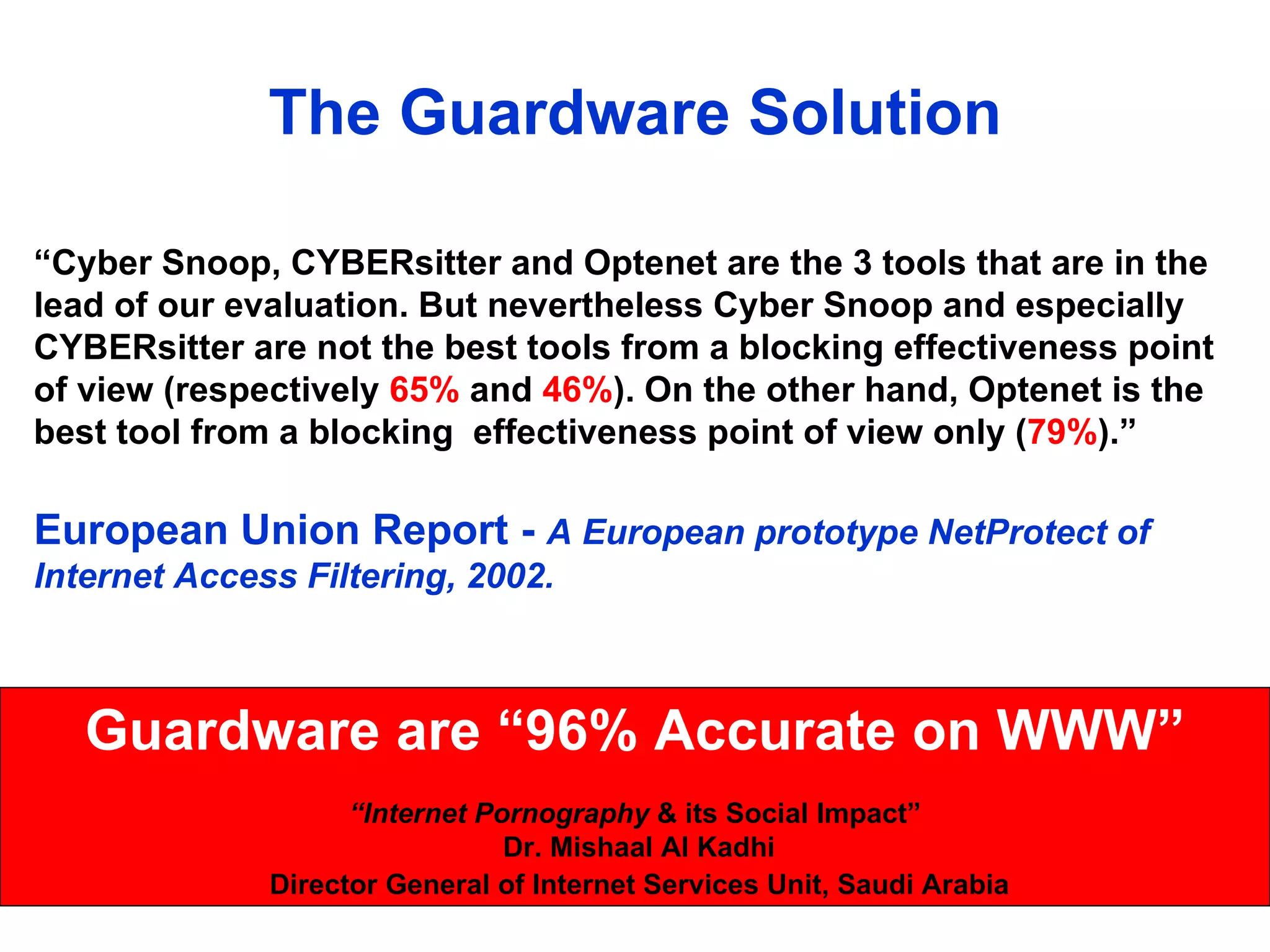
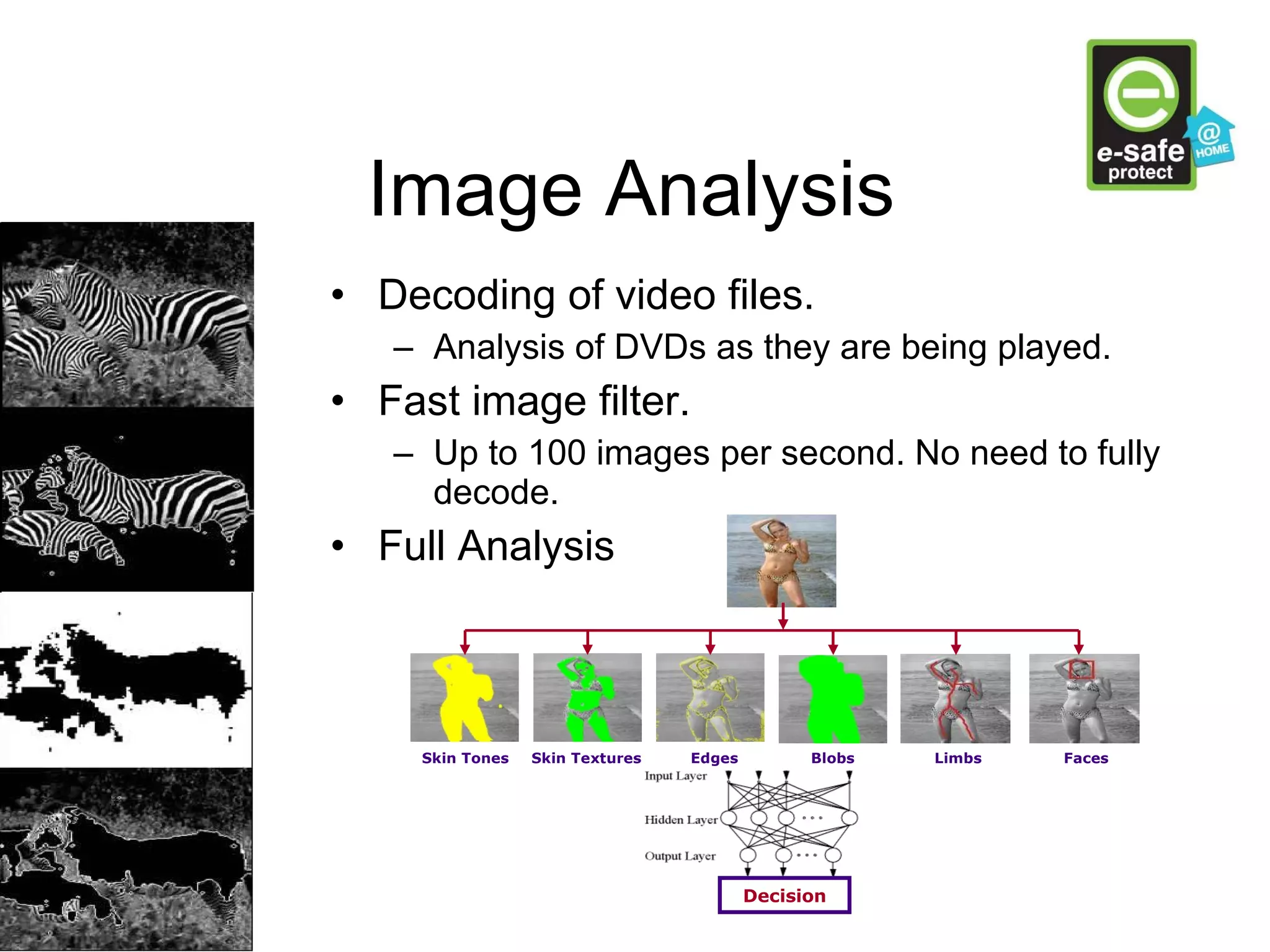
