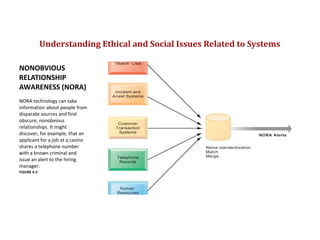
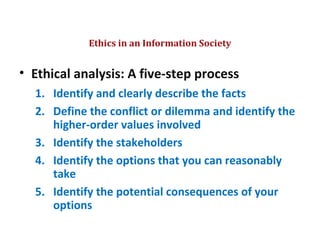
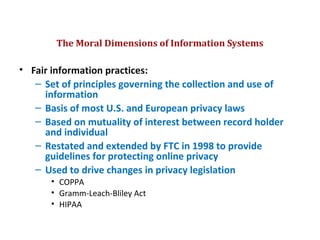
This document discusses ethical issues related to information systems. It introduces the concept of NORA technology which can find obscure relationships in data from multiple sources, potentially violating privacy. It then outlines principles of ethics like responsibility, accountability, and liability. The document presents a 5-step process for ethical analysis and 6 candidate ethical principles. Professional codes of conduct and real-world dilemmas are discussed. The rest of the document focuses on privacy, outlining US privacy protections and fair information practices that are the basis for many privacy laws. The European data protection directive and US safe harbor framework in response are also summarized.