โจทย์ปัญหา Pbl8.1
•Download as DOCX, PDF•
1 like•490 views
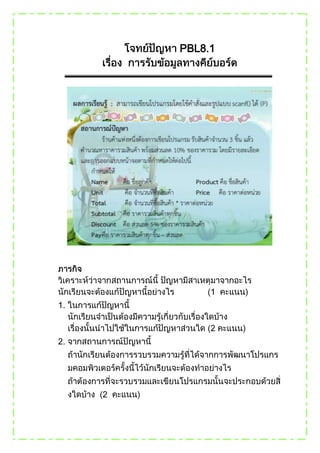
The document describes a C program that calculates the total price of two products, applies a 10% discount, and displays the results. The program prompts the user to enter their name and details of two products including unit price and quantity. It then calculates the total price, applies a 10% discount, and prints the total price and discounted amount.
Report
Share
Report
Share
Recommended
PyLadies Talk: Learn to love the command line!

This talks aims to uncover some of the magic powers of scripting and the command line.
I'll share with you some of my experience using the shell to schedule backups of a git repository or to find strings in files of unknown name and location.
And then you might see that it is a tough love!
Recommended
PyLadies Talk: Learn to love the command line!

This talks aims to uncover some of the magic powers of scripting and the command line.
I'll share with you some of my experience using the shell to schedule backups of a git repository or to find strings in files of unknown name and location.
And then you might see that it is a tough love!
DataStructures notes

Circular Queue, Double Ended Queue, Priority Queue, Applications of stacks, Applications of queue, Recursion,implementing stack using linked list, implementing queue using linked list,josephus problem, removing negatives values from queue
11 1 포인터

이 강의에서는 C언어의 가장 도전적인 주제인 포인터에 대하여 알아보겠습니다. C언어에서 포인터는 그 문법이 어렵기는 하지만 매우 강력한 기능이 있어서 널리 사용됩니다.
구체적으로 포인터는 컴퓨터 메모리에 있는 자료값이나 변수 혹은 함수의 주소를 가지는 변수로 다른 객체를 참조(refer)하기 위해서 사용됩니다.
여기에서는 컴퓨터의 메모리 구조와 주소연산, 그리고 포인터를 이용한 변수의 참조에 대해서도 살펴보겠습니다.
- Youtube 강의동영상
https://youtu.be/tIyTQ2VWSKo
- 코드는 여기에서 다운 받으세요
https://github.com/dongupak/Basic-C-Programming
Static and dynamic scoping

This presentation is all about Static and Dynamic rule used in the programming , It is important to understand the scope of variable and how program is processed inside the memory.
I hope this (.ppt) will be helpful to students studying Computer Science :)
Castle Vale Health and Wellbeing Board Presentation

An overview of the Castle Vale estate that was presented to the Castle Vale Health and Wellbeing Board on the 6th September.
More Related Content
What's hot
DataStructures notes

Circular Queue, Double Ended Queue, Priority Queue, Applications of stacks, Applications of queue, Recursion,implementing stack using linked list, implementing queue using linked list,josephus problem, removing negatives values from queue
11 1 포인터

이 강의에서는 C언어의 가장 도전적인 주제인 포인터에 대하여 알아보겠습니다. C언어에서 포인터는 그 문법이 어렵기는 하지만 매우 강력한 기능이 있어서 널리 사용됩니다.
구체적으로 포인터는 컴퓨터 메모리에 있는 자료값이나 변수 혹은 함수의 주소를 가지는 변수로 다른 객체를 참조(refer)하기 위해서 사용됩니다.
여기에서는 컴퓨터의 메모리 구조와 주소연산, 그리고 포인터를 이용한 변수의 참조에 대해서도 살펴보겠습니다.
- Youtube 강의동영상
https://youtu.be/tIyTQ2VWSKo
- 코드는 여기에서 다운 받으세요
https://github.com/dongupak/Basic-C-Programming
Static and dynamic scoping

This presentation is all about Static and Dynamic rule used in the programming , It is important to understand the scope of variable and how program is processed inside the memory.
I hope this (.ppt) will be helpful to students studying Computer Science :)
What's hot (18)
Viewers also liked
Castle Vale Health and Wellbeing Board Presentation

