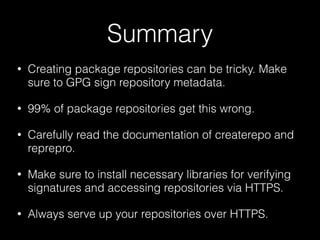
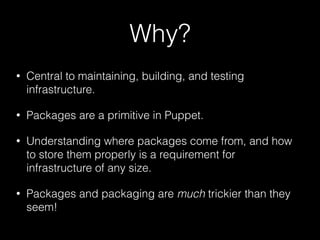
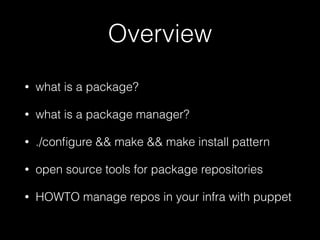
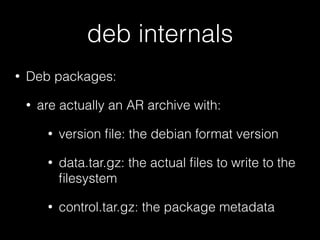
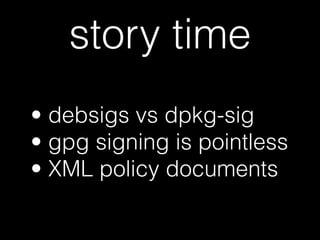
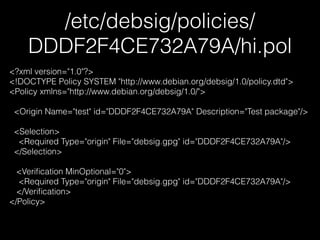
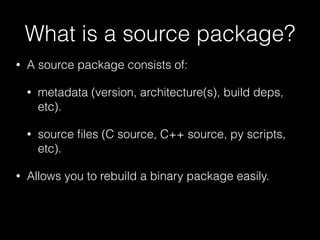
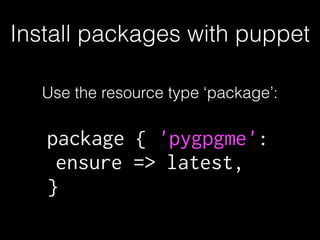
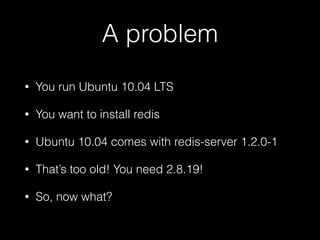
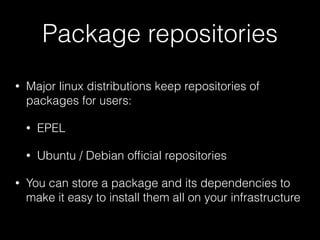
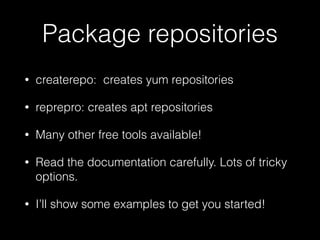
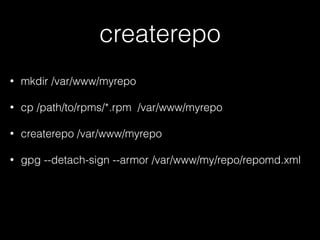
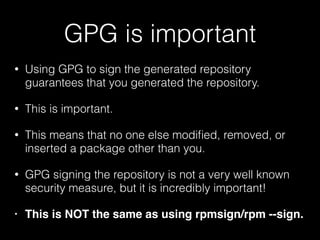
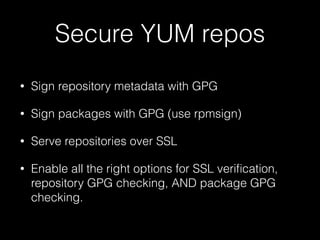
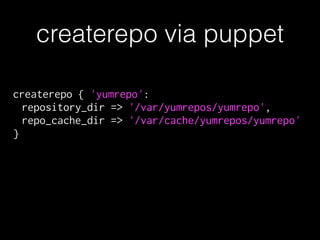
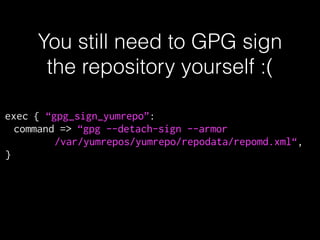
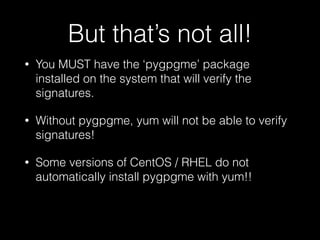
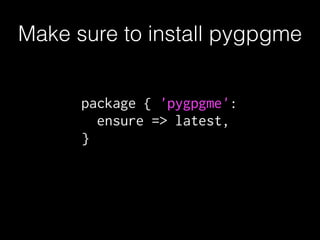
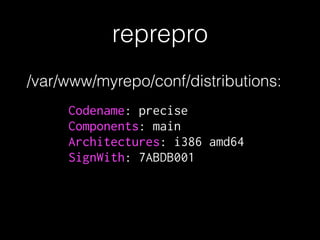
The document discusses the importance of package managers and their role in managing software infrastructure, specifically within the context of Puppet. It covers the definition and internals of various package types (like RPM and DEB), the functioning of package managers (such as YUM and APT), and how to manage packages through Puppet. The conclusion emphasizes that properly creating and managing package repositories, including necessary security measures like GPG signing, is crucial for maintaining secure infrastructure.














