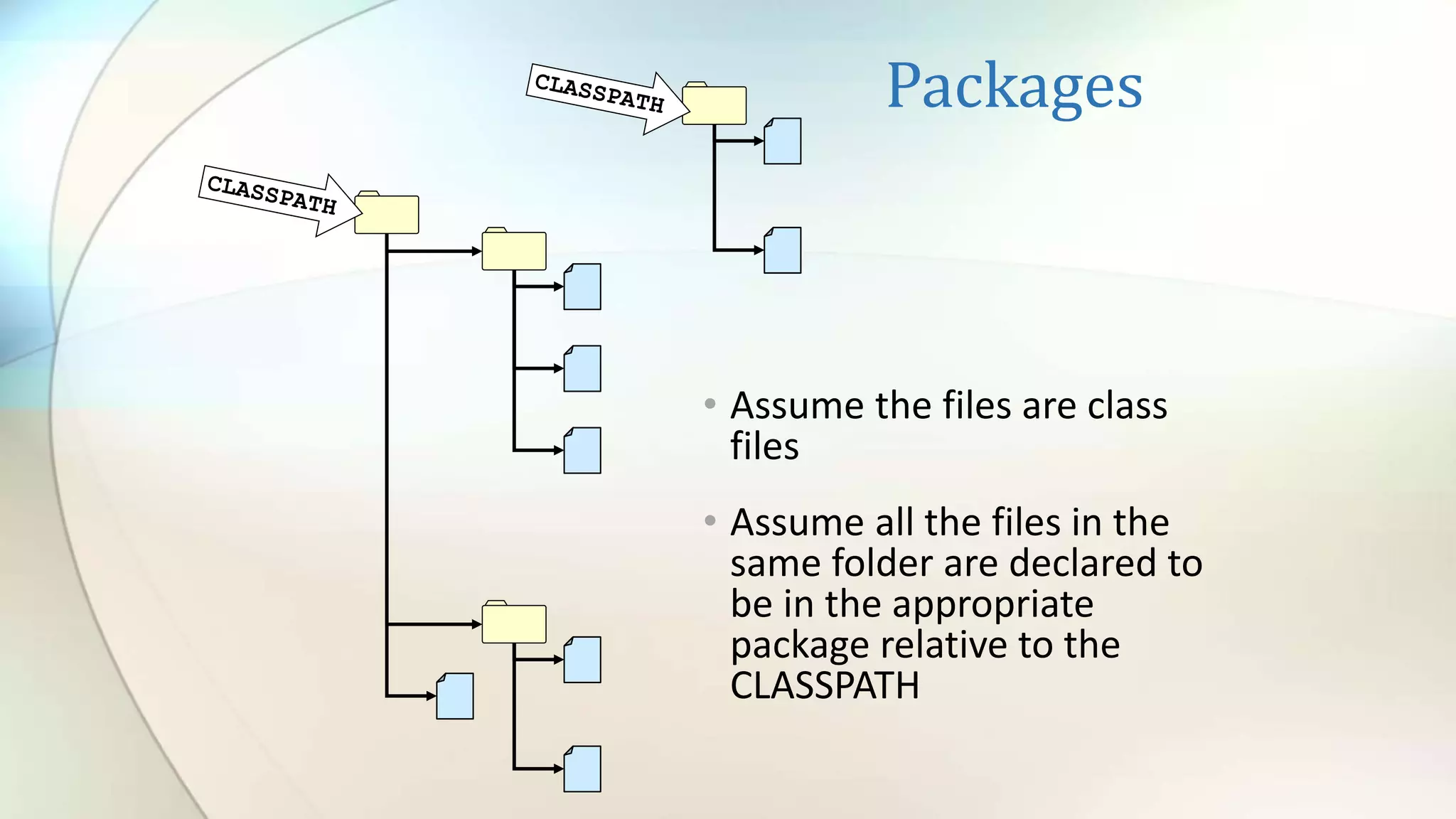
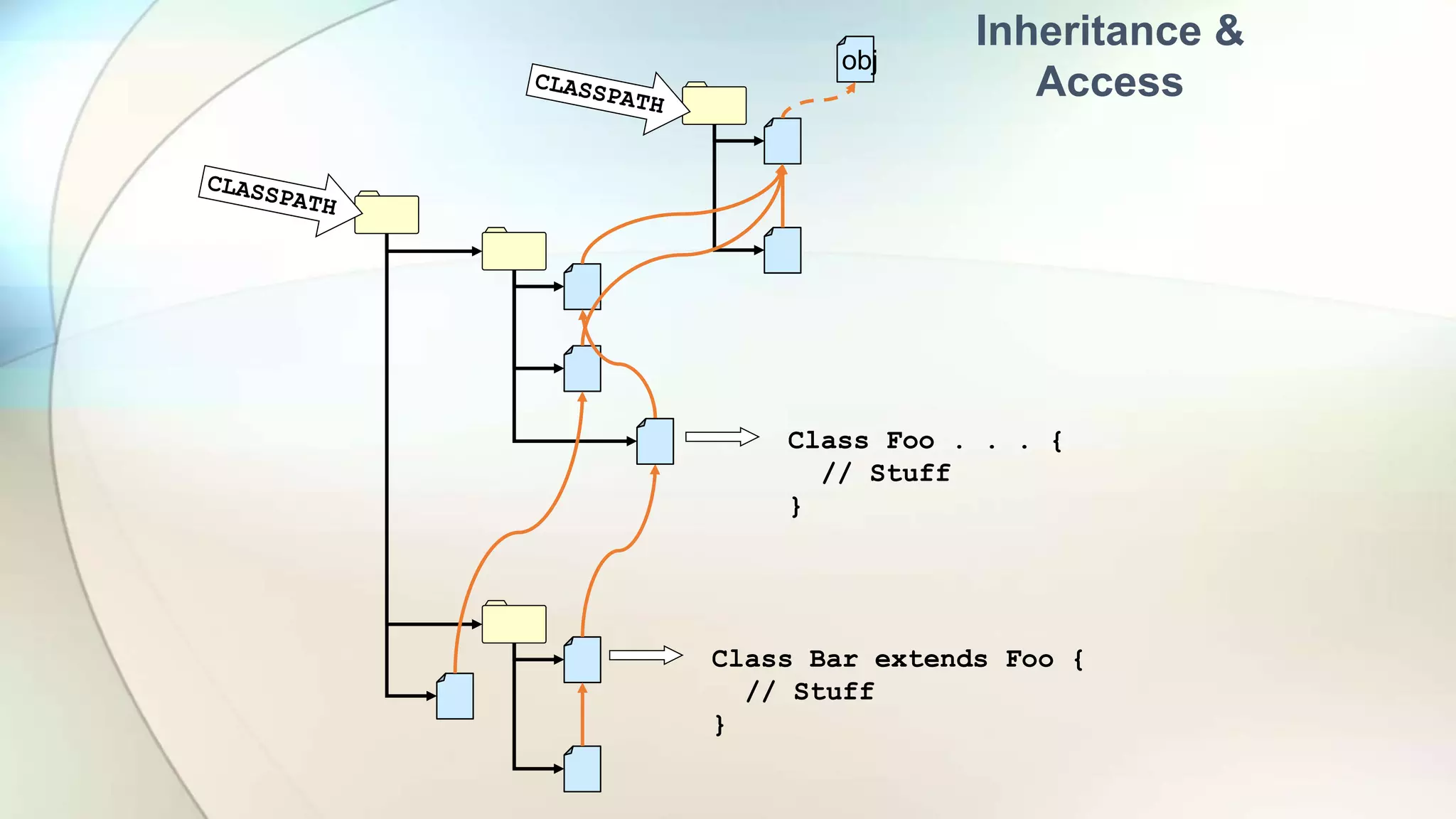
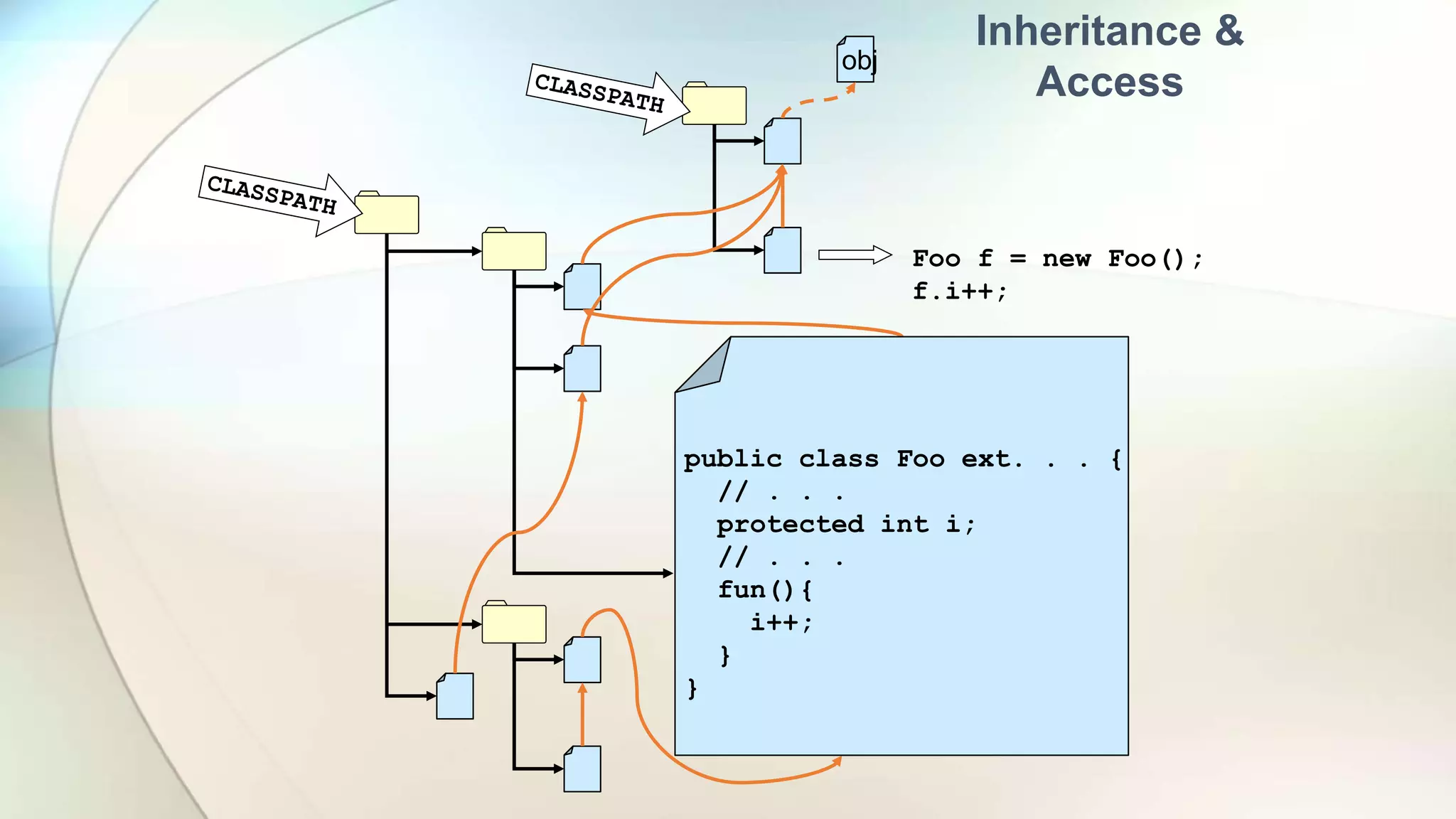
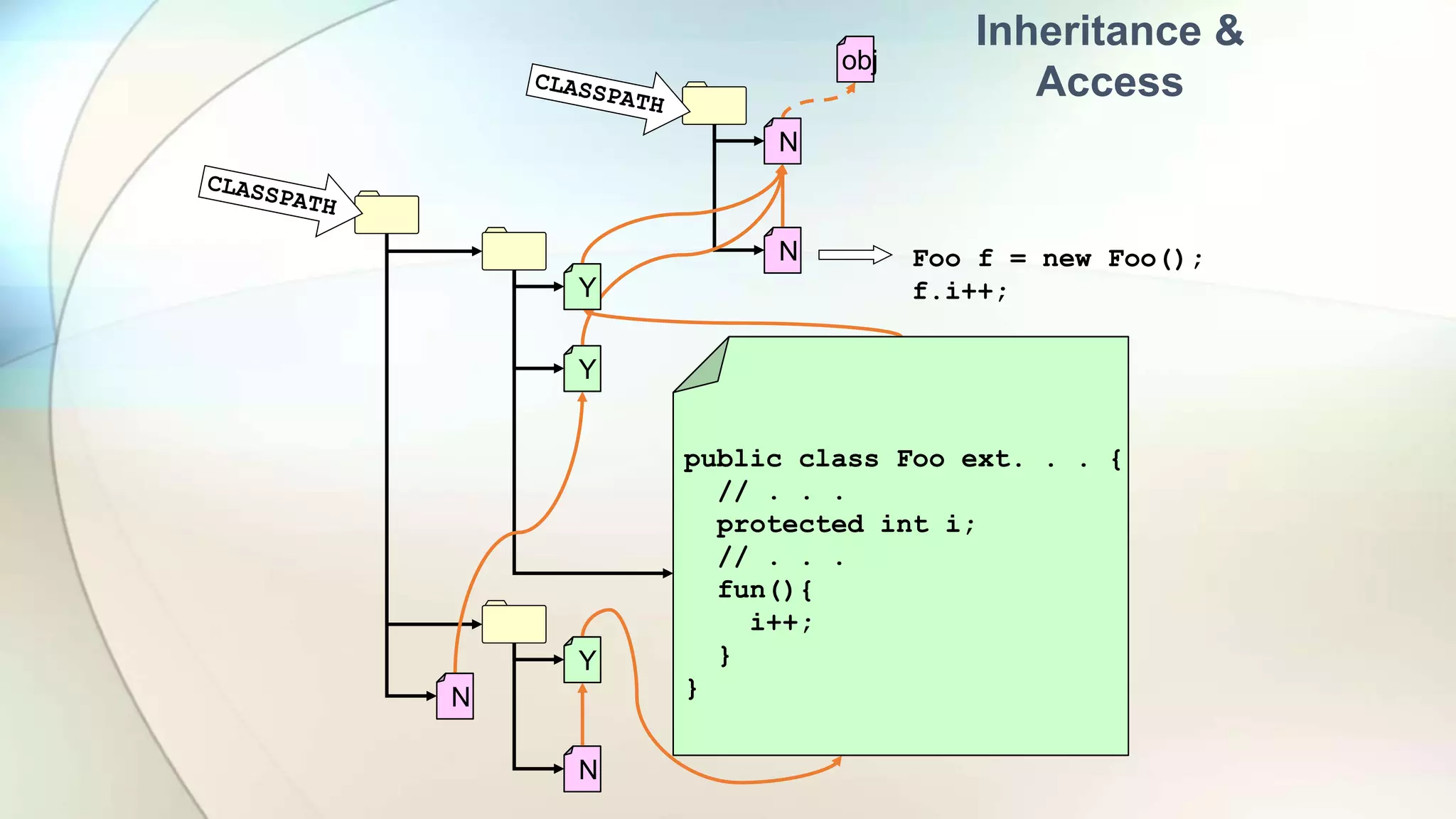
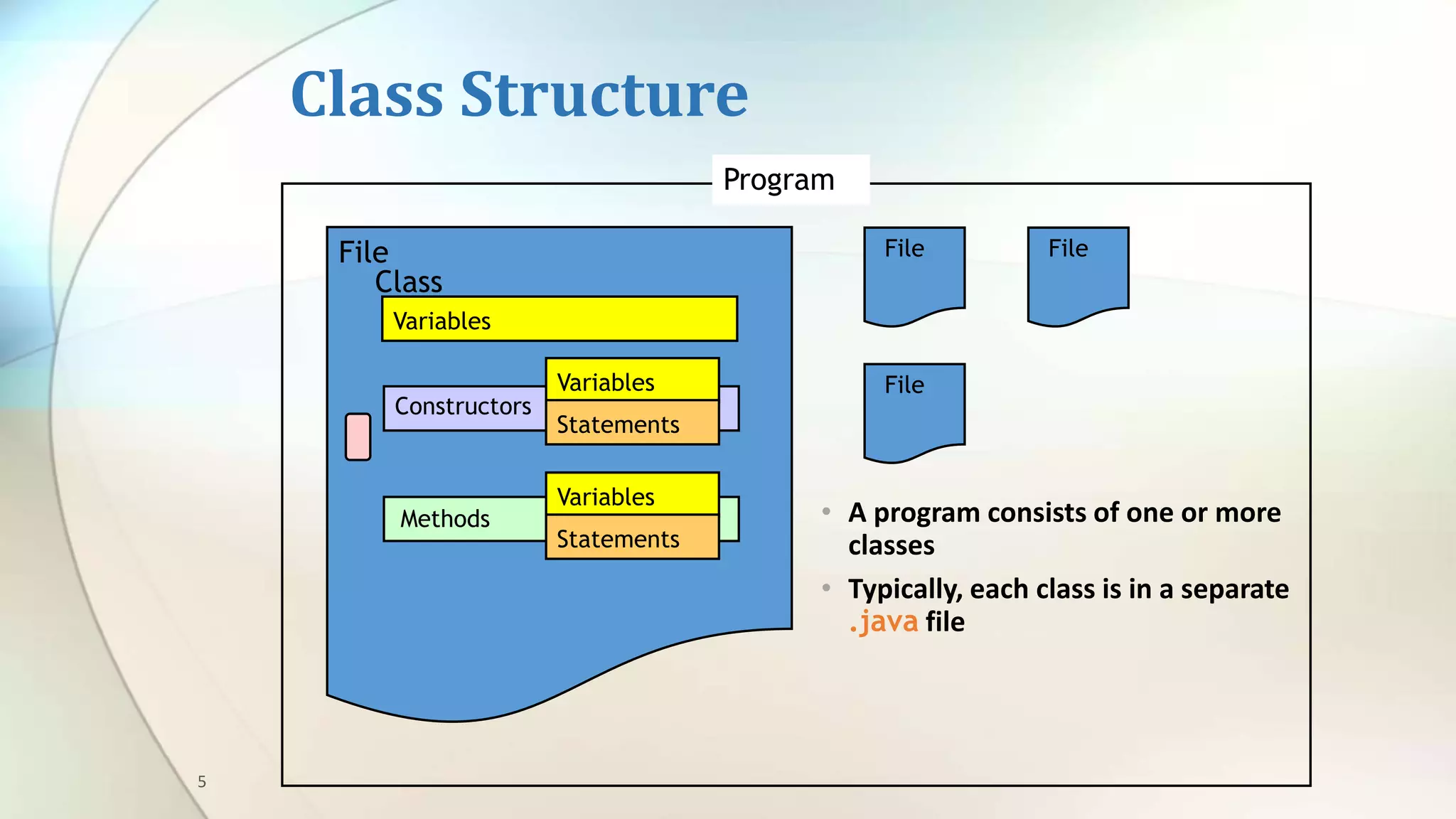
