Power Notes Physical vs. Chemical Day 1
•Download as PPT, PDF•
2 likes•169 views
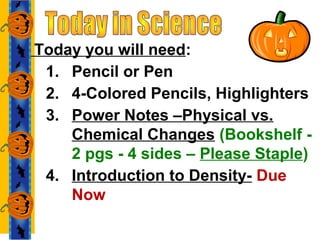
This document provides a schedule and instructions for students. It includes: 1. A list of materials needed for class today including a pencil, colored pencils, highlighters, and stapled power notes on physical vs. chemical changes. 2. Assignments that are due on specified dates, including power notes on physical vs. chemical changes due October 14th, a binder check due October 17th, and a test on October 17th. 3. Information on the differences between physical and chemical properties and changes, with examples of each. Chemical changes result in new substances while physical changes do not.
Report
Share
Report
Share
Recommended
Recommended
How chemistry and the environment mix lecture 2

Powerpoint for Lecture 2 Environmental Science
How chemistry and the environment mix
More Related Content
Viewers also liked
Viewers also liked (16)
Similar to Power Notes Physical vs. Chemical Day 1
How chemistry and the environment mix lecture 2

Powerpoint for Lecture 2 Environmental Science
How chemistry and the environment mix
K TO 12 GRADE 5 LEARNER’S MATERIAL IN SCIENCE (Q1-Q4)

K to 12 Learning Module/Material in SCIENCE for Grade 5 Quarter 1 to Quarter 4
Matter and its properties

What composes matter? Learn how individual composition affects the physical and chemical properties of a substance/object.
Similar to Power Notes Physical vs. Chemical Day 1 (20)
K TO 12 GRADE 5 LEARNER’S MATERIAL IN SCIENCE (Q1-Q4)

K TO 12 GRADE 5 LEARNER’S MATERIAL IN SCIENCE (Q1-Q4)
More from jmori
How Might you Solve this Challenge

There is a process for solving problems/challenges. You will have many opportunities to use your knowledge, imagination and creativity to solve simple to complex challenges.
Bridges -A Brief History

Why might we need bridges? What might be the best materials for bridges? Are there bridges stronger than others? Which cost the most to make?
More from jmori (20)
Recently uploaded
Epistemic Interaction - tuning interfaces to provide information for AI support

Paper presented at SYNERGY workshop at AVI 2024, Genoa, Italy. 3rd June 2024
https://alandix.com/academic/papers/synergy2024-epistemic/
As machine learning integrates deeper into human-computer interactions, the concept of epistemic interaction emerges, aiming to refine these interactions to enhance system adaptability. This approach encourages minor, intentional adjustments in user behaviour to enrich the data available for system learning. This paper introduces epistemic interaction within the context of human-system communication, illustrating how deliberate interaction design can improve system understanding and adaptation. Through concrete examples, we demonstrate the potential of epistemic interaction to significantly advance human-computer interaction by leveraging intuitive human communication strategies to inform system design and functionality, offering a novel pathway for enriching user-system engagements.
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

Effective Application Security in Software Delivery lifecycle using Deployment Firewall and DBOM
The modern software delivery process (or the CI/CD process) includes many tools, distributed teams, open-source code, and cloud platforms. Constant focus on speed to release software to market, along with the traditional slow and manual security checks has caused gaps in continuous security as an important piece in the software supply chain. Today organizations feel more susceptible to external and internal cyber threats due to the vast attack surface in their applications supply chain and the lack of end-to-end governance and risk management.
The software team must secure its software delivery process to avoid vulnerability and security breaches. This needs to be achieved with existing tool chains and without extensive rework of the delivery processes. This talk will present strategies and techniques for providing visibility into the true risk of the existing vulnerabilities, preventing the introduction of security issues in the software, resolving vulnerabilities in production environments quickly, and capturing the deployment bill of materials (DBOM).
Speakers:
Bob Boule
Robert Boule is a technology enthusiast with PASSION for technology and making things work along with a knack for helping others understand how things work. He comes with around 20 years of solution engineering experience in application security, software continuous delivery, and SaaS platforms. He is known for his dynamic presentations in CI/CD and application security integrated in software delivery lifecycle.
Gopinath Rebala
Gopinath Rebala is the CTO of OpsMx, where he has overall responsibility for the machine learning and data processing architectures for Secure Software Delivery. Gopi also has a strong connection with our customers, leading design and architecture for strategic implementations. Gopi is a frequent speaker and well-known leader in continuous delivery and integrating security into software delivery.
Elevating Tactical DDD Patterns Through Object Calisthenics

