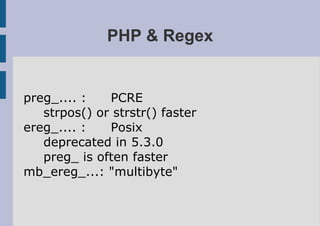
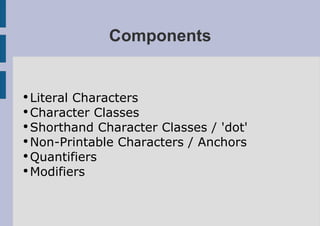
Regular expressions (regex) allow defining patterns to match in text strings using special characters like ., *, + to match types of characters or ranges. They have components like literal characters, character classes, shorthand classes, quantifiers and modifiers that define what is matched. PHP supports both PCRE and POSIX regex with functions like preg_match() and ereg_replace() as well as online tools for testing regular expressions.

![Character Classes
●
Groups of character
[abcdefgh0123]
●
Range of character
[a-h0-3]
●
Inverse Range of Character
[^i-z4-9]
e.g. /[gG]uide[lL]ine/ -> guideline or
guideLine](https://image.slidesharecdn.com/regexpresentatie-090703040338-phpapp01/85/Regex-Presentation-5-320.jpg)
![Shorthand Char. Classes
d -> [0-9]
w -> [a-zA-Z]
s -> whitespace + [trn]
negative:
D -> [^0-9]
W -> [^a-zA-Z]
S
'.' -> any character!!](https://image.slidesharecdn.com/regexpresentatie-090703040338-phpapp01/85/Regex-Presentation-6-320.jpg)