This document provides an overview of basic Java programming concepts including:
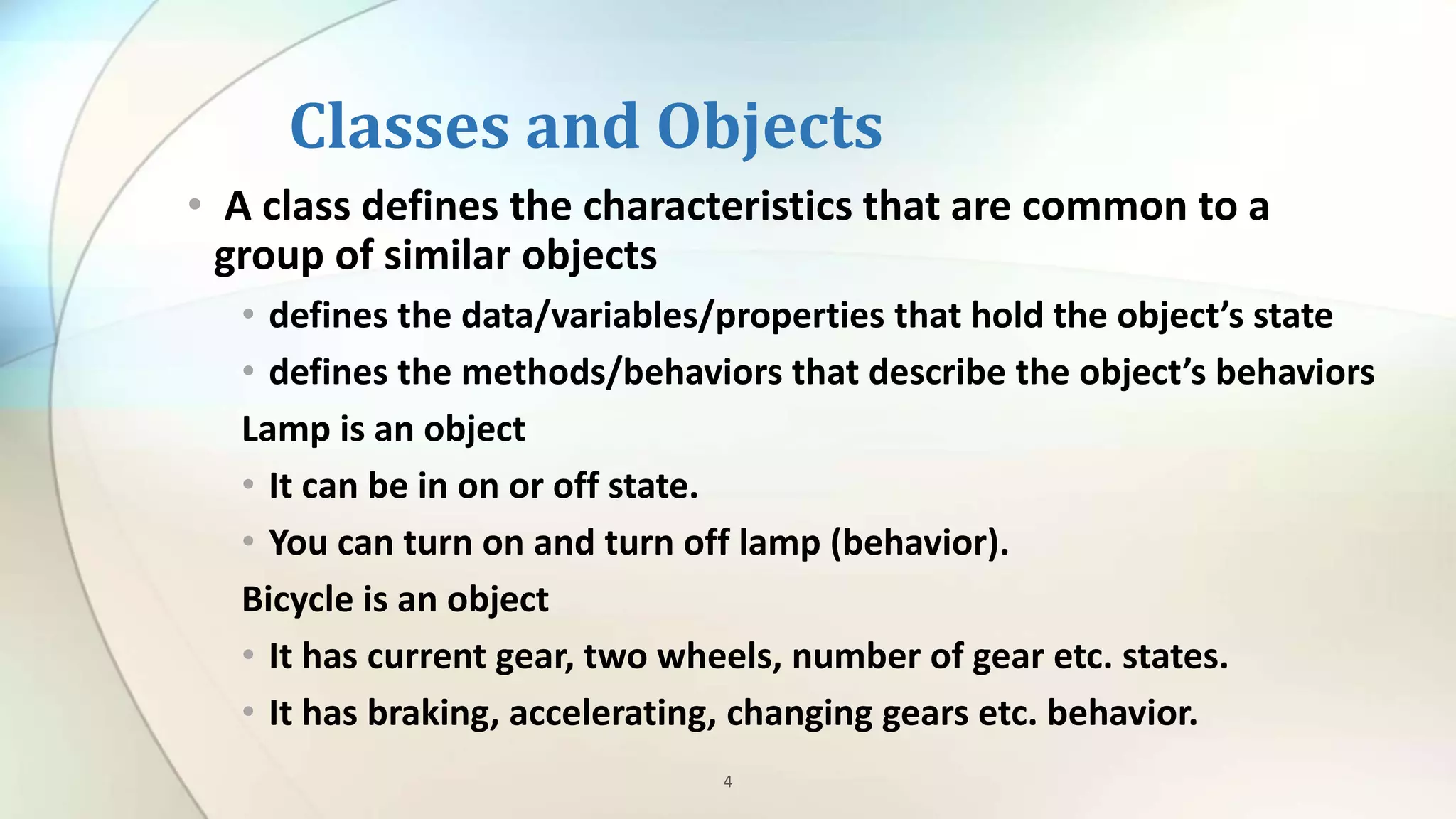
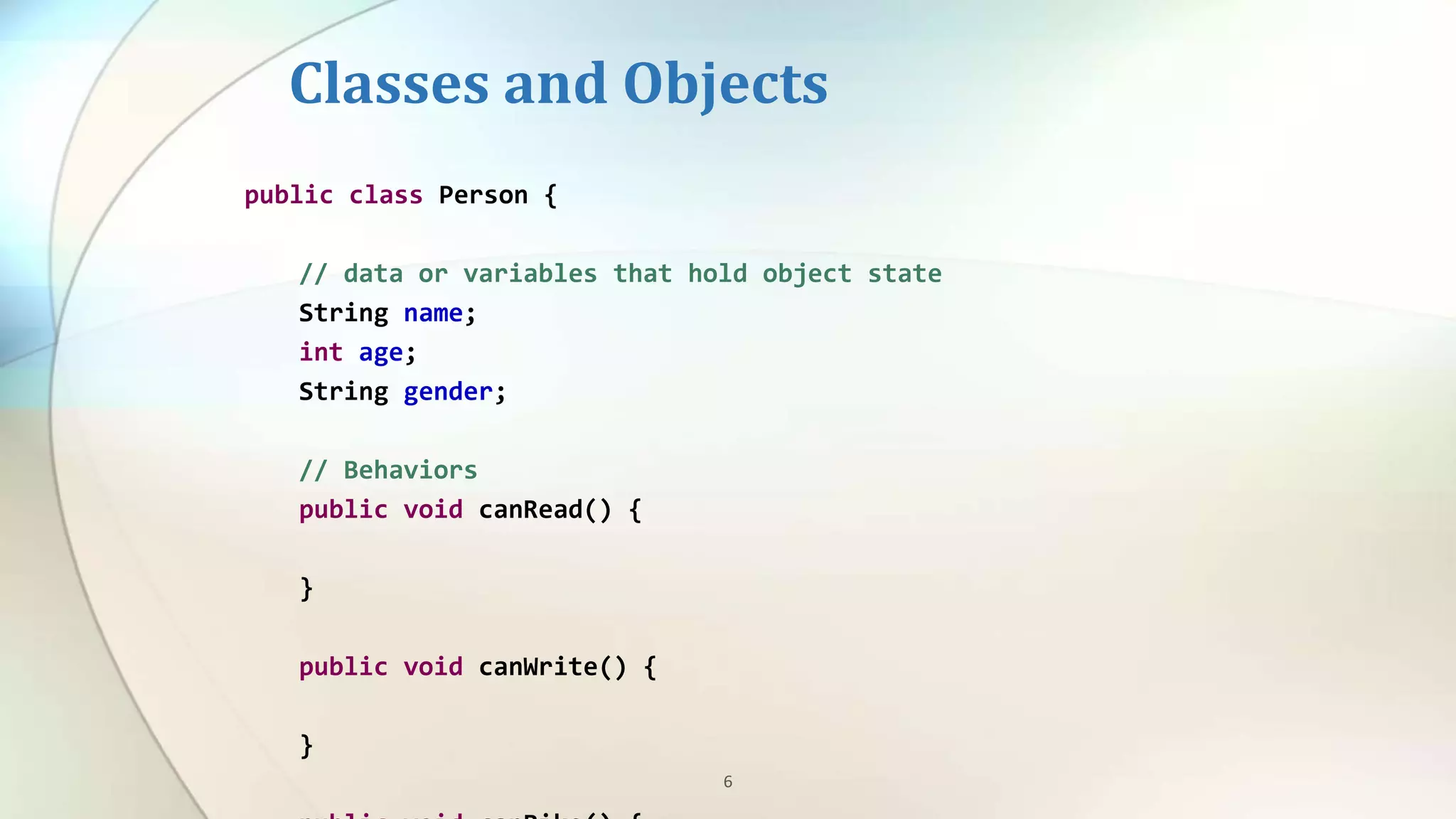
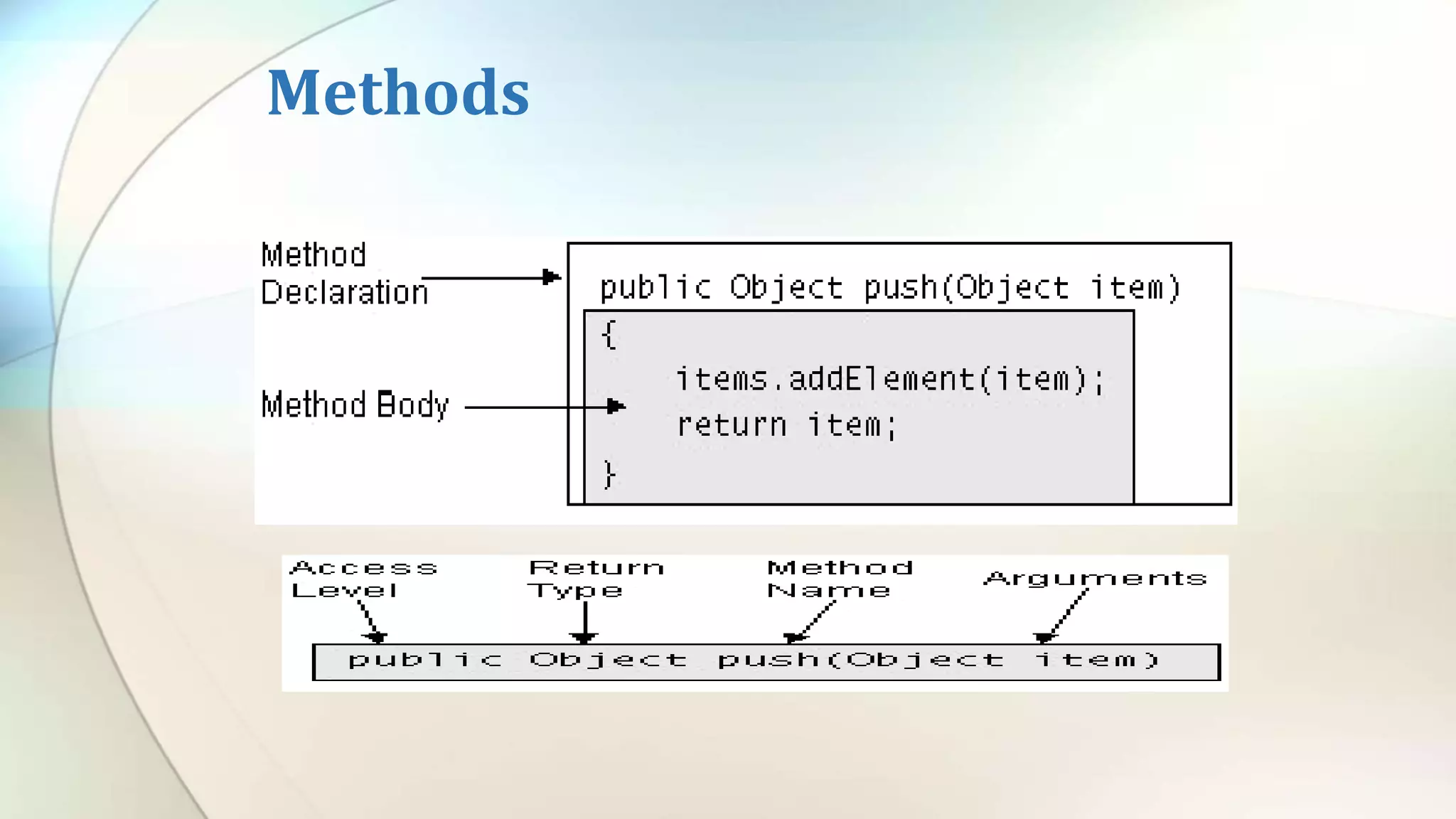