An overview of the Castle Vale estate that was presented to the Castle Vale Health and Wellbeing Board on the 6th September.
Public Health Transformation Workshop 1 

Slides to support Birmingham's first Public Health Workshop.
Community Budget Pilot Programme Presentation

A presentation on the Community Budget Pilot that is taking place in Castle Vale, Birmingham.
Birmingham City Council - Governance arrangements

Governance Arrangements for Birmingham City Council
West Midlands Assets Seminar nov 2012

A presentation from Tevor Hopkins from Asset Based Consulting (http://www.assetbasedconsulting.co.uk) on an Asset Based Approach to mapping Health and Wellbeing. This presentation was organised by the LGA to support West Midlands Health and Wellbeing Boards.
Sex and the City

A presentation on Sexual Health Services in Birmingham that was presented to the Public Health Transition Workshop on the 3rd July.
Teaching Action Verbs to the Deaf

Teaching Language to the Deaf - building vocabulary and sentence structure using Sign Language.
Viewers also liked (19)
Birmingham Health & Wellbeing Board Summit - July 2012

Birmingham Health & Wellbeing Board Summit - July 2012
Castle Vale Health and Wellbeing Board Presentation

Castle Vale Health and Wellbeing Board Presentation
Designing for Ownership workshop @Strelka Summerschool 2012

Designing for Ownership workshop @Strelka Summerschool 2012
Similar to โจทย์ปัญหา Pbl8.1
The solution manual of programming in ansi by Robin

solution manual of programming in ansi c by balagurusamy 1-6 Chapters.
Wildlife conservation project management adri jovin

This was my Software Engineering Mini-project while I was doing my UG in St.Xavier's Catholic College of Engineering
System Software/Operating Sytems lab report

This is my lab report for the System Software Lab ,APJ Abdul Kalam Kerala Technological University,Kerala-S5 Computer Science.Hope you guys appreciate it.
System Software /Operating System Lab Report

This is my report of System Software/Operating System lab for APJ Abdul Kalaam Kerala Technological University ,B Tech,S5 Computer Science.Please pardon me if there are any mistakes.
Functions in c

PowerPoint presentation of functions in C language. It will give you brief idea how function works in C along with its unique features like return statement.
DOS

SATYAJIT DASH SATYAJIT DASH SATYAJIT DASH SATYAJIT DASH SATYAJIT DASH SATYAJIT DASH SATYAJIT DASH SATYAJIT DASH SATYAJIT DASH SATYAJIT DASH
Similar to โจทย์ปัญหา Pbl8.1 (20)
The solution manual of programming in ansi by Robin

The solution manual of programming in ansi by Robin
Project code for Project on Student information management system

Project code for Project on Student information management system
Wildlife conservation project management adri jovin

Wildlife conservation project management adri jovin
More from anusong
More from anusong (7)
Recently uploaded
From Siloed Products to Connected Ecosystem: Building a Sustainable and Scala...

From Siloed Products to Connected Ecosystem: Building a Sustainable and Scalable Platform by VP of Product, The New York Times
Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024

As AI technology is pushing into IT I was wondering myself, as an “infrastructure container kubernetes guy”, how get this fancy AI technology get managed from an infrastructure operational view? Is it possible to apply our lovely cloud native principals as well? What benefit’s both technologies could bring to each other?
Let me take this questions and provide you a short journey through existing deployment models and use cases for AI software. On practical examples, we discuss what cloud/on-premise strategy we may need for applying it to our own infrastructure to get it to work from an enterprise perspective. I want to give an overview about infrastructure requirements and technologies, what could be beneficial or limiting your AI use cases in an enterprise environment. An interactive Demo will give you some insides, what approaches I got already working for real.
Builder.ai Founder Sachin Dev Duggal's Strategic Approach to Create an Innova...