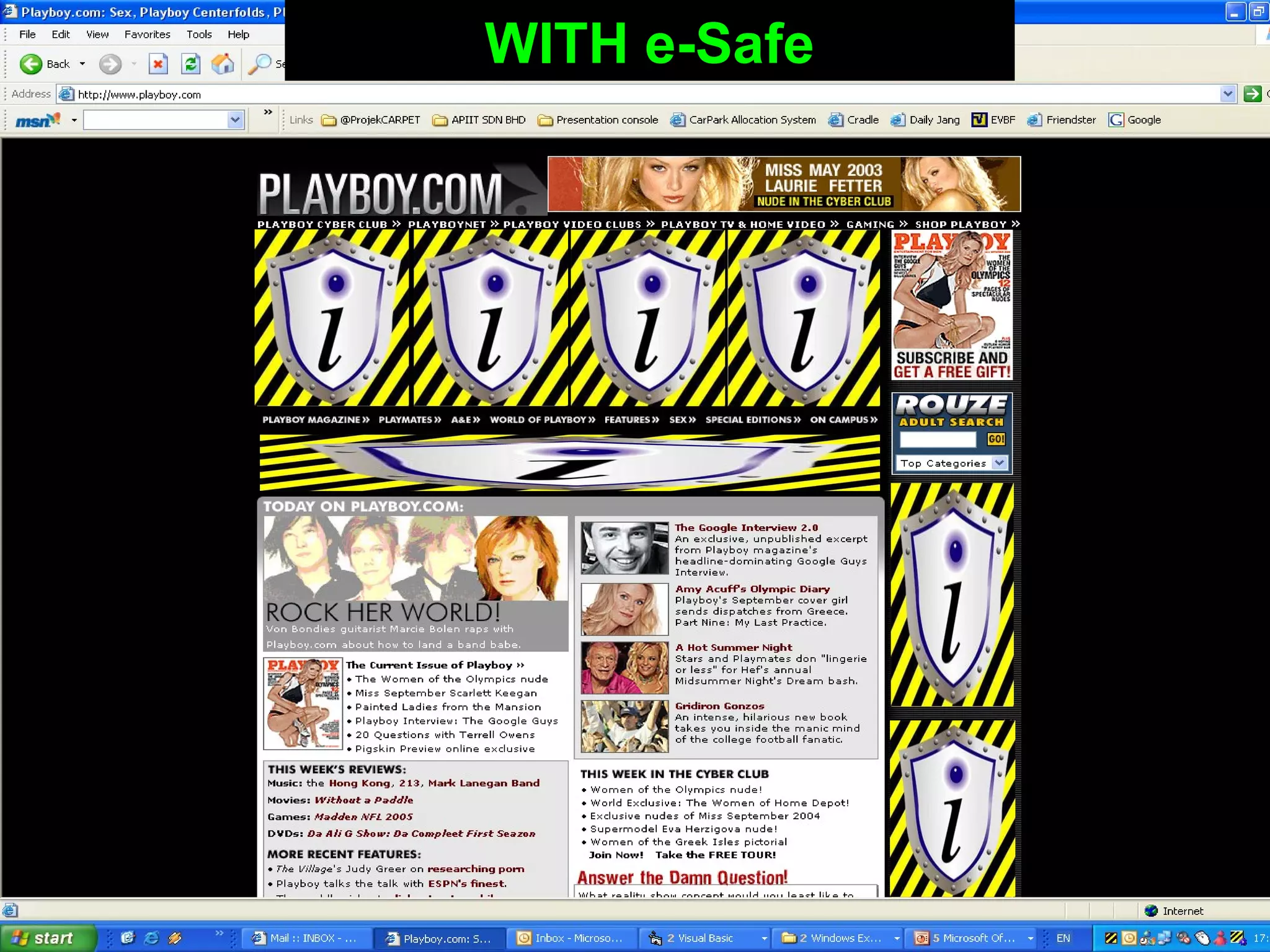
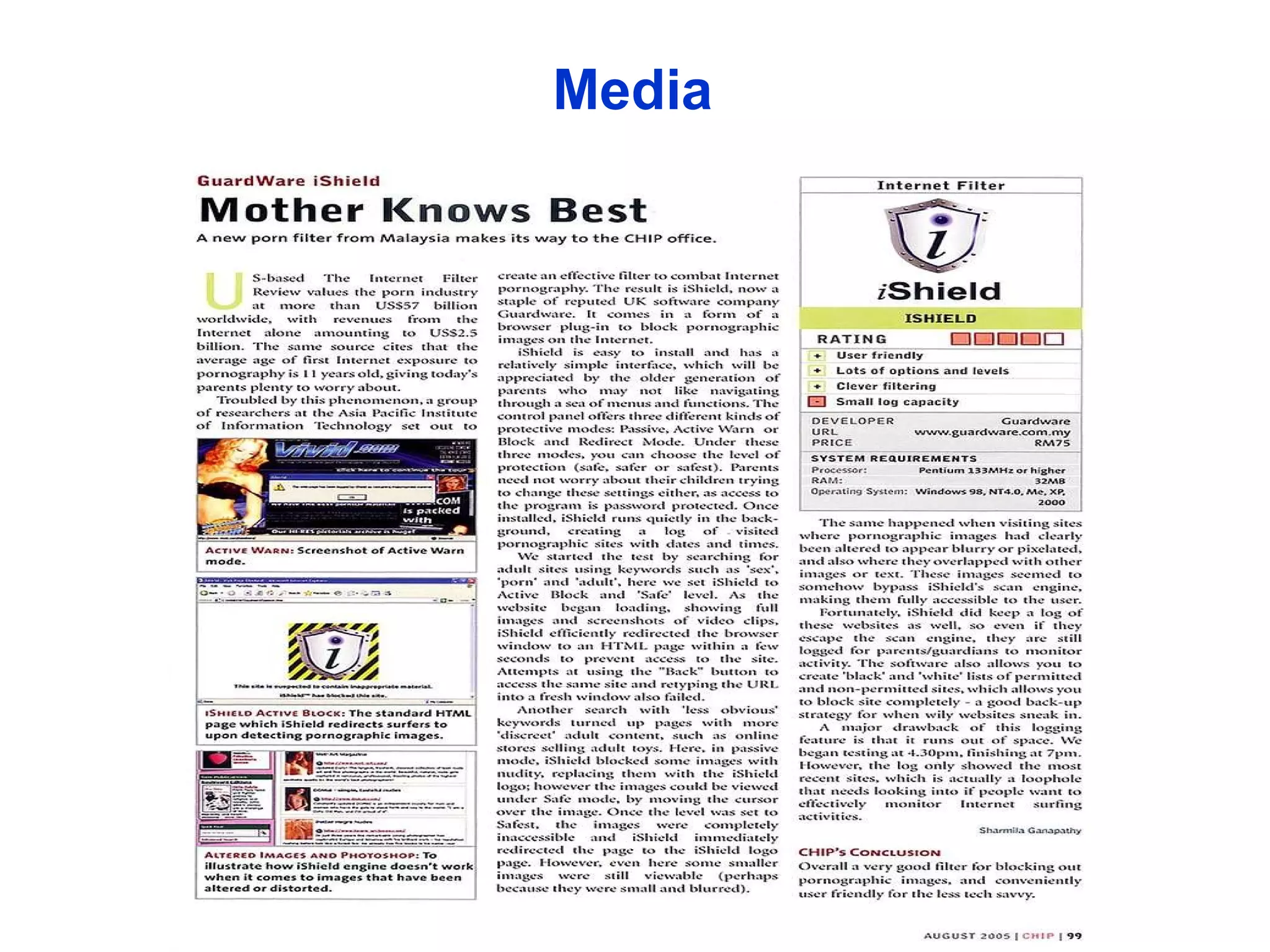
