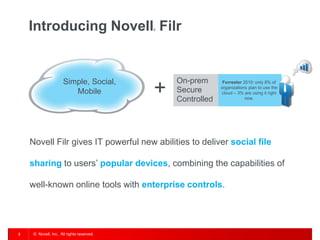
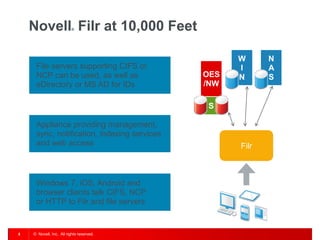
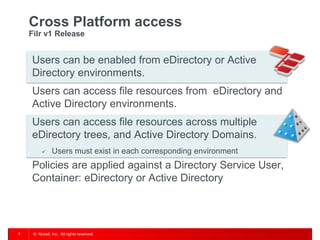
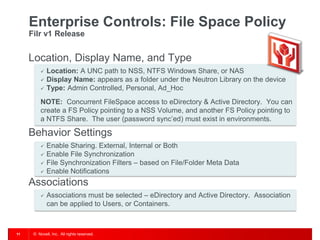
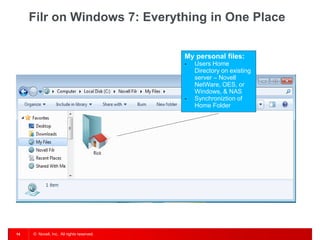
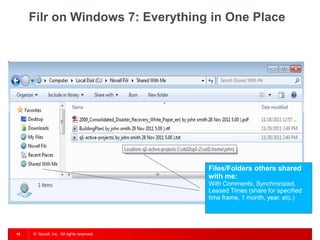
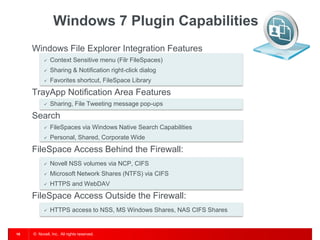
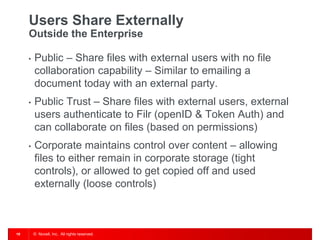
The document introduces Filr, a next generation file experience from Novell that provides simple, social, and mobile file sharing capabilities. It summarizes Filr's key features such as allowing access to file servers using CIFS or NCP, syncing files to devices, and enabling team collaboration through file sharing and social features. Filr can be deployed on-premises or in hybrid cloud environments to give users access to files across different directories and domains.