In today's fast-changing business world, Companies that adapt and embrace new ideas often need help to keep up with the competition. However, fostering a culture of innovation takes much work. It takes vision, leadership and willingness to take risks in the right proportion. Sachin Dev Duggal, co-founder of Builder.ai, has perfected the art of this balance, creating a company culture where creativity and growth are nurtured at each stage.
Generating a custom Ruby SDK for your web service or Rails API using Smithy

Have you ever wanted a Ruby client API to communicate with your web service? Smithy is a protocol-agnostic language for defining services and SDKs. Smithy Ruby is an implementation of Smithy that generates a Ruby SDK using a Smithy model. In this talk, we will explore Smithy and Smithy Ruby to learn how to generate custom feature-rich SDKs that can communicate with any web service, such as a Rails JSON API.
How world-class product teams are winning in the AI era by CEO and Founder, P...

How world-class product teams are winning in the AI era by CEO and Founder, Product School
Bits & Pixels using AI for Good.........

A whirlwind tour of tech & AI for socio-environmental impact.
UiPath Test Automation using UiPath Test Suite series, part 4

Welcome to UiPath Test Automation using UiPath Test Suite series part 4. In this session, we will cover Test Manager overview along with SAP heatmap.
The UiPath Test Manager overview with SAP heatmap webinar offers a concise yet comprehensive exploration of the role of a Test Manager within SAP environments, coupled with the utilization of heatmaps for effective testing strategies.
Participants will gain insights into the responsibilities, challenges, and best practices associated with test management in SAP projects. Additionally, the webinar delves into the significance of heatmaps as a visual aid for identifying testing priorities, areas of risk, and resource allocation within SAP landscapes. Through this session, attendees can expect to enhance their understanding of test management principles while learning practical approaches to optimize testing processes in SAP environments using heatmap visualization techniques
What will you get from this session?
1. Insights into SAP testing best practices
2. Heatmap utilization for testing
3. Optimization of testing processes
4. Demo
Topics covered:
Execution from the test manager
Orchestrator execution result
Defect reporting
SAP heatmap example with demo
Speaker:
Deepak Rai, Automation Practice Lead, Boundaryless Group and UiPath MVP
De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovati...

De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovation With Your Product by VP of Product Design, Warner Music Group
Assuring Contact Center Experiences for Your Customers With ThousandEyes

Presented by Suzanne Phillips and Alex Marcotte
GenAISummit 2024 May 28 Sri Ambati Keynote: AGI Belongs to The Community in O...

“AGI should be open source and in the public domain at the service of humanity and the planet.”
Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf

91mobiles recently conducted a Smart TV Buyer Insights Survey in which we asked over 3,000 respondents about the TV they own, aspects they look at on a new TV, and their TV buying preferences.
DevOps and Testing slides at DASA Connect

My and Rik Marselis slides at 30.5.2024 DASA Connect conference. We discuss about what is testing, then what is agile testing and finally what is Testing in DevOps. Finally we had lovely workshop with the participants trying to find out different ways to think about quality and testing in different parts of the DevOps infinity loop.
Empowering NextGen Mobility via Large Action Model Infrastructure (LAMI): pav...

Empowering NextGen Mobility via Large Action Model Infrastructure (LAMI)
To Graph or Not to Graph Knowledge Graph Architectures and LLMs

Reflecting on new architectures for knowledge based systems in light of generative ai
State of ICS and IoT Cyber Threat Landscape Report 2024 preview

The IoT and OT threat landscape report has been prepared by the Threat Research Team at Sectrio using data from Sectrio, cyber threat intelligence farming facilities spread across over 85 cities around the world. In addition, Sectrio also runs AI-based advanced threat and payload engagement facilities that serve as sinks to attract and engage sophisticated threat actors, and newer malware including new variants and latent threats that are at an earlier stage of development.
The latest edition of the OT/ICS and IoT security Threat Landscape Report 2024 also covers:
State of global ICS asset and network exposure
Sectoral targets and attacks as well as the cost of ransom
Global APT activity, AI usage, actor and tactic profiles, and implications
Rise in volumes of AI-powered cyberattacks
Major cyber events in 2024
Malware and malicious payload trends
Cyberattack types and targets
Vulnerability exploit attempts on CVEs
Attacks on counties – USA
Expansion of bot farms – how, where, and why
In-depth analysis of the cyber threat landscape across North America, South America, Europe, APAC, and the Middle East
Why are attacks on smart factories rising?
Cyber risk predictions
Axis of attacks – Europe
Systemic attacks in the Middle East
Download the full report from here:
https://sectrio.com/resources/ot-threat-landscape-reports/sectrio-releases-ot-ics-and-iot-security-threat-landscape-report-2024/
Designing Great Products: The Power of Design and Leadership by Chief Designe...

