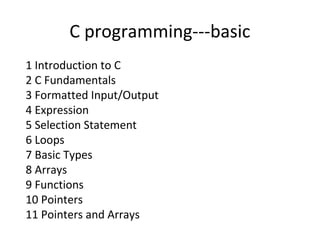
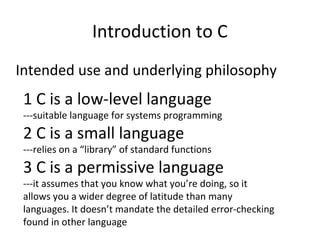
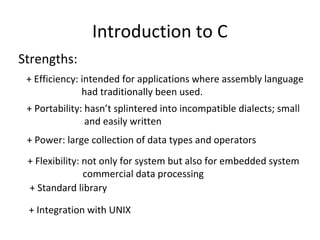
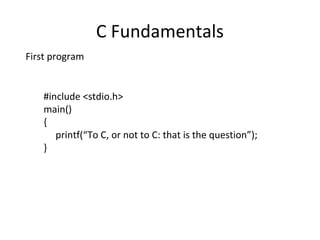
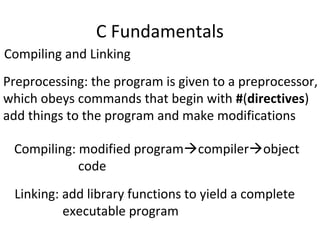
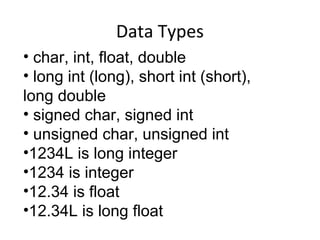
C is a low-level programming language suitable for systems programming. It is small but powerful, with a large collection of data types and operators. It assumes the programmer knows what they are doing and does not mandate extensive error checking. The document discusses the basics of C including data types, operators, input/output, expressions, selection statements, loops, functions, and pointers. It provides examples of basic C programs and comparisons between C and Java.
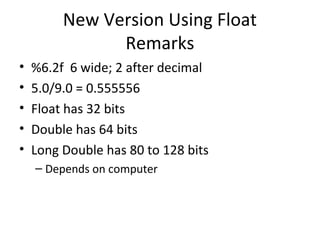
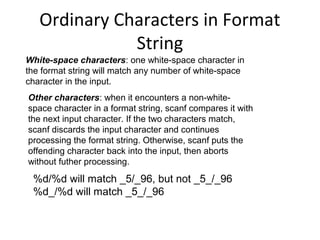
![Formatted Input/Output
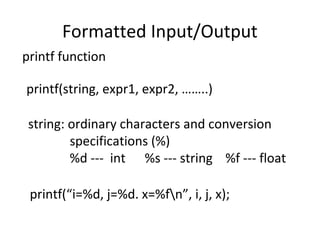
Conversion Specification
%[-]m.pX
m: specifies the minimum number of characters to print.
%4d-- _123; %-4--123_
p: depends on the choice of X
X:
-d: decimal form
-e: floating-point number in exponential format
-f: floating-point number in “fixed decimal” format
-g: either exponential format or fixed decimal format,
depending on the number’s size](https://image.slidesharecdn.com/cbasic-140516010239-phpapp01/85/Cbasic-26-320.jpg)
![Conditional Expressions
• Conditional expressions
• expr1? expr2:expr3;
• if expr1 is true then expr2 else expr3
for (i=0; i<n; i++)
printf("%6d %c",a[i],(i%10==9||i==(n1))?'n':' ');](https://image.slidesharecdn.com/cbasic-140516010239-phpapp01/85/Cbasic-37-320.jpg)