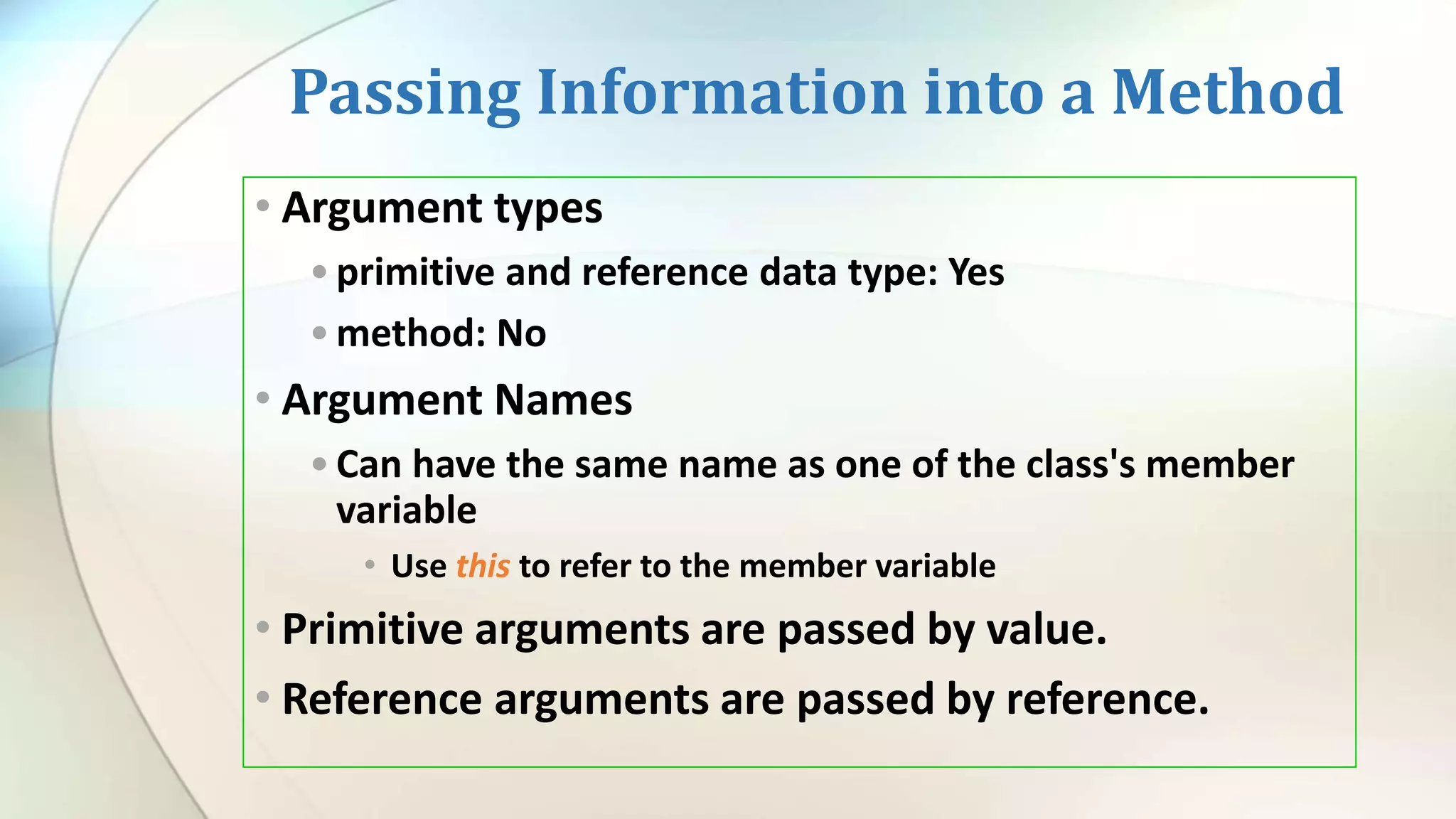
- Classes define objects with properties (variables) and behaviors (methods)
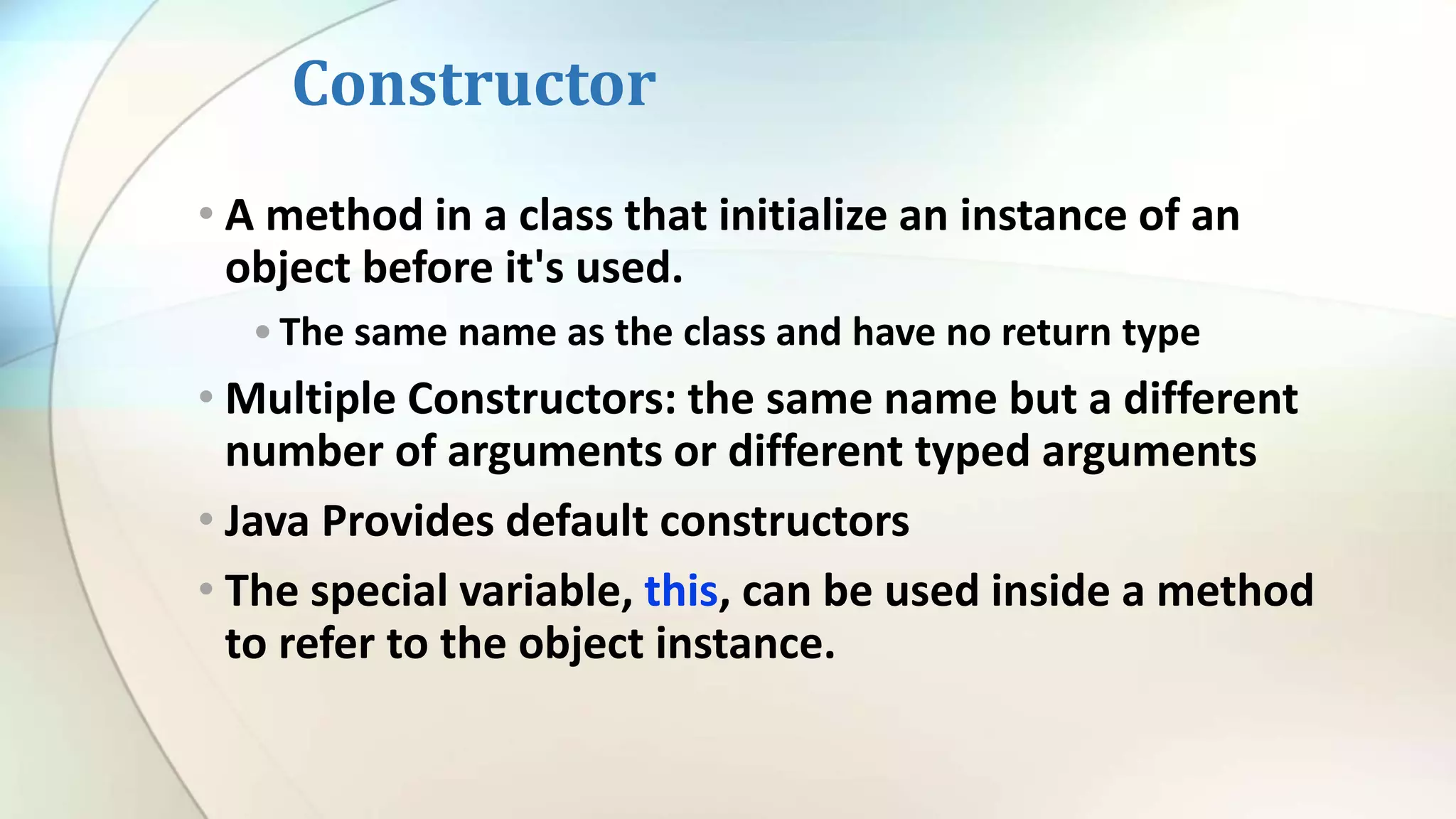
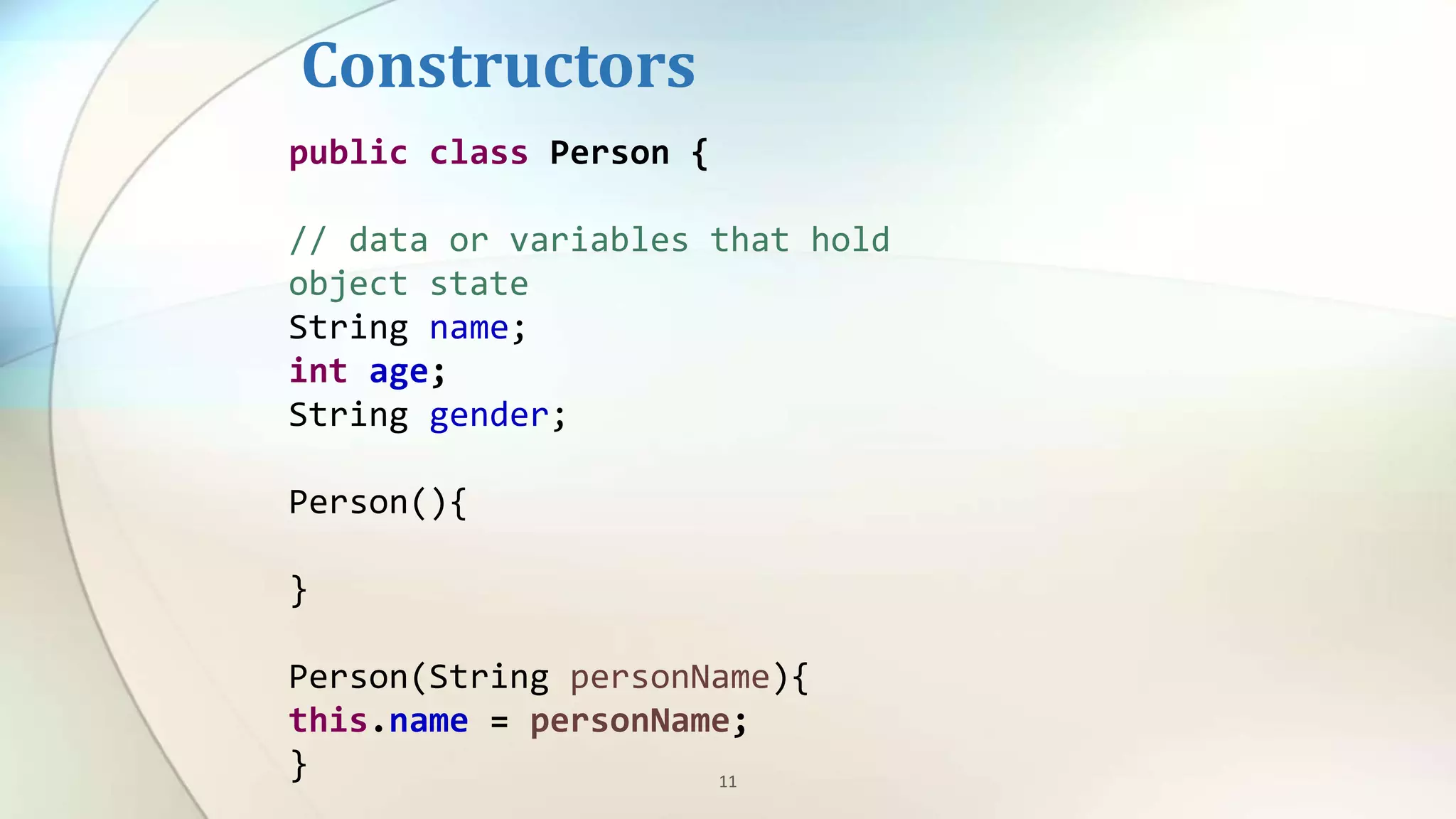
