RC4 is a stream cipher created in 1987. It was initially a trade secret but was later posted online. RC4 is fast and simple to implement, making it popular despite weaknesses in its key scheduling algorithm. RC4 has a large key space but around 1 in 256 keys are weak. Attacks exist against RC4's KSA that can help determine parts of the encryption key. While RC4 remains in common use, its weaknesses have led experts to recommend moving away from its use where possible.

![KSA
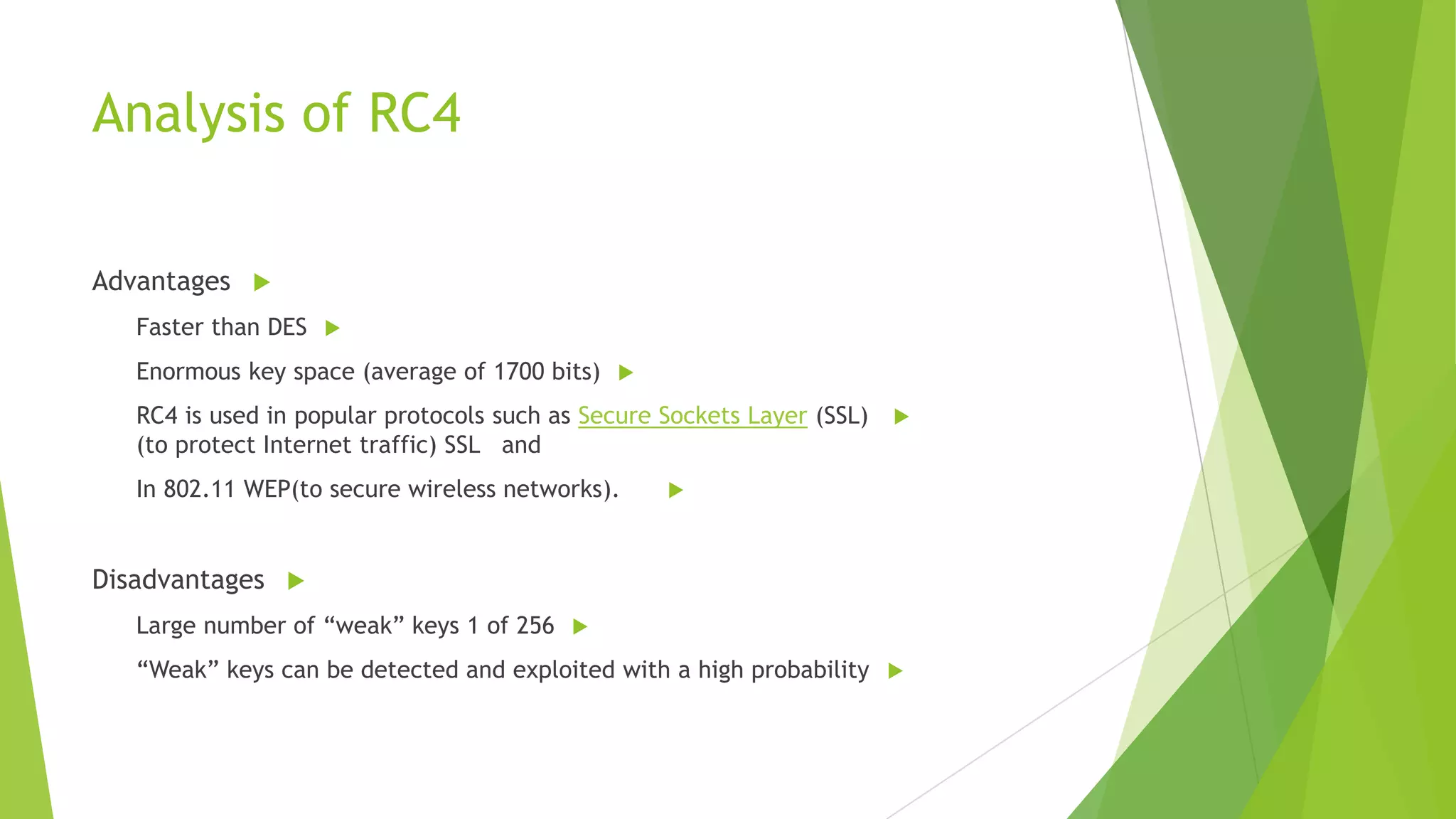
K = {1, 7, 1, 7}
S[0]
K[0]
First Iteration (i = 0, j = 0, S = {0, 1, 2, 3}):
j = (j + S[ i ] + K[ i ]) = (0 + 0 + 1) = 1
Swap S[ i ] with S[ j ]: S = {1, 0, 2, 3}
S[i]
S = {0,1, 2, 3}
S[j]
Second Iteration (i = 1, j = 1, S = {1, 0, 2, 3}):