After immersing yourself in the blue book and its red counterpart, attending DDD-focused conferences, and applying tactical patterns, you're left with a crucial question: How do I ensure my design is effective? Tactical patterns within Domain-Driven Design (DDD) serve as guiding principles for creating clear and manageable domain models. However, achieving success with these patterns requires additional guidance. Interestingly, we've observed that a set of constraints initially designed for training purposes remarkably aligns with effective pattern implementation, offering a more ‘mechanical’ approach. Let's explore together how Object Calisthenics can elevate the design of your tactical DDD patterns, offering concrete help for those venturing into DDD for the first time!
Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024

As AI technology is pushing into IT I was wondering myself, as an “infrastructure container kubernetes guy”, how get this fancy AI technology get managed from an infrastructure operational view? Is it possible to apply our lovely cloud native principals as well? What benefit’s both technologies could bring to each other?
Let me take this questions and provide you a short journey through existing deployment models and use cases for AI software. On practical examples, we discuss what cloud/on-premise strategy we may need for applying it to our own infrastructure to get it to work from an enterprise perspective. I want to give an overview about infrastructure requirements and technologies, what could be beneficial or limiting your AI use cases in an enterprise environment. An interactive Demo will give you some insides, what approaches I got already working for real.
Securing your Kubernetes cluster_ a step-by-step guide to success !

Today, after several years of existence, an extremely active community and an ultra-dynamic ecosystem, Kubernetes has established itself as the de facto standard in container orchestration. Thanks to a wide range of managed services, it has never been so easy to set up a ready-to-use Kubernetes cluster.
However, this ease of use means that the subject of security in Kubernetes is often left for later, or even neglected. This exposes companies to significant risks.
In this talk, I'll show you step-by-step how to secure your Kubernetes cluster for greater peace of mind and reliability.
Assuring Contact Center Experiences for Your Customers With ThousandEyes

Presented by Suzanne Phillips and Alex Marcotte
To Graph or Not to Graph Knowledge Graph Architectures and LLMs

Reflecting on new architectures for knowledge based systems in light of generative ai
Empowering NextGen Mobility via Large Action Model Infrastructure (LAMI): pav...

Empowering NextGen Mobility via Large Action Model Infrastructure (LAMI)
Leading Change strategies and insights for effective change management pdf 1.pdf

Leading Change strategies and insights for effective change management pdf 1.pdf
Encryption in Microsoft 365 - ExpertsLive Netherlands 2024

In this session I delve into the encryption technology used in Microsoft 365 and Microsoft Purview. Including the concepts of Customer Key and Double Key Encryption.
The Art of the Pitch: WordPress Relationships and Sales

Clients don’t know what they don’t know. What web solutions are right for them? How does WordPress come into the picture? How do you make sure you understand scope and timeline? What do you do if sometime changes?
All these questions and more will be explored as we talk about matching clients’ needs with what your agency offers without pulling teeth or pulling your hair out. Practical tips, and strategies for successful relationship building that leads to closing the deal.
Transcript: Selling digital books in 2024: Insights from industry leaders - T...

