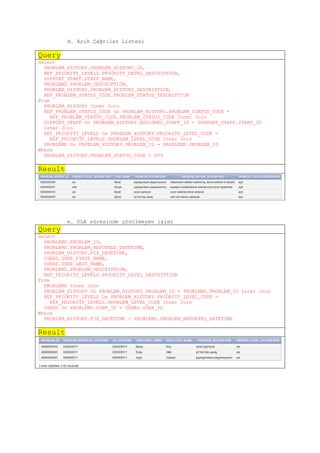
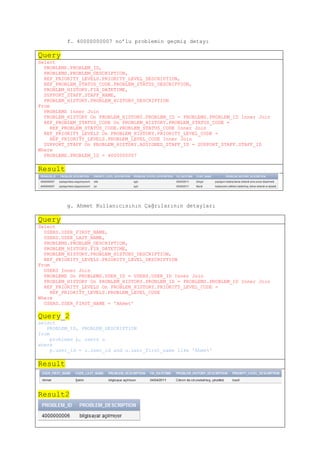
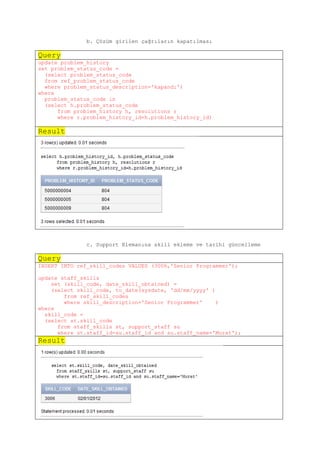
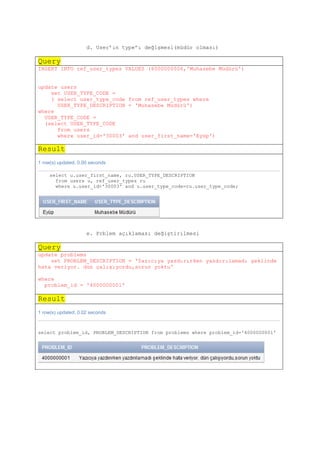
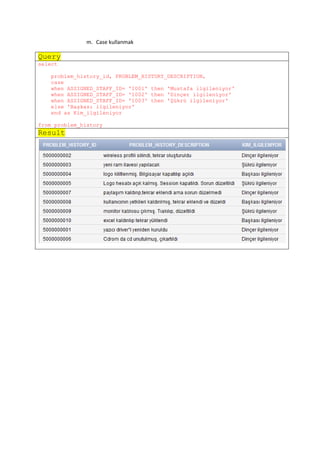
This document summarizes a database project for a help desk database. The database allows for tracking of users, problems and their histories, inventory tracking, and IT staff skills. All queries were designed to address real scenarios that could be encountered.