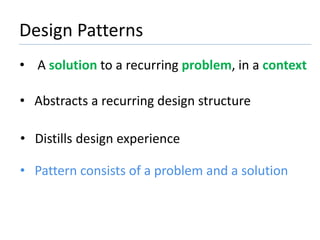
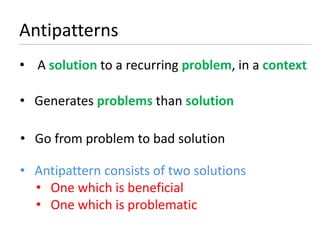
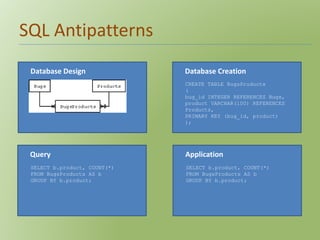
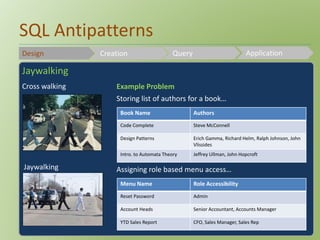
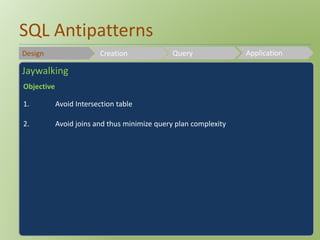
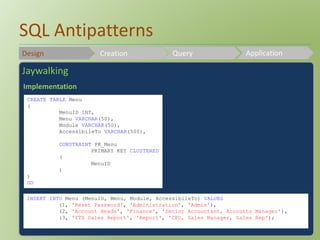
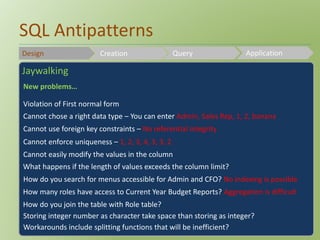
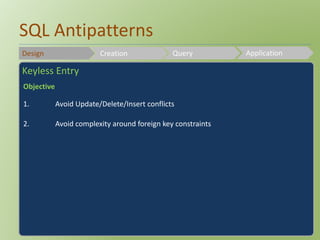
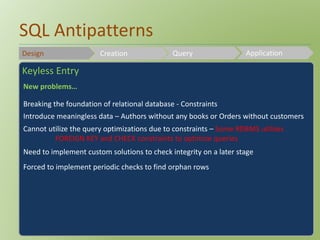
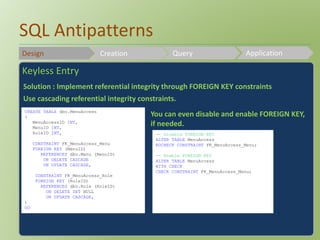
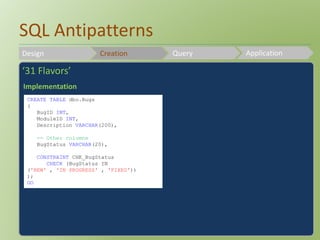
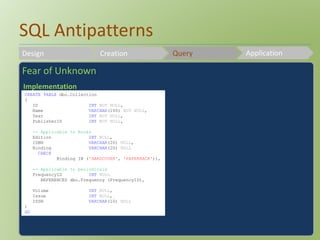
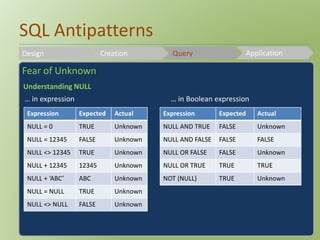
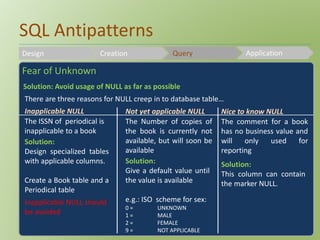
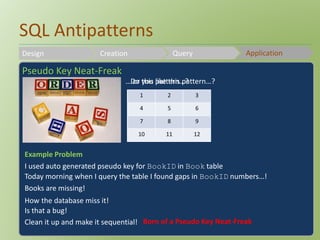
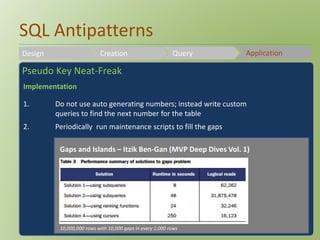
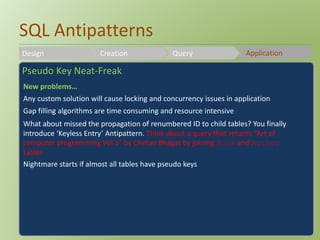
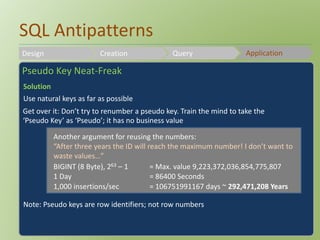
The document discusses SQL antipatterns, which are common mistakes in database design that lead to more issues than solutions. It emphasizes the importance of recognizing these bad practices alongside good design patterns to improve software development. Various examples and solutions are provided to illustrate how to avoid and address these antipatterns.