- Constructors initialize new objects
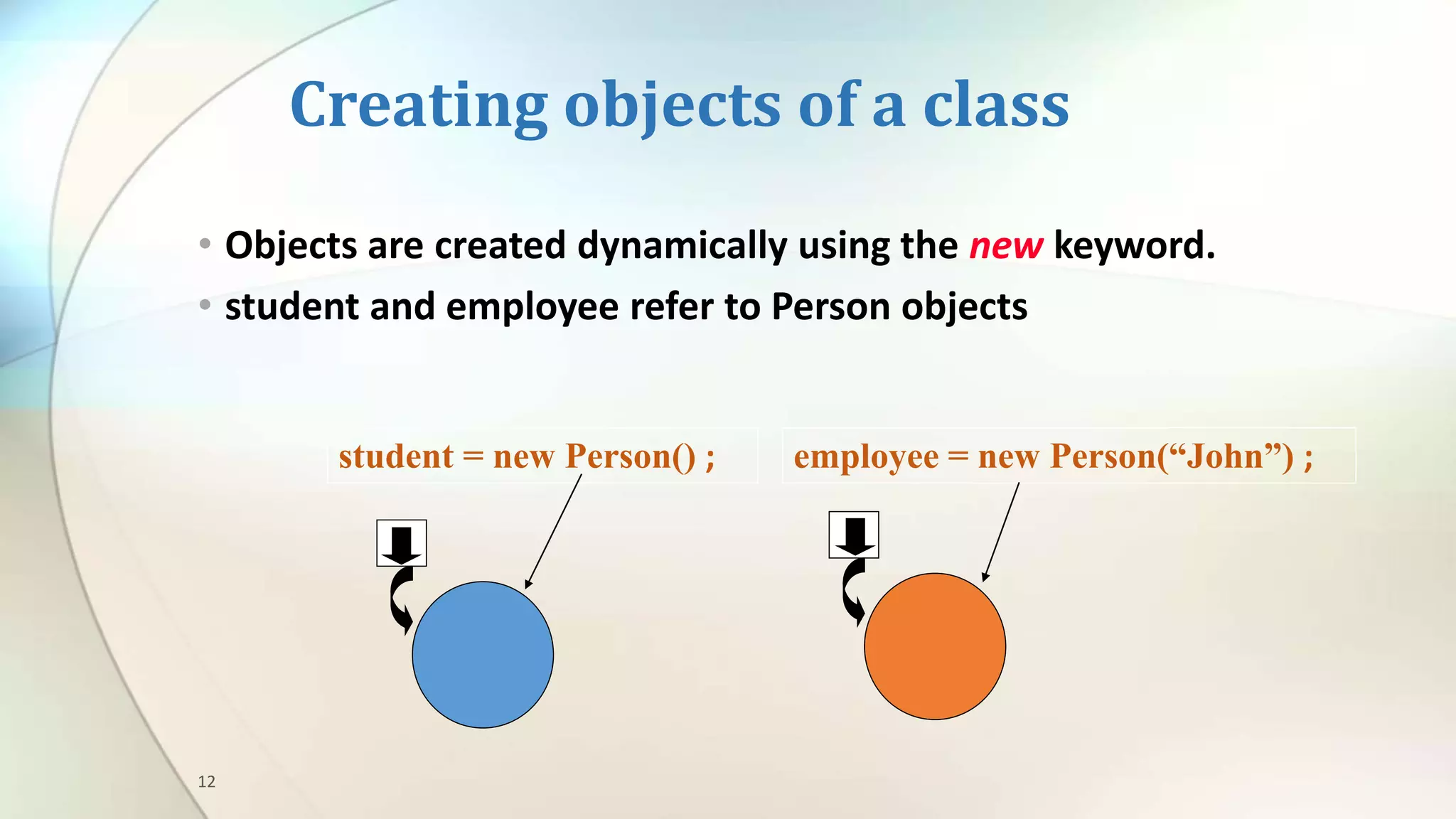
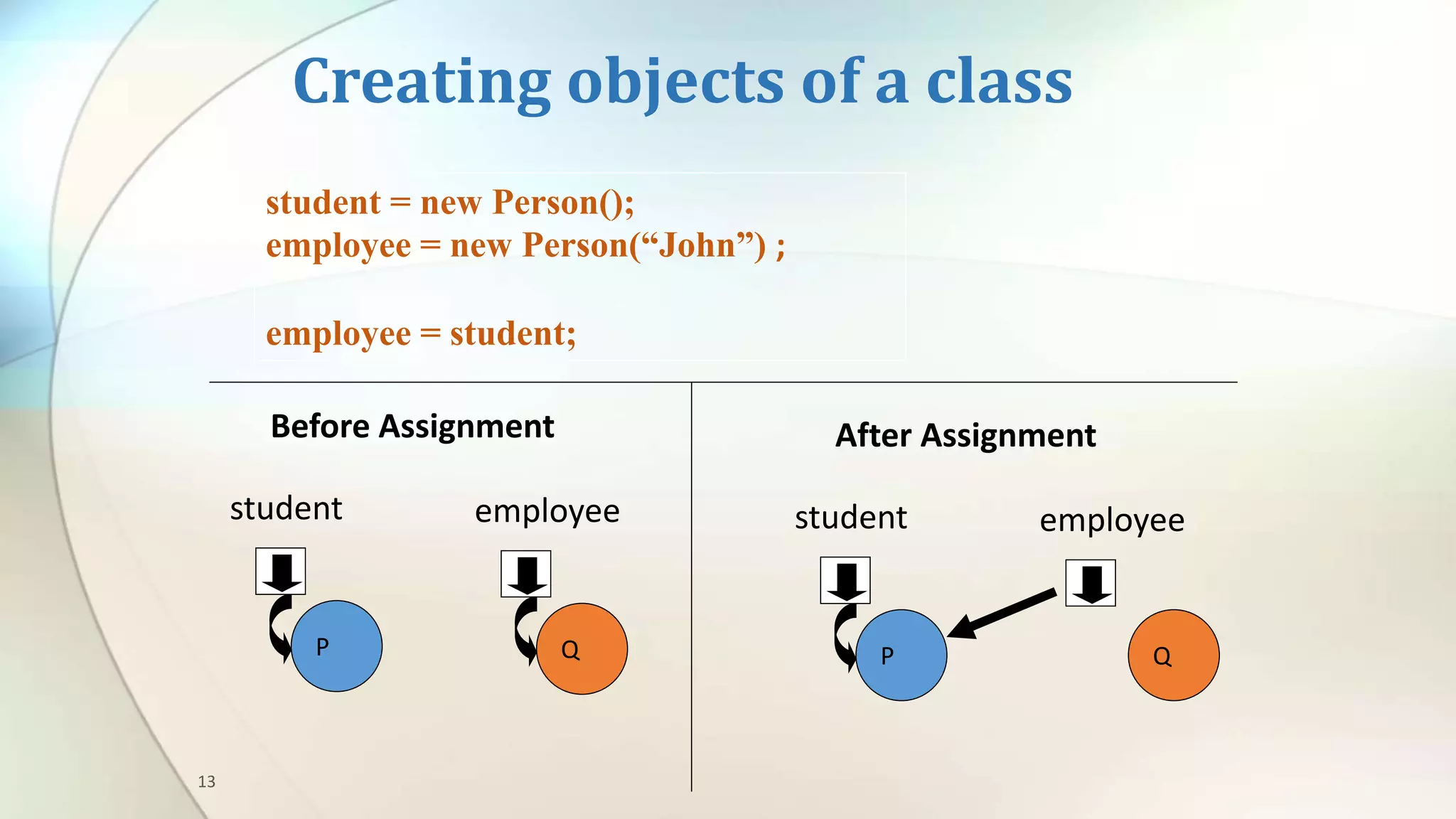
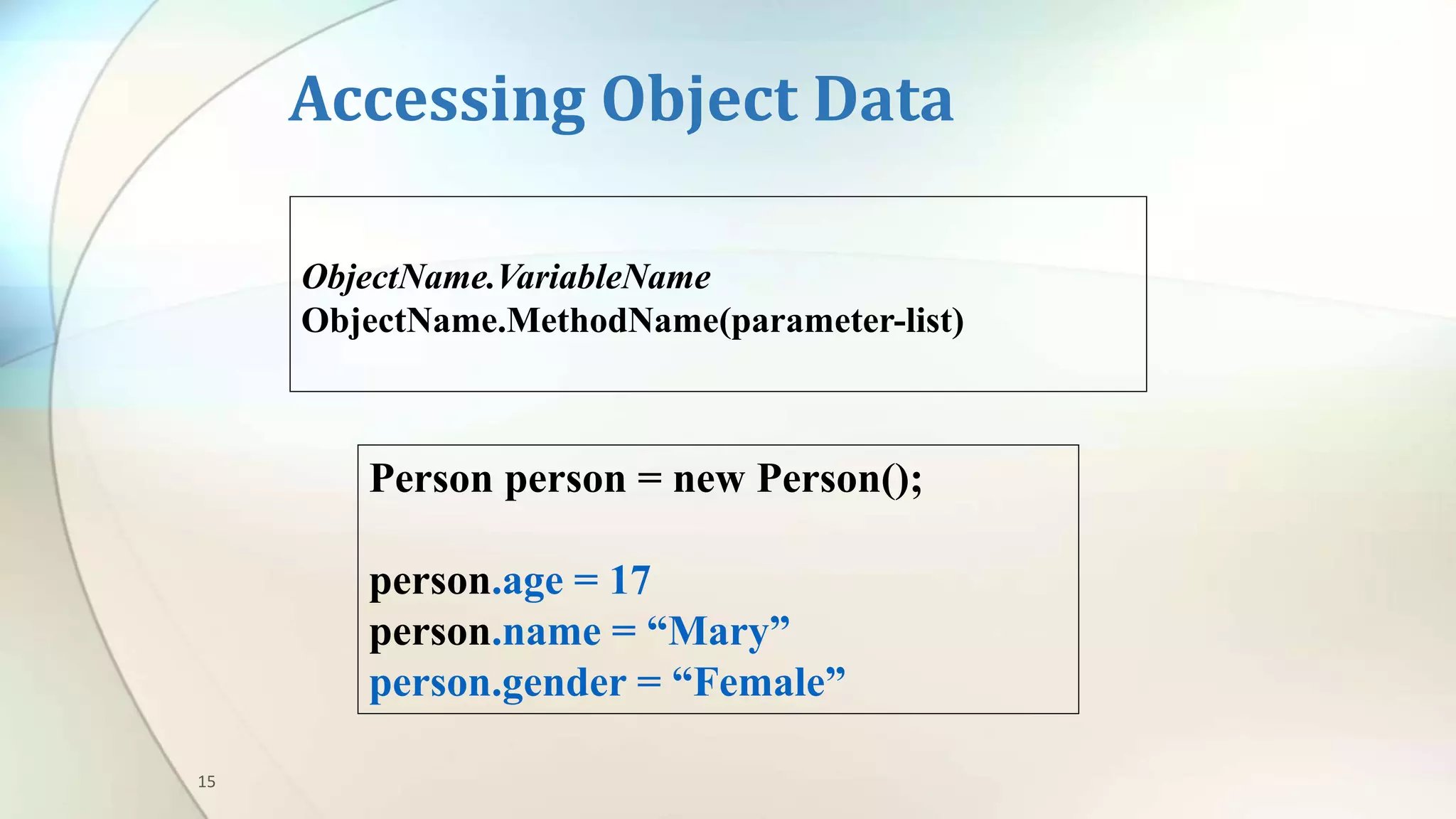
- Objects are instances of classes and access class properties and methods
