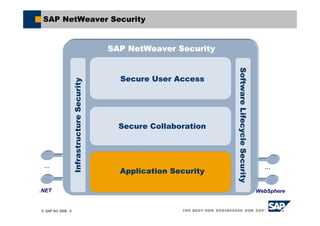
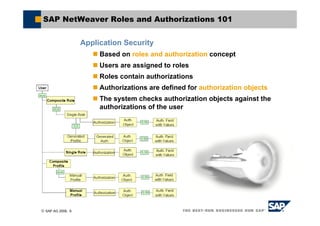
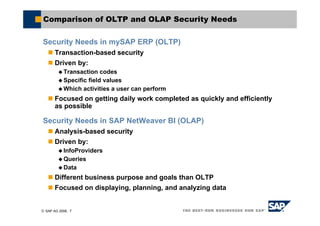
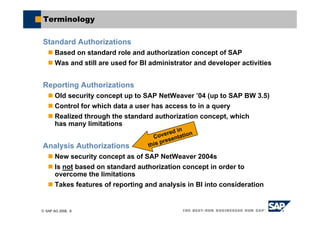
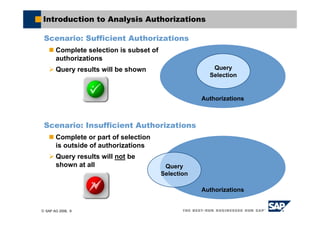
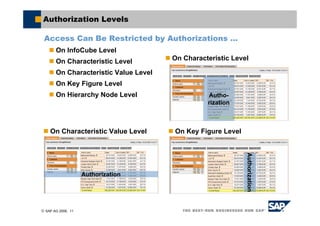
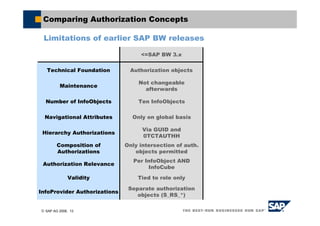
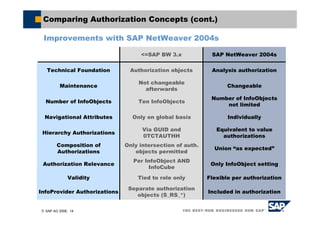
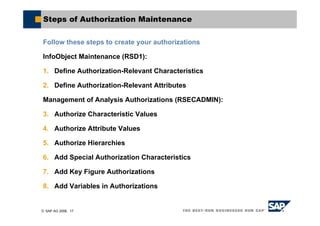
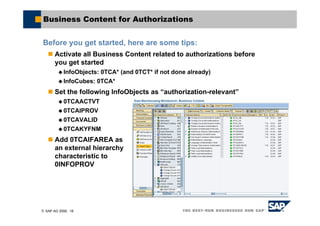
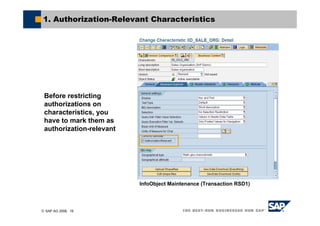
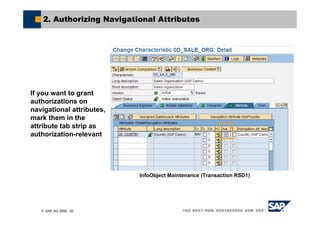
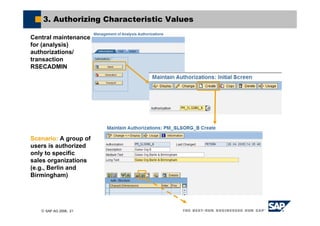
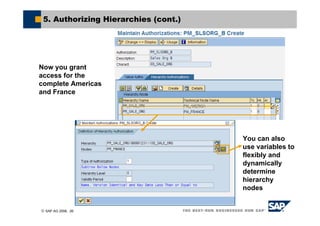
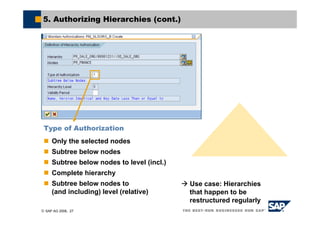
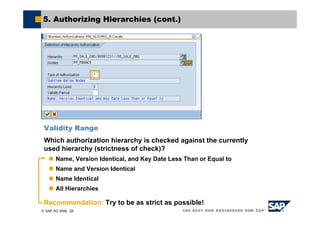
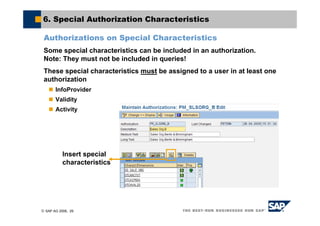
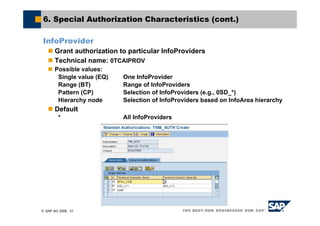
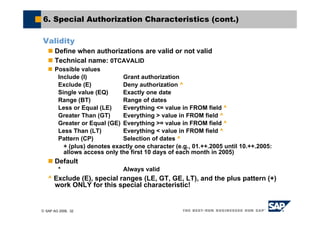
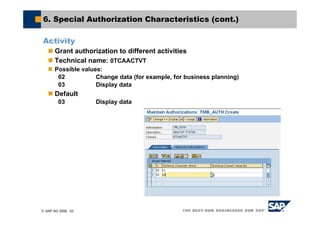
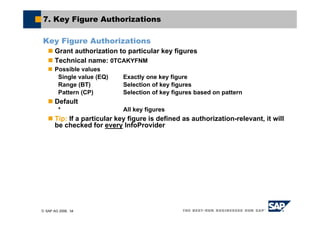
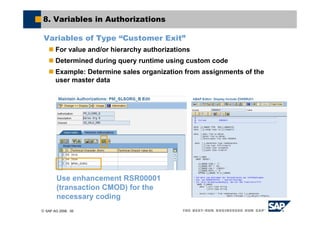
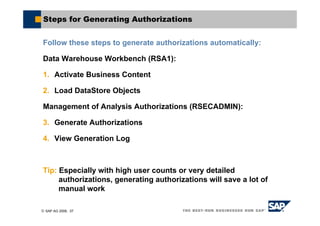
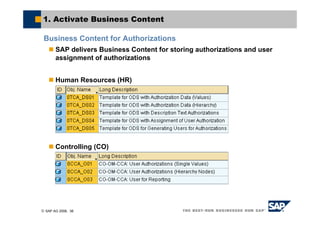
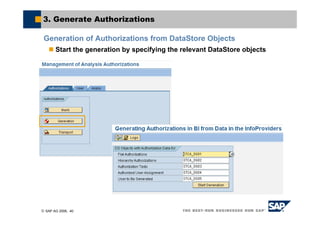
