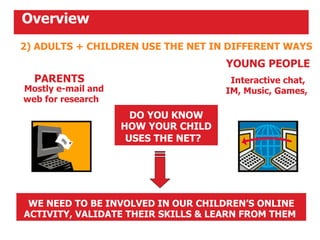
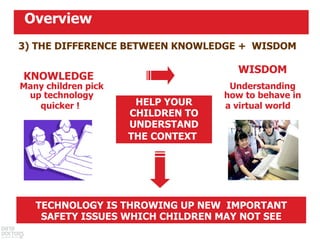
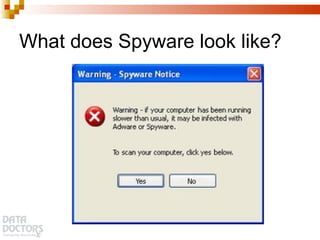
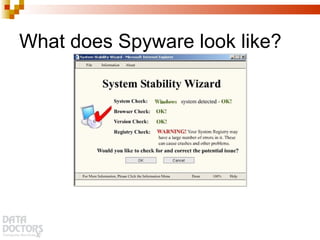
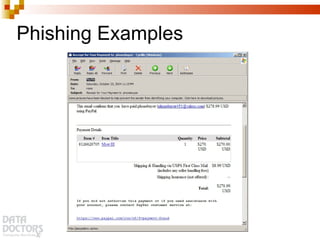
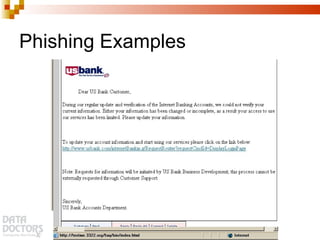
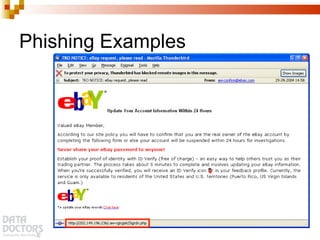
This document provides tips and guidance on internet safety. It discusses the benefits of internet use but also the risks like malware, phishing and exposure to inappropriate content. It emphasizes that children and adults use the internet differently and parents should be involved in their child's online activities. It provides tips for safe internet practices like using antivirus software, strong passwords, backing up data and installing security updates.