j = (j + S[ i ] + K[ i ]) = (1 + 0 + 7) = 0 (mod 4)
Swap S[ i ] with S[ j ]: S = {0, 1, 2, 3}](https://image.slidesharecdn.com/rc42013-140128131058-phpapp01/75/Rc4-Research-2013-11-2048.jpg)
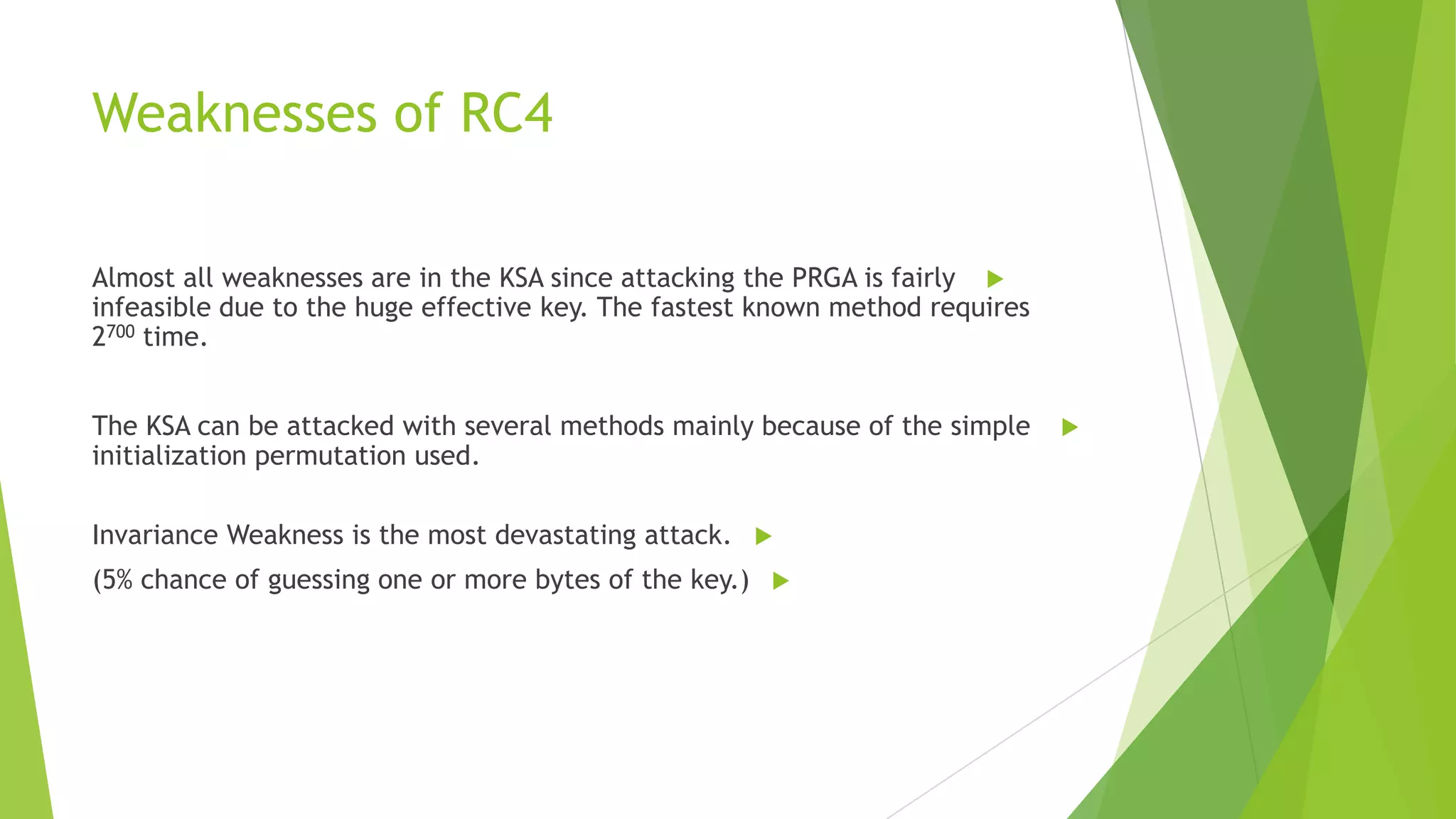
![KSA
K = {1, 7, 1, 7}
S[0]
K[0]
First Iteration (i = 0, j = 0, S = {0, 1, 2, 3}):
j = (j + S[ i ] + K[ i ]) = (0 + 0 + 1) = 1
Swap S[ i ] with S[ j ]: S = {1, 0, 2, 3}
Second Iteration (i = 1, j = 1, S = {1, 0, 2, 3}):
j = (j + S[ i ] + K[ i ]) = (1 + 0 + 7) = 0 (mod 4)
Swap S[ i ] with S[ j ]: S = {0, 1, 2, 3}
S[i]
1
S = {0 ,1 , 2, 3}
0
S[j]](https://image.slidesharecdn.com/rc42013-140128131058-phpapp01/75/Rc4-Research-2013-12-2048.jpg)
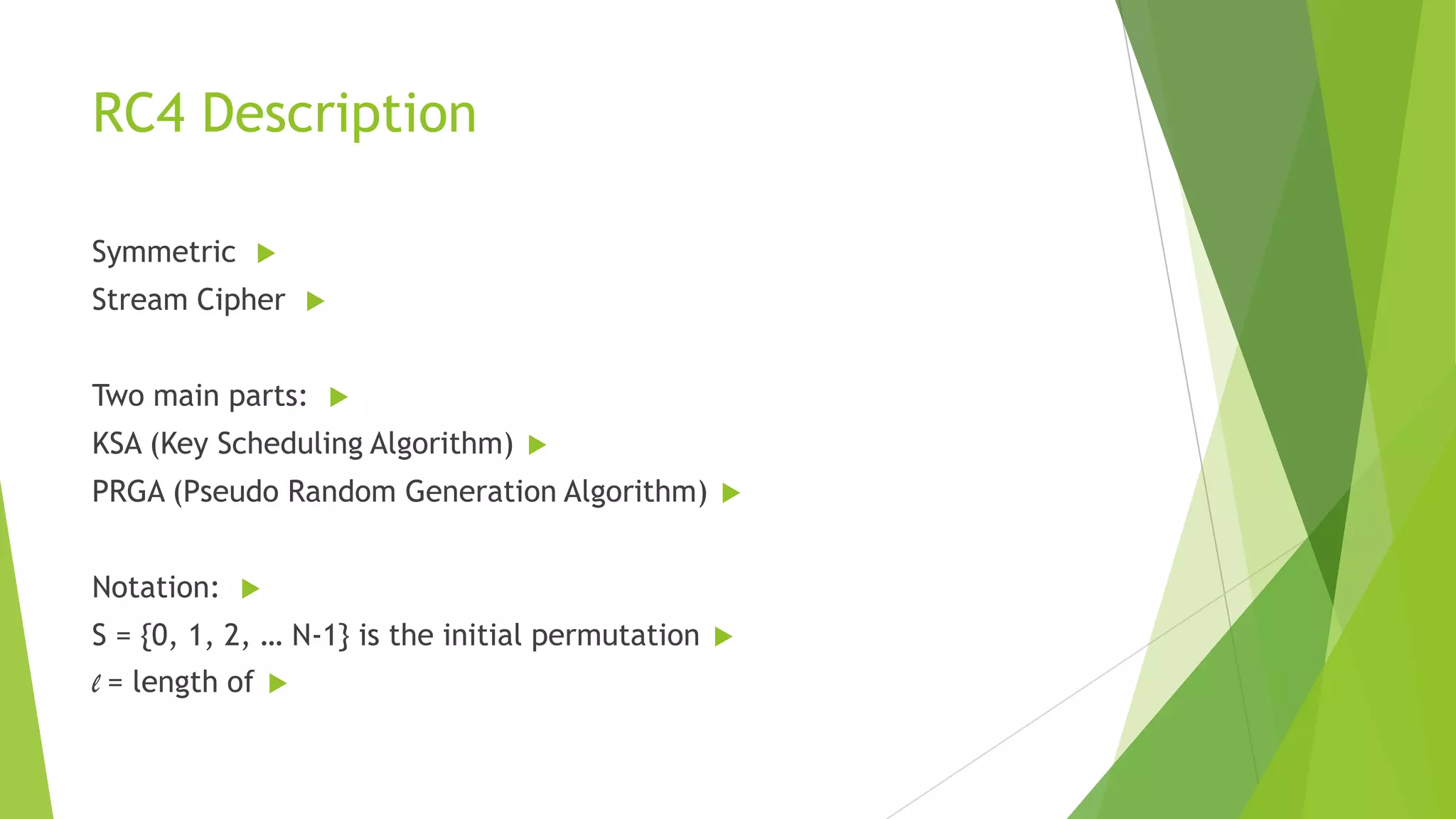
![KSA
K = {1, 7, 1, 7}
S[0]
K[0]
First Iteration (i = 0, j = 0, S = {0, 1, 2, 3}):
