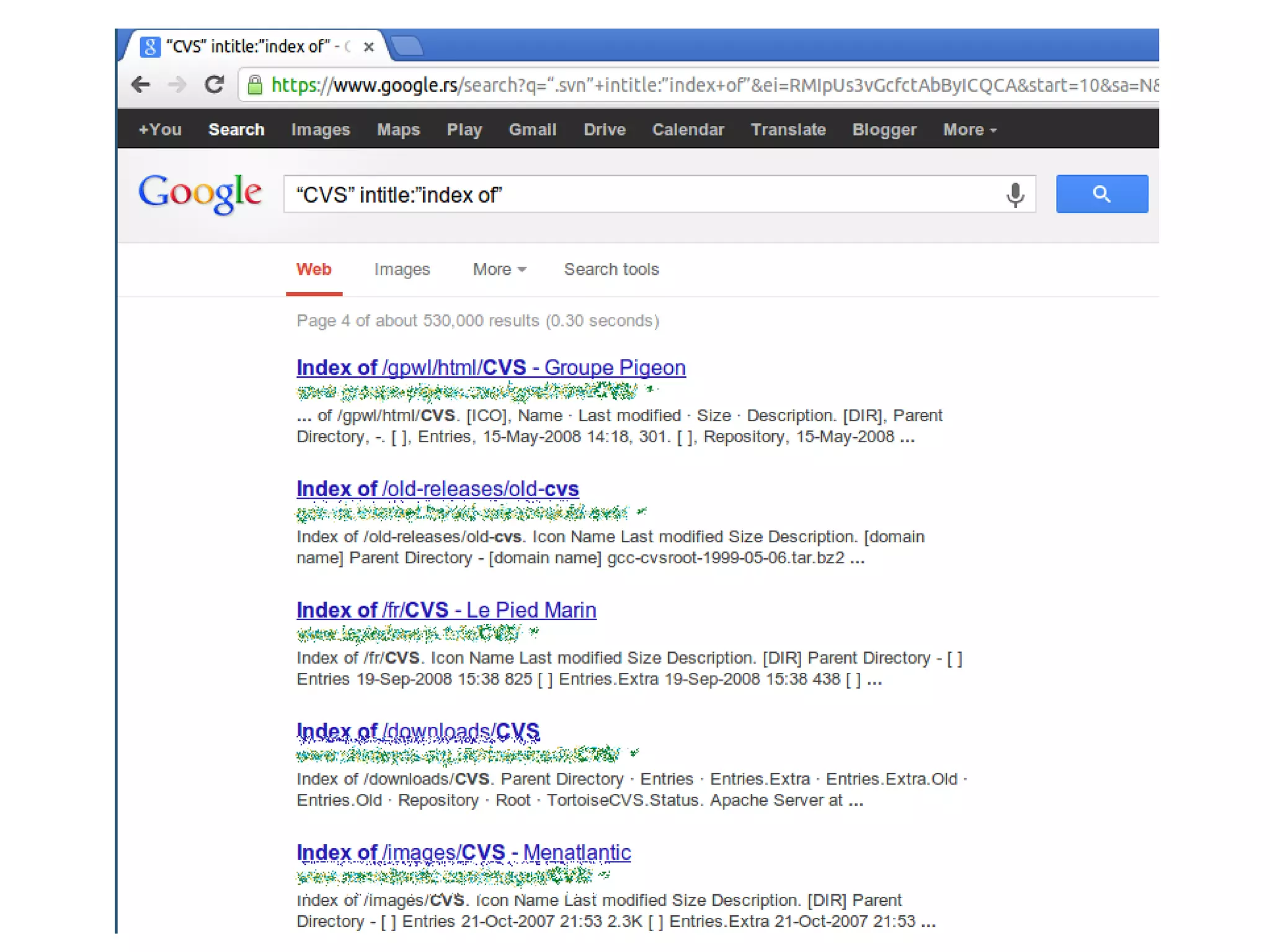
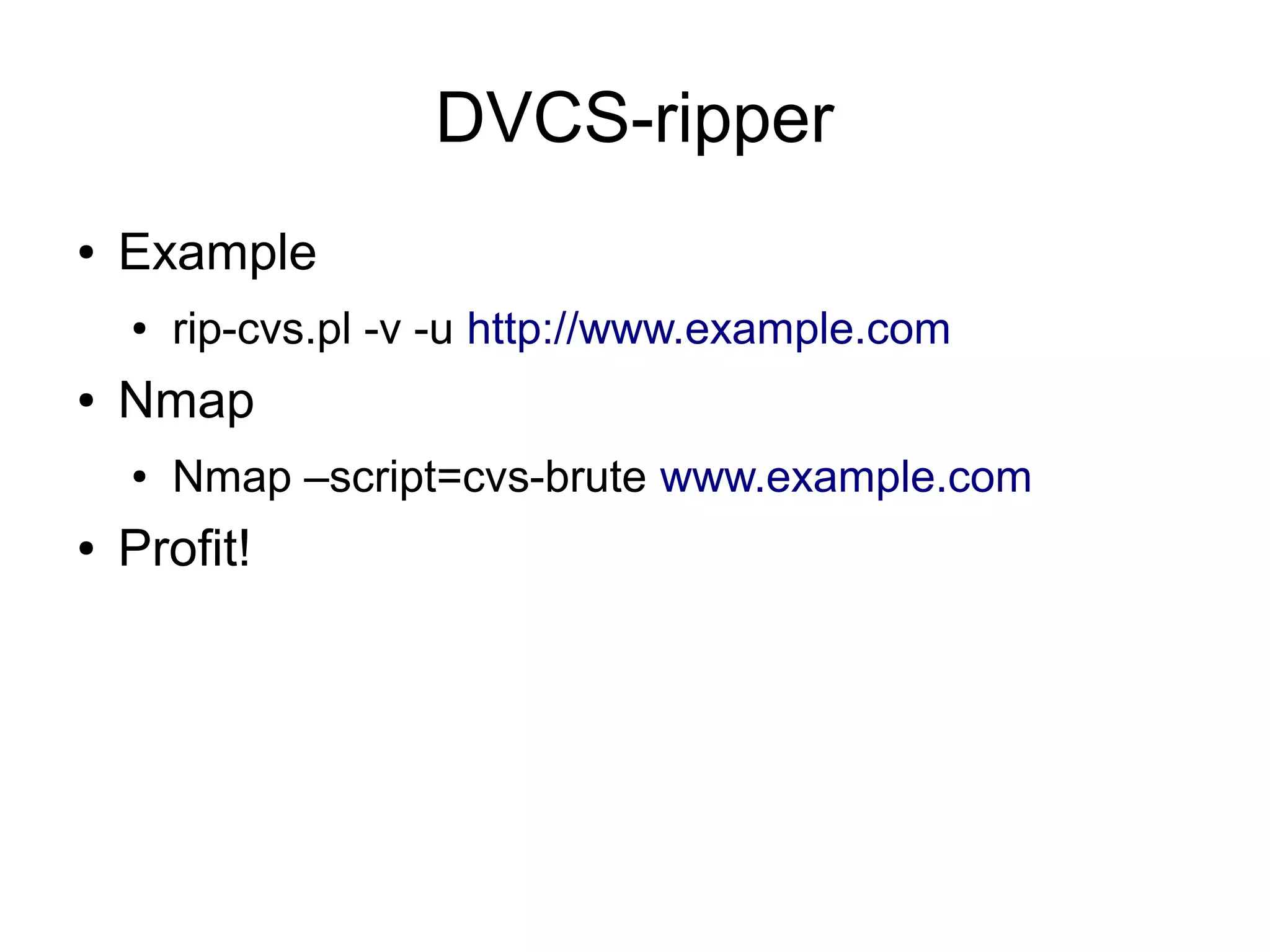
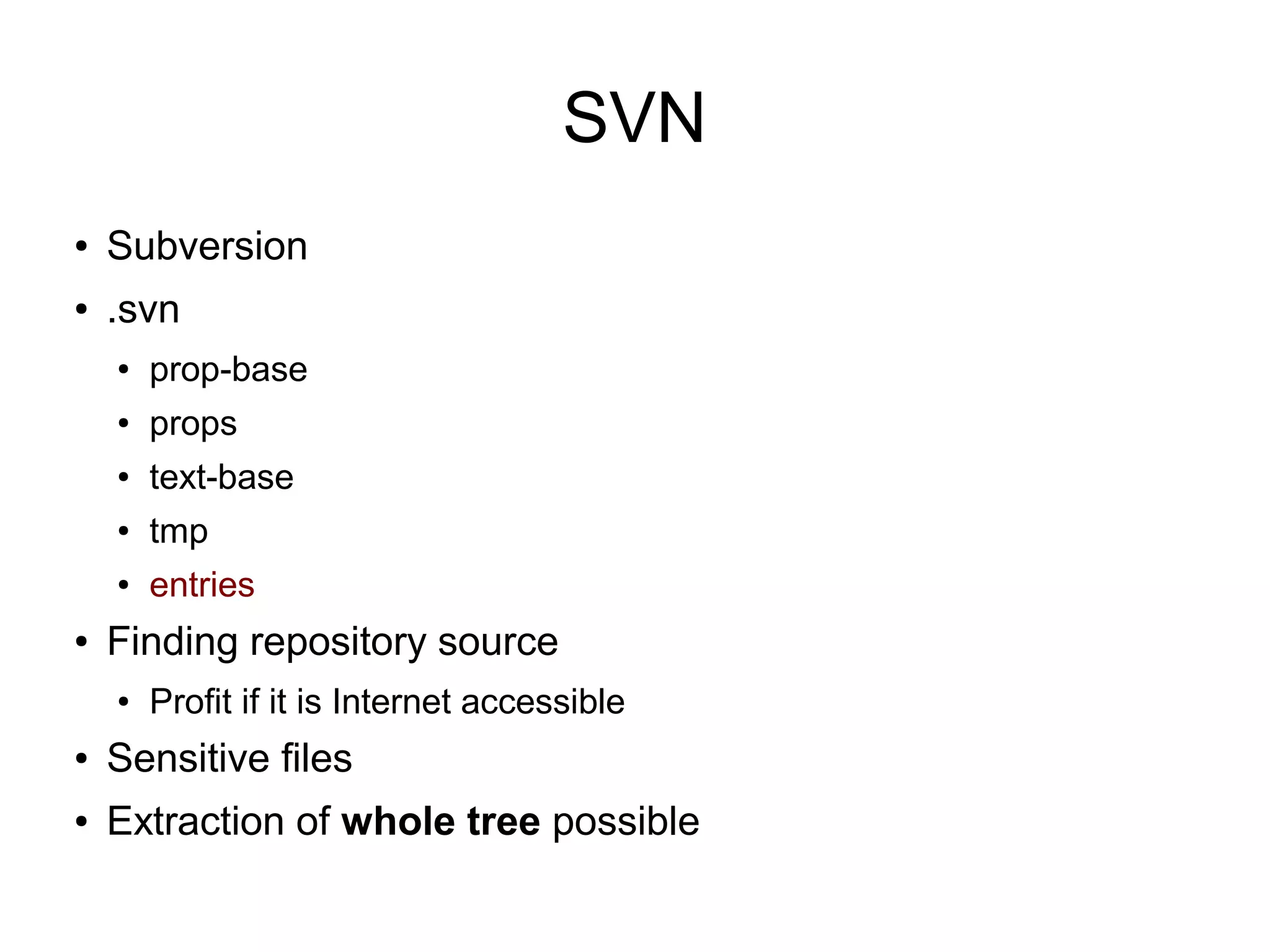
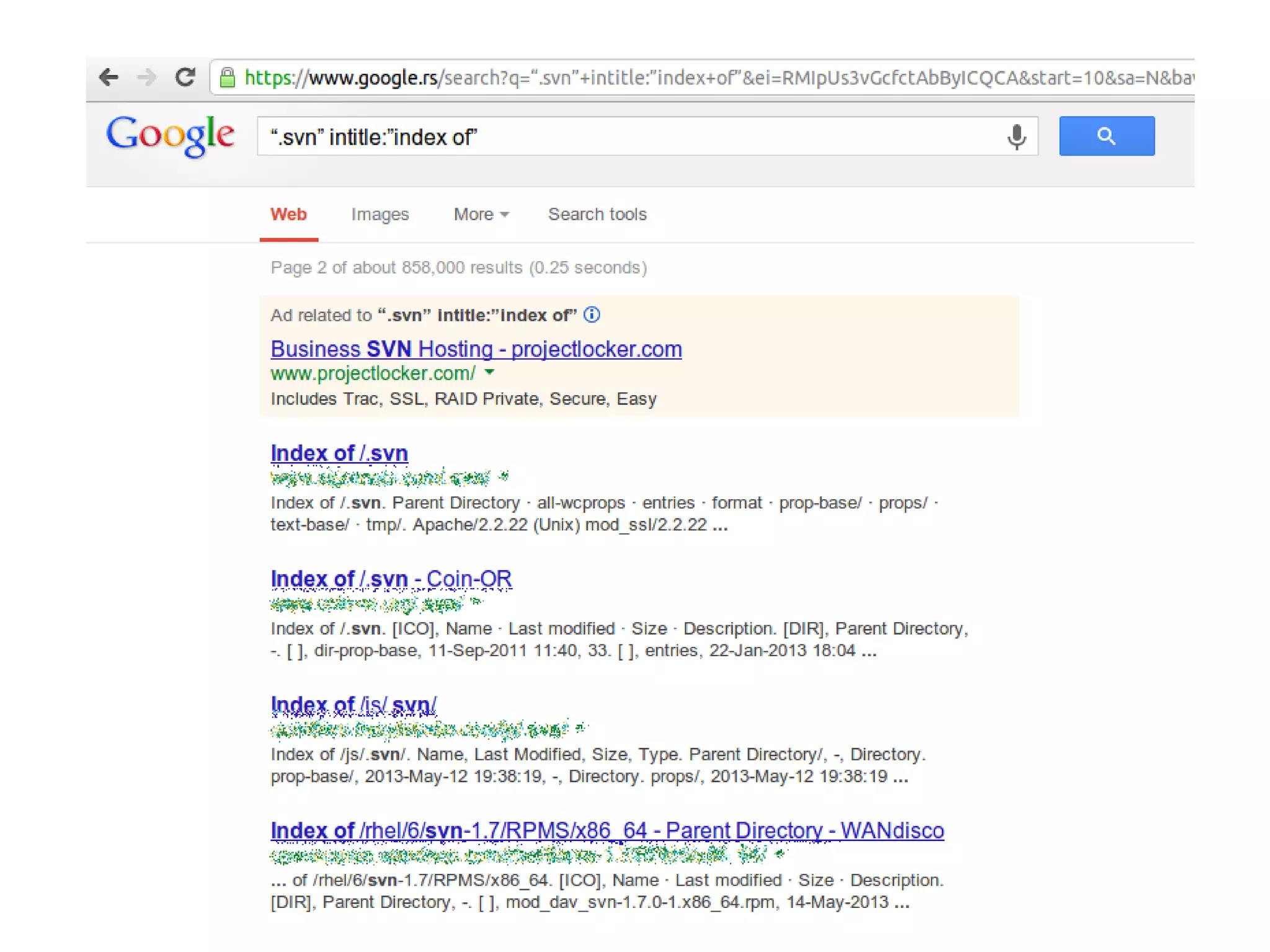
