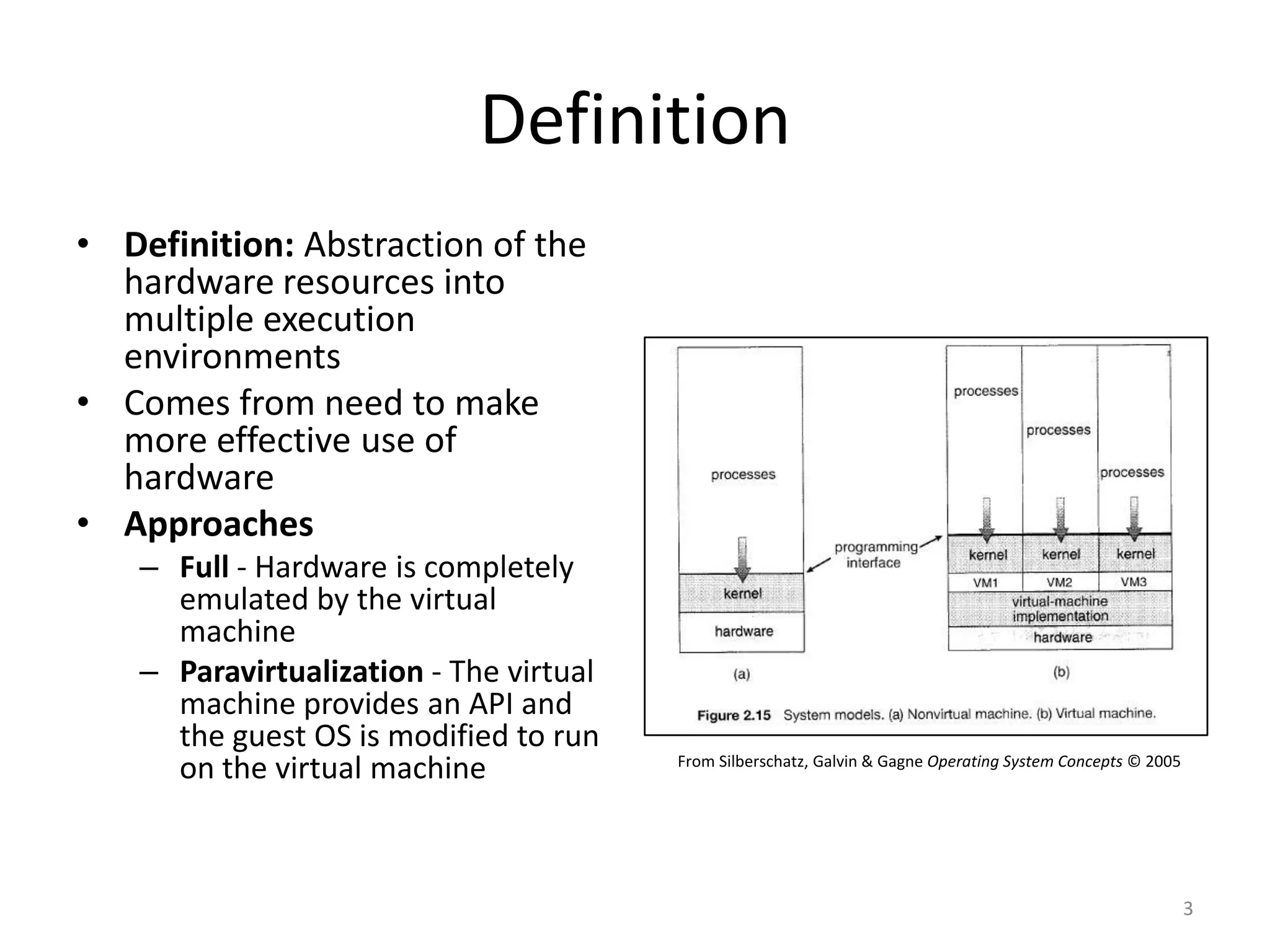
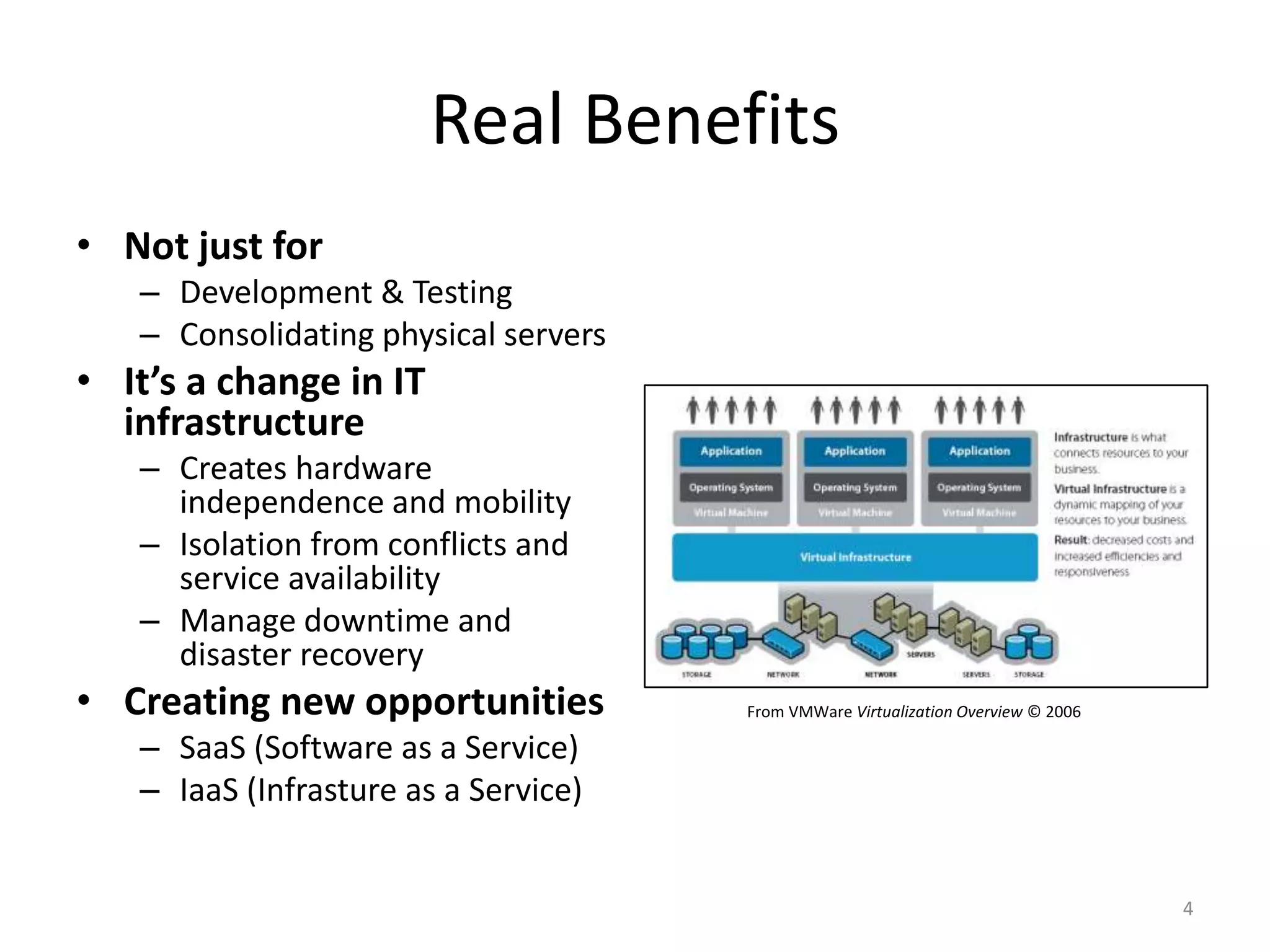
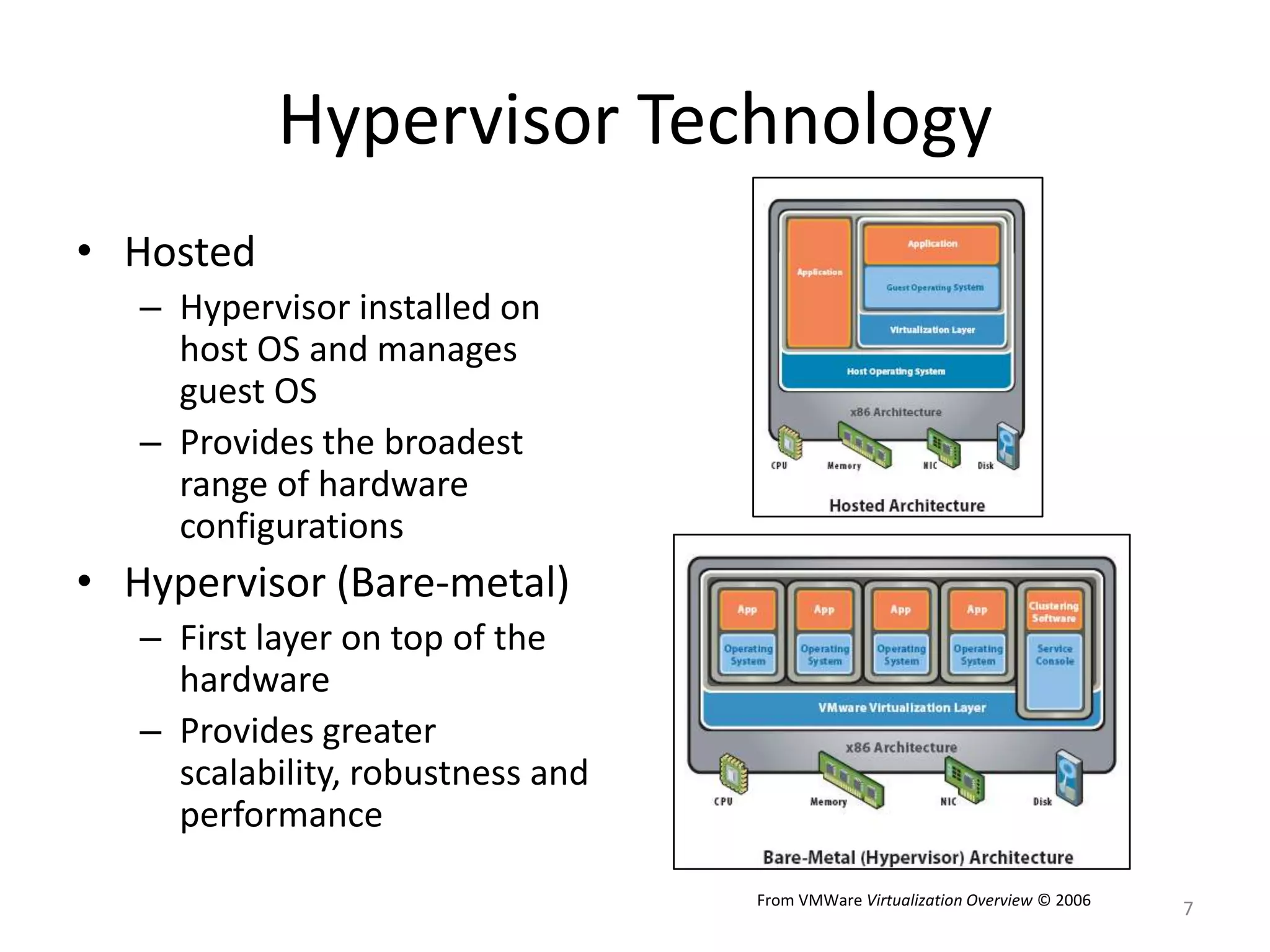
This document provides an overview of system virtualization. It defines virtualization as the abstraction of hardware resources into multiple execution environments. The benefits of virtualization include hardware independence, isolation, manageability and new opportunities like software as a service. The history of virtualization is discussed, along with hypervisor architecture and how hardware assists with virtualization. Considerations for virtualization like management complexity, pitfalls and skills requirements are also covered.