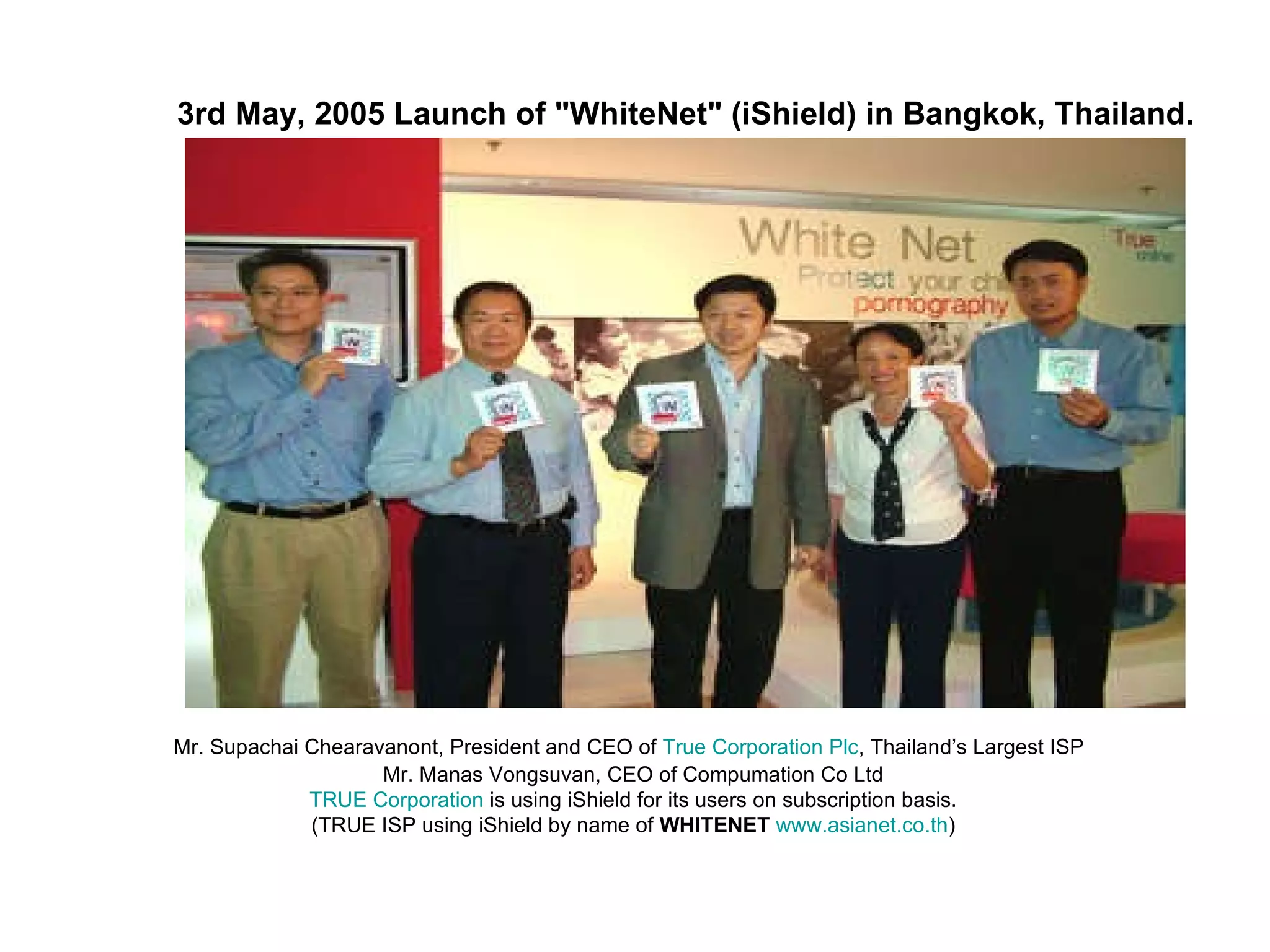
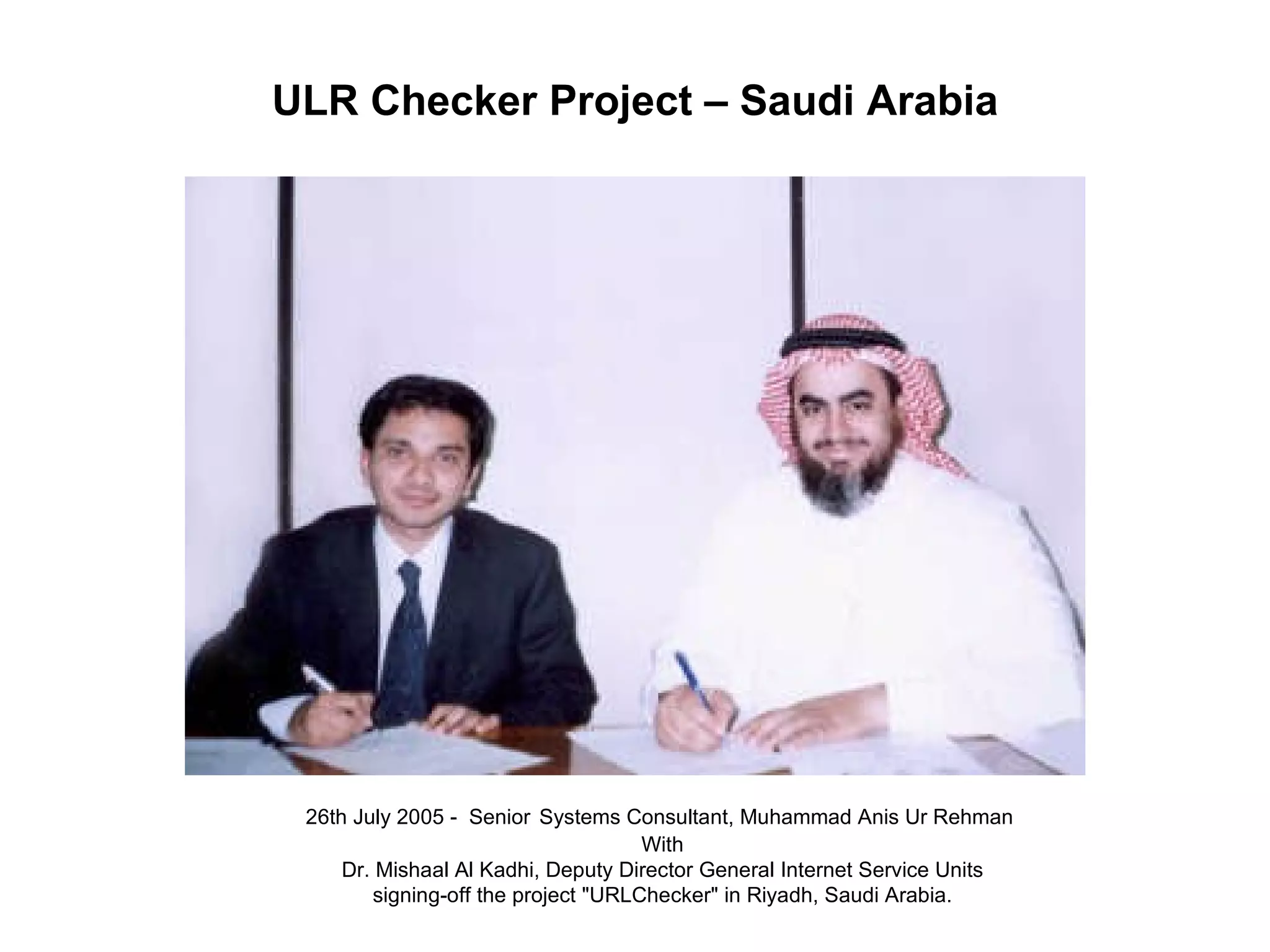