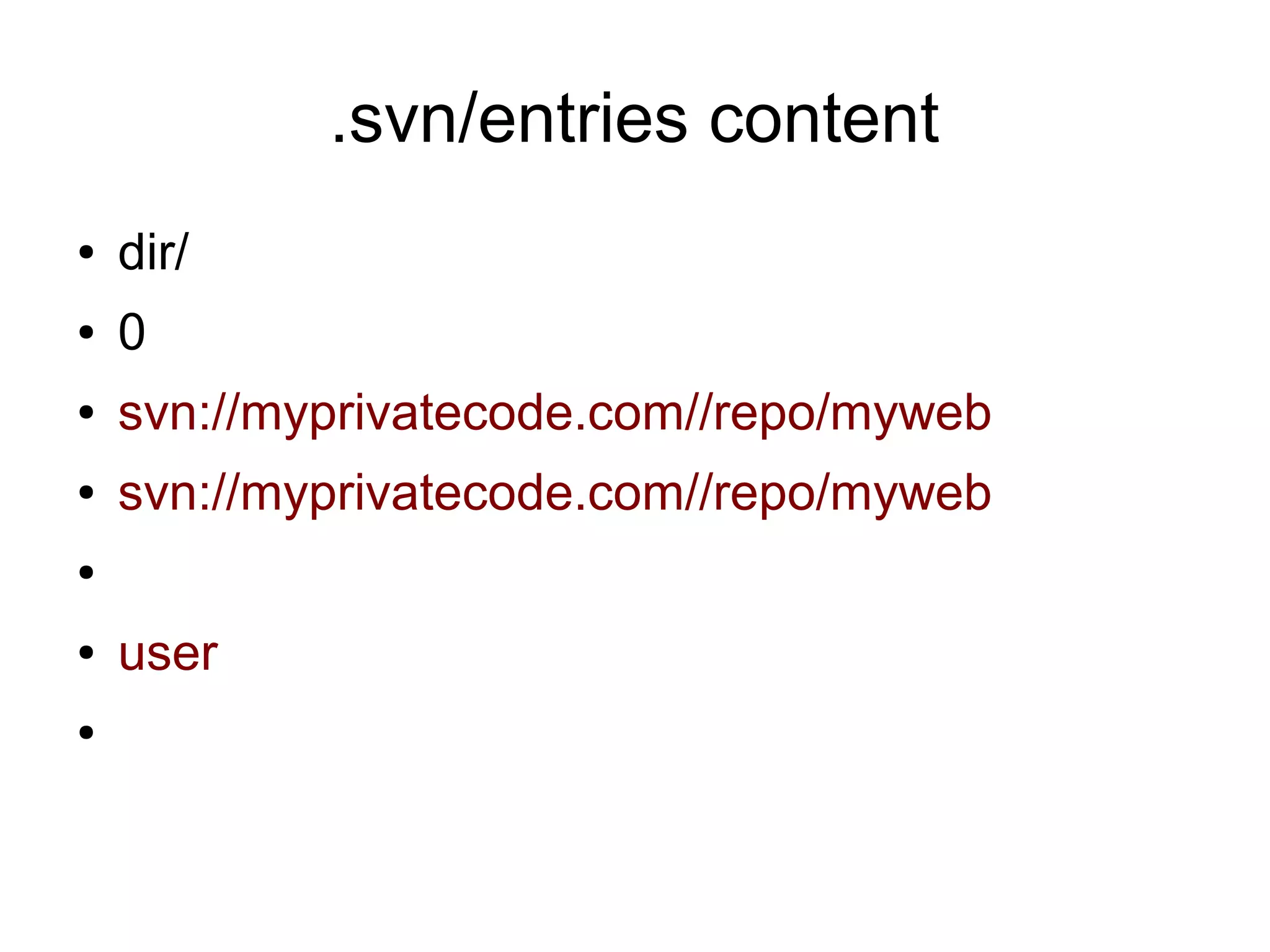
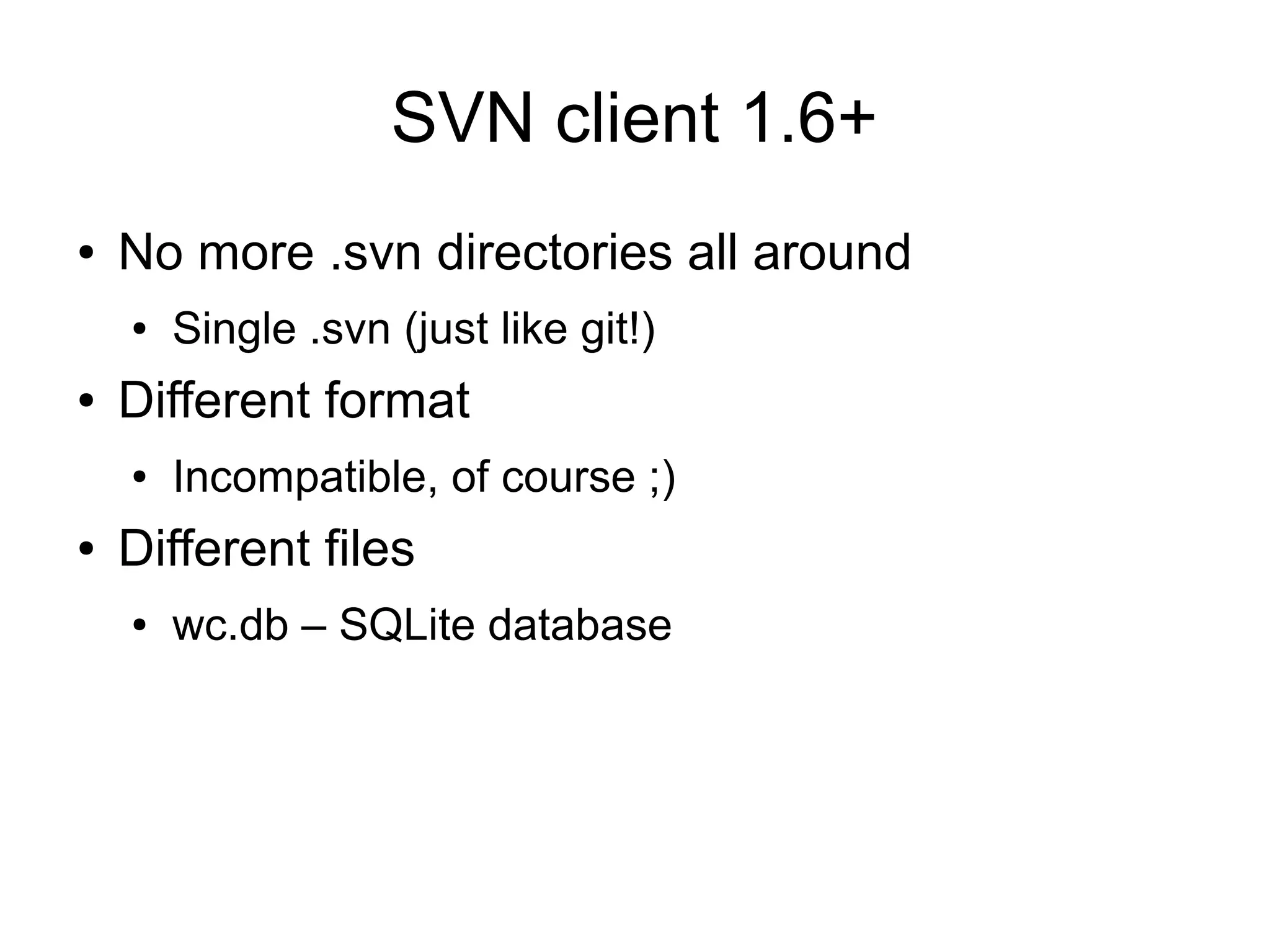
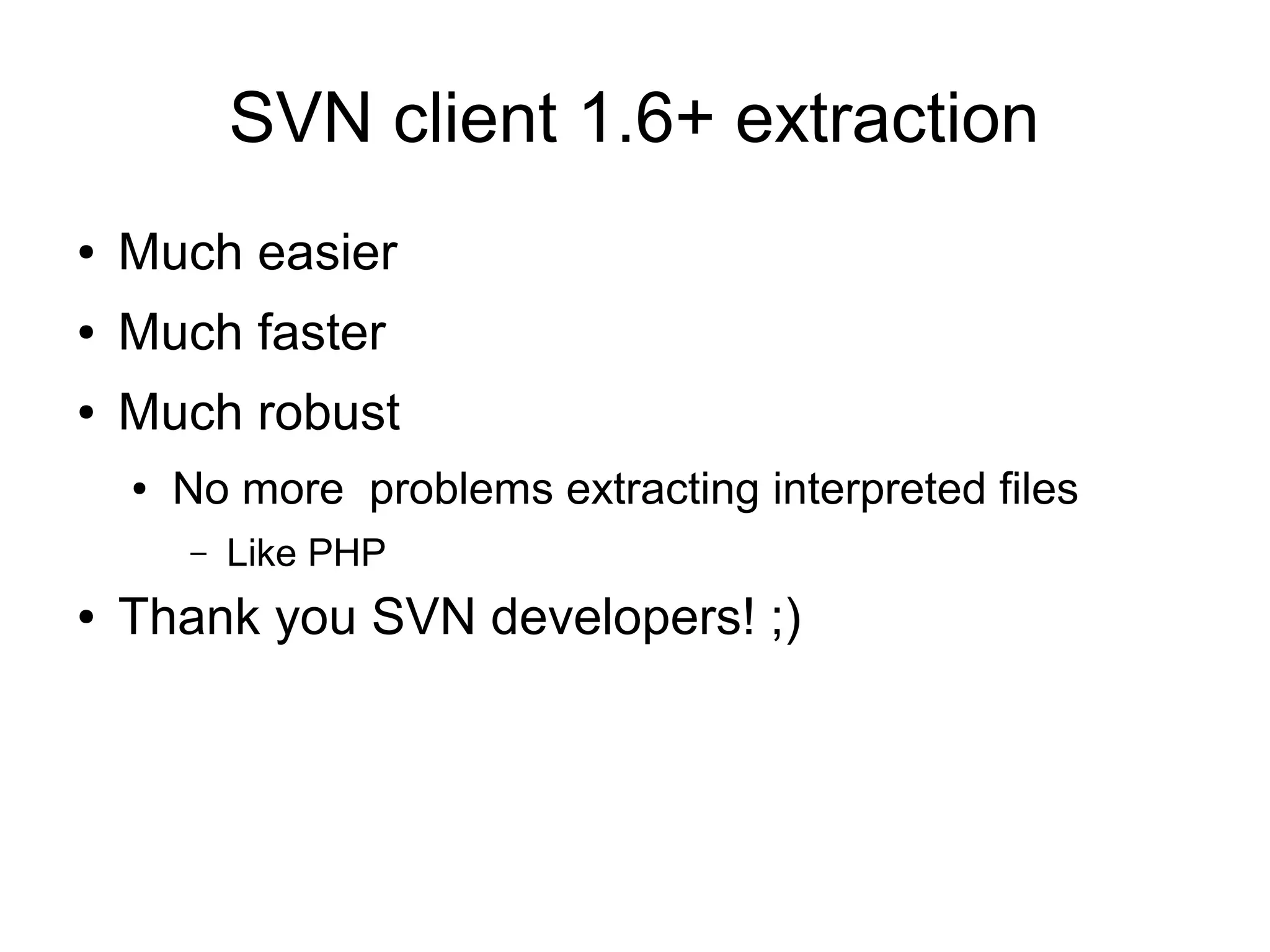
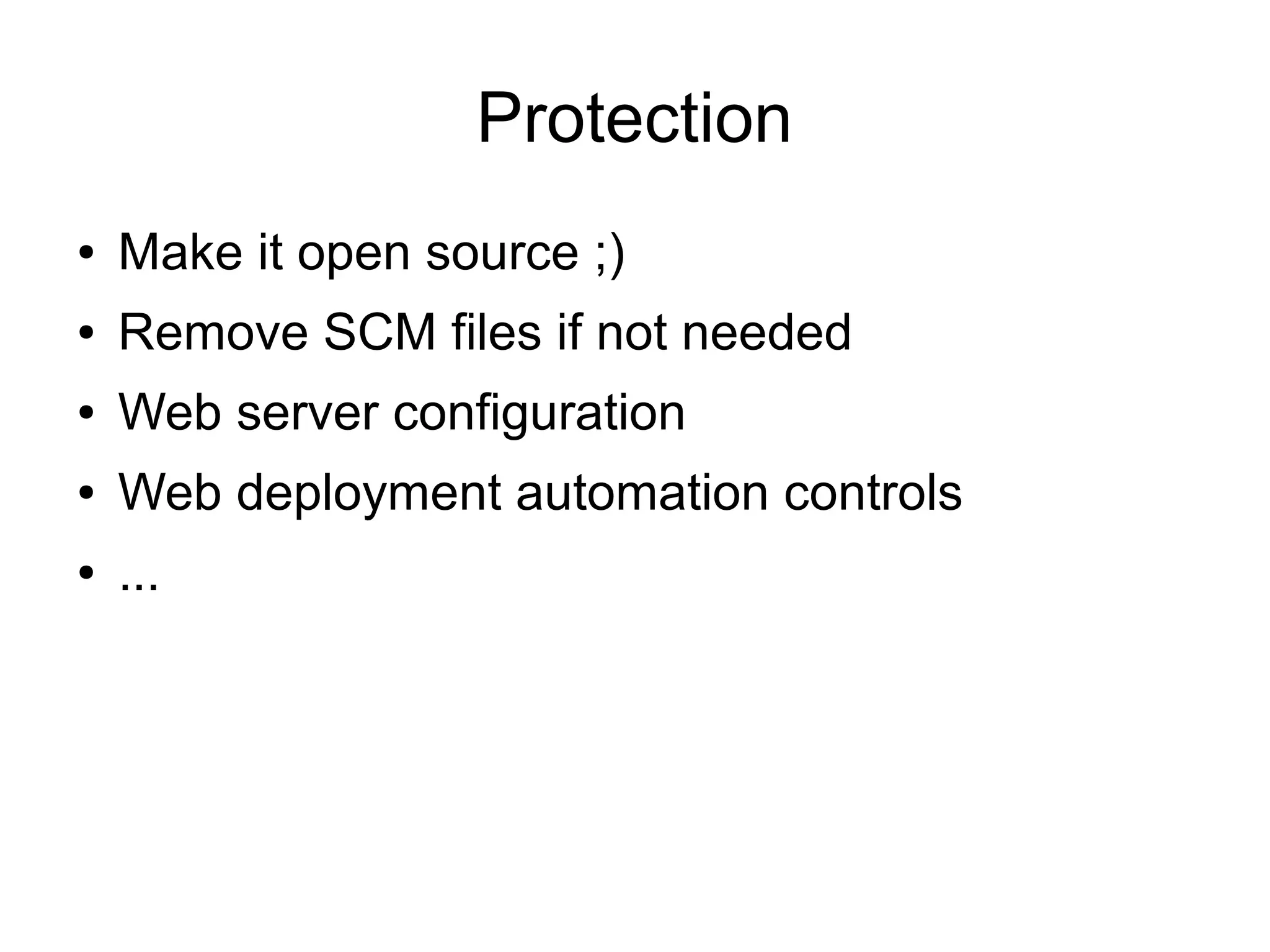
