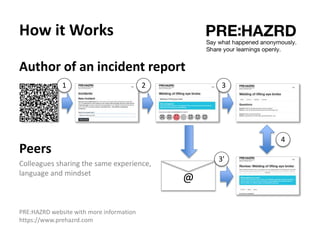
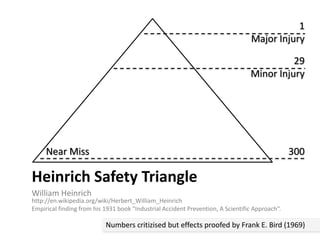
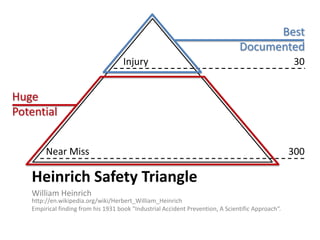
The document discusses near-miss incidents, highlighting that they are unplanned events with the potential for injury that fortunately did not result in harm. It critiques the Heinrich Safety Triangle and suggests that serious and minor injuries stem from different causes, advocating for decentralized and anonymous documentation of incidents. The importance of sharing experiences and identifying patterns in safety protocols is emphasized as a means to enhance safety awareness and prevention.
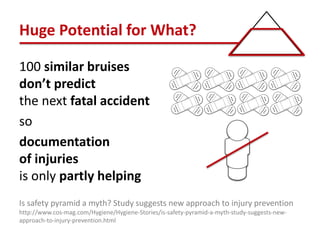
![Huge Potential for What??
• “The BST study suggests […] that serious
injuries have different underlying causes than
minor ones.”
• “These underlying factors — missing controls,
lax procedures, badly designed equipment —
create high-risk situations that are likely to
lead to a major incident.”
Is safety pyramid a myth? Study suggests new approach to injury prevention
http://www.cos-mag.com/Hygiene/Hygiene-Stories/is-safety-pyramid-a-myth-study-suggests-new-
approach-to-injury-prevention.html](https://image.slidesharecdn.com/prehazrdintro20151112-151113221016-lva1-app6891/85/PRE-HAZRD-Intro-7-320.jpg)