The publishing industry has been selling digital audiobooks and ebooks for over a decade and has found its groove. What’s changed? What has stayed the same? Where do we go from here? Join a group of leading sales peers from across the industry for a conversation about the lessons learned since the popularization of digital books, best practices, digital book supply chain management, and more.
Link to video recording: https://bnctechforum.ca/sessions/selling-digital-books-in-2024-insights-from-industry-leaders/
Presented by BookNet Canada on May 28, 2024, with support from the Department of Canadian Heritage.
Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf

91mobiles recently conducted a Smart TV Buyer Insights Survey in which we asked over 3,000 respondents about the TV they own, aspects they look at on a new TV, and their TV buying preferences.
State of ICS and IoT Cyber Threat Landscape Report 2024 preview

The IoT and OT threat landscape report has been prepared by the Threat Research Team at Sectrio using data from Sectrio, cyber threat intelligence farming facilities spread across over 85 cities around the world. In addition, Sectrio also runs AI-based advanced threat and payload engagement facilities that serve as sinks to attract and engage sophisticated threat actors, and newer malware including new variants and latent threats that are at an earlier stage of development.
The latest edition of the OT/ICS and IoT security Threat Landscape Report 2024 also covers:
State of global ICS asset and network exposure
Sectoral targets and attacks as well as the cost of ransom
Global APT activity, AI usage, actor and tactic profiles, and implications
Rise in volumes of AI-powered cyberattacks
Major cyber events in 2024
Malware and malicious payload trends
Cyberattack types and targets
Vulnerability exploit attempts on CVEs
Attacks on counties – USA
Expansion of bot farms – how, where, and why
In-depth analysis of the cyber threat landscape across North America, South America, Europe, APAC, and the Middle East
Why are attacks on smart factories rising?
Cyber risk predictions
Axis of attacks – Europe
Systemic attacks in the Middle East
Download the full report from here:
https://sectrio.com/resources/ot-threat-landscape-reports/sectrio-releases-ot-ics-and-iot-security-threat-landscape-report-2024/
Knowledge engineering: from people to machines and back

Keynote at the 21st European Semantic Web Conference
From Daily Decisions to Bottom Line: Connecting Product Work to Revenue by VP...

From Daily Decisions to Bottom Line: Connecting Product Work to Revenue by VP of Product, Amplitude
Generating a custom Ruby SDK for your web service or Rails API using Smithy

Have you ever wanted a Ruby client API to communicate with your web service? Smithy is a protocol-agnostic language for defining services and SDKs. Smithy Ruby is an implementation of Smithy that generates a Ruby SDK using a Smithy model. In this talk, we will explore Smithy and Smithy Ruby to learn how to generate custom feature-rich SDKs that can communicate with any web service, such as a Rails JSON API.
De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovati...

De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovation With Your Product by VP of Product Design, Warner Music Group
Recently uploaded (20)
Epistemic Interaction - tuning interfaces to provide information for AI support

Epistemic Interaction - tuning interfaces to provide information for AI support
FIDO Alliance Osaka Seminar: Passkeys at Amazon.pdf

FIDO Alliance Osaka Seminar: Passkeys at Amazon.pdf
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...
Elevating Tactical DDD Patterns Through Object Calisthenics

Elevating Tactical DDD Patterns Through Object Calisthenics
Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024

Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024
Securing your Kubernetes cluster_ a step-by-step guide to success !

Securing your Kubernetes cluster_ a step-by-step guide to success !
Assuring Contact Center Experiences for Your Customers With ThousandEyes

Assuring Contact Center Experiences for Your Customers With ThousandEyes
To Graph or Not to Graph Knowledge Graph Architectures and LLMs

To Graph or Not to Graph Knowledge Graph Architectures and LLMs
Empowering NextGen Mobility via Large Action Model Infrastructure (LAMI): pav...

Empowering NextGen Mobility via Large Action Model Infrastructure (LAMI): pav...
Leading Change strategies and insights for effective change management pdf 1.pdf

Leading Change strategies and insights for effective change management pdf 1.pdf
Encryption in Microsoft 365 - ExpertsLive Netherlands 2024

Encryption in Microsoft 365 - ExpertsLive Netherlands 2024
The Art of the Pitch: WordPress Relationships and Sales

The Art of the Pitch: WordPress Relationships and Sales
Transcript: Selling digital books in 2024: Insights from industry leaders - T...