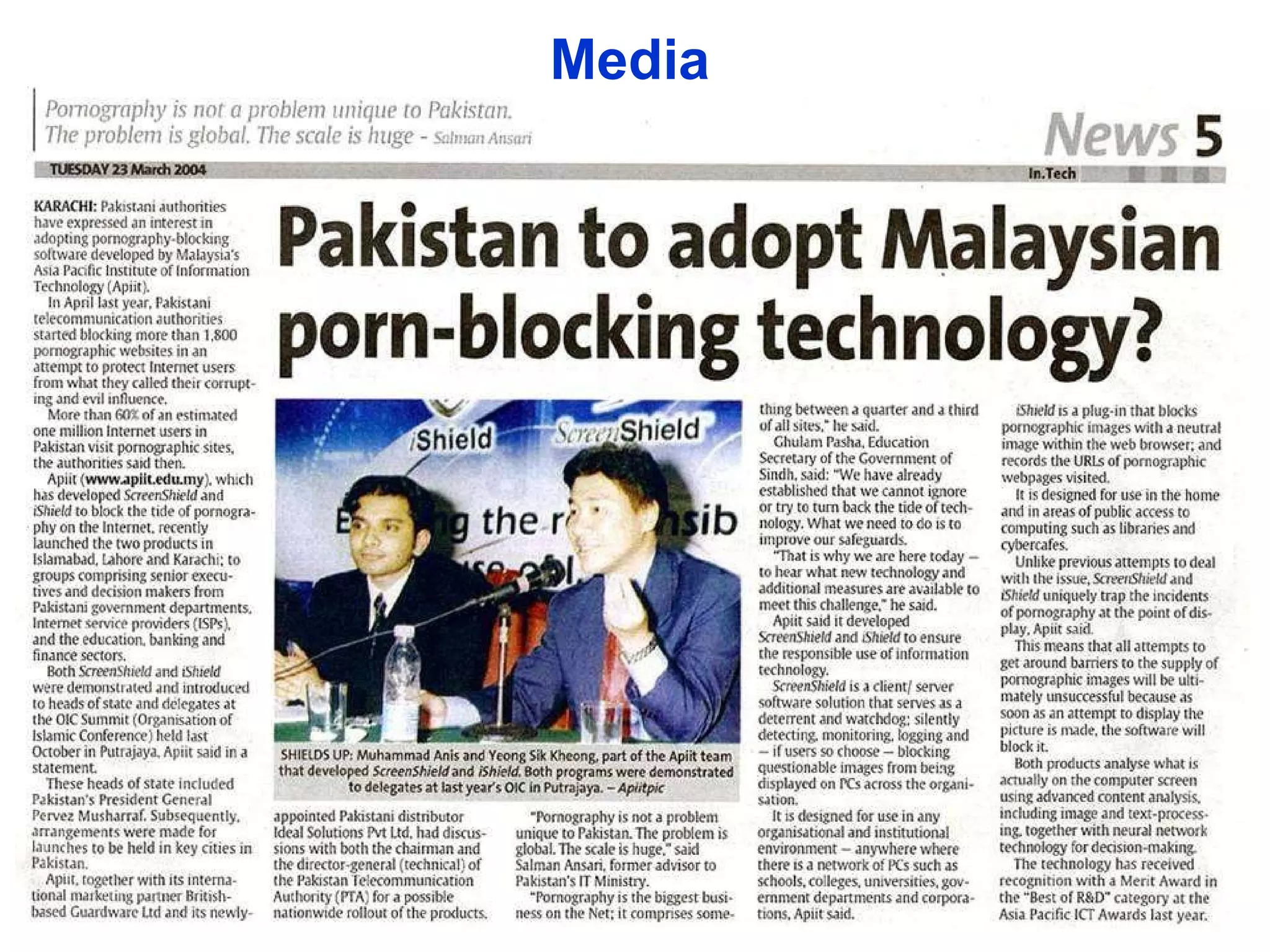
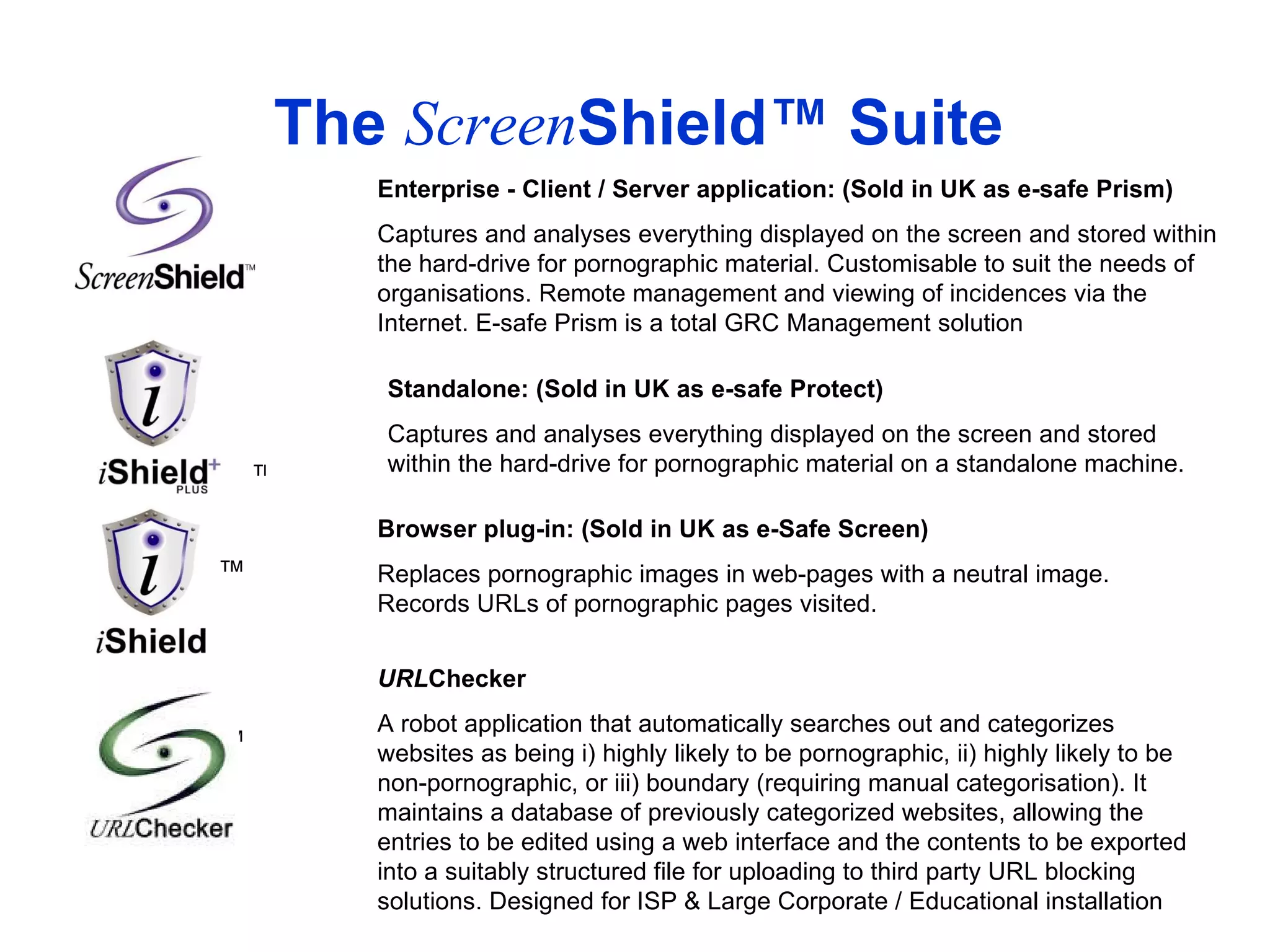
The document discusses the prevalence of pornography online and its negative consequences. It then summarizes the Guardware solution, which uses image and text analysis to detect and filter pornographic content on computers and networks. The system has been successfully implemented by organizations to block inappropriate content and improve productivity.