Designing Great Products: The Power of Design and Leadership by Chief Designer, Beats by Dr Dre
Key Trends Shaping the Future of Infrastructure.pdf

Keynote at DIGIT West Expo, Glasgow on 29 May 2024.
Cheryl Hung, ochery.com
Sr Director, Infrastructure Ecosystem, Arm.
The key trends across hardware, cloud and open-source; exploring how these areas are likely to mature and develop over the short and long-term, and then considering how organisations can position themselves to adapt and thrive.
Recently uploaded (20)
From Siloed Products to Connected Ecosystem: Building a Sustainable and Scala...

From Siloed Products to Connected Ecosystem: Building a Sustainable and Scala...
Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024

Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024
Builder.ai Founder Sachin Dev Duggal's Strategic Approach to Create an Innova...

Builder.ai Founder Sachin Dev Duggal's Strategic Approach to Create an Innova...
Generating a custom Ruby SDK for your web service or Rails API using Smithy

Generating a custom Ruby SDK for your web service or Rails API using Smithy
How world-class product teams are winning in the AI era by CEO and Founder, P...

How world-class product teams are winning in the AI era by CEO and Founder, P...
FIDO Alliance Osaka Seminar: Passkeys and the Road Ahead.pdf

FIDO Alliance Osaka Seminar: Passkeys and the Road Ahead.pdf
FIDO Alliance Osaka Seminar: Passkeys at Amazon.pdf

FIDO Alliance Osaka Seminar: Passkeys at Amazon.pdf
UiPath Test Automation using UiPath Test Suite series, part 4

UiPath Test Automation using UiPath Test Suite series, part 4
De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovati...

De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovati...
Assuring Contact Center Experiences for Your Customers With ThousandEyes

Assuring Contact Center Experiences for Your Customers With ThousandEyes
GenAISummit 2024 May 28 Sri Ambati Keynote: AGI Belongs to The Community in O...

GenAISummit 2024 May 28 Sri Ambati Keynote: AGI Belongs to The Community in O...
Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf

Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf
Empowering NextGen Mobility via Large Action Model Infrastructure (LAMI): pav...

Empowering NextGen Mobility via Large Action Model Infrastructure (LAMI): pav...
To Graph or Not to Graph Knowledge Graph Architectures and LLMs

To Graph or Not to Graph Knowledge Graph Architectures and LLMs
State of ICS and IoT Cyber Threat Landscape Report 2024 preview

State of ICS and IoT Cyber Threat Landscape Report 2024 preview
Designing Great Products: The Power of Design and Leadership by Chief Designe...

Designing Great Products: The Power of Design and Leadership by Chief Designe...
Key Trends Shaping the Future of Infrastructure.pdf

Key Trends Shaping the Future of Infrastructure.pdf
โจทย์ปัญหา Pbl8.1
- 1. PBL8.1 1. 2.
- 2. PBL 8.1 1. 2. 3. - 3 10% - /
- 3. http://kroohathaichon.w ordpress.com 3 10% #include <stdio.h>
- 4. #include <conio.h> main() { float U1,P1,T,U2,P2,discount; char Pd1[20],name[20],Pd2[20]; printf("n Enter your namet:t"); scanf("%s",name); printf("nPd1t:t"); scanf("%s",Pd1); printf("nU1tt:t"); scanf("%f",&U1); printf("nP1tt:t"); scanf("%f",&P1); printf("n+++++++++++++++++++++++++n"); printf("nnPd2t:t"); scanf("%s",Pd2); printf("nU2tt:t"); scanf("%f",&U2); printf("nP2tt:t"); scanf("%f",&P2); T=((U1*P1)+(U2*P2));
- 5. discount=(T*.10); printf("n+++++++++++++++++++++++++nn"); printf("Total Price ==>t:t%.2f",T); printf("n+++++++++++++++++++++++++nn"); printf("ndiscount 10% ==>t:t%.2f",discount); getch(); } 5 3-4 1-2