Transcript: Selling digital books in 2024: Insights from industry leaders - T...
Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf

Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf
State of ICS and IoT Cyber Threat Landscape Report 2024 preview

State of ICS and IoT Cyber Threat Landscape Report 2024 preview
Knowledge engineering: from people to machines and back

Knowledge engineering: from people to machines and back
From Daily Decisions to Bottom Line: Connecting Product Work to Revenue by VP...

From Daily Decisions to Bottom Line: Connecting Product Work to Revenue by VP...
Generating a custom Ruby SDK for your web service or Rails API using Smithy

Generating a custom Ruby SDK for your web service or Rails API using Smithy
De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovati...

De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovati...
Power Notes Physical vs. Chemical Day 1
- 1. Today you will need: 1. Pencil or Pen 2. 4-Colored Pencils, Highlighters 3. Power Notes –Physical vs. Chemical Changes (Bookshelf - 2 pgs - 4 sides – Please Staple) 4. Introduction to Density- Due Now
- 2. 1) Power Notes – Physical vs. Chemical – Due on Monday, Oct. 14th 2) Binder Check #2 – Due Thur. Oct. 17th at the beginning of class 3) Test #2 – Thur. Oct. 17th - Target Concepts on-line- ½ page of notes front side only done by hand
- 3. •Basic particles that make up a substance. We can identify substances according to their __________ & ___________ properties Brainstorm – OK to have the same ideas – a minimum of 2
- 4. Why do we have to use more than just physical properties to determine what a substance is? •required knowledge of more properties. Physical Properties 1. Characteristics of materials that can be observed w/out carrying out a chemical reaction 2. Usually easy to reverse 3. NO NEW substance created Examples of Physical Properties Color, size, texture, density, freezing pt. electrical & thermal conductivity, luster, malleability, ductility, hardness, mass, solubility H2O Ice water + Heat = H2O Liquid water
- 5. Chemical Properties 1. Characteristics that cannot be easily seen 2. Must create a chemical reaction to observe 3. NEW substance created 4. Difficult to reverse 5. Happens quickly (explosion) or slowly (rusting). Examples of Chemical Change Flammability, reacting with acid Oxidation (rusting-reacting w/oxygen), digesting, decomposition 2 H2O + = O2 H2 H2 2 molecules of water electricity 1 molecules of diatomic oxygen 2 molecules of diatomic Hydrogen Different Substances
- 6. Chemical Properties continues….. Notice that water can be separated into its constituents(parts) ……..2x the amount of hydrogen is collected as compared to oxygen. (H2O) Why?
- 7. On Lined Paper Signs a Chemical Reaction may be occurring: 1. Change in Color 2. Bubbling or Fizzing 3. Precipitant is created http://www.harpercollege.edu/tm- ps/chm/100/dgodambe/thedisk/chemrxn/signs.htm 4. Heat is absorbed or released (endothermic vs. exothermic) 5. Energy is produced What is the difference between endothermic and exothermic? http://antoine.frostburg.edu/chem/senese/101/therm o/faq/exothermic-endothermic-examples.shtml Endothermic – Therm (heat) Endo (in) Ex: Cooking and egg, baking bread, photosynthesis Exothermic = Therm (heat) Exo (out) Ex: Rusting, Explosions, Fireworks
- 8. Physical or Chemical? 1. Identify whether the change is Physical or Chemical 2. Identify the reason as either you still have the Same substance or a Different one was created Event • Identify the event as either physical or chemical. • Explain why in bullet format • Use your notes as reference. Your Ideas 1) Come up with one chemical and one physical event – MUST BE YOUR OWN & DIFFERENT THAN ANYONE IN YOUR GROUP
- 9. Remember: The Law of Conservation of Mass – Matter cannot be CREATED or DESTROYED. It can only change form(physical) or become rearranged (chemical – a change in how the atoms are connected) Review Questions 1-10 • Answers in your notes • Bullet format On-line activity Graded for HONESTY & PARTICIPATION Hyperlink on Learning Point under Daily Assignments for this week. SELECT: Quia Quiz How many did you get correct on your first try? ____/20
- 10. Power Notes – Physical vs. Chemical – Due on Monday Oct. 14th at the beginning of class Don’t forget to Review and Reflect