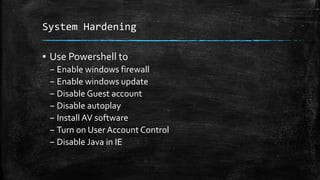
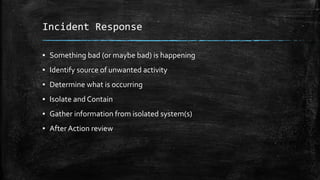
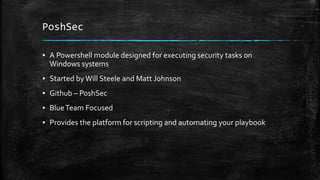
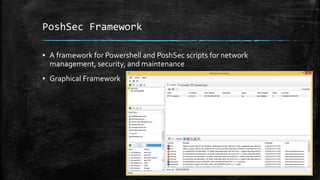
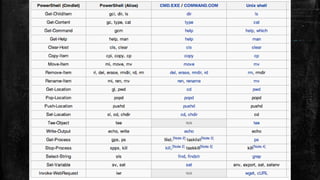
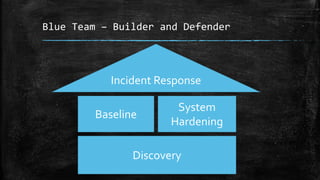
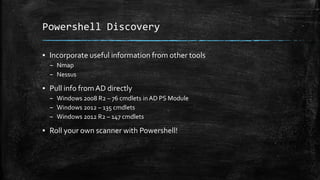
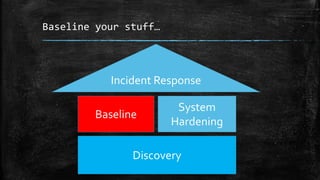
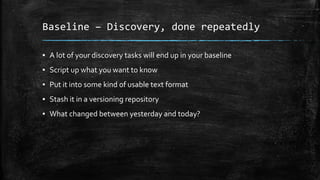
This document discusses the advantages and applications of PowerShell for security professionals, emphasizing its integration into Windows and its superiority over traditional scripting tools. It outlines PowerShell's functionalities such as cmdlets, remoting, and automation for discovery, baseline management, and incident response. The document also touches on tools and frameworks like PoshSec for security automation and highlights best practices for writing and managing PowerShell code.



![Automate Reporting
▪ Need to nicely present Nessus or nmap output?
▪ Previous work
– Carlos Perez (DarkOperator) – Posh-NVS
▪ https://github.com/darkoperator/Posh-NVS
▪ Powershell easily handles XML and CSV inputs
[xml]$report = Get-Content –Raw .scan.nessus
$reporthosts = $report.NessusClientData_v2.Report.ReportHost
$reporthosts | foreach {$_.ReportItem} | Out-GridView](https://image.slidesharecdn.com/powershellpreso-150528121813-lva1-app6892/85/Who-Should-Use-Powershell-You-Should-Use-Powershell-27-320.jpg)