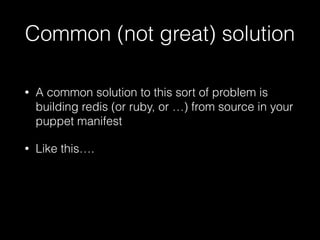
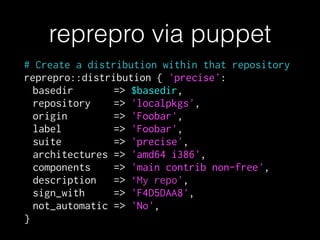
![exec { 'install-redis':
command => "make && make install PREFIX=${redis_bin_dir}",
cwd => $redis_src_dir,
path => '/bin:/usr/bin',
unless => "test $(${redis_bin_dir}/bin/redis-server --version | cut -d
' ' -f 1) = ‘Redis'",
require => [ Exec['unpack-redis'], Class['gcc'] ],
}
Common (not great) solution](https://image.slidesharecdn.com/puppetconf-2015-151009210509-lva1-app6891/85/Package-manages-and-Puppet-PuppetConf-2015-53-320.jpg)







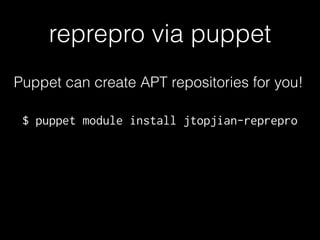
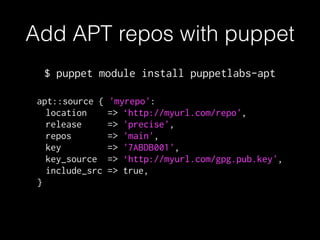
![# Base Directory shortcut
$basedir = '/var/lib/apt/repo'
!
# Main reprepro class
class { 'reprepro':
basedir => $basedir,
}
!
# Set up a repository
reprepro::repository { 'localpkgs':
ensure => present,
basedir => $basedir,
options => ['basedir .'],
}
reprepro via puppet](https://image.slidesharecdn.com/puppetconf-2015-151009210509-lva1-app6891/85/Package-manages-and-Puppet-PuppetConf-2015-93-320.jpg)