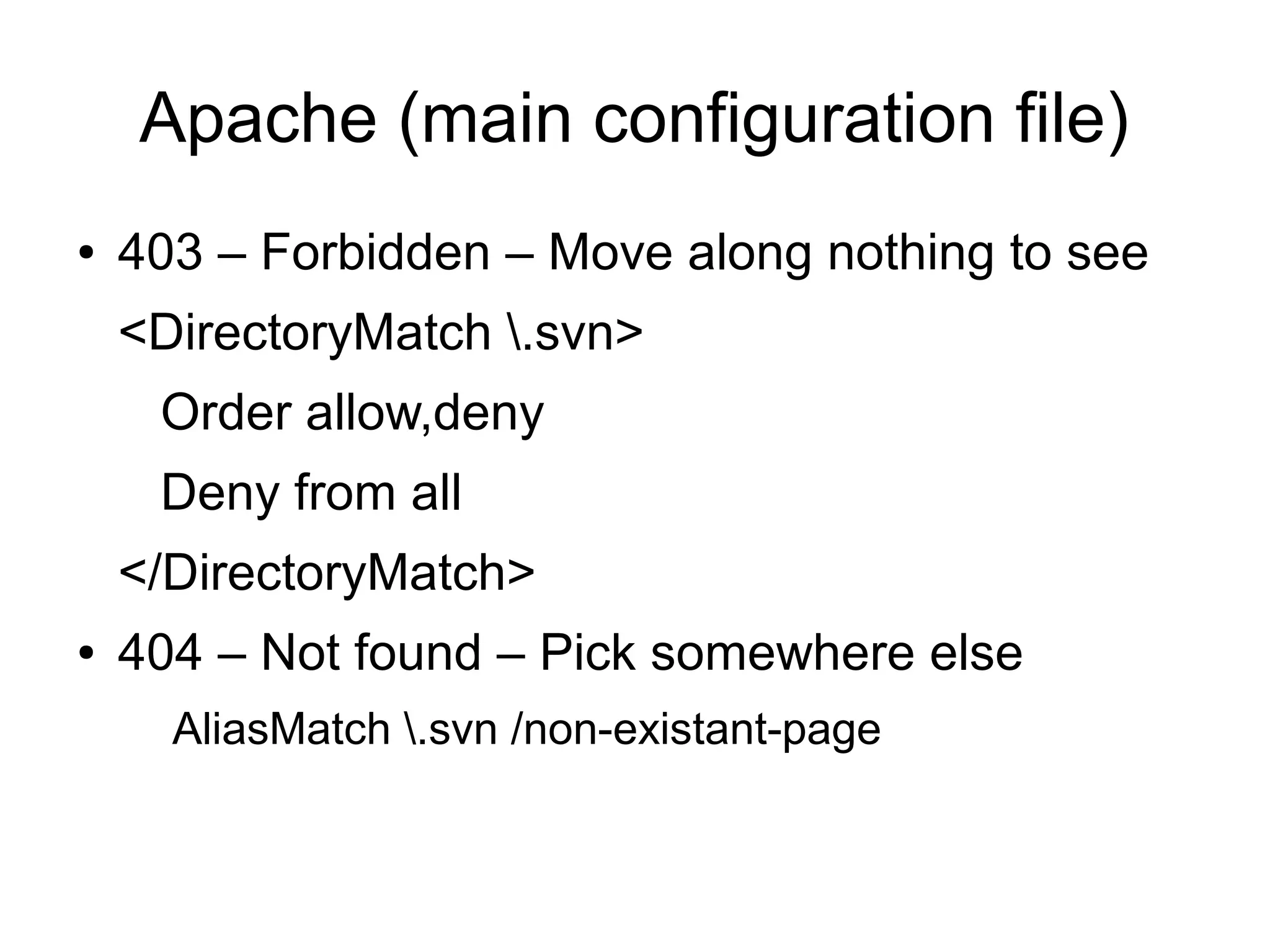
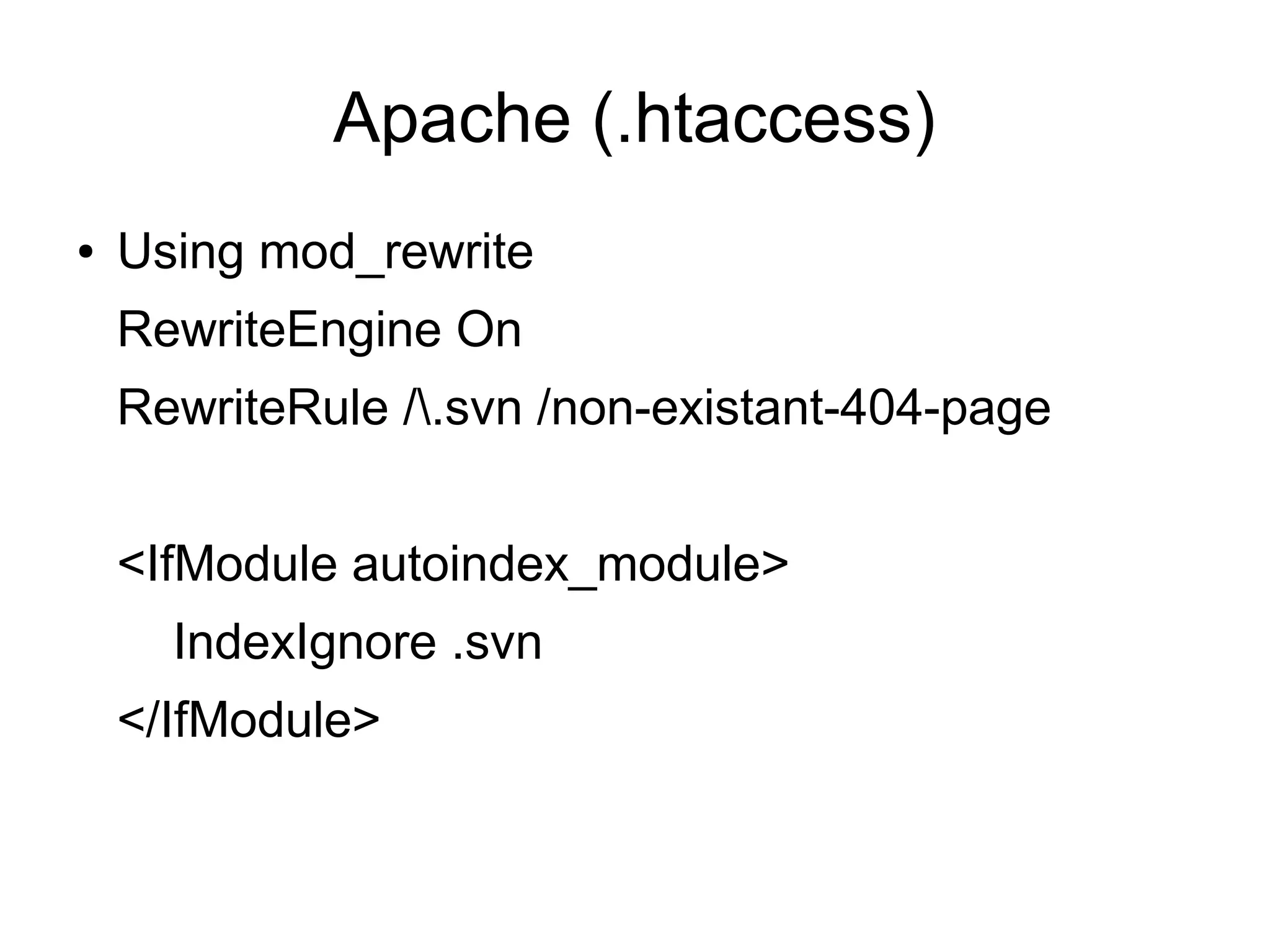
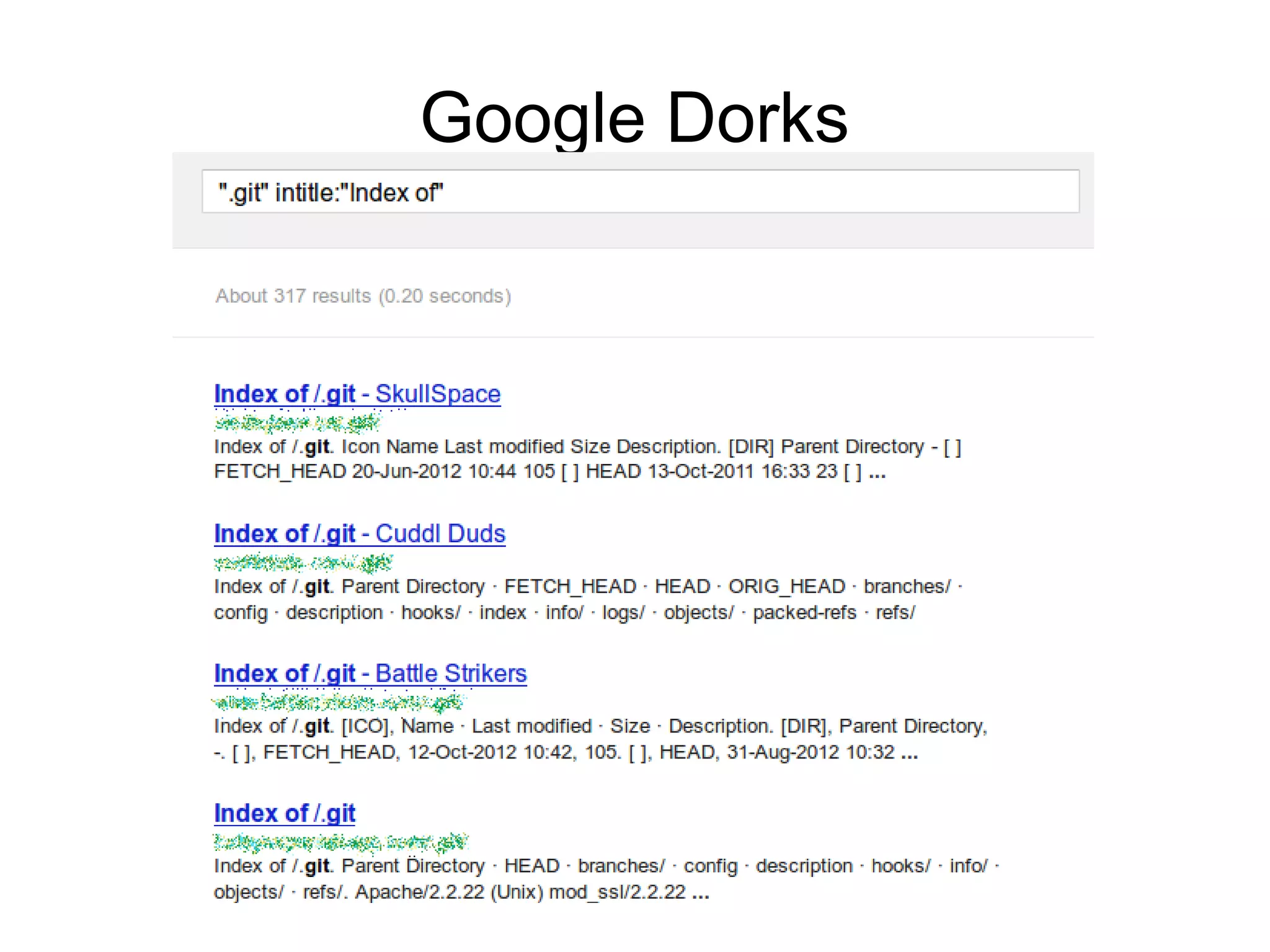
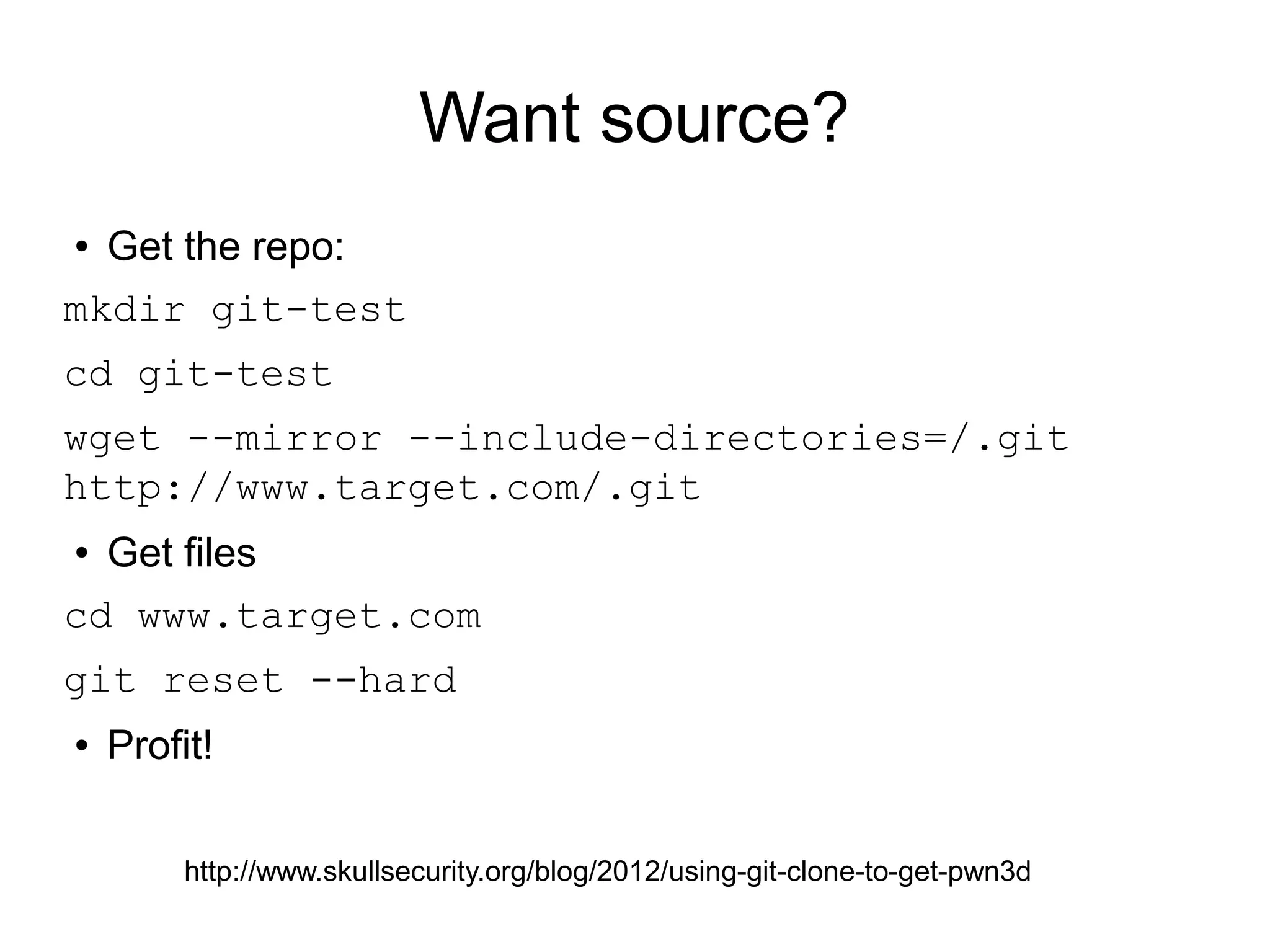
