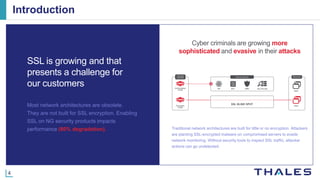
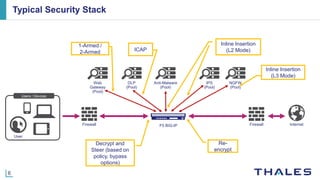
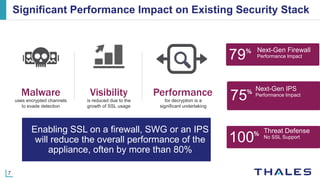
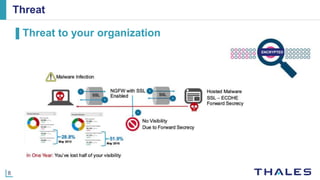
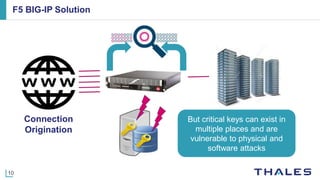
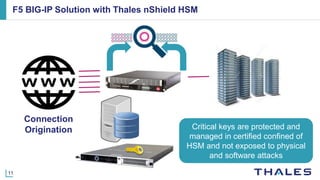
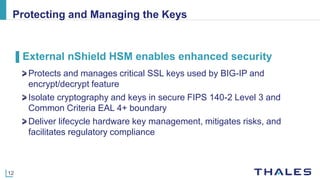
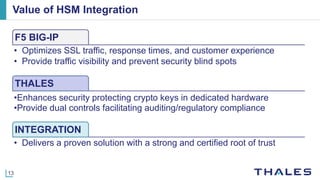
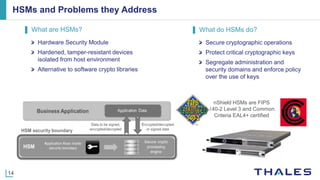
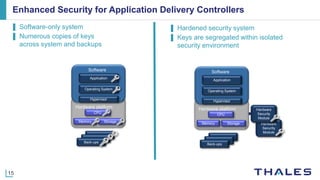
The document discusses the challenges posed by network security blind spots, particularly due to increasing SSL usage, which can hinder threat detection and reduce the performance of security appliances. It outlines best practices for mitigating these risks, including the integration of Thales nShield HSM with F5 BIG-IP for enhanced key management and security. The results aim to optimize security stack performance, improve traffic visibility, and ensure compliance with regulatory standards.