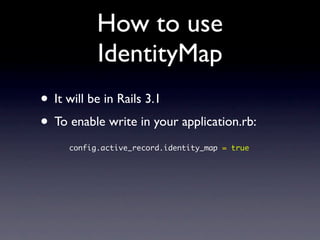
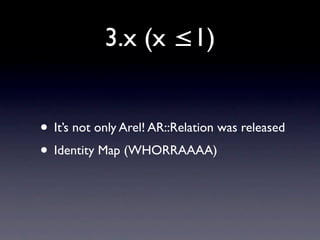
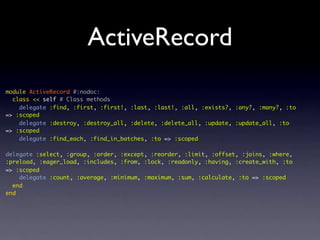
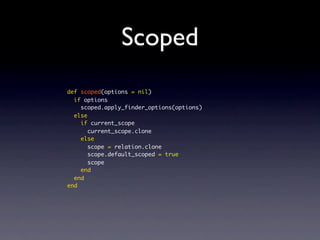
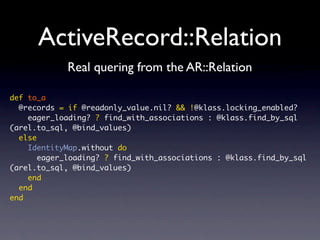
Active Record Relation (AR::Relation) allows queries to be built up in steps and later executed all at once. It provides identity mapping, which caches objects in memory to ensure that multiple queries for the same object return the same object instance. Identity mapping was added by Emilio Tagua and provides performance and consistency benefits. Developers are encouraged to contribute to further improvements in AR::Relation and identity mapping.

![Without IdentityMap
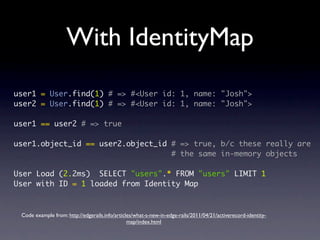
user1 = User.find(1) # => #<User id: 1, name: "Josh">
user2 = User.find(1) # => #<User id: 1, name: "Josh">
user1 == user2 # => true, b/c AR::Base recognizes that
# they have the same primary key
user1.object_id == user2.object_id # => false, b/c these are two
# different in-memory objects
User Load (0.2ms) SELECT "users".* FROM "users" WHERE "users"."id" = ? LIMIT 1 [["id", 1]]
CACHE (0.0ms) SELECT "users".* FROM "users" WHERE "users"."id" = ? LIMIT 1 [["id", 1]]
Code example from: http://edgerails.info/articles/what-s-new-in-edge-rails/2011/04/21/activerecord-identity-
map/index.html](https://image.slidesharecdn.com/ar-relationkeynote-160315141541/85/AR-Relation-19-320.jpg)
![Thread safe
• Creates for each request
• Uses Thread.current
def repository
Thread.current[:identity_map] ||= Hash.new { |h,k| h[k] = {} }
end](https://image.slidesharecdn.com/ar-relationkeynote-160315141541/85/AR-Relation-22-320.jpg)
![Interesting...
def update
@survey = Survey.find(params[:id])
@surveys = Survey.all
if @survey.update_attributes(params[:survey])
redirect_to(@survey, :notice => 'Survey was successfully updated.')
else
render :action => "edit"
end
end
def update
@survey = Survey.find(params[:id])
if @survey.update_attributes(params[:survey])
redirect_to(@survey, :notice => 'Survey was successfully updated.')
else
@surveys = Survey.all
render :action => "edit"
end
end](https://image.slidesharecdn.com/ar-relationkeynote-160315141541/85/AR-Relation-23-320.jpg)