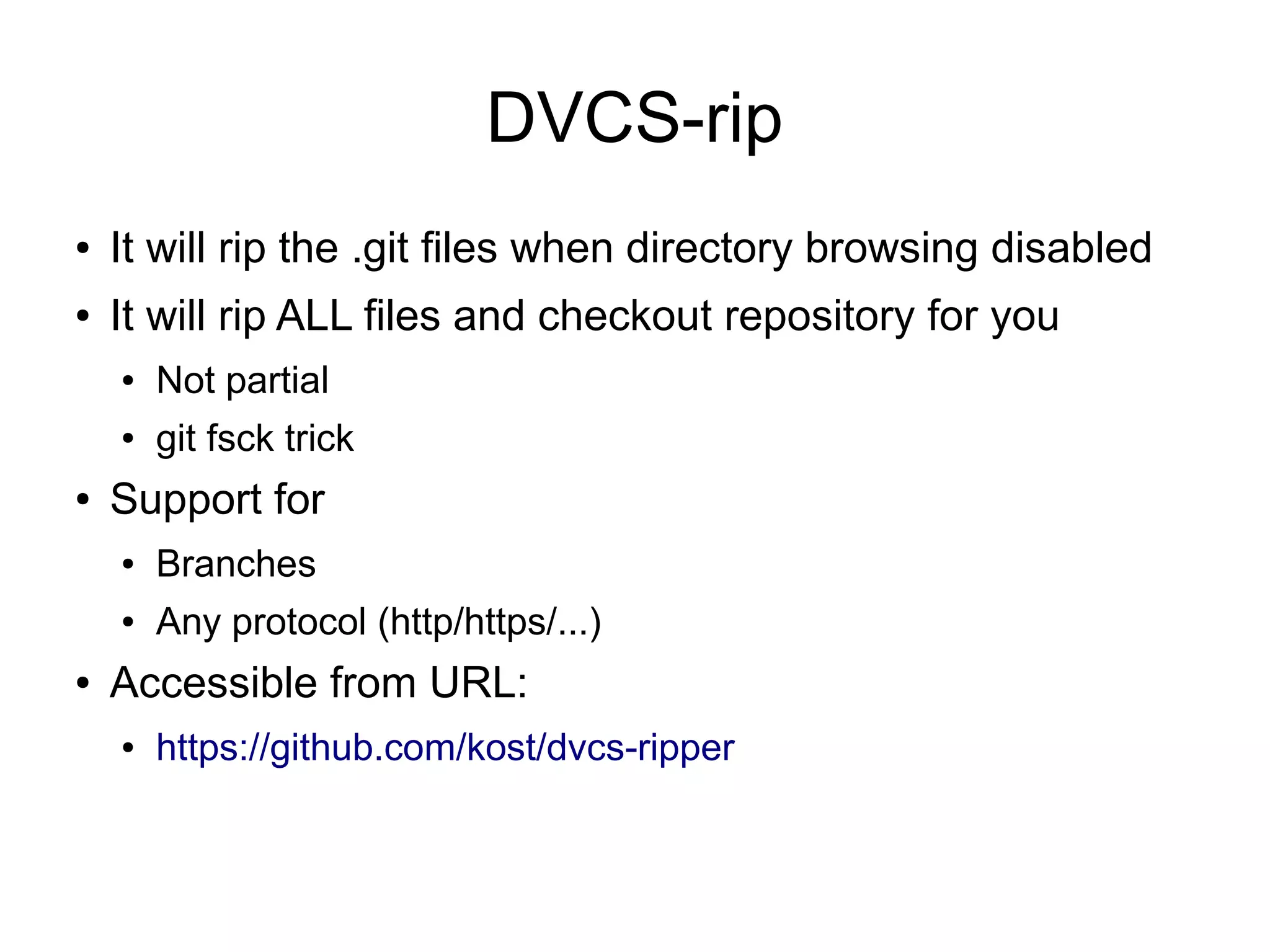
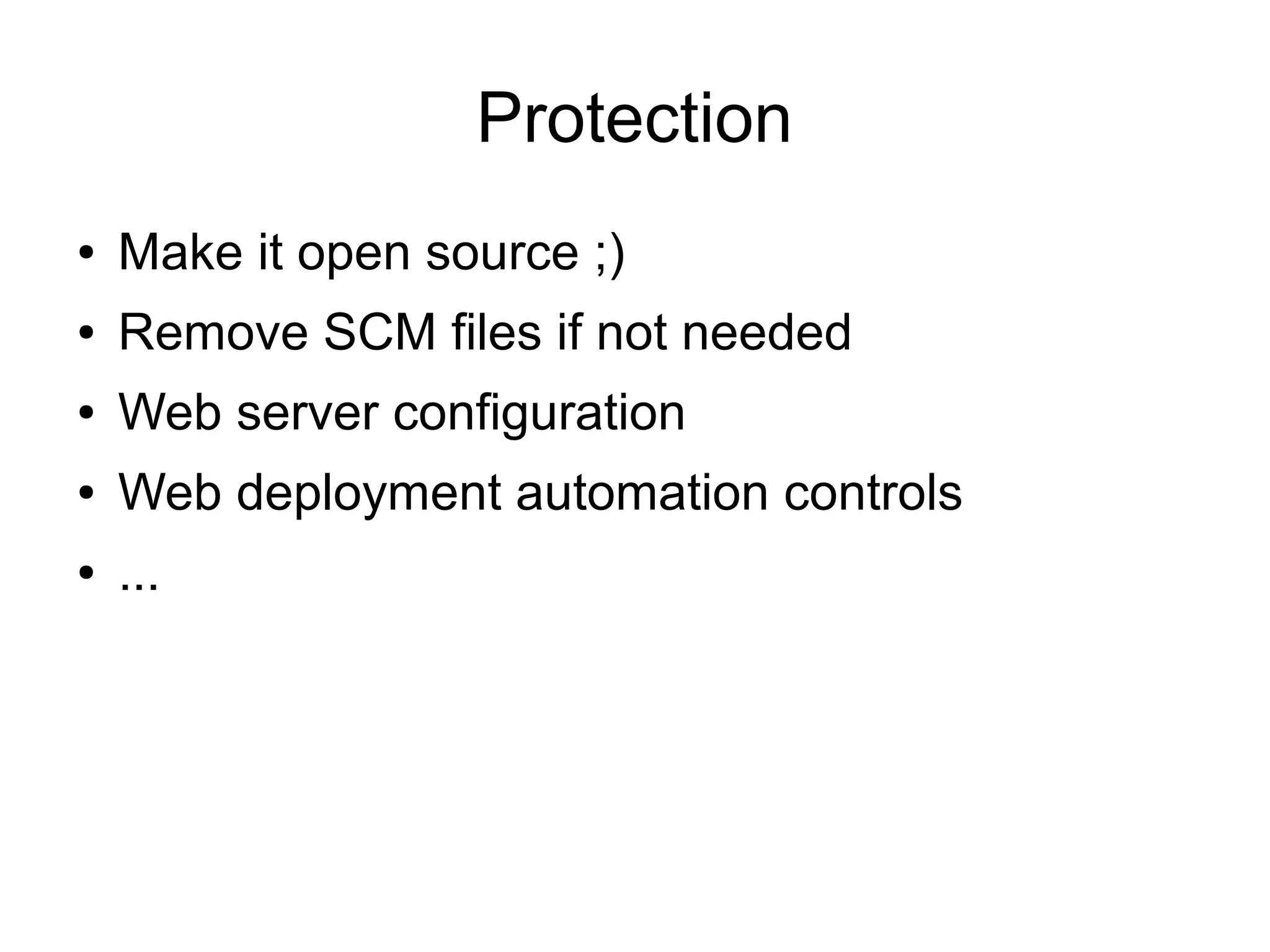
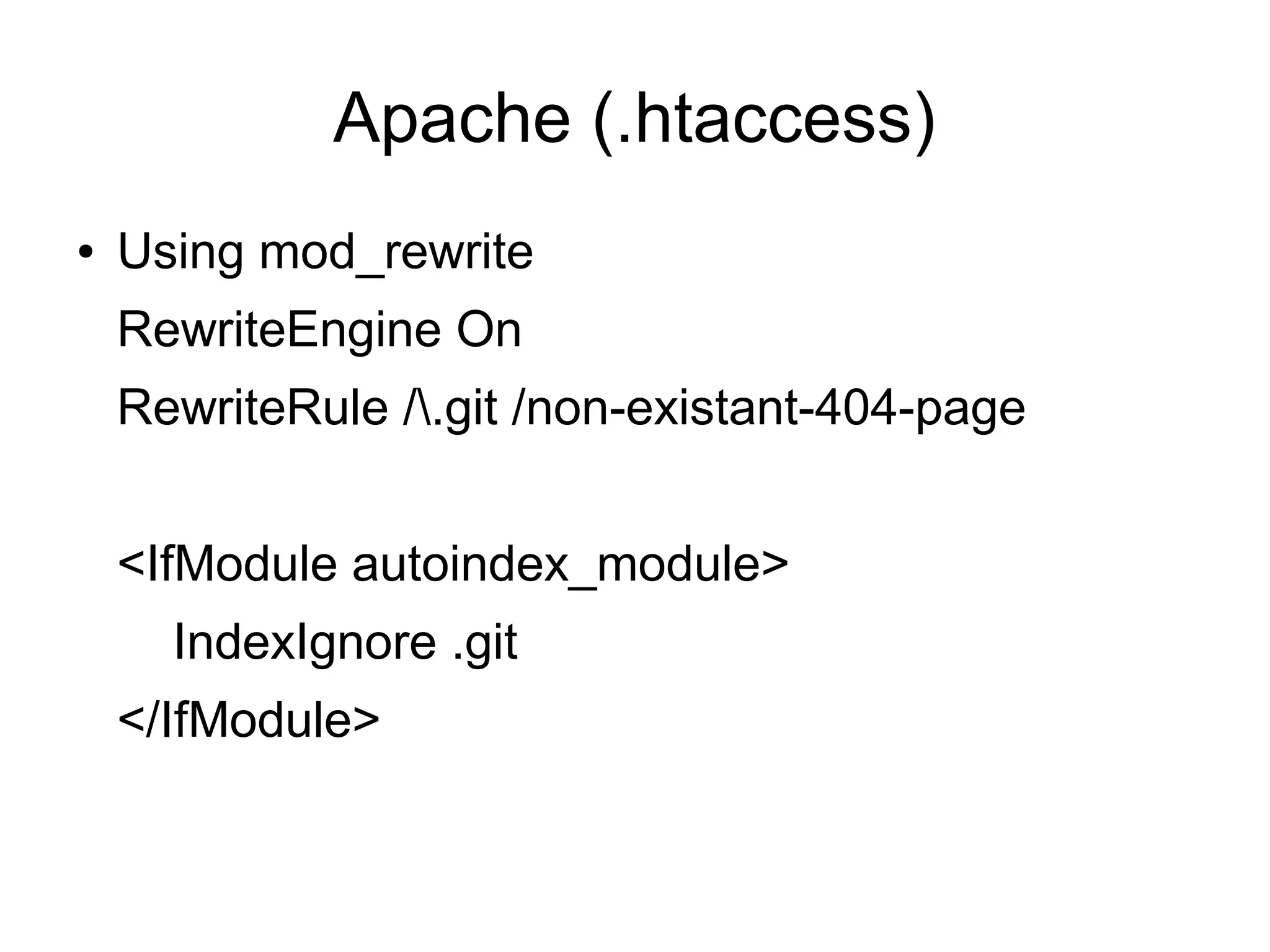
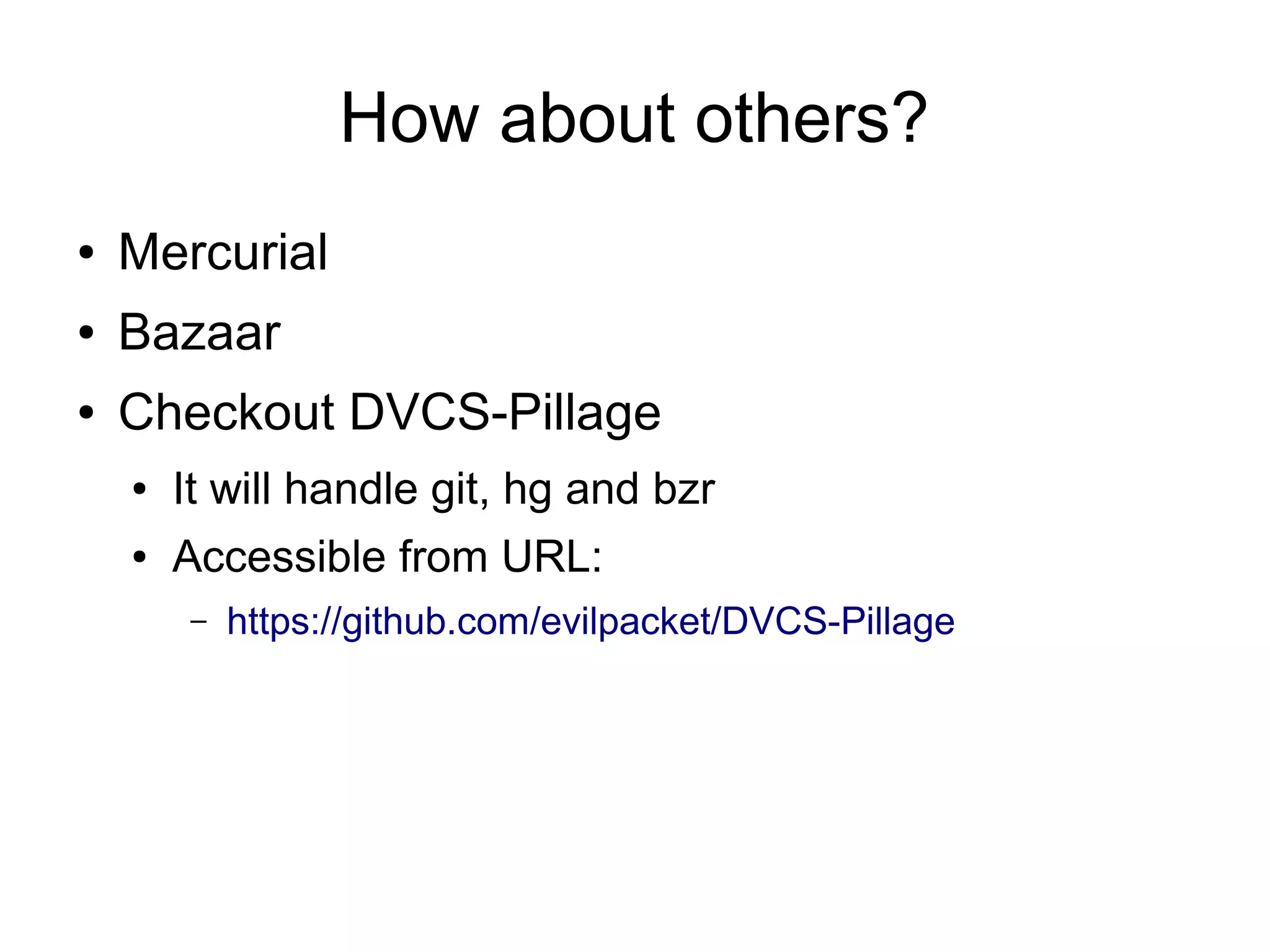