j = (j + S[ i ] + K[ i ]) = (0 + 0 + 1) = 1
Swap S[ i ] with S[ j ]: S = {1, 0, 2, 3}
Second Iteration (i = 1, j = 1, S = {1, 0, 2, 3}):
j = (j + S[ i ] + K[ i ]) = (1 + 0 + 7) = 0 (mod 4)
Swap S[ i ] with S[ j ]: S = {0, 1, 2, 3}
1
S = { 1, 0, 2, 3}
0](https://image.slidesharecdn.com/rc42013-140128131058-phpapp01/75/Rc4-Research-2013-13-2048.jpg)
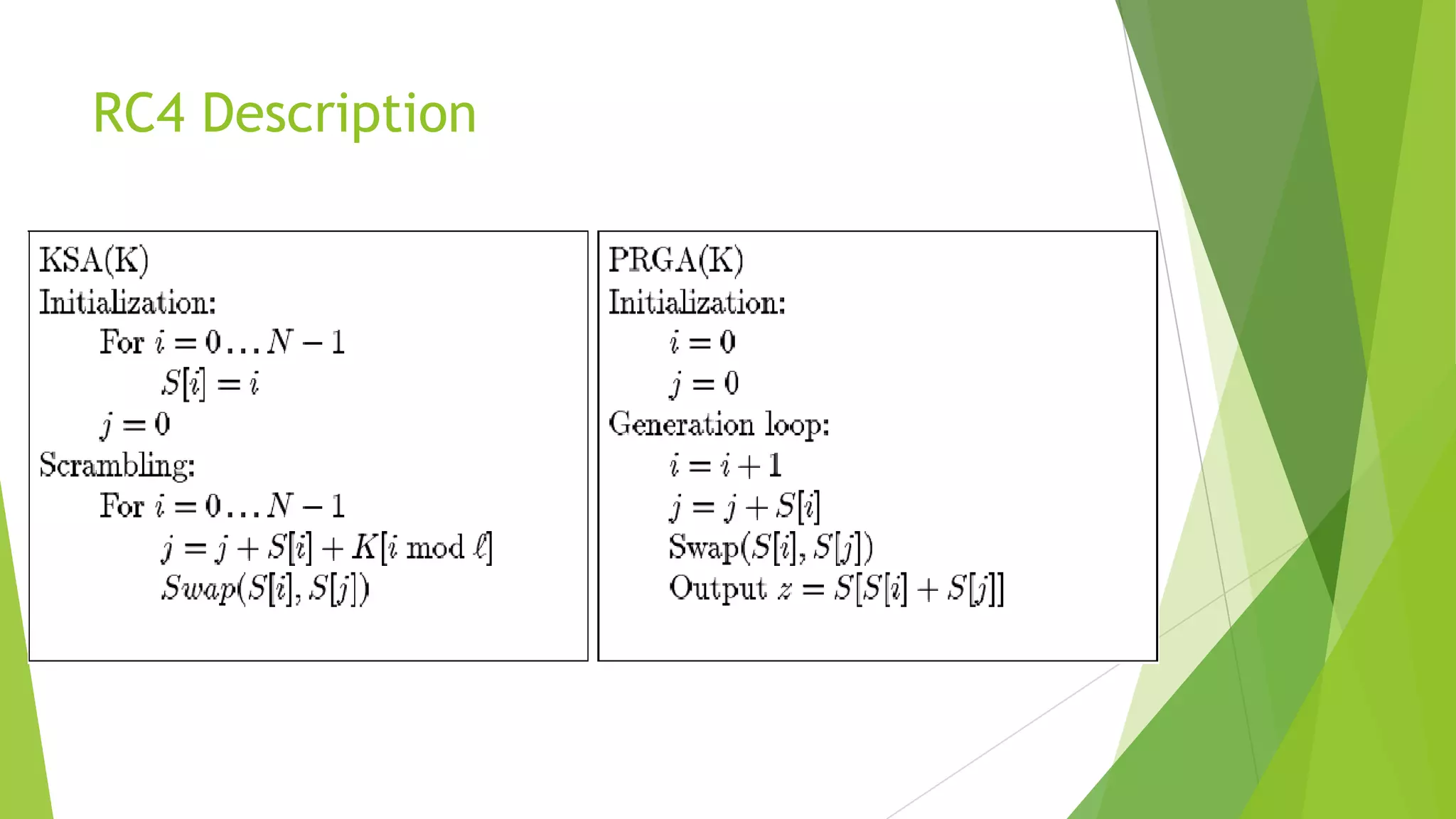
![KSA
K = {1, 7, 1, 7}
K[1]
First Iteration (i = 0, j = 0, S = {0, 1, 2, 3}):
j = (j + S[ i ] + K[ i ]) = (0 + 0 + 1) = 1
Swap S[ i ] with S[ j ]: S = {1, 0, 2, 3}
S[1]
Second Iteration (i = 1, j = 1, S = {1, 0, 2, 3}):
j = (j + S[ i ] + K[ i ]) = (1 + 0 + 7) = 0 (mod 4)
Swap S[ i ] with S[ j ]: S = {0, 1, 2, 3}](https://image.slidesharecdn.com/rc42013-140128131058-phpapp01/75/Rc4-Research-2013-14-2048.jpg)