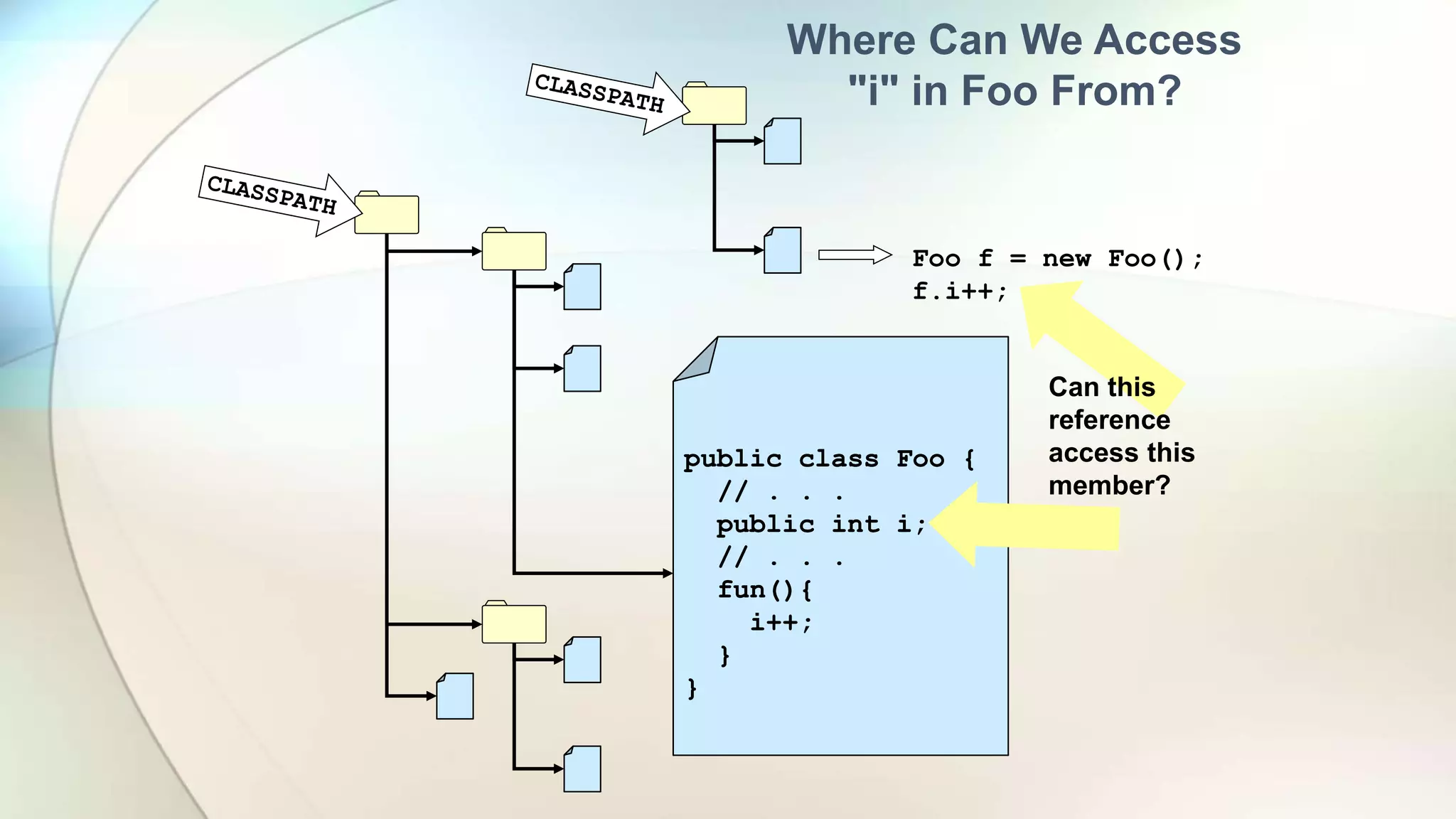
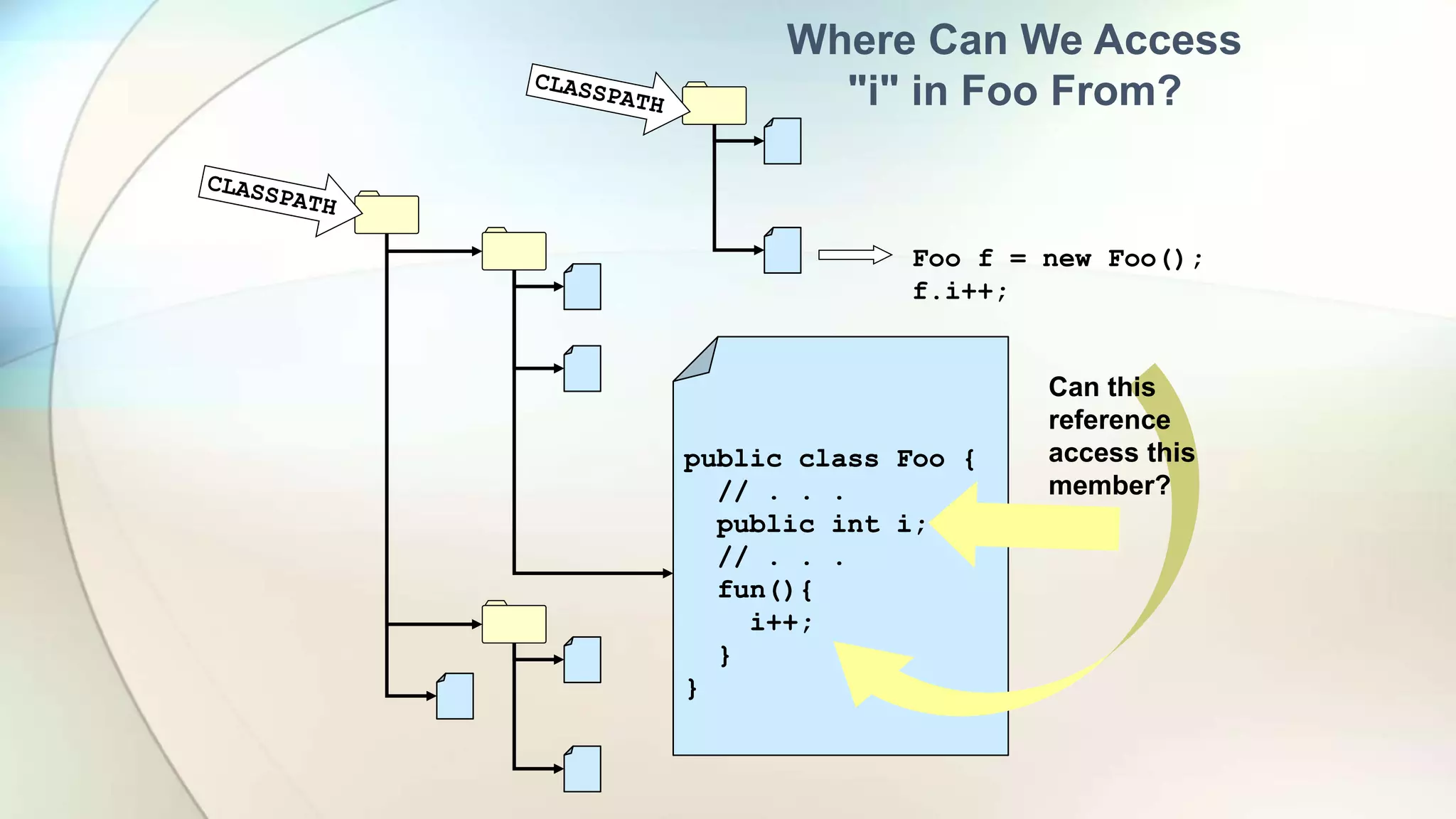
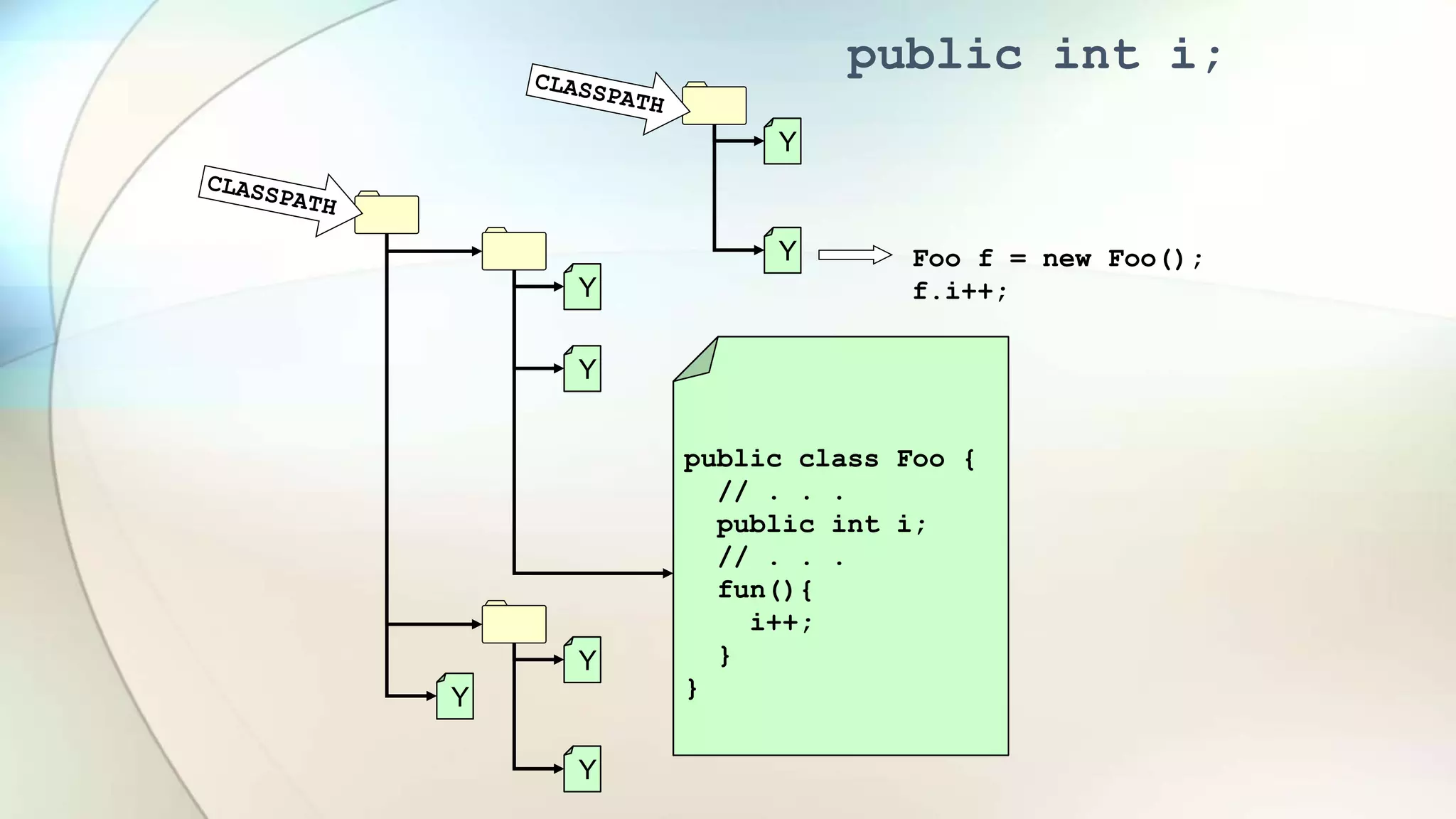
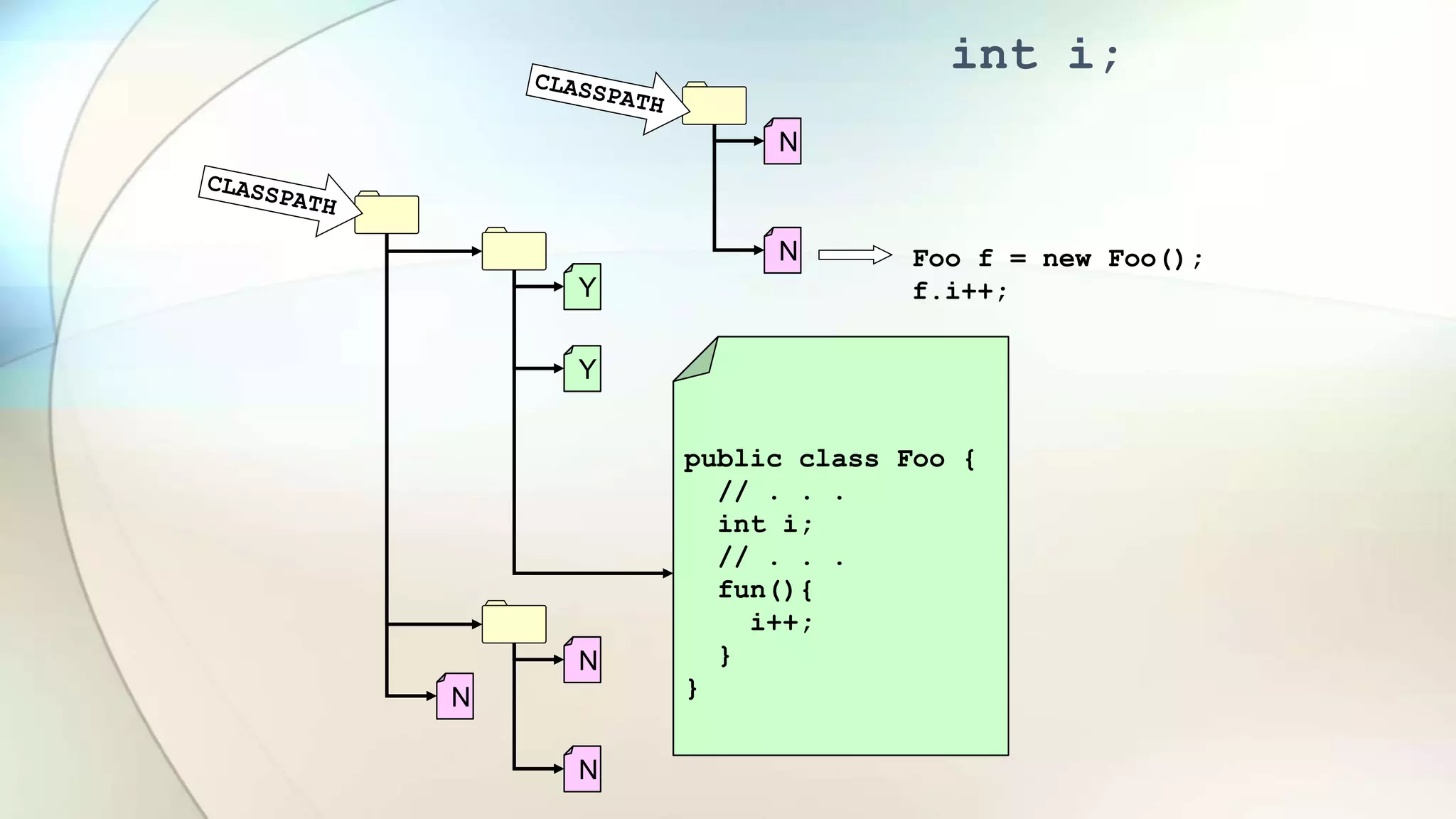
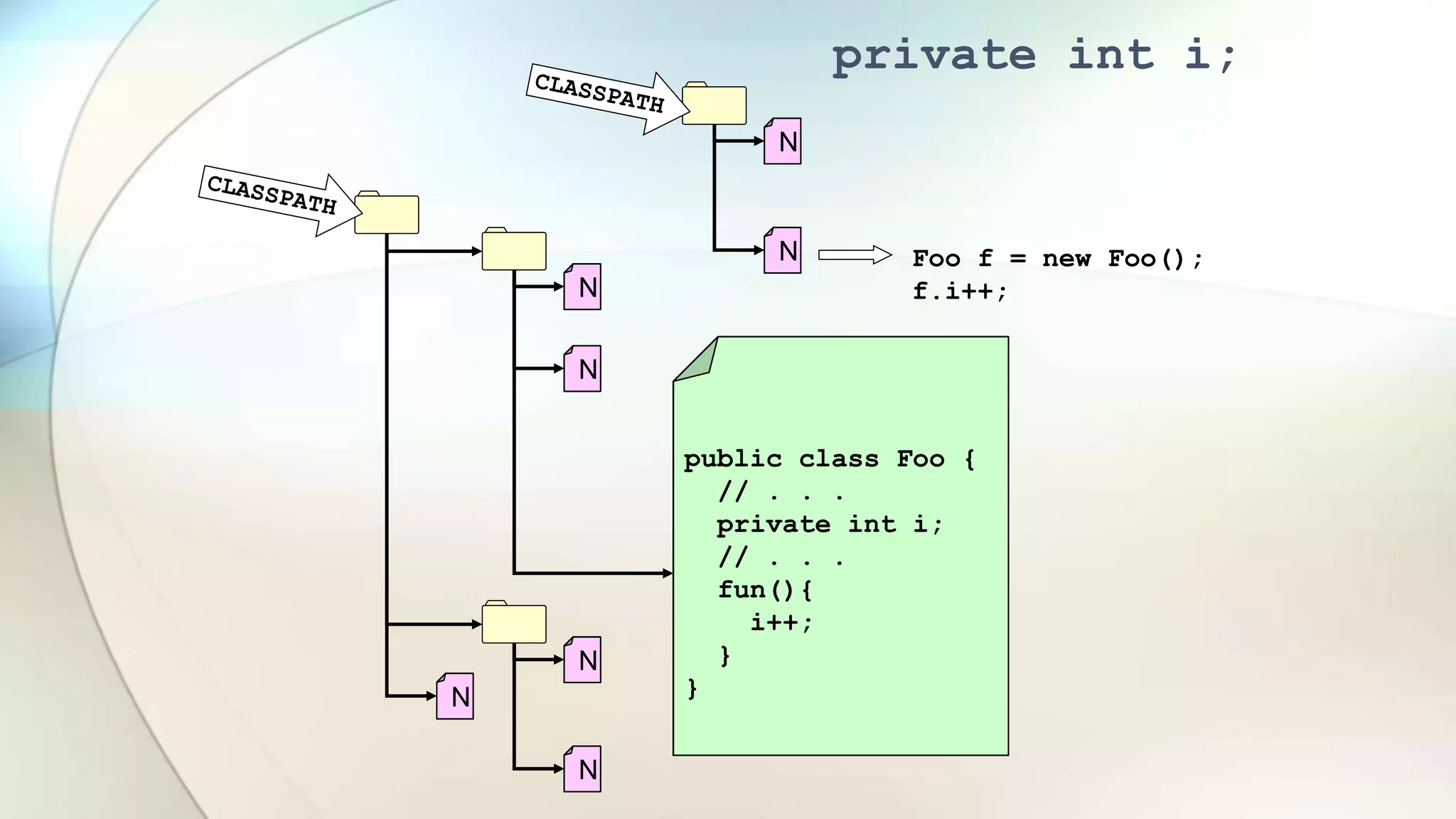