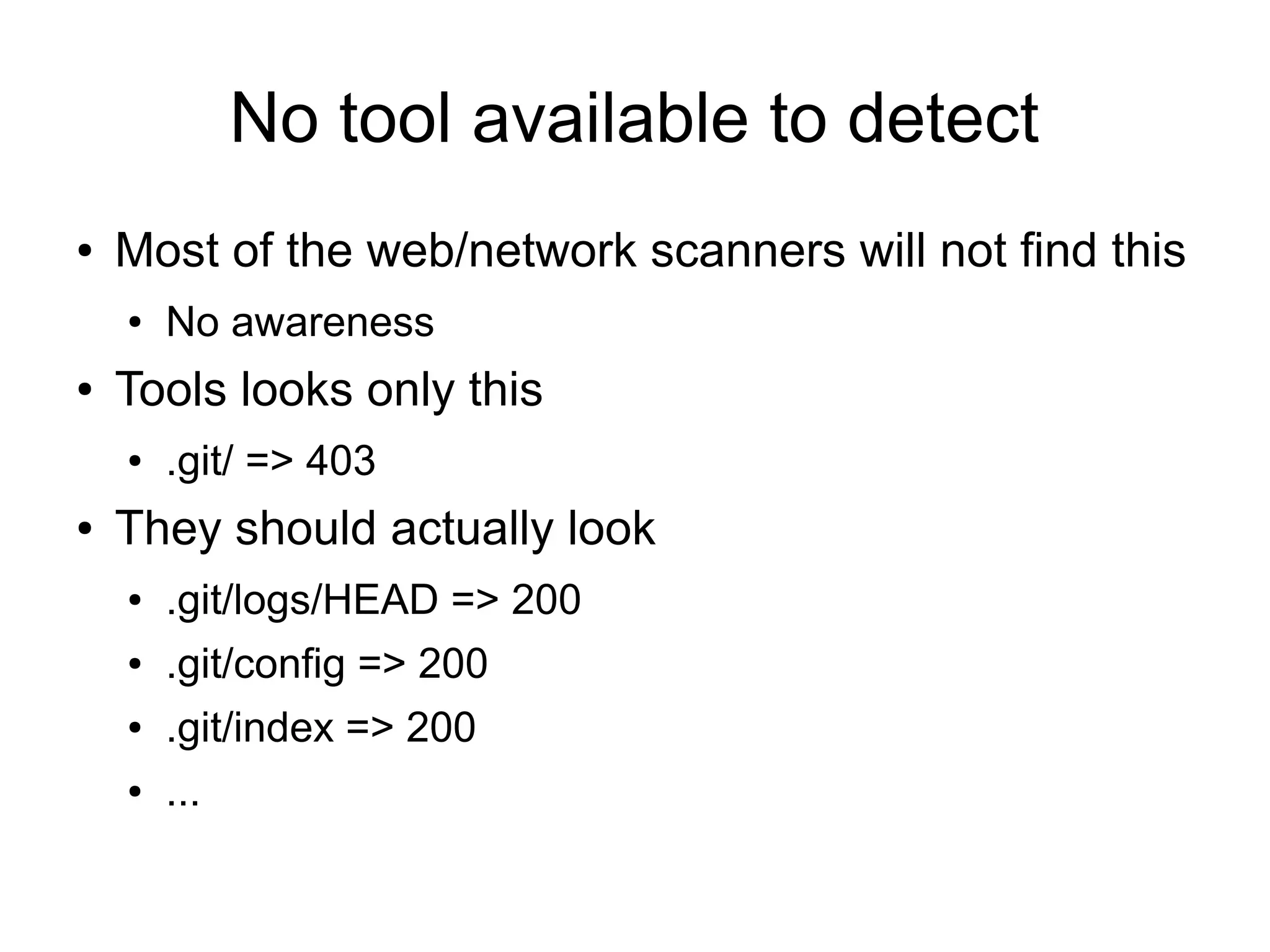
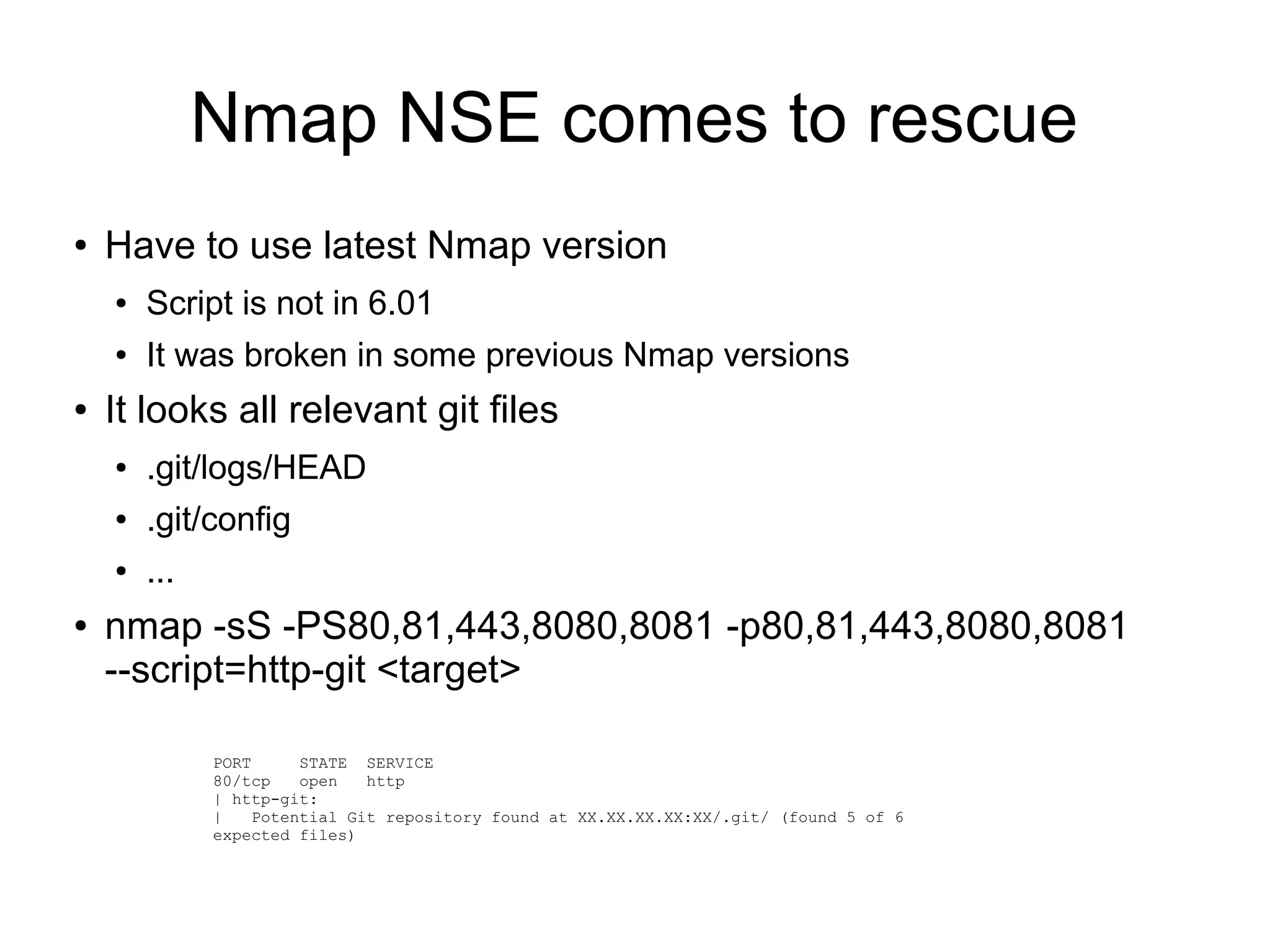
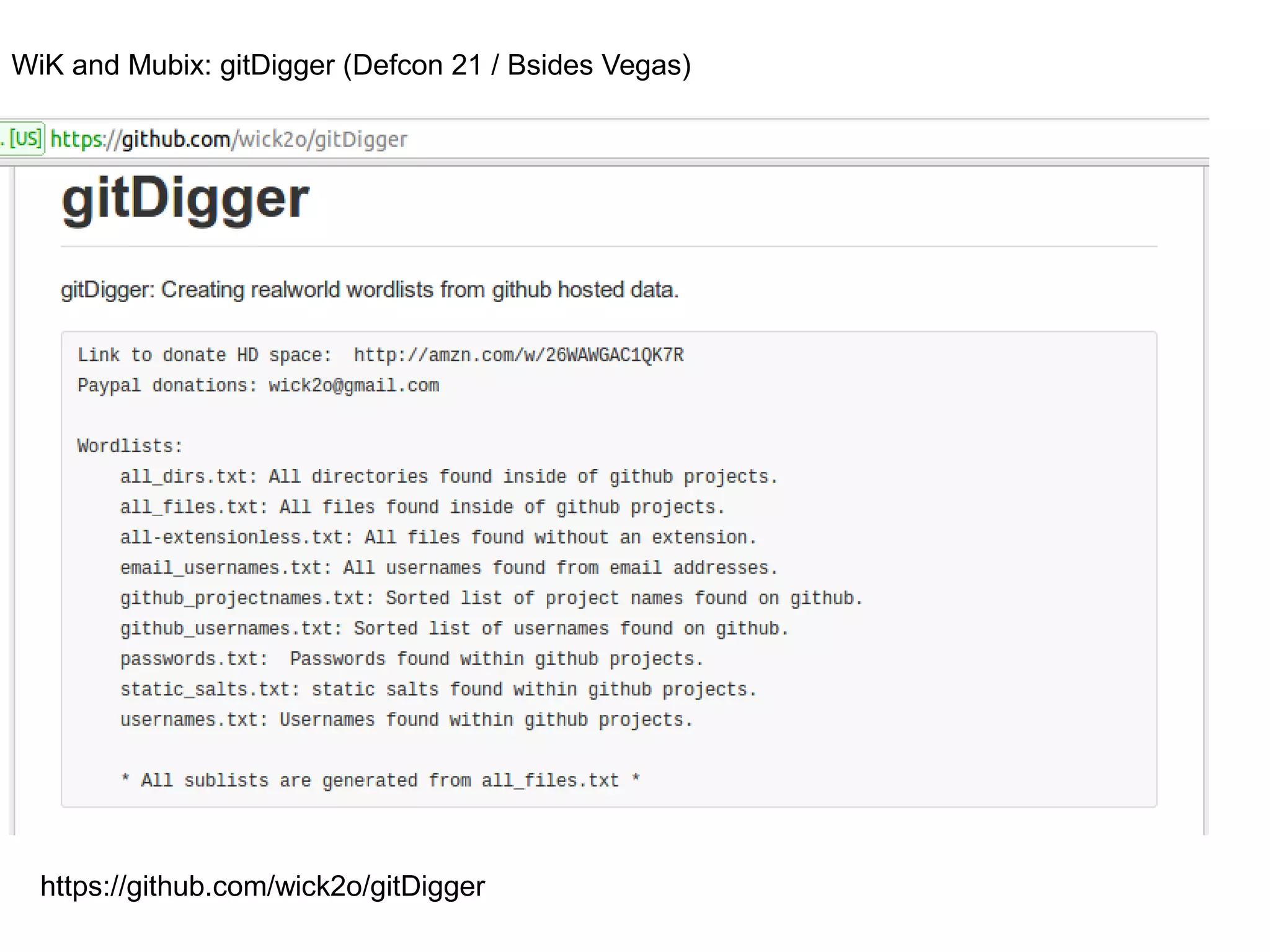
The document discusses the security implications of distributed source control management (SCM) systems, including practices for extracting source code from closed source applications. It highlights the risks of exposing sensitive information online and provides recommendations for developers, system administrators, and management to protect source code and sensitive data. Additionally, it mentions various tools and techniques for identifying and preventing unauthorized access to SCM files.