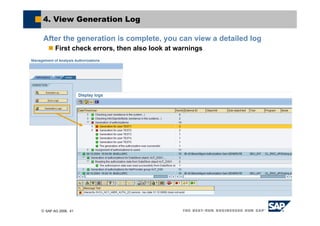
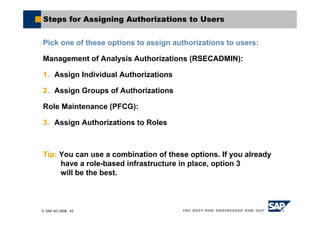
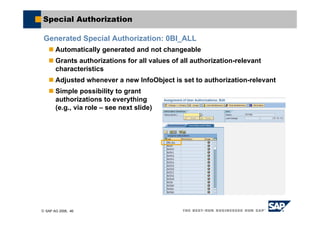
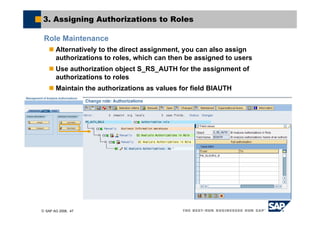
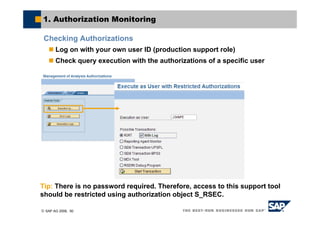
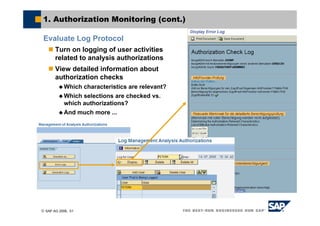
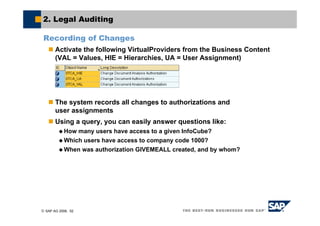
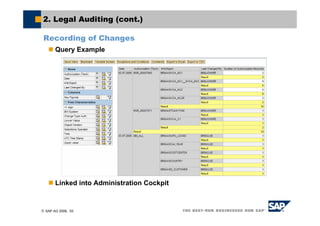
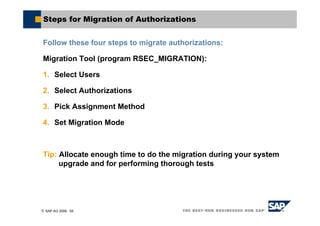
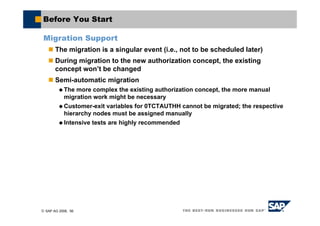
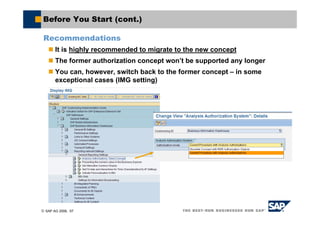
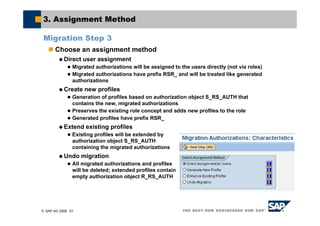
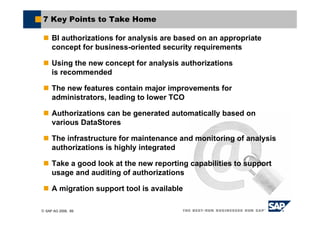
This document provides an overview of new security features for SAP BI, including analysis authorizations. It discusses the steps to create, maintain, and assign authorizations, as well as tools for monitoring, auditing, and testing authorizations. The key topics covered include a comparison of old and new authorization concepts, authorization maintenance, generating authorizations automatically, assigning authorizations to users and roles, and migration tools.