![KSA
K = {1, 7, 1, 7}
S[2]
K[2]
Third Iteration (i = 2, j = 0, S = {0, 1, 2, 3}):
j = (j + S[ i ] + K[ i ]) = (0 + 2 + 1) = 3
Swap S[ i ] with S[ j ]: S = {0, 1, 3, 2}
Fourth Iteration (i = 3, j = 3, S = {0, 1, 3, 2}):
j = (j + S[ i ] + K[ i ]) = (3 + 2 + 7) = 0 (mod 4)
Swap S[ i ] with S[ j ]: S = {2, 1, 3, 0}](https://image.slidesharecdn.com/rc42013-140128131058-phpapp01/75/Rc4-Research-2013-15-2048.jpg)
![KSA
K = {1, 7, 1, 7}
K[3]
Third Iteration (i = 2, j = 0, S = {0, 1, 2, 3}):
j = (j + S[ i ] + K[ i ]) = (0 + 2 + 1) = 3
Swap S[ i ] with S[ j ]: S = {0, 1, 3, 2}
S[3]
Fourth Iteration (i = 3, j = 3, S = {0, 1, 3, 2}):
j = (j + S[ i ] + K[ i ]) = (3 + 2 + 7) = 0 (mod 4)
Swap S[ i ] with S[ j ]: S = {2, 1, 3, 0}](https://image.slidesharecdn.com/rc42013-140128131058-phpapp01/75/Rc4-Research-2013-16-2048.jpg)
![PRGA
For this example we use plaintext “HI”
Reset i = j = 0, Recall S = {2, 1, 3, 0}
i=i+1=1
j = j + S[ i ] = 0 + 1 = 1
Swap S[ i ] and S[ j ]: S = {2, 1, 3, 0}
Output z = S[ S[ i ] + S[ j ] ] = S[2] = 3
Z = 3 ( 0000 0011 )
H
0100 1000
XOR 0000 0011
0100 1011](https://image.slidesharecdn.com/rc42013-140128131058-phpapp01/75/Rc4-Research-2013-17-2048.jpg)
![i=1 , j=1 , S = {2, 1, 3, 0}
i=i+1=2
j = j + S[ i ] = 1 + 3 = 4 (mod 4) = 0
Swap S[ i ] and S[ j ]: S = {3, 1, 2, 0}
Output z = S[ S[ i ] + S[ j ] ] = S[1] = 1
Z = 1 ( 0000 0001 )
I
0100 1001
XOR 0000 0001
0100 1000
Result : Plaint Text : 0100 1000 0100 1001
Cipher Text: 0100 1011 0100 1000](https://image.slidesharecdn.com/rc42013-140128131058-phpapp01/75/Rc4-Research-2013-18-2048.jpg)