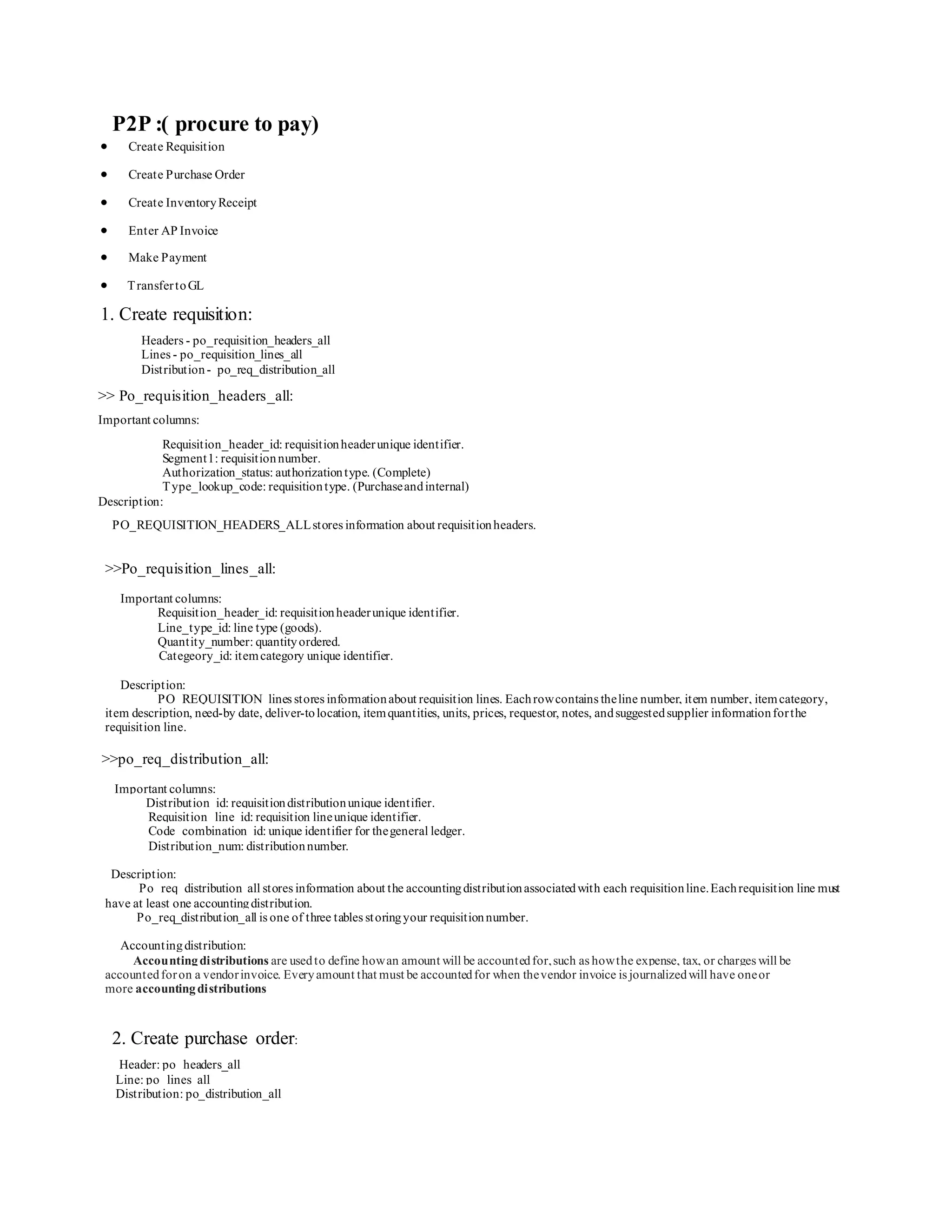
This document summarizes the key tables and steps involved in the procure-to-pay (P2P) process in Oracle Applications, including creating a requisition, purchase order, goods receipt, invoice, payment, and general ledger transfer. It provides descriptions of over 15 tables used to store header and line item information at each stage of the process, as well as important columns within each table.