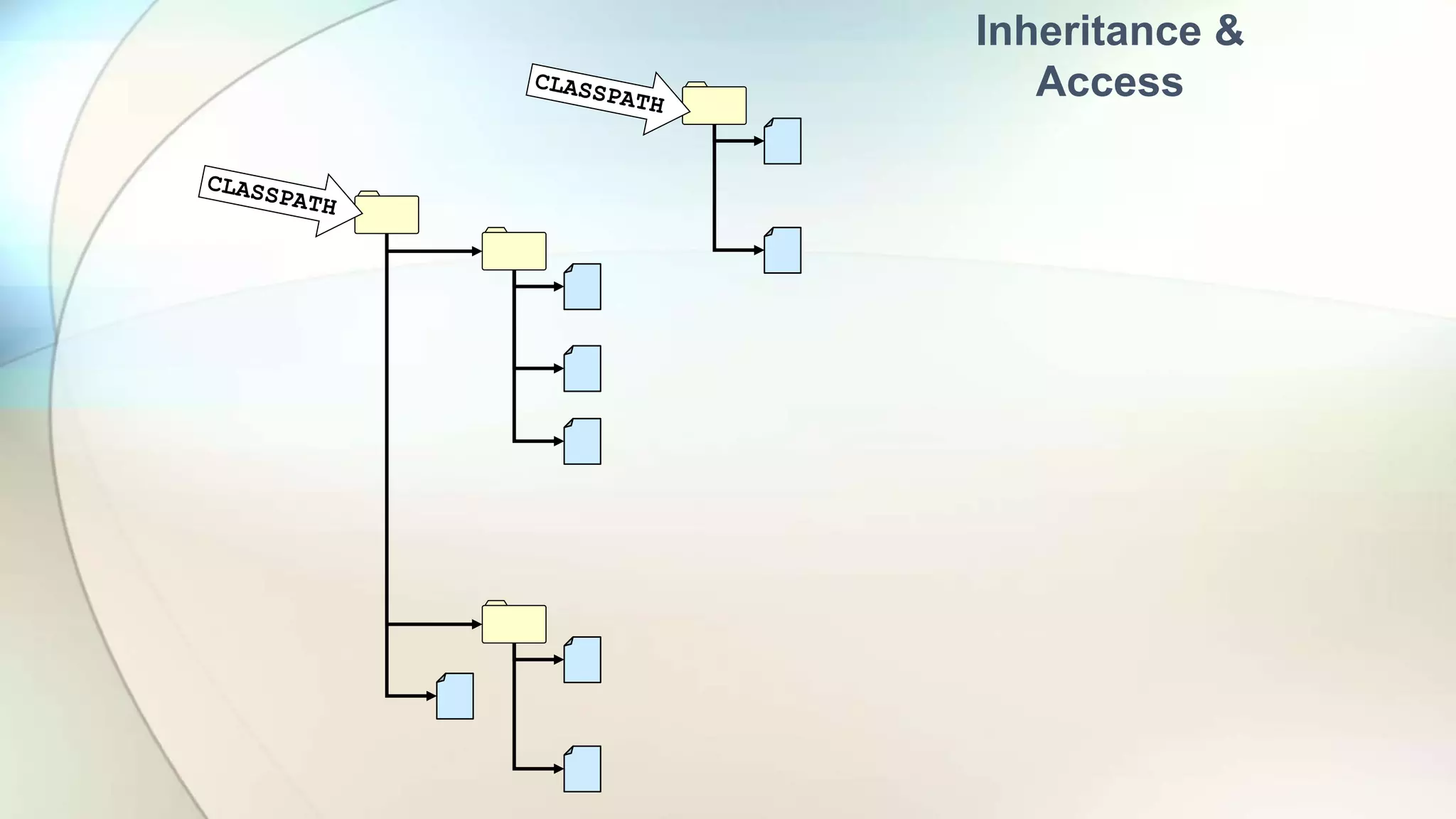
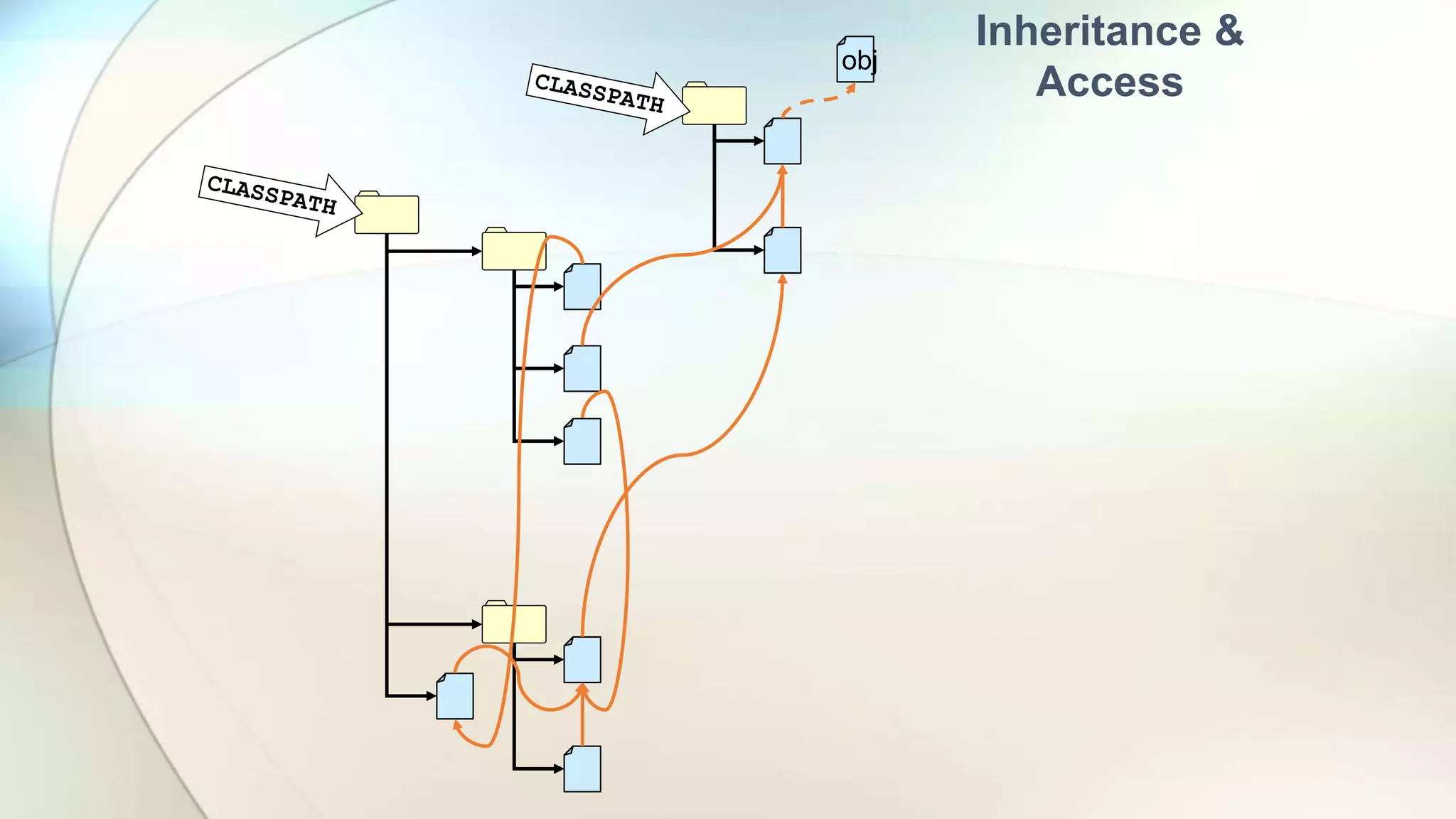
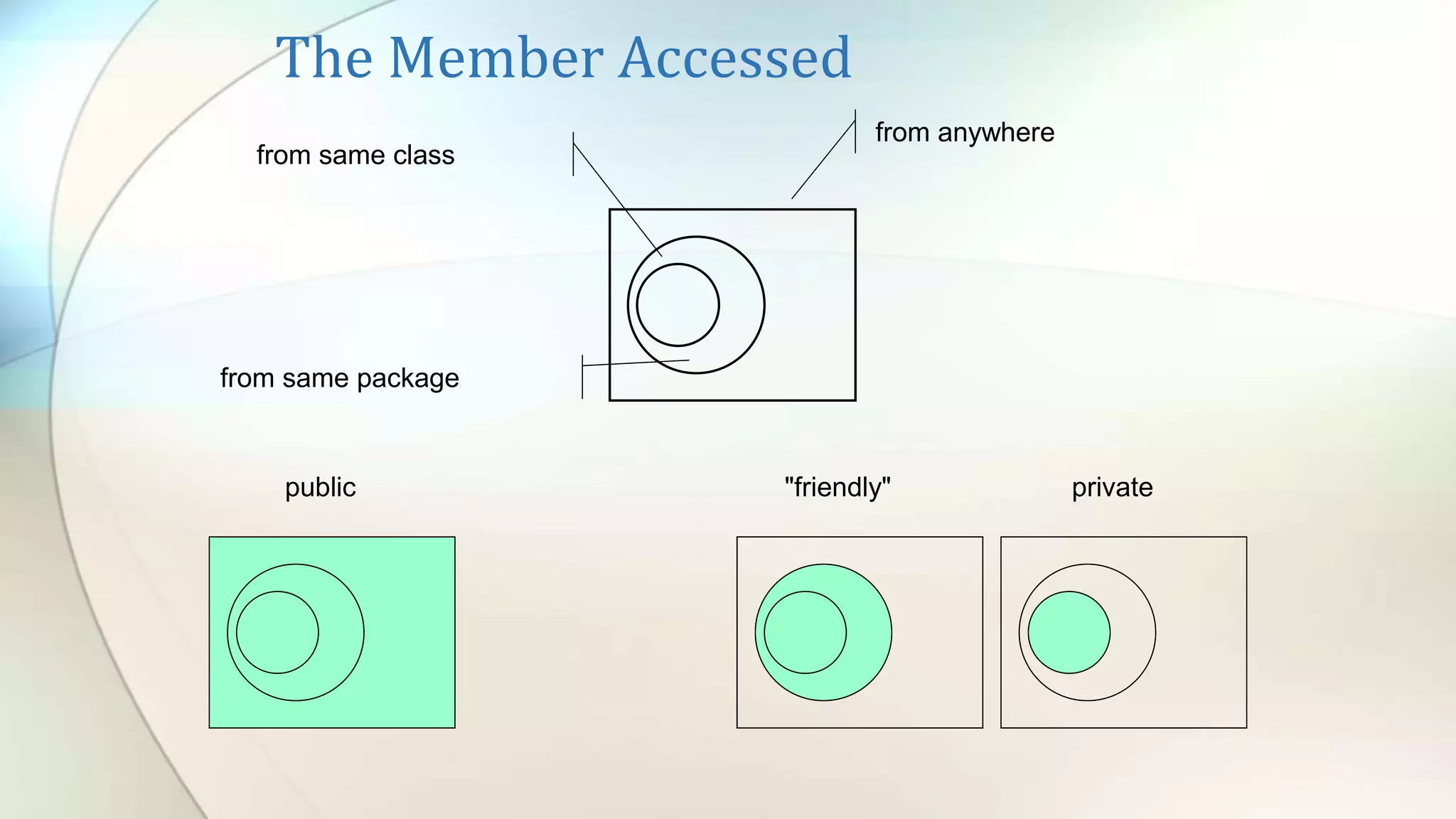
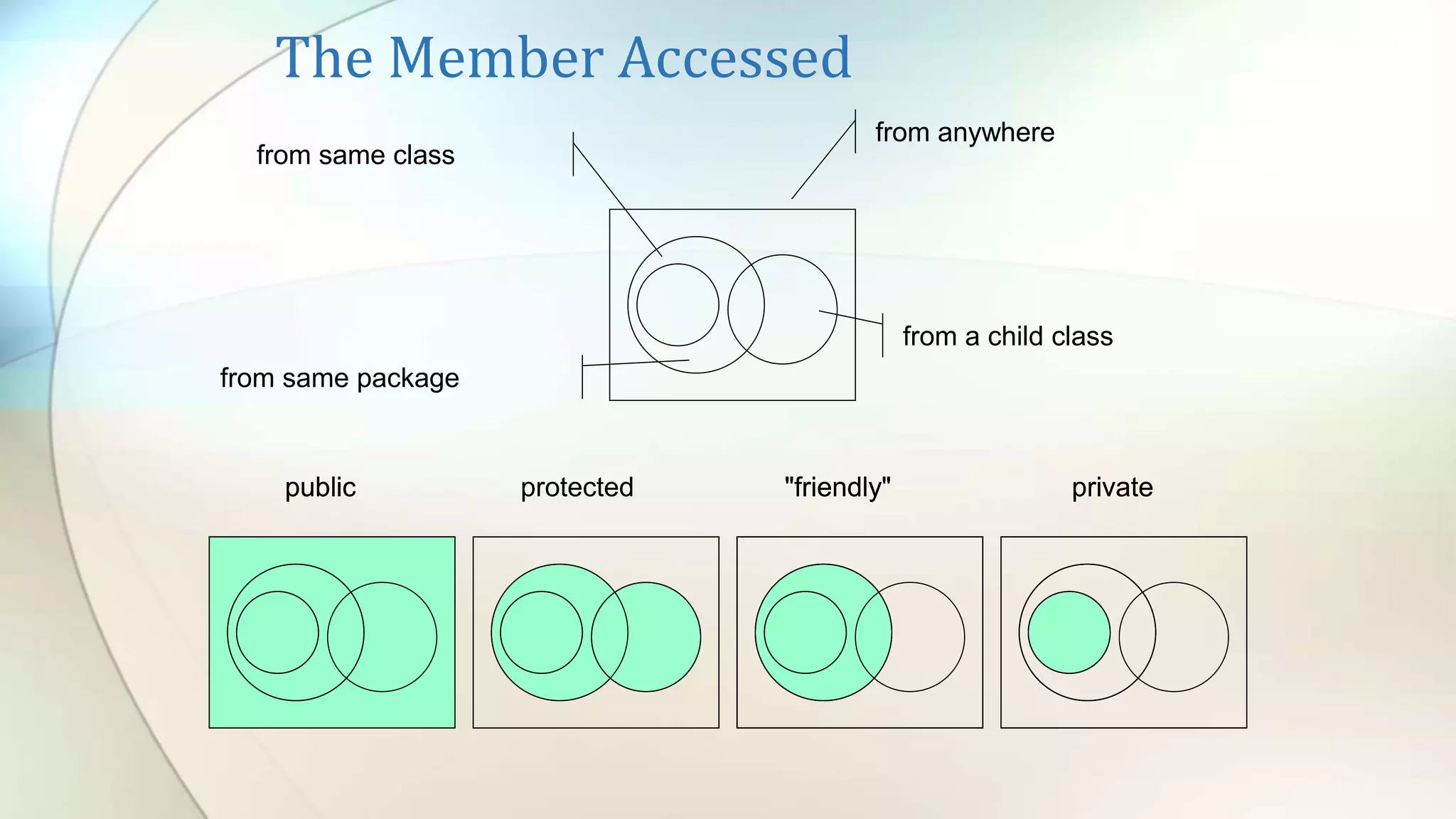
- Access modifiers (public, private, etc.) determine where properties and methods can be accessed from

![class DoFoo {
public static void main(String[] args) {
Foo f = new Foo();
f.fun();
f.i = f.i + 1;
}
}
public class Foo {
// . . .
int i;
// . . .
fun(){
i = i + 1;
}
}
new
Foo.class
javac
Access
to
What?
Access
to
Everything](https://image.slidesharecdn.com/pj01-x-classesandobjects-220320120708/75/Pj01-x-classes-and-objects-19-2048.jpg)