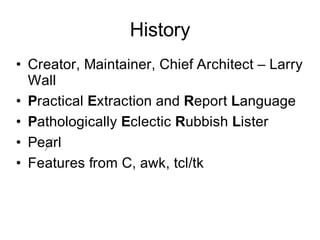
Perl was created by Larry Wall as a scripting language that combines features from C, sed, awk, and tcl. It can be used for text processing and system management tasks. Some key points about Perl include:
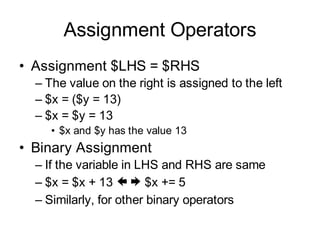
- Perl scripts have a .pl extension and are executed using the perl command. It supports scalar variables like numbers and strings as well as arrays to hold lists of data.
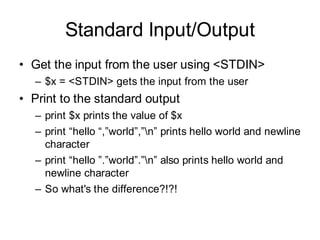
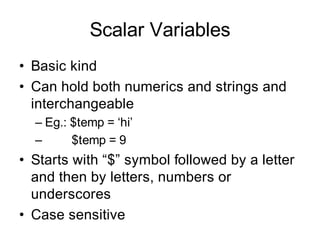
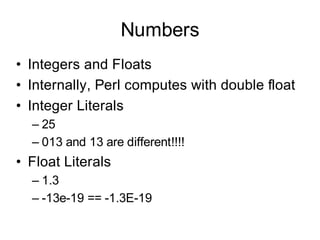
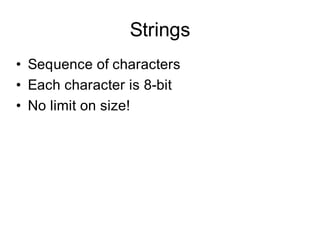
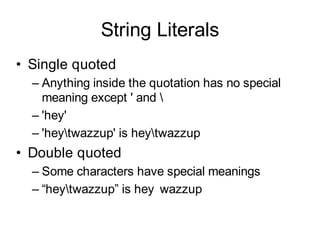
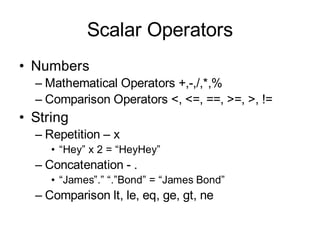
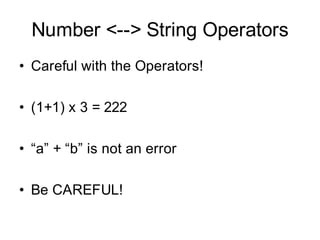
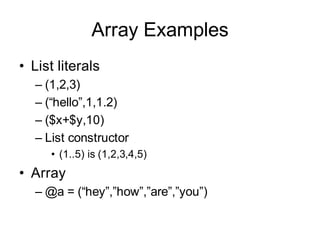
- Common data types in Perl include scalars for single values, arrays for lists, and associative arrays for key-value pairs. Strings can be delimited by single or double quotes.
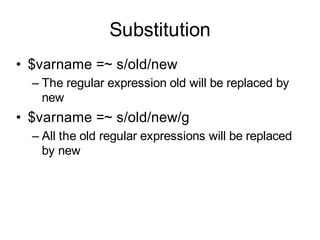
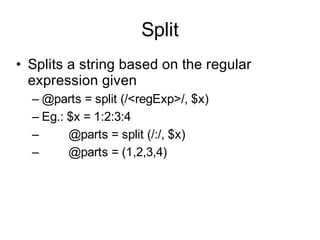
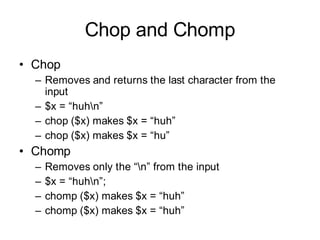
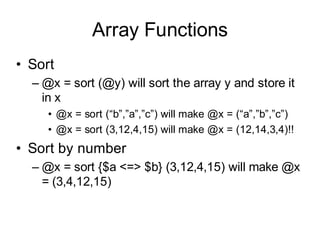
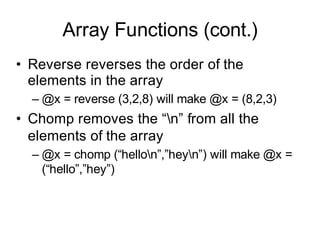
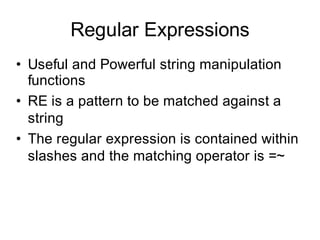
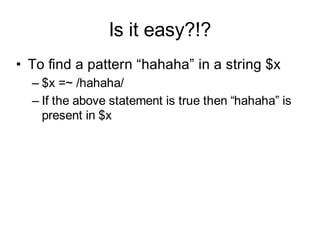
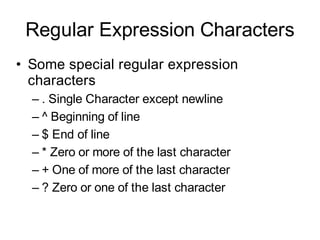
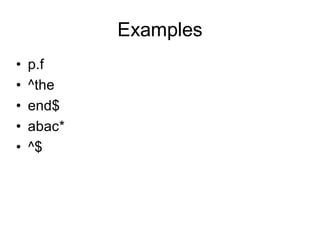
- Perl provides functions for text manipulation like regular expressions, substitution, splitting strings. Arrays can be sorted, reversed, and
![Auto [Increment, Decrement]
• Similar to C
• For both integers and float
• ++ operator adds 1 to its operand
• -- operator subtracts 1 from its operand
• $x = $y++ is different from $x = ++$y](https://image.slidesharecdn.com/2620393/85/Perl_Tutorial_v1-14-320.jpg)
![Array
• List is ordered scalar data
• Array holds list
• No limits
• Array variable name starts with @
– @var1
• Individual elements can be accessed
using $
– $var1[0] is the first element](https://image.slidesharecdn.com/2620393/85/Perl_Tutorial_v1-16-320.jpg)
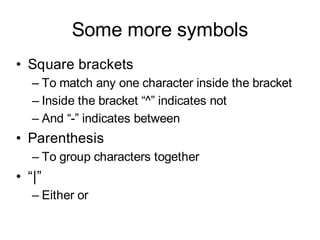
![Examples
• [aeiou]
• [^aeiou]
• [a-z]
• [0-9]
• [a-zA-Z0-9]
• hello|hey
• (ab)*](https://image.slidesharecdn.com/2620393/85/Perl_Tutorial_v1-25-320.jpg)